This guide walks through creating an AWS CloudFormation StackSet that deploys an S3 bucket across multiple accounts and regions. You’ll create a minimal CloudFormation template, prepare the required IAM roles (administration + execution), update the execution role’s trust policy, and deploy the StackSet. This is ideal for multi-account, multi-region resource provisioning with consistent naming via CloudFormation intrinsics. Table of contentsDocumentation Index
Fetch the complete documentation index at: https://notes.kodekloud.com/llms.txt
Use this file to discover all available pages before exploring further.
-
- Create the CloudFormation template
-
- Prepare the IAM roles required by StackSets
-
- Create the StackSet in CloudFormation
-
- Monitor progress and verify
- Summary and references
1) Create the CloudFormation template
Create a new file in your project namedstackset.yaml and add a simple S3 bucket resource. Use the !Sub intrinsic with pseudo-parameters to ensure uniqueness across regions and accounts:
2) Prepare the IAM roles required by StackSets
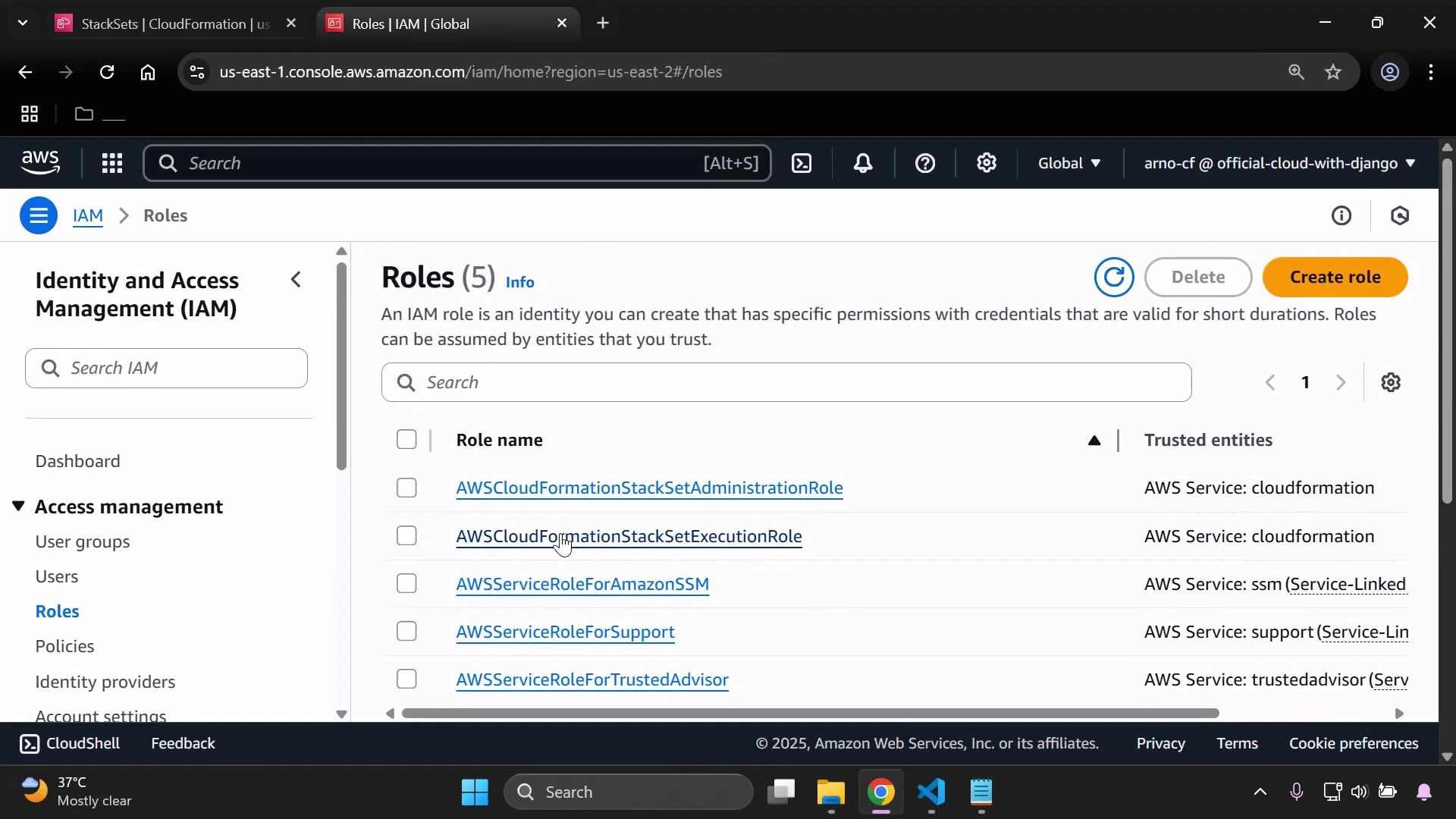
CloudFormation StackSets require two specific IAM roles with exact names so the StackSet controller can perform deployments:| Role name | Purpose | Where to create |
|---|---|---|
| AWSCloudFormationStackSetAdministrationRole | Administration role — created in the account where you create the StackSet (the StackSet controller) | Admin account |
| AWSCloudFormationStackSetExecutionRole | Execution role — created in each target account (or the same account if deploying locally) that allows CloudFormation to create resources there | Target accounts |
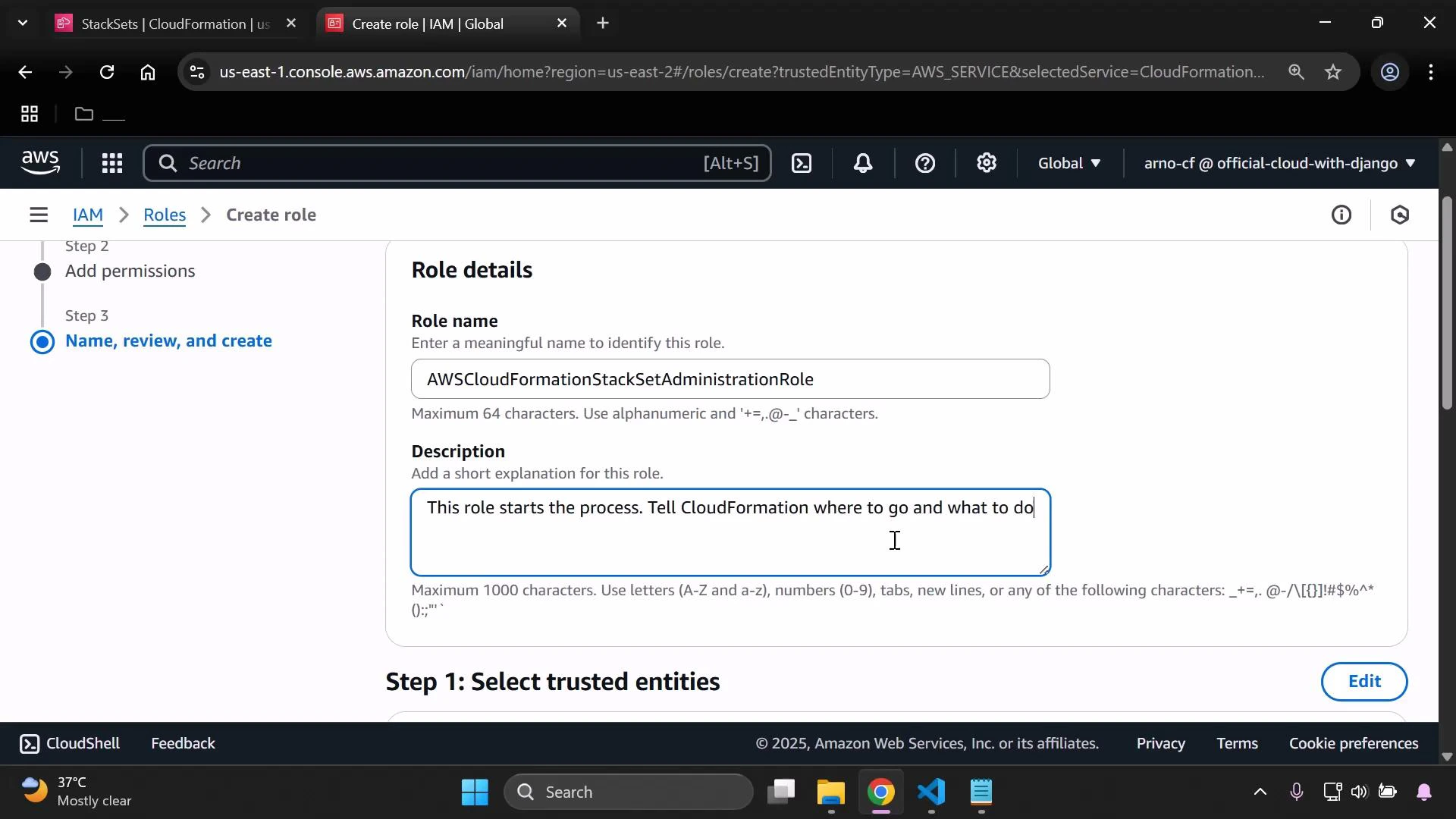
- In the AWS console go to IAM > Roles > Create role.
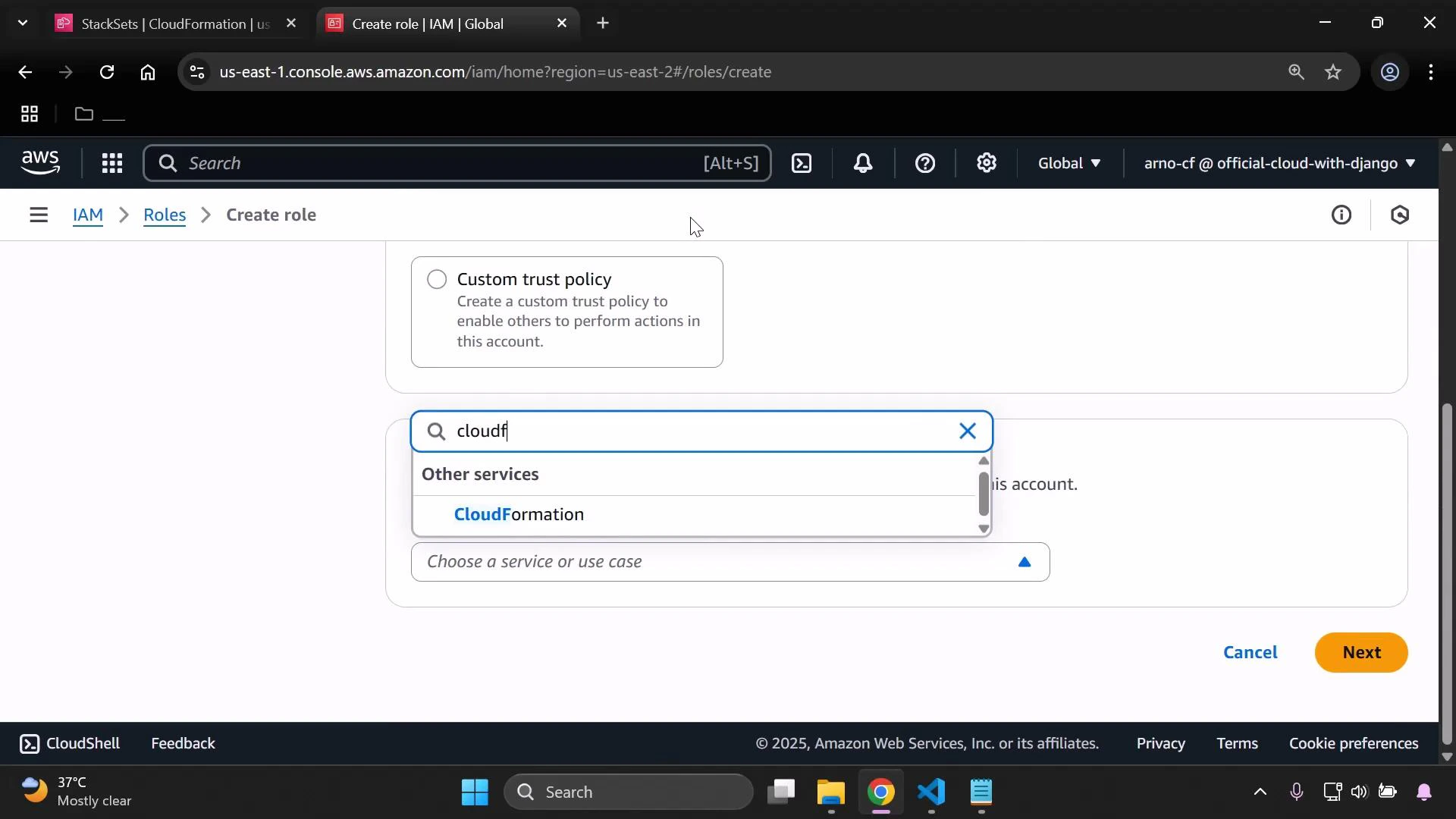
- Select AWS service → CloudFormation.
- Attach AdministratorAccess or a scoped policy granting sufficient CloudFormation and resource permissions.
- Name the role exactly: AWSCloudFormationStackSetAdministrationRole
- Add a helpful description like: “This role starts the StackSet process and tells CloudFormation where and what to deploy.”
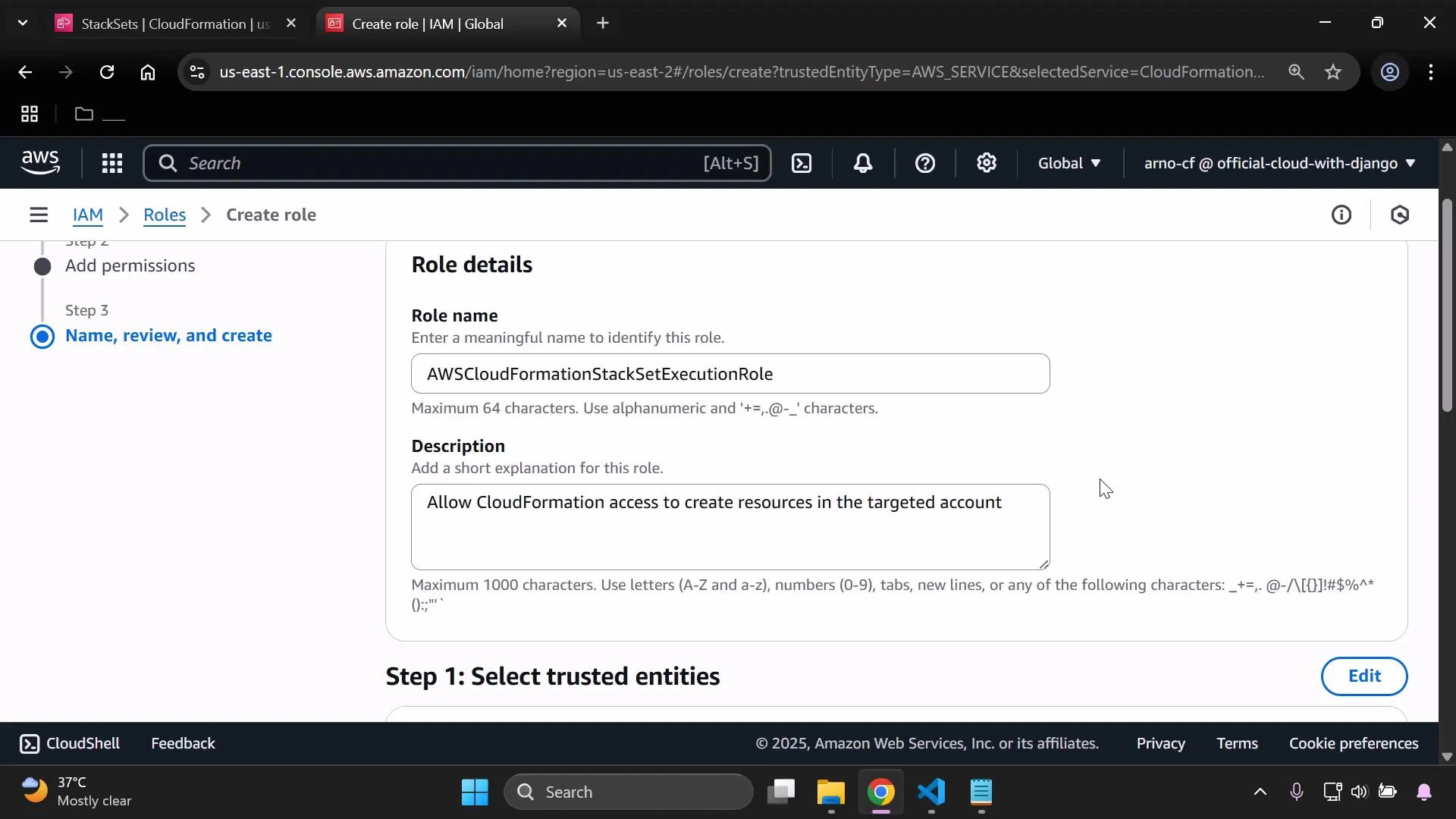
- In IAM > Roles > Create role, choose AWS service → CloudFormation.
- Attach AdministratorAccess or a policy granting the permissions needed by the resources in your template.
- Set the role name exactly to: AWSCloudFormationStackSetExecutionRole
- Add a description such as: “Allows CloudFormation to create resources in the target account.”
Be sure to use the exact role names: AWSCloudFormationStackSetAdministrationRole and AWSCloudFormationStackSetExecutionRole. StackSets expect these names; mismatches will prevent deployments.
Be careful when granting AdministratorAccess in execution roles. Prefer least-privilege policies tailored to the resources in your template. Granting full administrative rights increases attack surface across target accounts.
3) Create the StackSet in CloudFormation
- Open the CloudFormation console and choose Create StackSet.
- Upload your
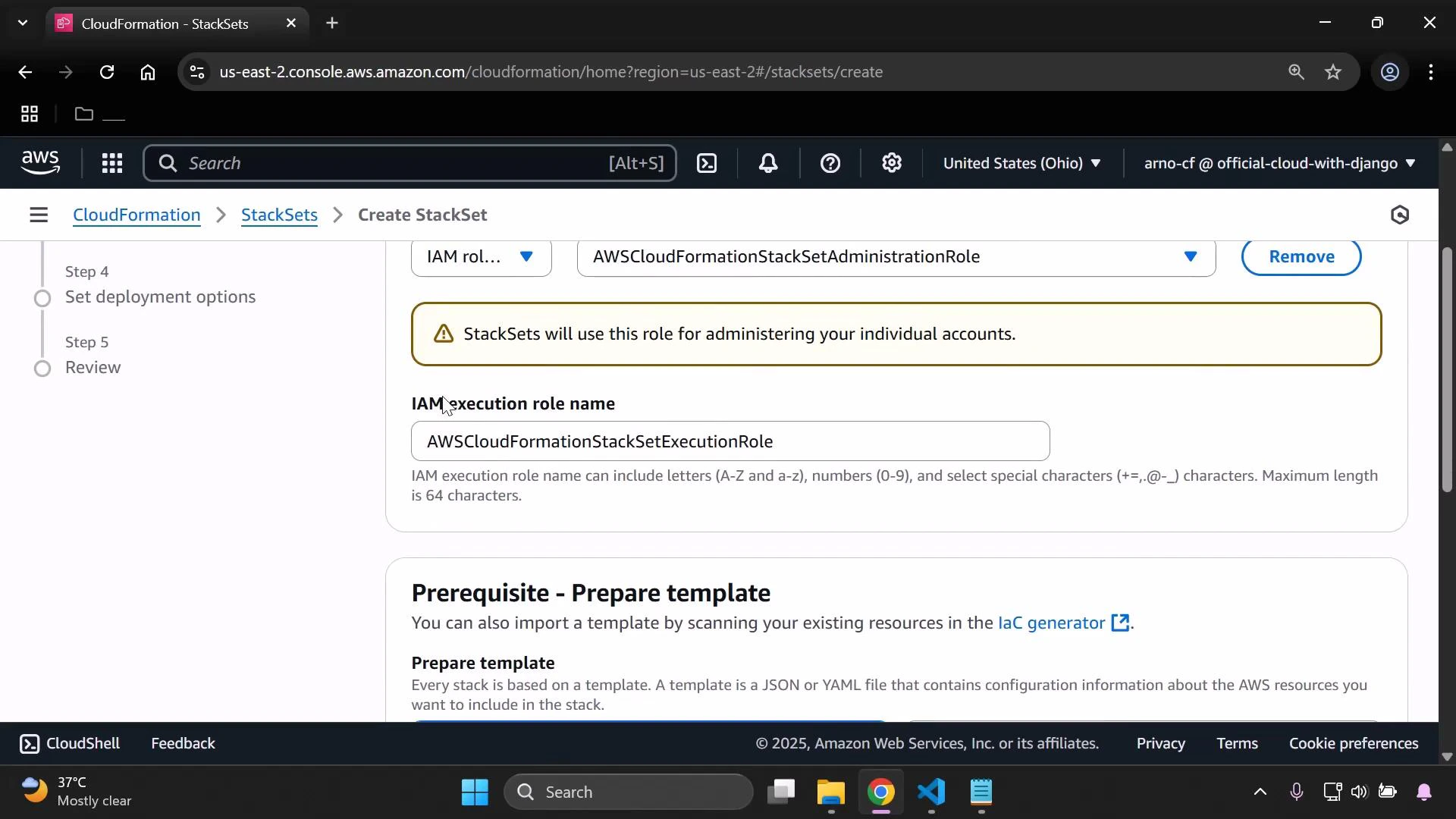
stackset.yamlfile or provide a template URL. - For the administration role, select AWSCloudFormationStackSetAdministrationRole.
- For the execution role name, enter AWSCloudFormationStackSetExecutionRole — CloudFormation will look for this role name in each target account.
- Enter a StackSet name and optional description.
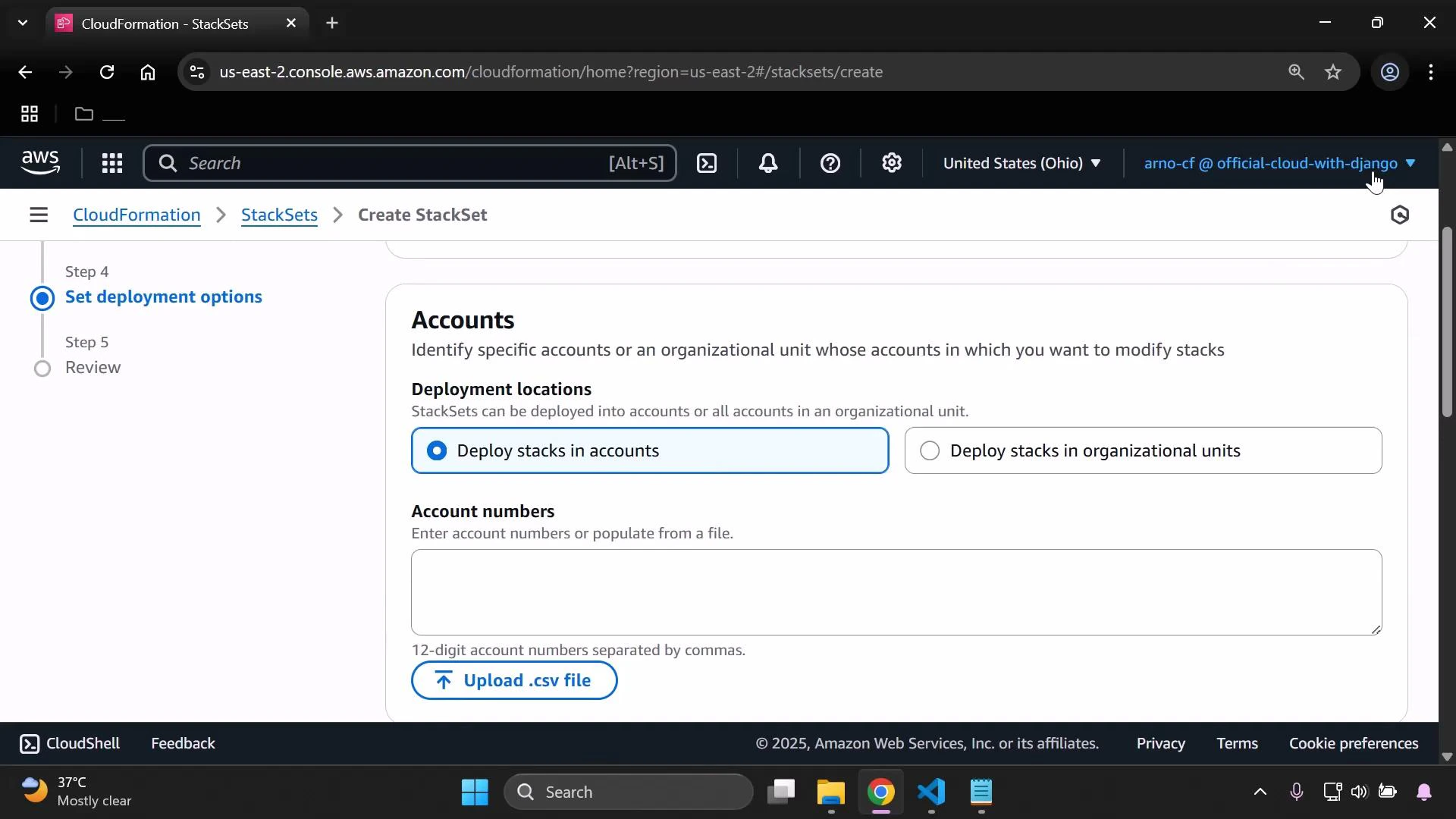
- Specify the target accounts by entering 12-digit AWS account numbers (or upload a CSV of account IDs). If deploying into the same account, include that account ID.
- Choose the regions for deployment. Each account+region combination becomes a stack instance.
4) Monitor progress and verify
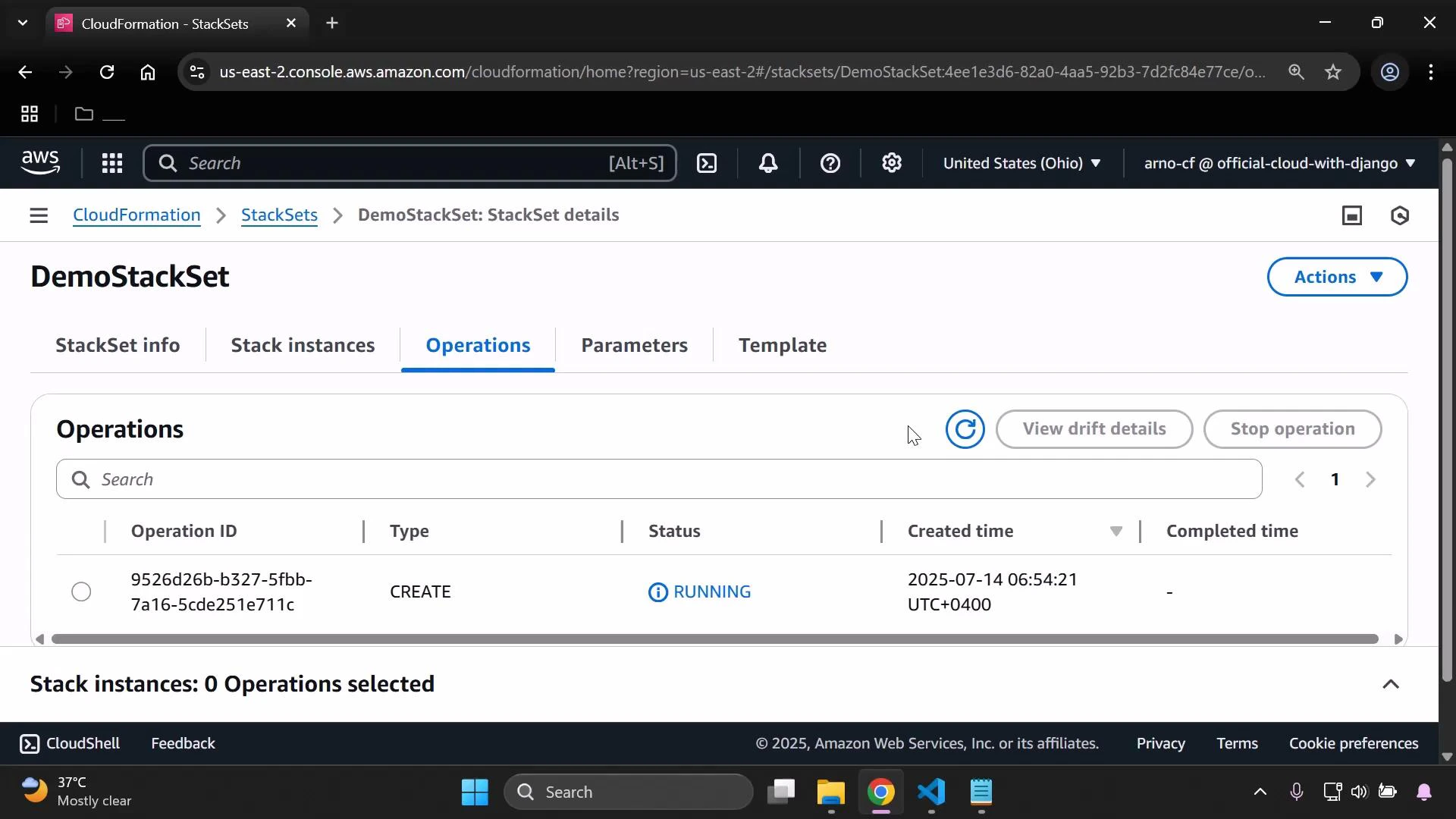
- Open the StackSet and view the Stack instances pane to monitor each stack instance’s status across regions and accounts.
- When operations finish, each Stack instance should be in CREATE_COMPLETE. For deeper inspection, open CloudFormation stacks in the target account/region and review events and resources.
Summary
- Create a CloudFormation template (example: S3 bucket using AWS::Region and AWS::AccountId for unique naming).
- Create two IAM roles with exact names:
- AWSCloudFormationStackSetAdministrationRole (admin account)
- AWSCloudFormationStackSetExecutionRole (target accounts)
- Update the execution role trust policy to allow assumption by the administration role.
- Create the StackSet, specify target accounts and regions, and monitor stack instance creation via the CloudFormation console.