In this demo you’ll learn how to create an IAM role and instance profile so an EC2 instance running cfn-init can retrieve CloudFormation stack metadata and configuration. This is a short, practical guide covering why the role is needed, what permissions to attach, and how to create the role using the AWS Console. Why this mattersDocumentation Index
Fetch the complete documentation index at: https://notes.kodekloud.com/llms.txt
Use this file to discover all available pages before exploring further.
- cfn-init runs on the EC2 instance and must call CloudFormation APIs to fetch metadata and configuration.
- EC2 instances cannot store IAM credentials directly. Instead, an instance assumes an IAM role that is associated with the instance through an instance profile.
- Without the correct IAM role/instance profile, cfn-init will not be able to retrieve configuration data and therefore cannot install or configure software as defined in your CloudFormation template.
- An IAM role trusted by the EC2 service (ec2.amazonaws.com).
- A permissions policy allowing read access to CloudFormation stack metadata (AWSCloudFormationReadOnlyAccess).
- (Console note) The AWS Console creates a matching instance profile for the role automatically. If you use CloudFormation or the CLI to create your role, you might need to create an AWS::IAM::InstanceProfile resource explicitly.
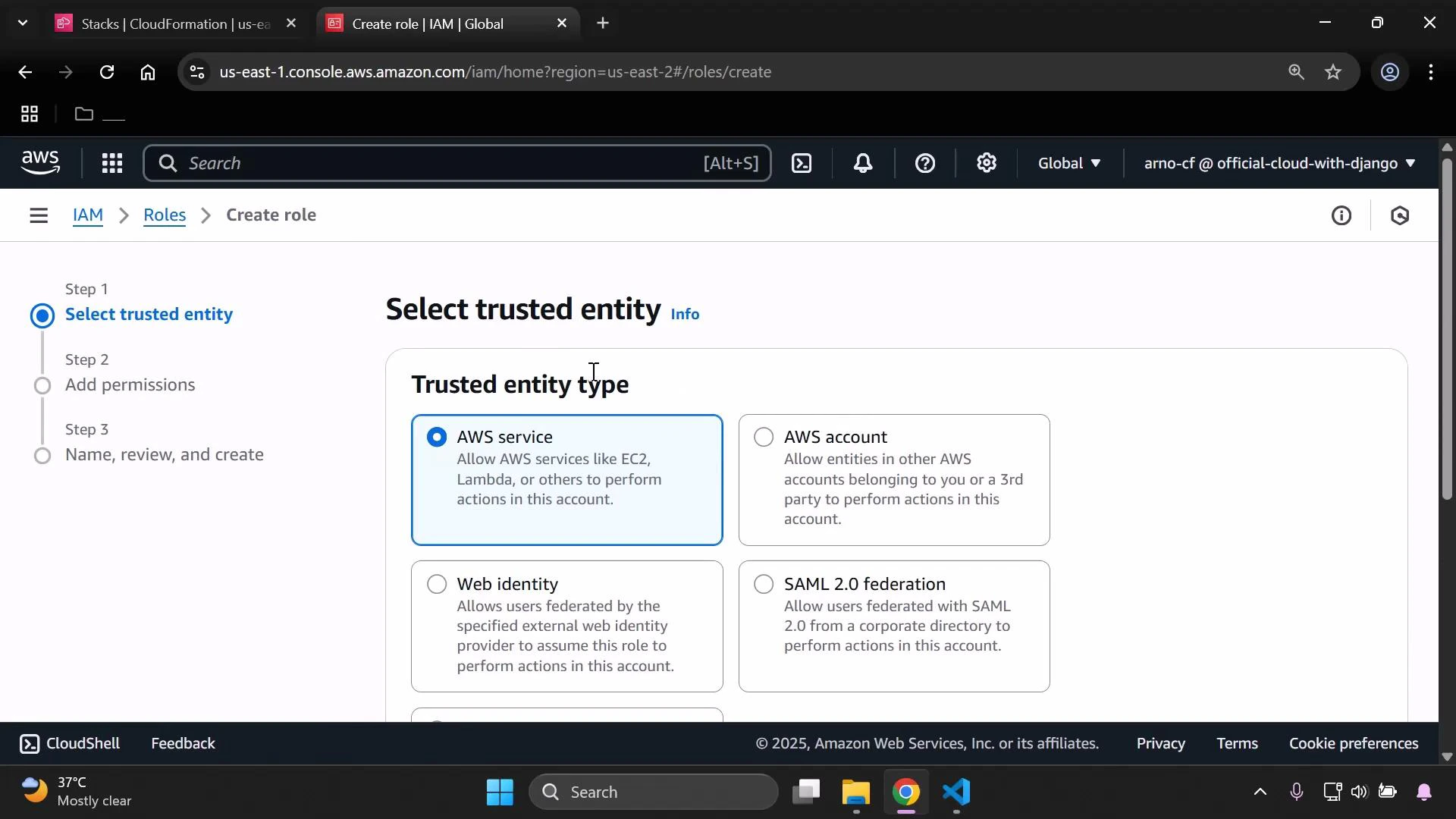
- Open the IAM console, choose Roles → Create role. Select the trusted entity type “AWS service” and choose EC2 as the use case.
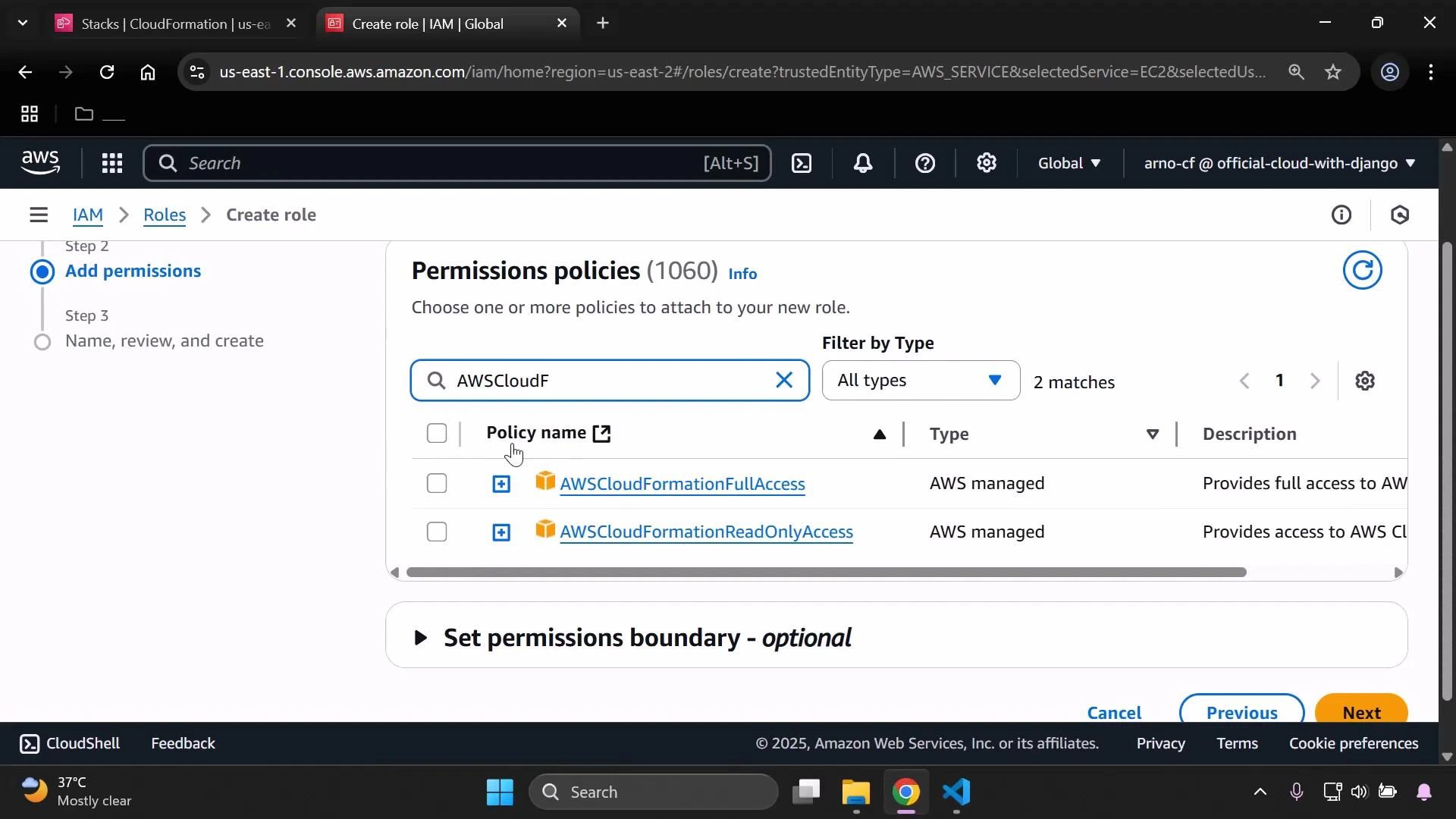
- Click Next to open the Permissions step. For cfn-init’s typical needs, attach the managed policy AWSCloudFormationReadOnlyAccess so the instance can read stack metadata from CloudFormation.
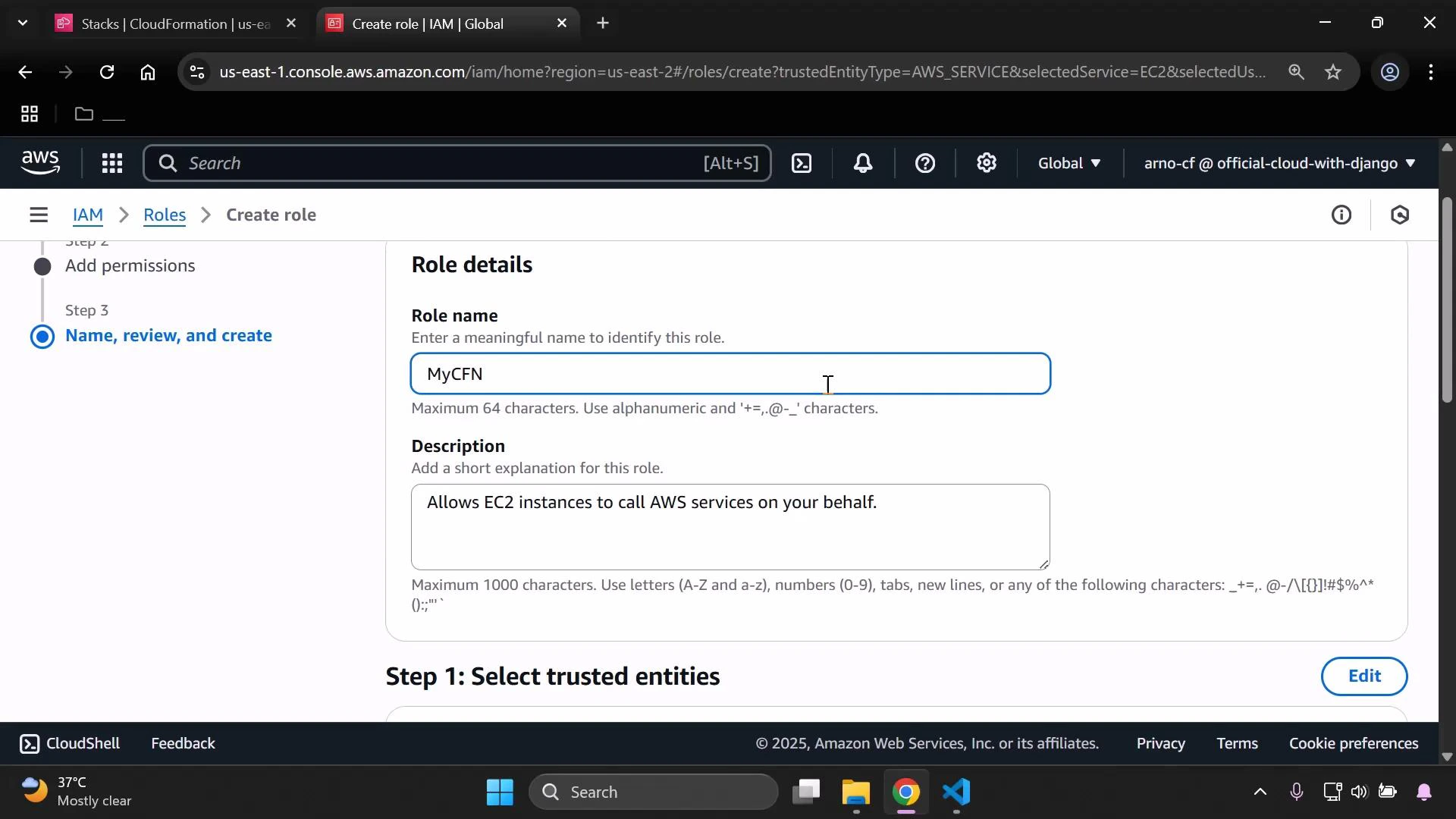
- Click Next, then give the role a descriptive name (for example: MyCFN or MyCFNInstanceRole) and an optional description. Click Create role.
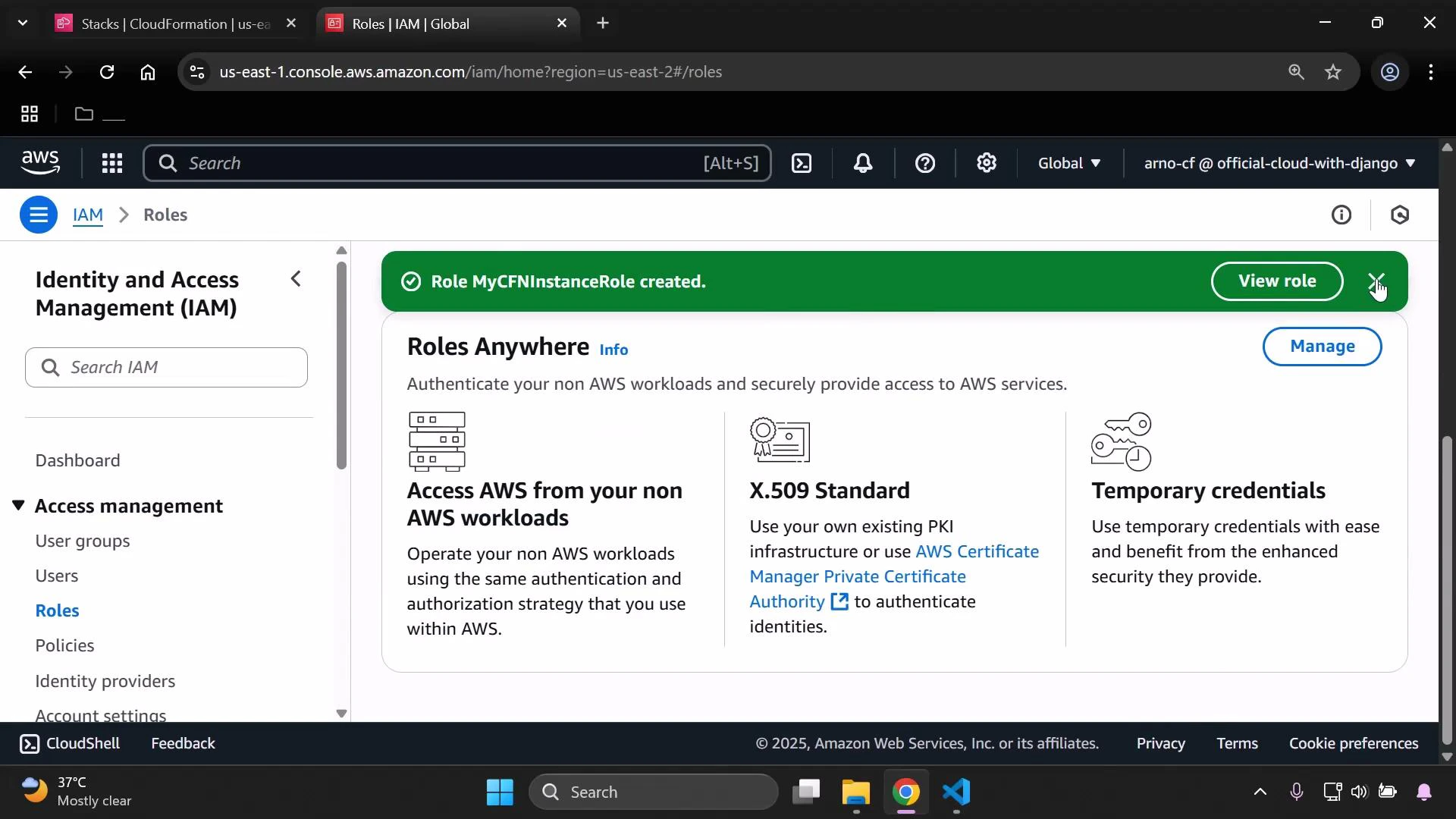
- After creation, verify the success message and note the exact role name. You will reference this role when attaching it to EC2 instances (via the console, API, or CloudFormation).
| Item | Purpose | Example |
|---|---|---|
| Trusted entity | Allows EC2 to assume the role | ec2.amazonaws.com |
| Managed policy | Grants CloudFormation read access | AWSCloudFormationReadOnlyAccess |
| Role name | Reference when attaching to instance | MyCFNInstanceRole |
| Instance profile | Allows EC2 to use the role | Created automatically by Console |
The AWS Console will create an instance profile with the same name as the role automatically when you create a role for EC2. If you create roles programmatically or with CloudFormation, you may need to create an AWS::IAM::InstanceProfile resource and associate the role explicitly.
AWSCloudFormationReadOnlyAccess allows cfn-init to read CloudFormation metadata. If your cfn-init configuration needs to download artifacts from S3 or access other AWS services, add the appropriate S3 or service-specific permissions to the role (least-privilege principle recommended).