In this lesson, we explore how to assign roles to AWS services so they can securely perform operations within your AWS account.Documentation Index
Fetch the complete documentation index at: https://notes.kodekloud.com/llms.txt
Use this file to discover all available pages before exploring further.
CloudFormation Example
In this section, we demonstrate how to assign a role when using AWS CloudFormation. Start by navigating to CloudFormation and creating a new stack. Choose any sample template for demonstration purposes, as the specifics of the template do not affect role assignments. Click Next. On the next screen, you will find sections for specifying a stack name and other parameters. For example: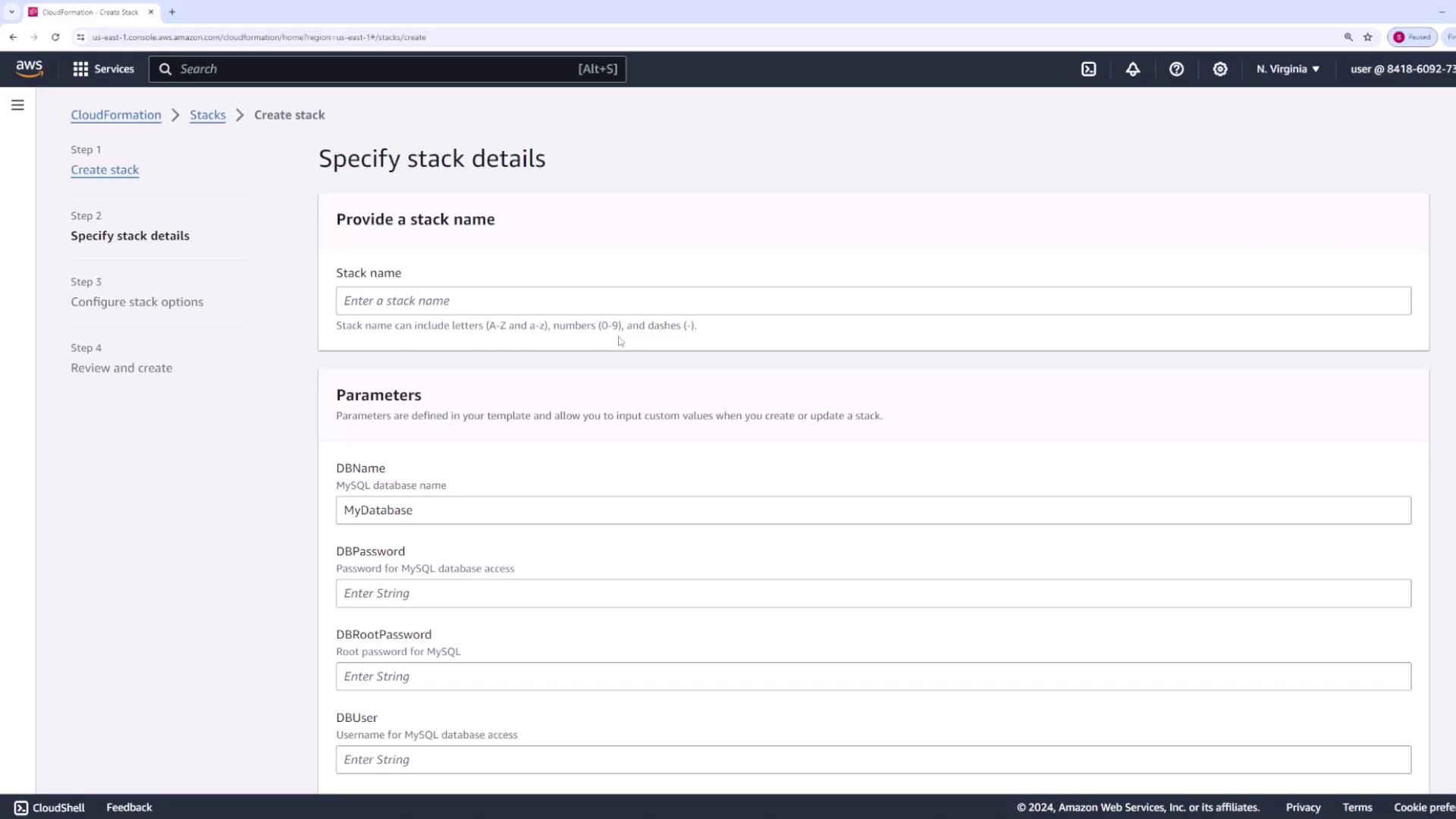
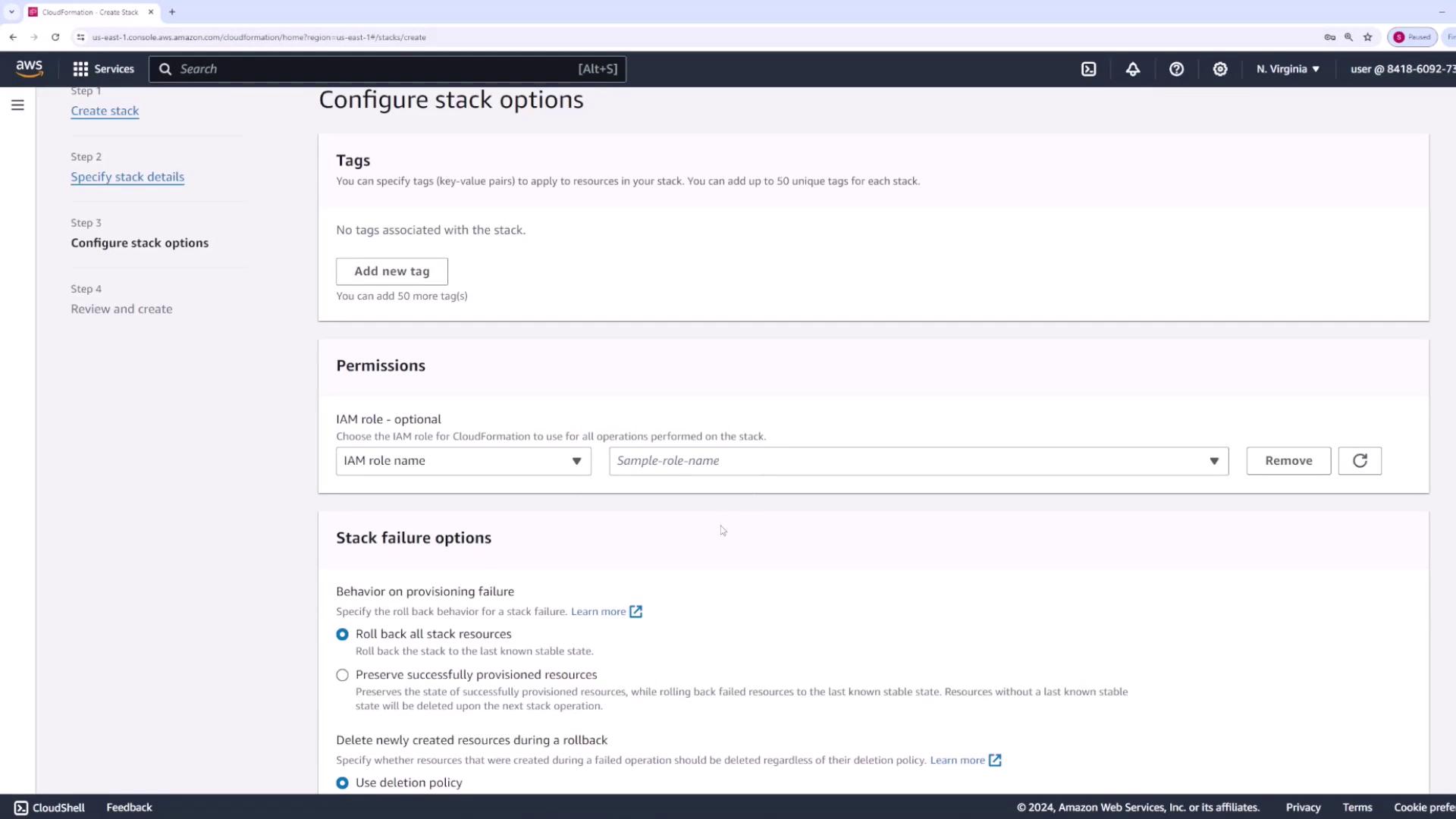
Ensure that the IAM role you assign to CloudFormation includes all the permissions required for the resources specified in your stack.
Lambda Example
Next, consider an example using AWS Lambda—a compute service that lets you run code without the need to manage servers. While you do not need a deep understanding of Lambda’s inner workings, it is essential to know that your function code might require permissions to interact with other AWS services. For example, if your Lambda function is designed to upload files to an S3 bucket or create an API, it must have the appropriate permissions for these tasks. When you click Create function and provide a function name (e.g., “demo”), you will notice a permissions section in the Lambda console.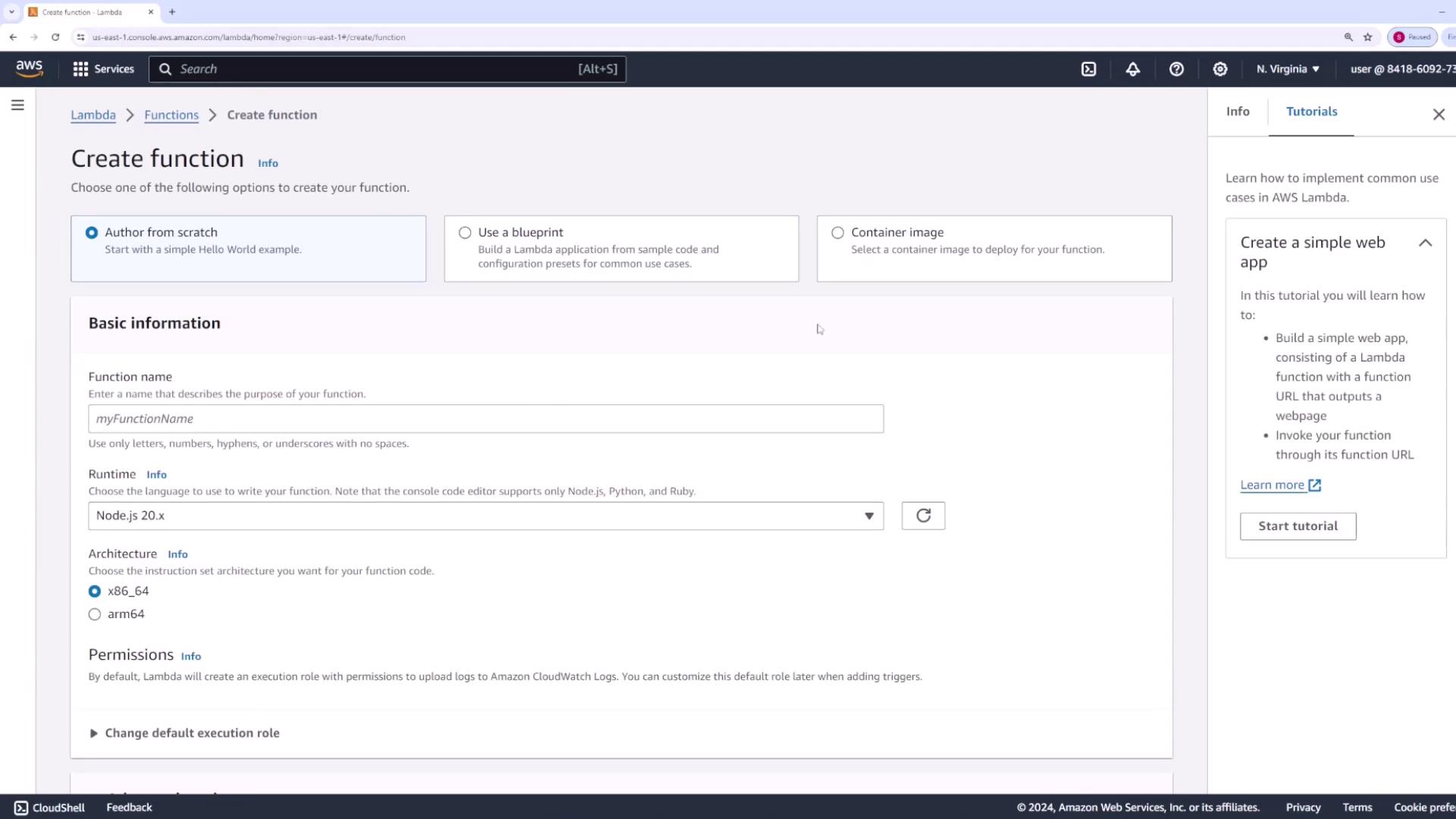
- Create a new role with basic Lambda permissions.
- Use an existing role.
- Generate a new role using an AWS policy template.
Do not overlook the assignments of proper permissions to your Lambda function. Insufficient role permissions can result in unexpected errors when the function attempts to interact with other AWS services.