Hi everyone — welcome to an essential lesson and a core part of this course: AWS CloudFormation. AWS CloudFormation is an Infrastructure as Code (IaC) service that lets you declare and manage AWS resources—such as EC2 instances, S3 buckets, databases, and more—using templates written in YAML or JSON. You describe the desired end state in a template and CloudFormation provisions and configures those resources in the correct order.Documentation Index
Fetch the complete documentation index at: https://notes.kodekloud.com/llms.txt
Use this file to discover all available pages before exploring further.
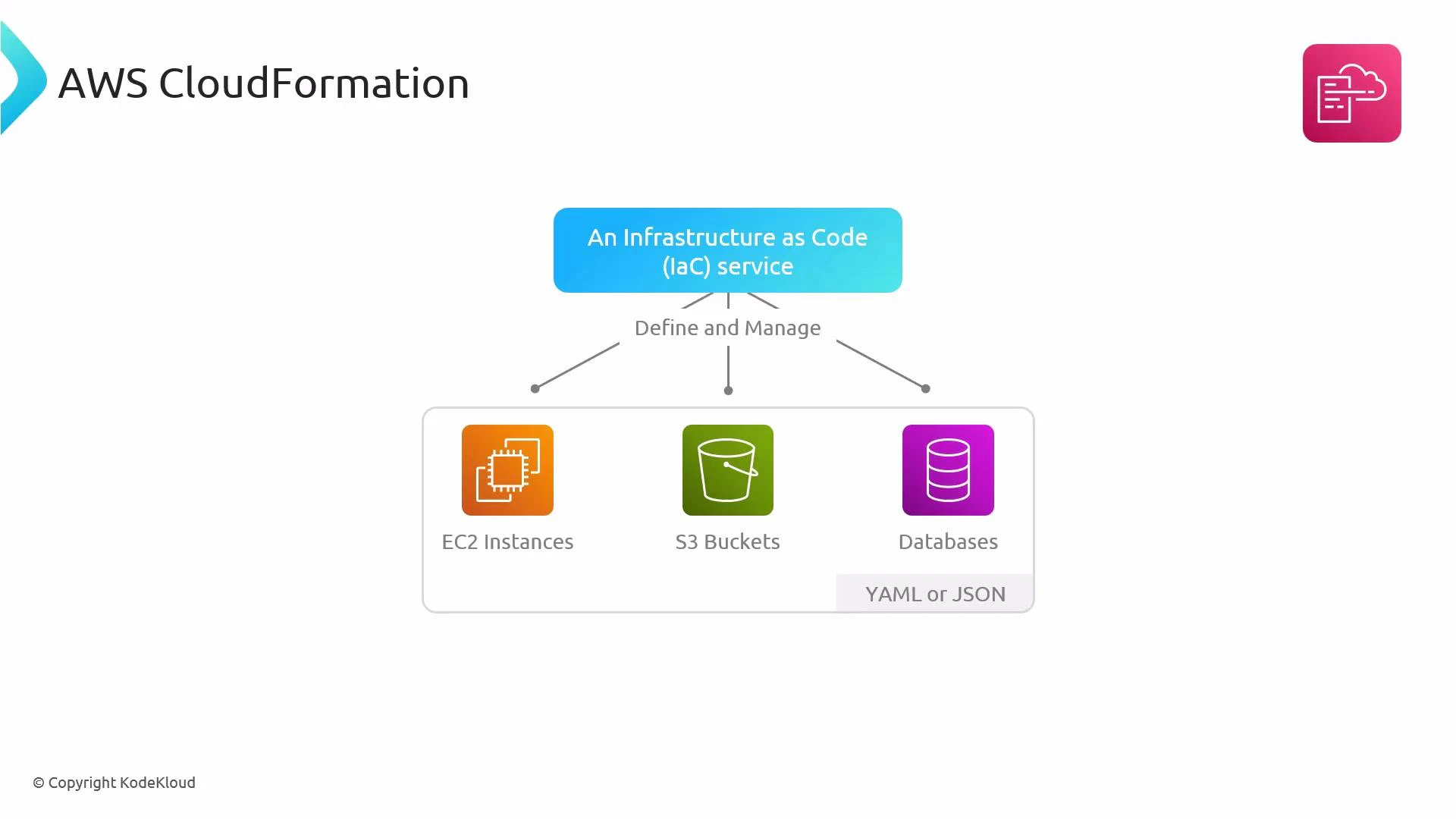
- Declarative: Describe the end state (for example, “an EC2 instance in this VPC with that security group”) and CloudFormation determines how to achieve it.
- Template-driven: Templates are plain text (YAML or JSON), making them easy to version, review, and reuse.
- Automated & repeatable: Provisioning is automated for consistent setups across environments.
- Change tracking & rollback: CloudFormation tracks stack events and can roll back to a previous known-good state if creation or updates fail.
- Parameters — values you pass in when creating a stack (e.g., AMI ID, KeyPair).
- Resources — the AWS resources to create (EC2, SecurityGroup, EIP, etc.).
- Outputs — values returned after stack creation (for example, a public IP or ARN).
- (Optional) Mappings, Conditions, Transform, and Metadata to make templates dynamic and reusable.
This template demonstrates Parameters, Resources, and Outputs. The AMI is parameterized so you can choose an AMI valid for your region when you create the stack.
Many AWS accounts are VPC-only. When creating security groups in a VPC, include a VpcId property on the AWS::EC2::SecurityGroup resource or pass the VPC ID via a parameter. Note: !Ref on a security group returns its ID, which is what SecurityGroupIds expects on an instance.
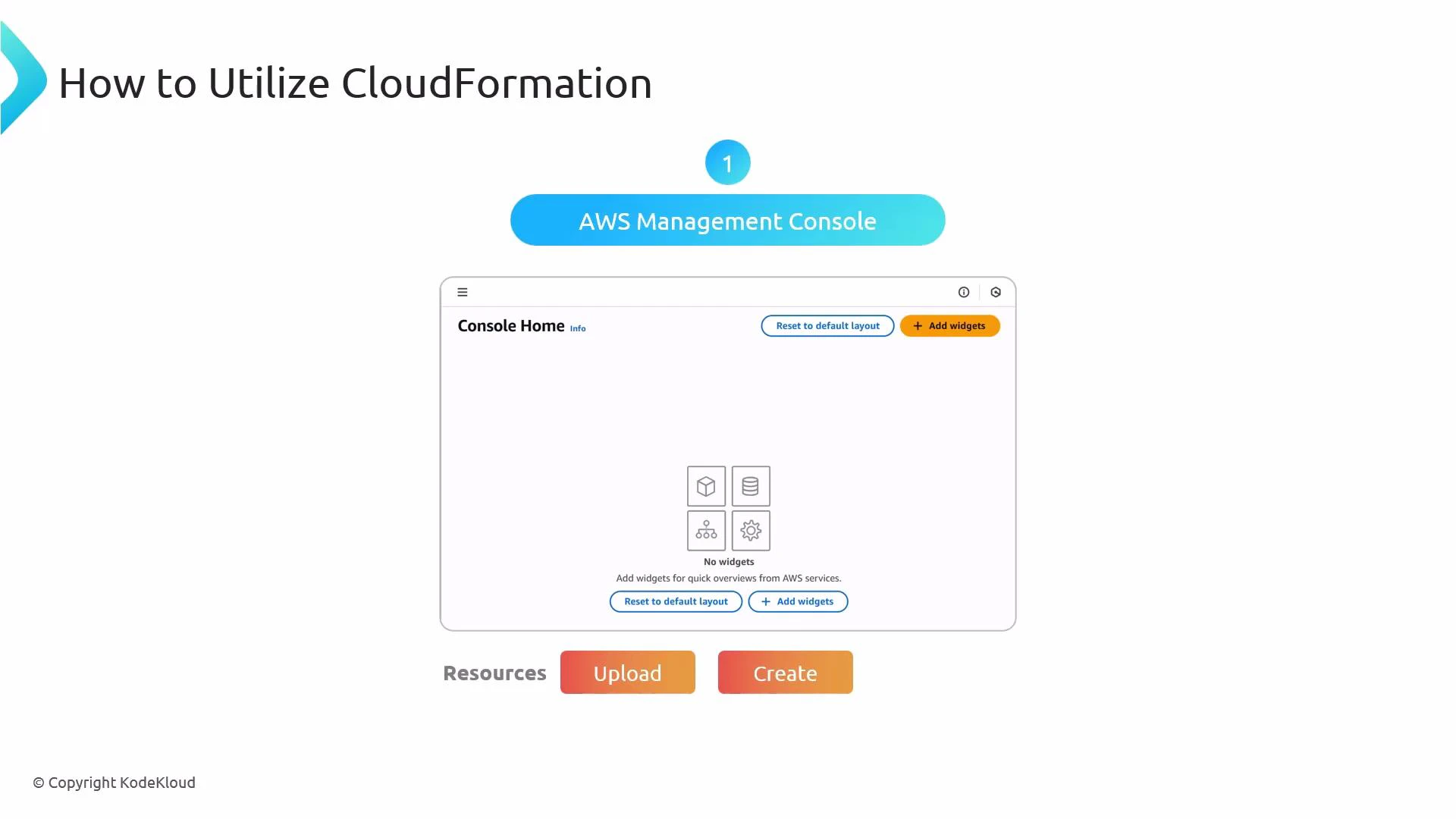
- Write a template describing the resources and properties you need.
- Upload the template (Console, CLI, or API) and create a CloudFormation stack.
- CloudFormation provisions resources in dependency order, provides stack events, and reports status.
- Update the stack as requirements change; CloudFormation makes the necessary modifications, and can roll back on failure.
| Benefit | Description |
|---|---|
| Automation | Create and configure AWS resources automatically from a template. |
| Consistency | Ensure identical infrastructure across development, staging, and production. |
| Reusability | Reuse templates and nest stacks for modular, maintainable infrastructure. |
| Version control | Store infrastructure as code (text) and track changes through Git. |
| Dependency management | CloudFormation resolves resource creation order and dependencies. |
| Safe rollbacks | Automatic rollback helps avoid partial or inconsistent deployments. |

| Method | Typical use case | Example / Tip |
|---|---|---|
| AWS Management Console | Quick authoring, guided stack creation, visual monitoring | Upload or author a template and create a stack; view events in the console. |
| AWS CLI | Automation in scripts and pipelines | aws cloudformation create-stack --stack-name my-stack --template-body file://template.yaml |
| SDK / API | Integration with apps and CI/CD | Programmatically create/update stacks from your tooling or deploy pipelines. |
- Create a stack: aws cloudformation create-stack —stack-name my-stack —template-body file://template.yaml —parameters ParameterKey=KeyName,ParameterValue=myKey
- Update a stack: aws cloudformation update-stack —stack-name my-stack —template-body file://template.yaml
- Delete a stack: aws cloudformation delete-stack —stack-name my-stack
- Parameterize values that differ between environments (AMI IDs, instance sizes, VPC IDs).
- Break large templates into nested stacks for modularity and easier maintenance.
- Use Change Sets to preview the impact of updates before applying them.
- Store templates in a version control system (Git) and include stack creation as part of CI/CD.
- Use IAM roles and least privilege for any automation that creates or updates stacks.
- AWS CloudFormation Documentation: https://docs.aws.amazon.com/cloudformation/
- CloudFormation Best Practices: https://docs.aws.amazon.com/AWSCloudFormation/latest/UserGuide/best-practices.html
- Kubernetes Documentation (concept reference)
- Docker Hub
- Terraform Registry