In this lesson you’ll see how to resolve an authorization error when deleting an AWS CloudFormation stack because the current IAM identity lacks the required identity-based permission. The workflow:Documentation Index
Fetch the complete documentation index at: https://notes.kodekloud.com/llms.txt
Use this file to discover all available pages before exploring further.
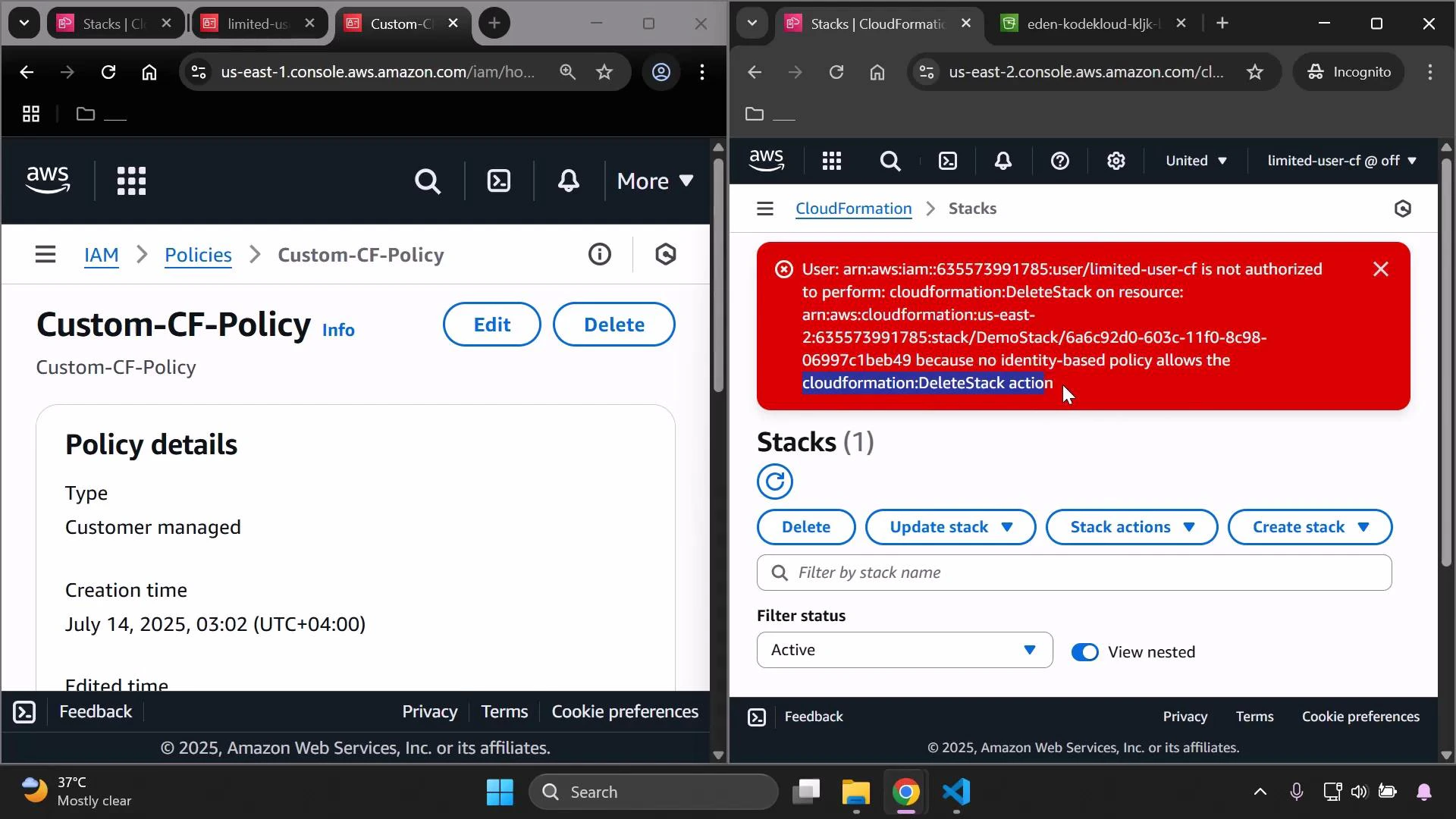
- Reproduce the authorization error in the CloudFormation console.
- Update a customer-managed IAM policy to allow deletion.
- Retry and delete the stack (and any S3 bucket the stack created).
- Clean up the temporary IAM resources.
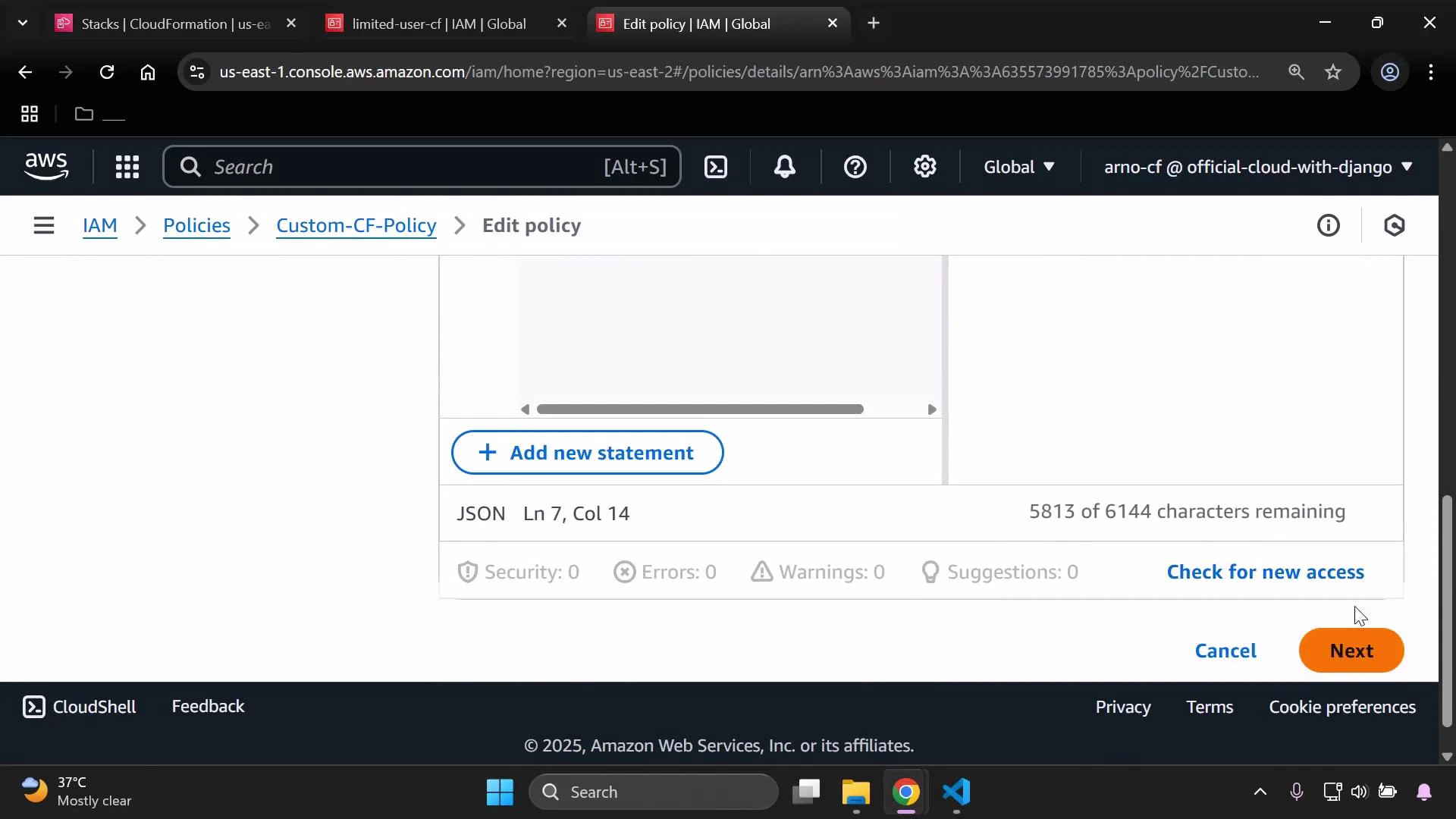
cloudformation:DeleteStack action to the policy’s allowed actions. If the stack creates an S3 bucket, include S3 permissions because CloudFormation must be able to delete that bucket as part of the stack deletion (CloudFormation cannot remove non-empty buckets).
Example JSON policy that allows stack deletion and S3 access:
Deleting a stack will remove the stack and its associated resources (for example, S3 buckets). Empty any S3 buckets first if necessary, and be certain you want to remove these resources — deletion is irreversible.
If your stack contains resources that require special deletion steps (for example, non-empty S3 buckets or resources protected by termination protection), remove those prerequisites before deleting the stack.
| Action | Description |
|---|---|
| Detach policy from user | Remove the customer-managed policy from the limited user to revert their permissions. |
| Delete the policy | Sign in as a user with permission to delete the customer-managed policy and remove the policy. |
| Delete the temporary user | Remove the temporary user if it’s no longer required. |
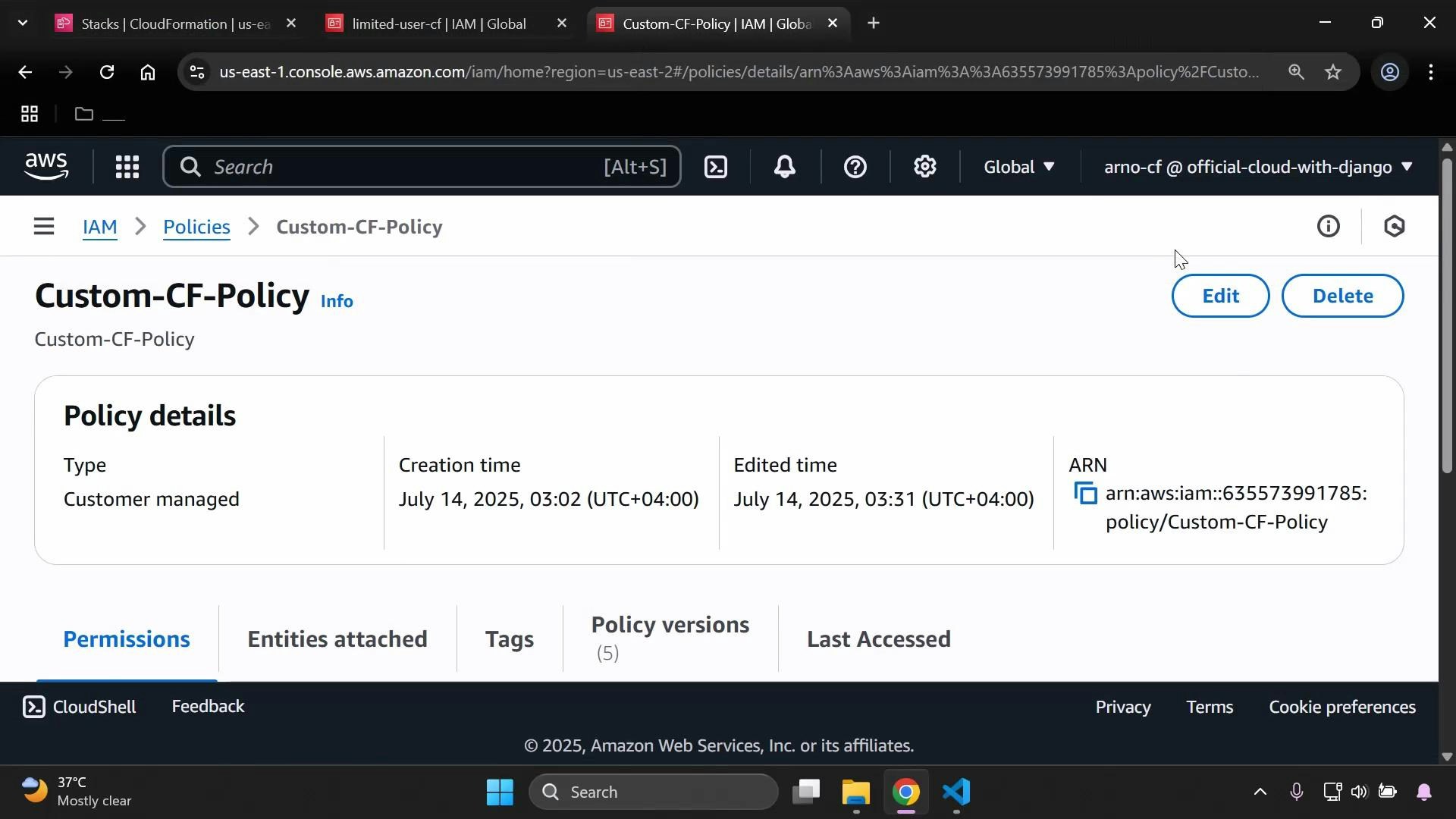
- Refresh the IAM and CloudFormation consoles to ensure the user, policy, and stack are removed.
- Confirm S3 bucket and object listings are empty for resources created by the stack.
- AWS CloudFormation User Guide — Deleting a Stack
- AWS Identity and Access Management (IAM) Documentation
- S3 Considerations When Deleting Stacks