In this lesson we’ll update an AWS CloudFormation template to allow SSH access in addition to HTTP. This is a common requirement when you need shell access to an EC2 instance for debugging or administration. We’ll show the minimal CloudFormation changes, how to validate the update in the console, and a checklist to avoid common pitfalls.Documentation Index
Fetch the complete documentation index at: https://notes.kodekloud.com/llms.txt
Use this file to discover all available pages before exploring further.
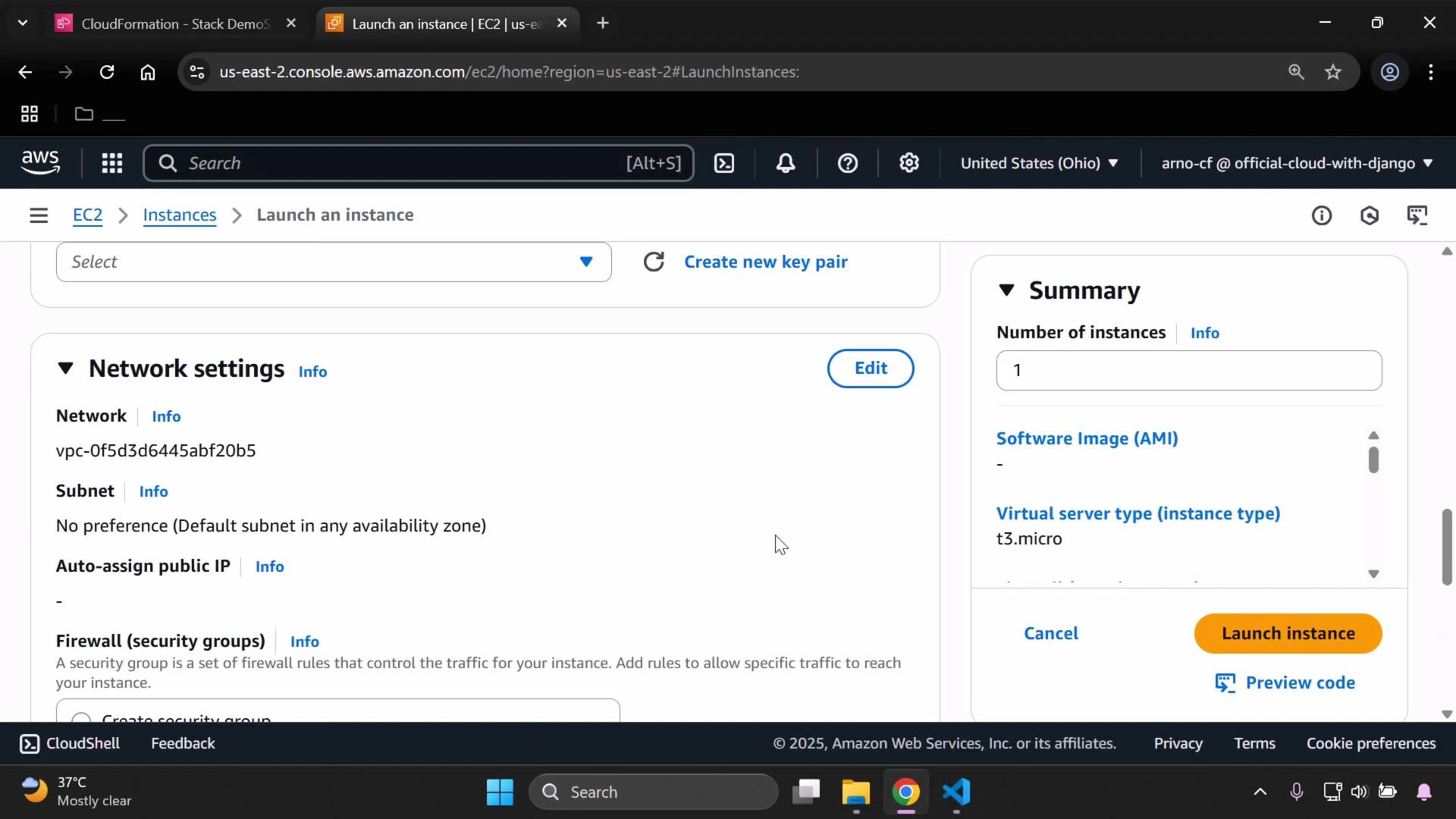
Before you begin, confirm which VPC you’re using (for example, the default VPC in the us-east-2 Ohio region). You can verify the VPC when launching an Amazon Elastic Compute Cloud (EC2) instance or by checking the VPC console. Also ensure you have the CloudFormation stack and template file ready to modify.
- Each dash (-) under SecurityGroupIngress defines a single inbound rule.
- In this example we used the region default VPC; replace the VpcId with the correct VPC for your environment.
| Field | Purpose | Example |
|---|---|---|
| IpProtocol | Protocol for the rule | tcp |
| FromPort | Starting port of range | 22 |
| ToPort | Ending port of range | 22 |
| CidrIp | Source CIDR allowed to connect | 0.0.0.0/0 (open to the Internet) |
Allowing SSH from 0.0.0.0/0 exposes port 22 to the entire Internet. Do not use this for production. Instead, restrict CidrIp to a known IP range (your office/home IP) or use a more secure pattern such as a bastion host or AWS Systems Manager Session Manager for secure access.
- Open the AWS CloudFormation console and select your stack.
- Choose “Update” and upload the modified template (replacing the existing template).
- Proceed through the update steps. The update may take a few minutes to complete.
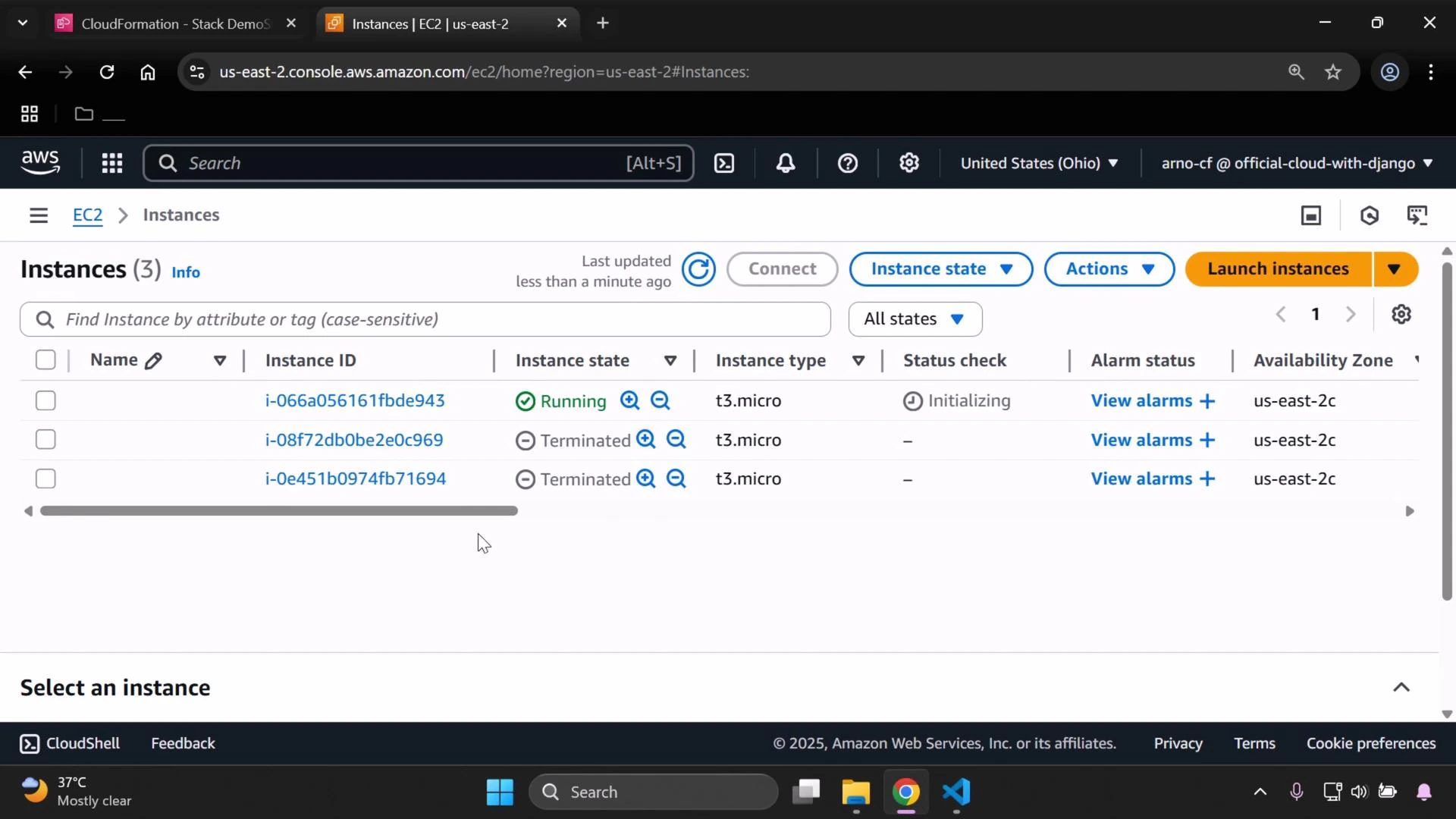
- In the EC2 console, select the running instance.
- Scroll down to the Security groups section and click the security group link.
- Under the Inbound rules tab, confirm there are two rules: HTTP (port 80) and SSH (port 22), with the expected source CIDR ranges.
| Check | How to verify |
|---|---|
| Public IP assigned | Confirm instance has a public IPv4 address or an Elastic IP |
| Security group | Verify inbound rule for port 22 and correct CidrIp |
| Network ACLs | Ensure NACLs on the subnet allow inbound/outbound traffic |
| Instance OS firewall | Check iptables/ufw settings on the VM |
| Key pair & SSH client | Confirm correct private key and SSH command (ssh -i key.pem ec2-user@public-ip) |
| Replacement instance | If CloudFormation replaced the instance, use the new instance’s public IP |