This lesson demonstrates how to create and apply an AWS CloudFormation stack policy that prevents updates to a specific resource in your template. You’ll create a stack policy file, attach it during stack creation, attempt an update to a protected resource, and observe CloudFormation deny the update and roll back the change. Tools and references:Documentation Index
Fetch the complete documentation index at: https://notes.kodekloud.com/llms.txt
Use this file to discover all available pages before exploring further.
- Visual Studio Code: https://code.visualstudio.com/
- CloudFormation stack policies: https://docs.aws.amazon.com/AWSCloudFormation/latest/UserGuide/protect-stack-resources.html
- CloudFormation basics: https://docs.aws.amazon.com/AWSCloudFormation/latest/UserGuide/Welcome.html
- Open your project in Visual Studio Code.
- In Explorer, create a new file named
stack-policy.json.
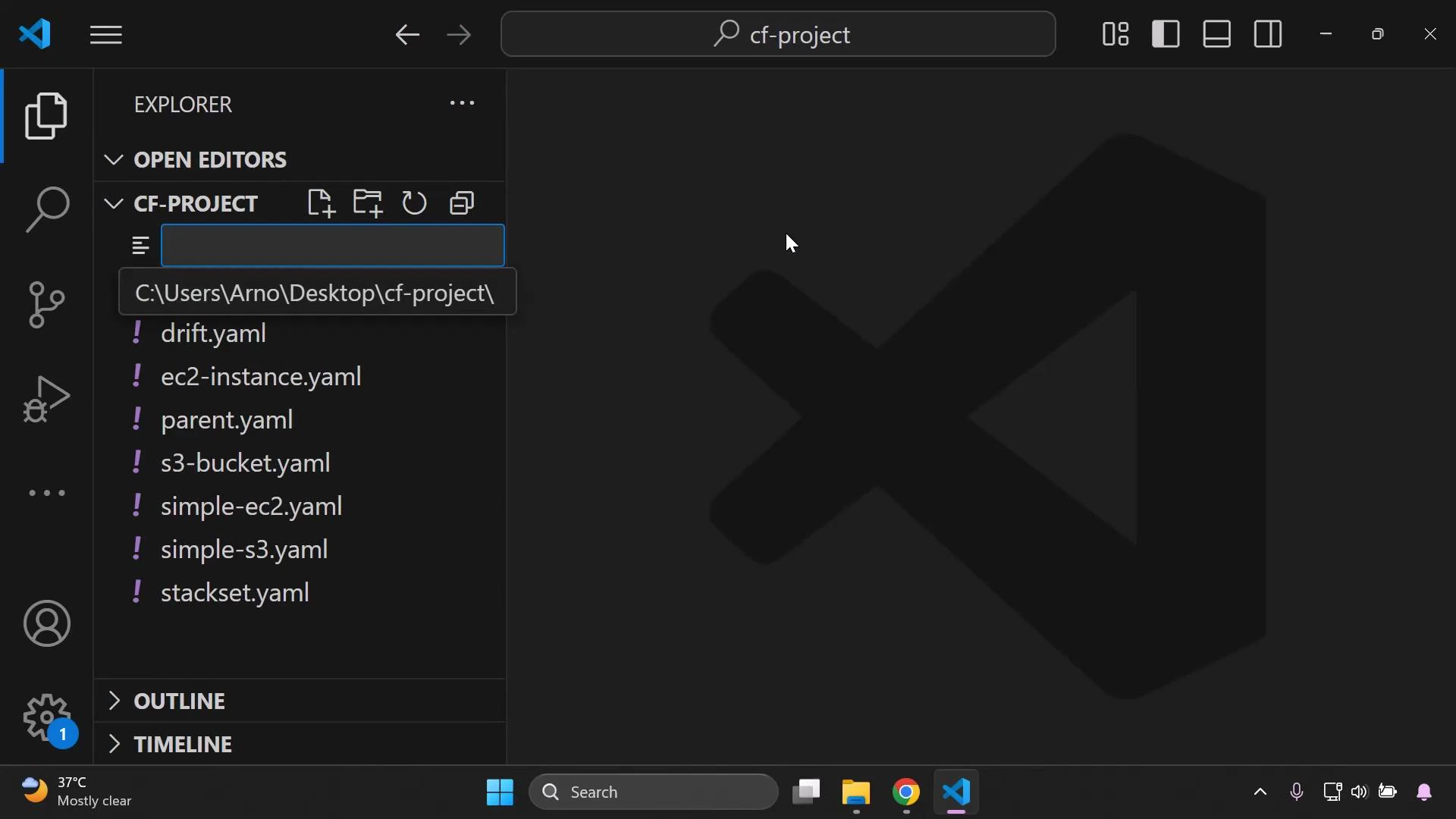
stack-policy.json. This policy explicitly denies any update actions on the resource whose logical ID is MyBucket:
| Field | Purpose | Example in this policy |
|---|---|---|
| Effect | Whether to allow or deny matching actions | ”Deny” |
| Action | Action or actions the policy covers | ”Update:*” (all update operations) |
| Principal | Who the policy applies to | ”*” (all principals) |
| Resource | Target resource, referenced by logical ID | ”LogicalResourceId/MyBucket” |
Stack policies refer to the resource’s logical ID defined in the template (for example,
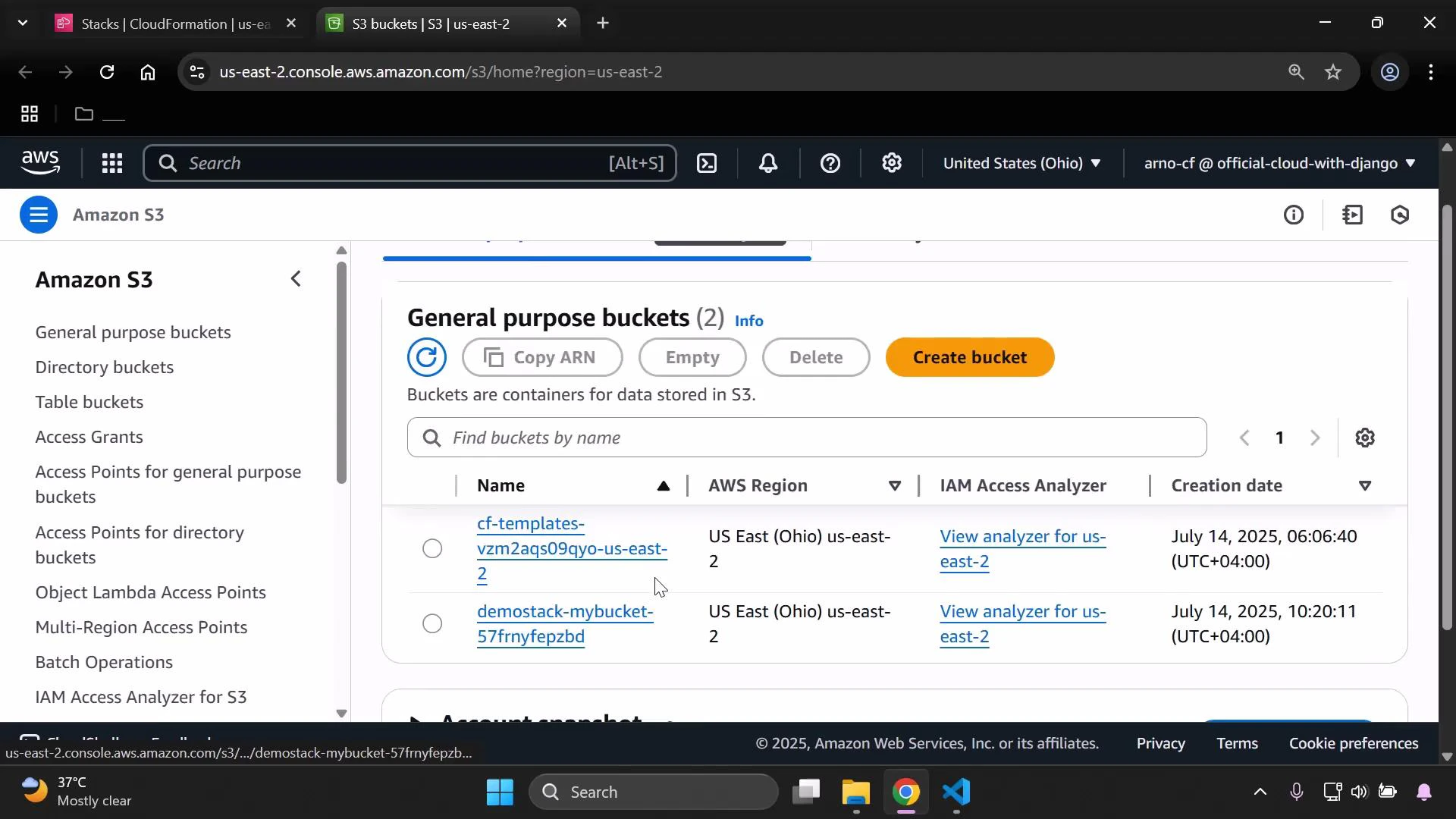
MyBucket under Resources). They do not refer to the physical resource name, ARN, or bucket name.MyBucket. Example initial template to deploy the stack:
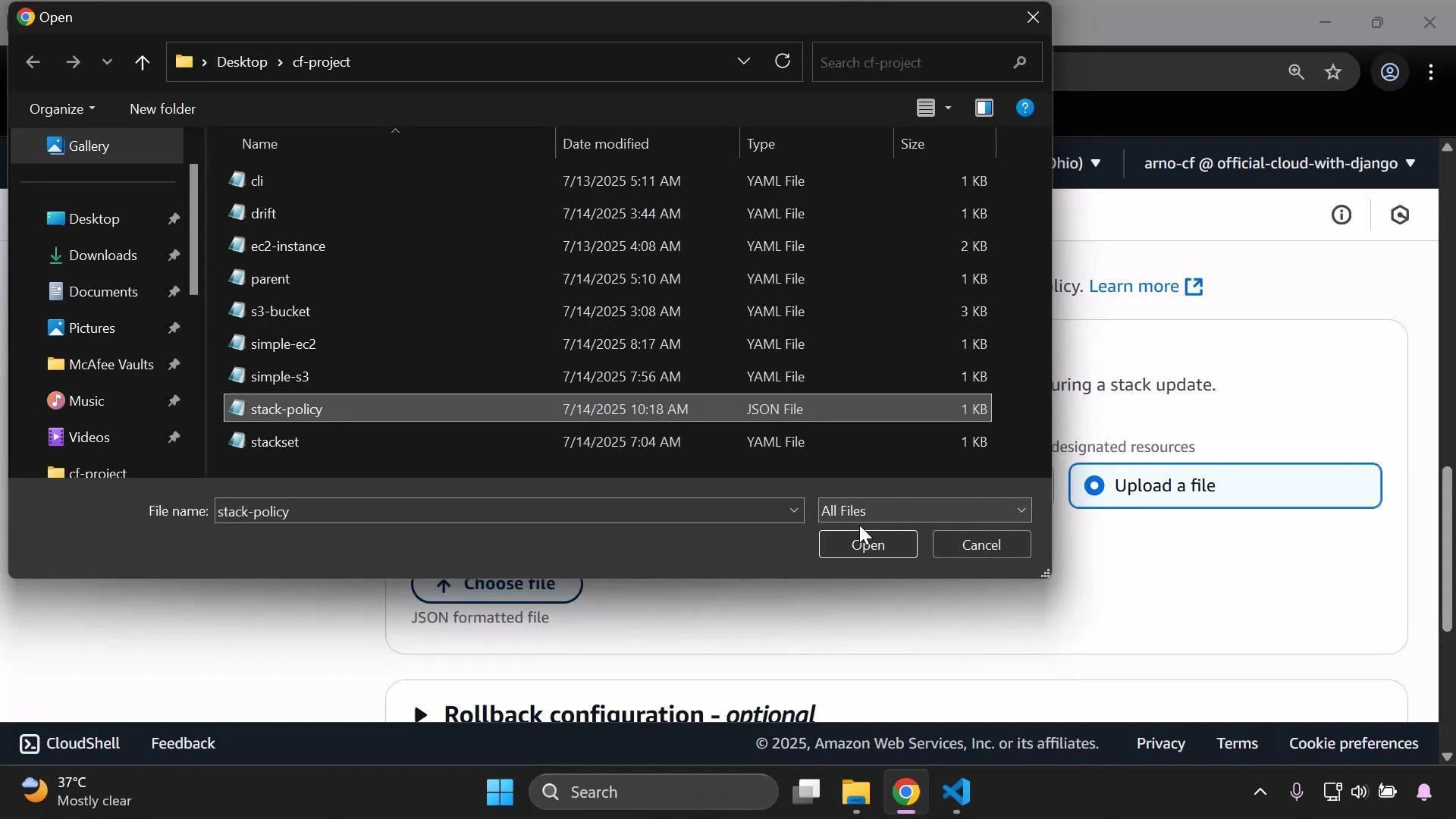
- In the CloudFormation console, begin creating your stack using the template above.
- When prompted for a stack policy, upload the
stack-policy.jsonfile you created.
MyBucket. For example, add an additional Tag and submit a stack update:
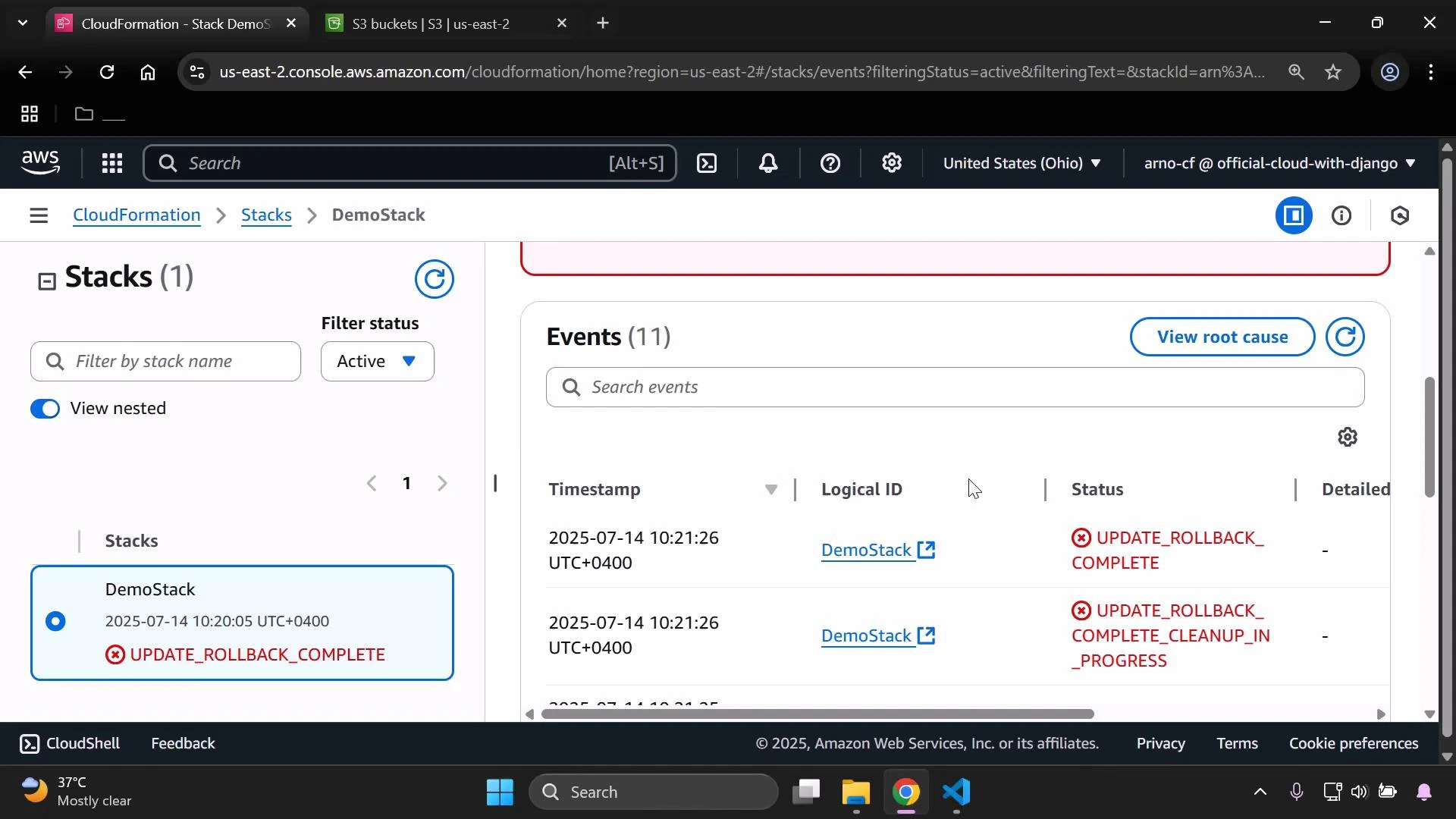
MyBucket, CloudFormation will block the update, report UPDATE_FAILED for that resource, and the stack will roll back the attempted change.
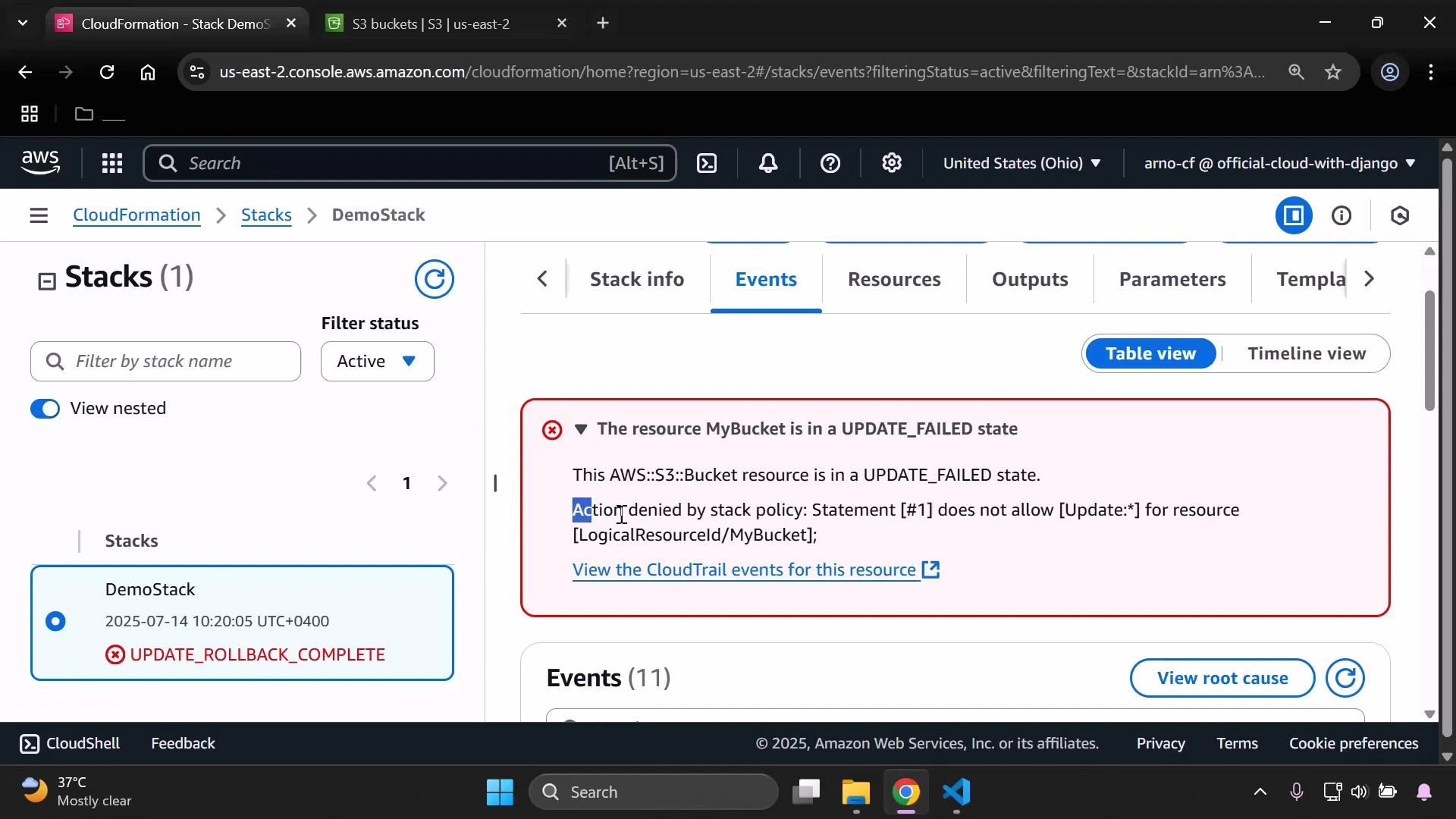
- Stack policies protect resources by logical ID from specific actions (for example, updates).
- In this walkthrough, the policy denied all updates to the logical resource
MyBucket, preventing the Tag modification and causing an update rollback. - Use stack policies when you need to prevent accidental or unauthorized changes to critical resources in a CloudFormation stack.
When you delete a stack, CloudFormation removes the stack’s resources depending on their DeletionPolicy. If a resource is set to be deleted, removing the stack will also delete that resource (for example, an S3 bucket). Make sure you no longer need the data before deleting the stack.