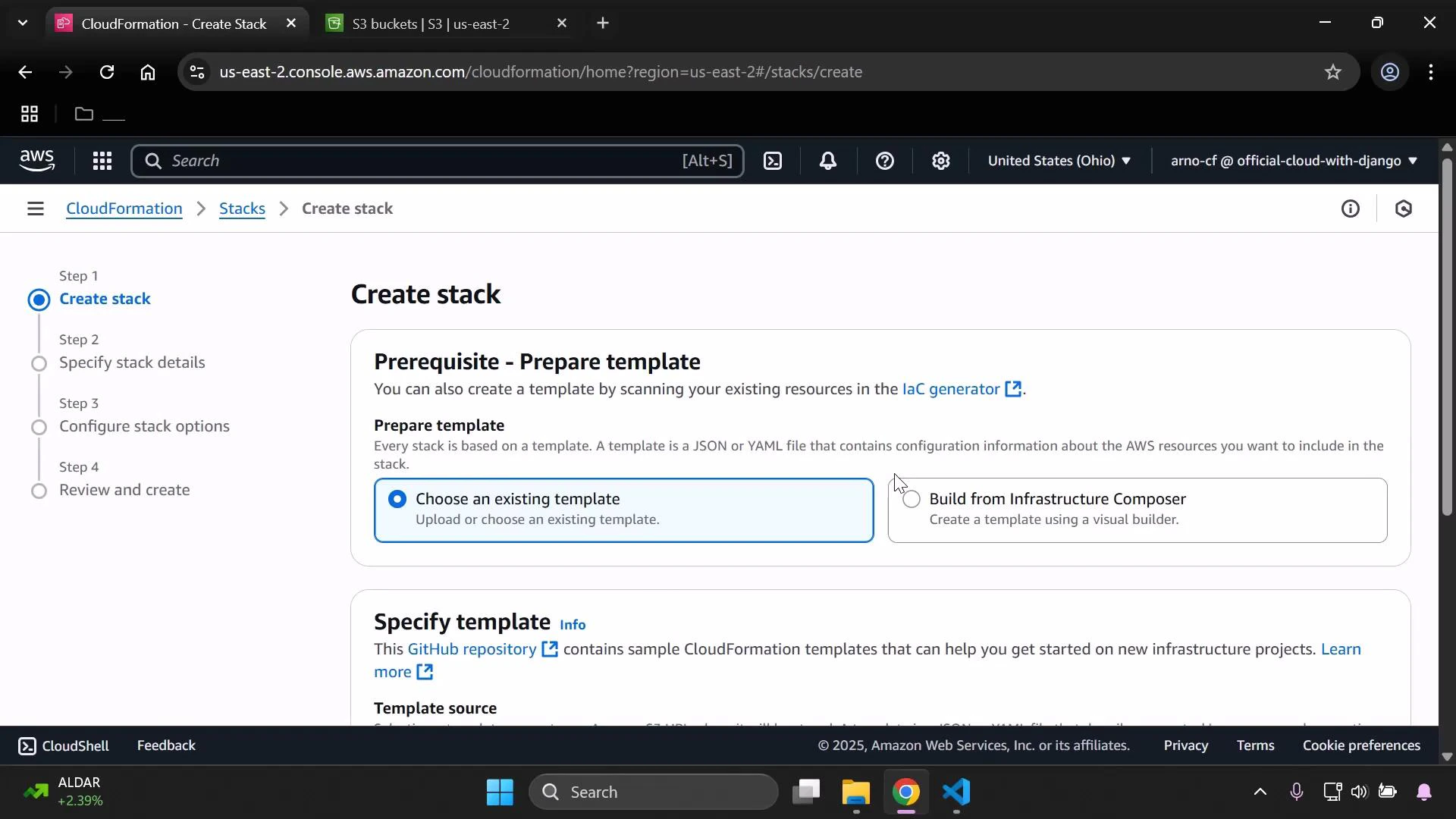
In this walkthrough you’ll use AWS CloudFormation’s Infrastructure Composer to visually design a resource, export the generated template, and create a CloudFormation stack. This is useful when you prefer a drag-and-drop experience to build CloudFormation templates (YAML or JSON), inspect the output, and then deploy it. Key concepts covered:Documentation Index
Fetch the complete documentation index at: https://notes.kodekloud.com/llms.txt
Use this file to discover all available pages before exploring further.
- Use Infrastructure Composer to add an S3 bucket visually
- Inspect and edit the generated CloudFormation template
- Export the template to CloudFormation and deploy the stack
- Understand deletion behavior for S3 buckets created by CloudFormation
1. Add resources in Infrastructure Composer
When Infrastructure Composer launches, you’ll see the visual canvas. Use the search box to find the resource you want to add (for example, type “S3”), then drag an S3 bucket onto the canvas. Select the resource to open the resource properties in the right-hand sidebar. There you can:- Change the logical ID (for example, from the default “bucket” to
MyS3BucketSpecial) - Enable features like static website hosting
- Override the bucket name to supply a specific globally unique name
S3 bucket names must be unique across the entire AWS global namespace and must follow S3 bucket naming rules. If you supply a custom bucket name, ensure it’s globally unique.
eden-kodekloud-vbnc-bkt. Infrastructure Composer fills in reasonable defaults for security and encryption, such as blocking public access and enabling server-side encryption. You can preview and edit the generated template before exporting.
2. Example generated template (YAML)
Below is the CloudFormation YAML that Infrastructure Composer created for the S3 bucket and an attached bucket policy that denies non-HTTPS requests: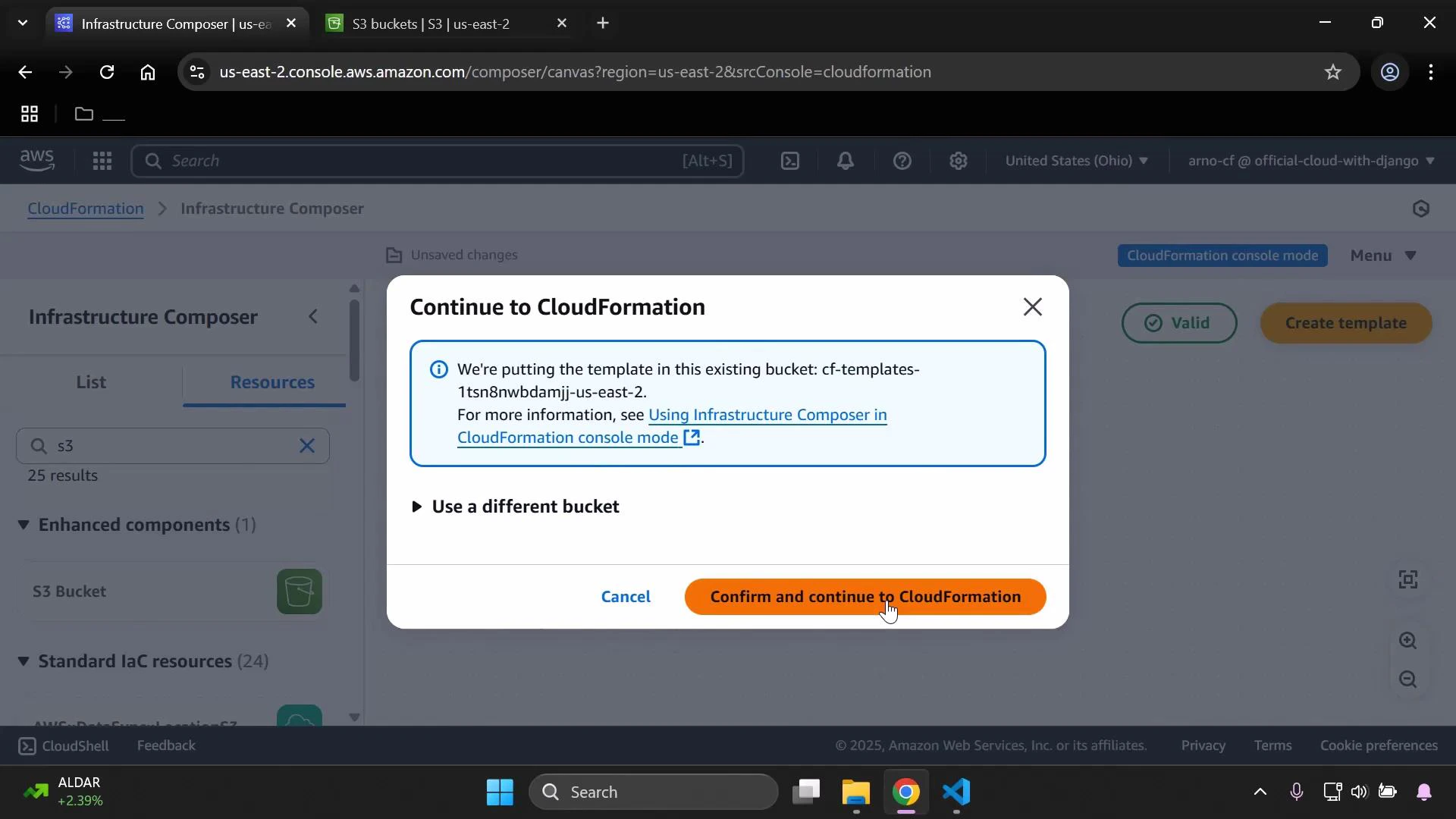
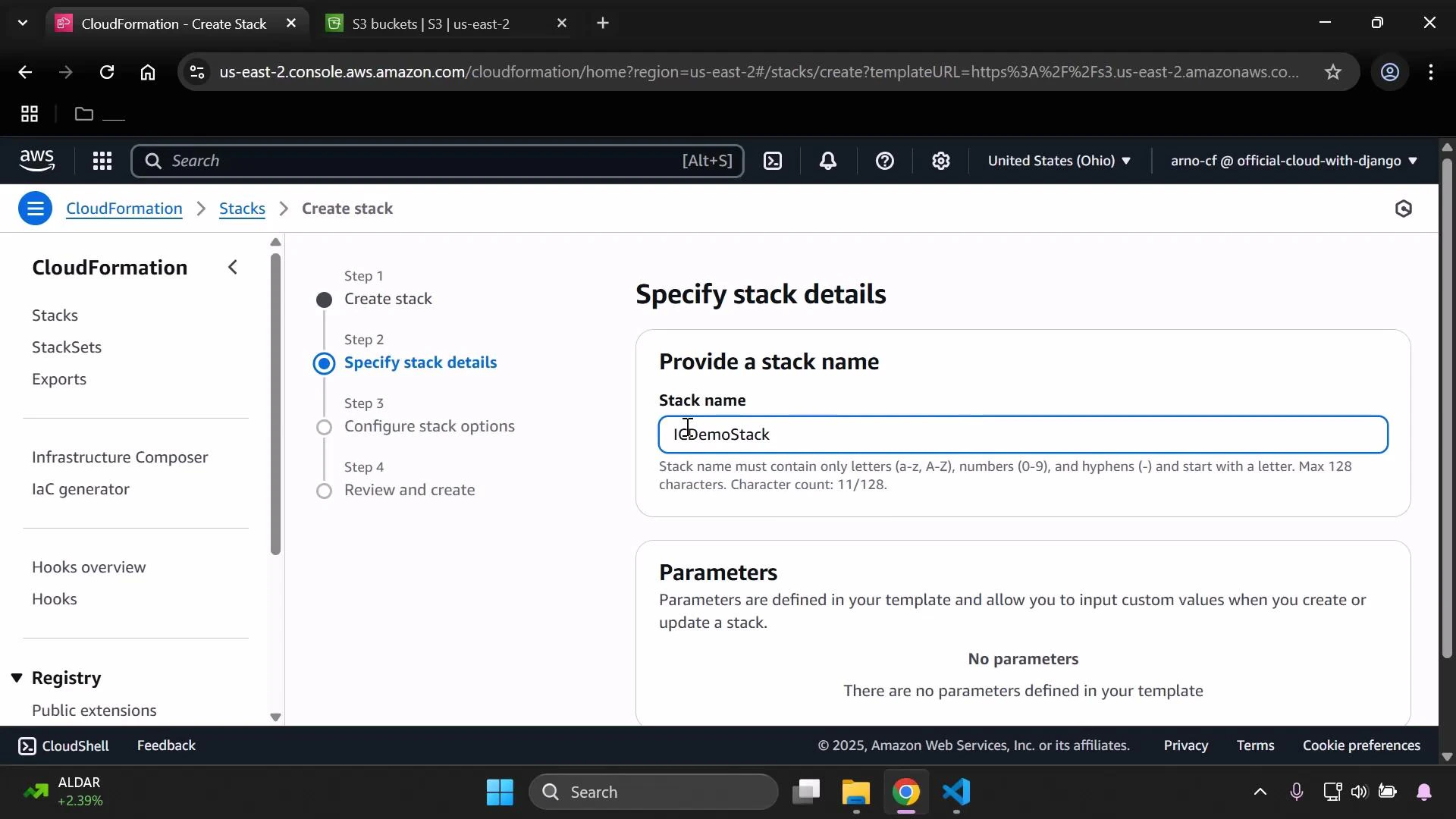
3. Create the CloudFormation stack
Provide a stack name (for example,ICDemoStack) and proceed through the CloudFormation create-stack workflow. Review parameters, options, tags, and IAM capabilities as you normally would.
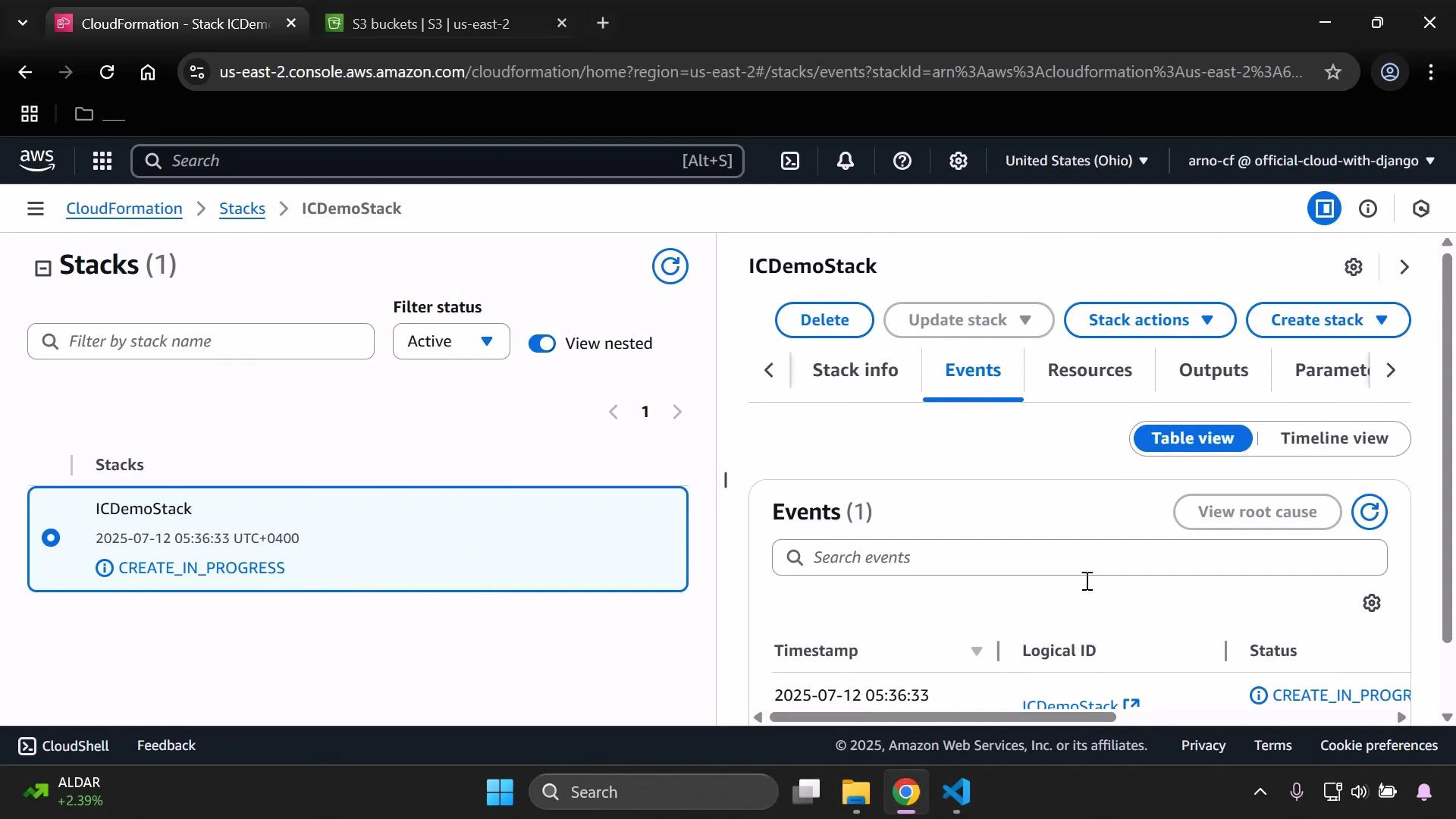
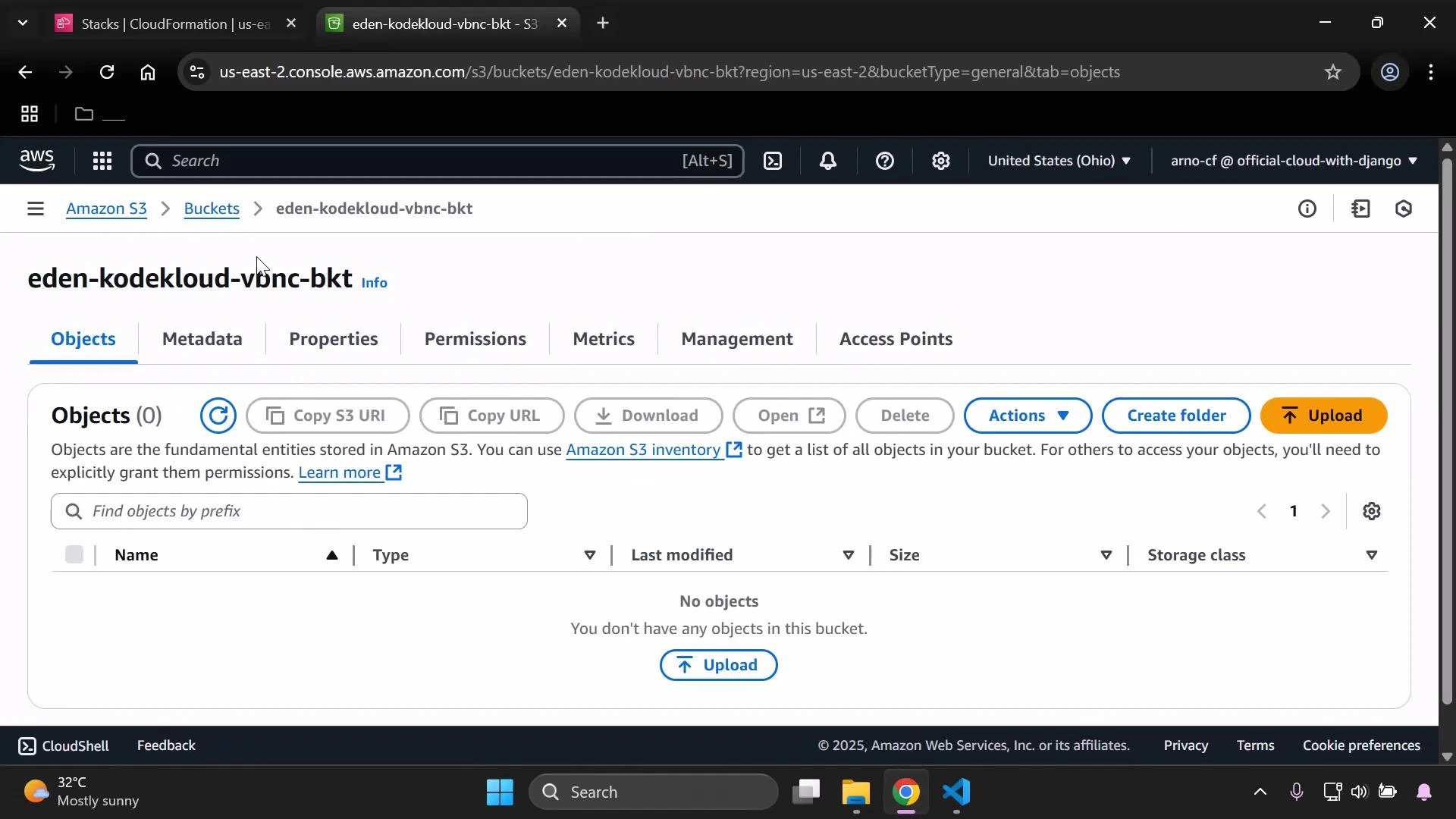
4. Confirm resource creation
After the stack completes, the S3 bucket is available in the S3 console. In the example shown, the bucketeden-kodekloud-vbnc-bkt is present and initially empty.
If an S3 bucket contains objects, CloudFormation stack deletion will fail for the bucket resource unless you explicitly handle object removal (for example with a Lambda-backed custom resource or an S3 lifecycle/configuration that empties the bucket). Always ensure you understand retention and deletion behavior before removing stacks that include S3 buckets.
Resources created by this example
| Resource Type | Logical ID | Purpose |
|---|---|---|
| AWS::S3::Bucket | MyS3BucketSpecial | Stores objects; has server-side encryption and public access blocked |
| AWS::S3::BucketPolicy | MyS3BucketSpecialBucketPolicy | Denies unencrypted (non-HTTPS) requests to the bucket |
Summary
Using Infrastructure Composer you can:- Visually design resources and relationships
- Preview and edit the generated CloudFormation YAML/JSON
- Export the template to CloudFormation for deployment
- Monitor stack creation and validate resulting AWS resources
- Infrastructure Composer — CloudFormation User Guide
- S3 bucket naming rules
- AWS CloudFormation documentation