Welcome to the continuation of conditional, resource-based creation with AWS CloudFormation. This lesson walks through a compact CloudFormation template that:Documentation Index
Fetch the complete documentation index at: https://notes.kodekloud.com/llms.txt
Use this file to discover all available pages before exploring further.
- selects environment-specific metadata from a mapping,
- evaluates an environment-based Condition, and
- either configures or creates resources based on that Condition.
Template overview
Below are the template sections we use in this demo: Mappings, Parameters, Conditions, and Resources. The mapping links developer names to a Profession (“Field”) and an environment (“Env”). The InputDeveloperName parameter selects which mapping entry to use.Evaluate environment with a Condition
We check whether the selected developer maps to a production environment by comparing the mapped Env value to “Production”:Conditional resources and properties
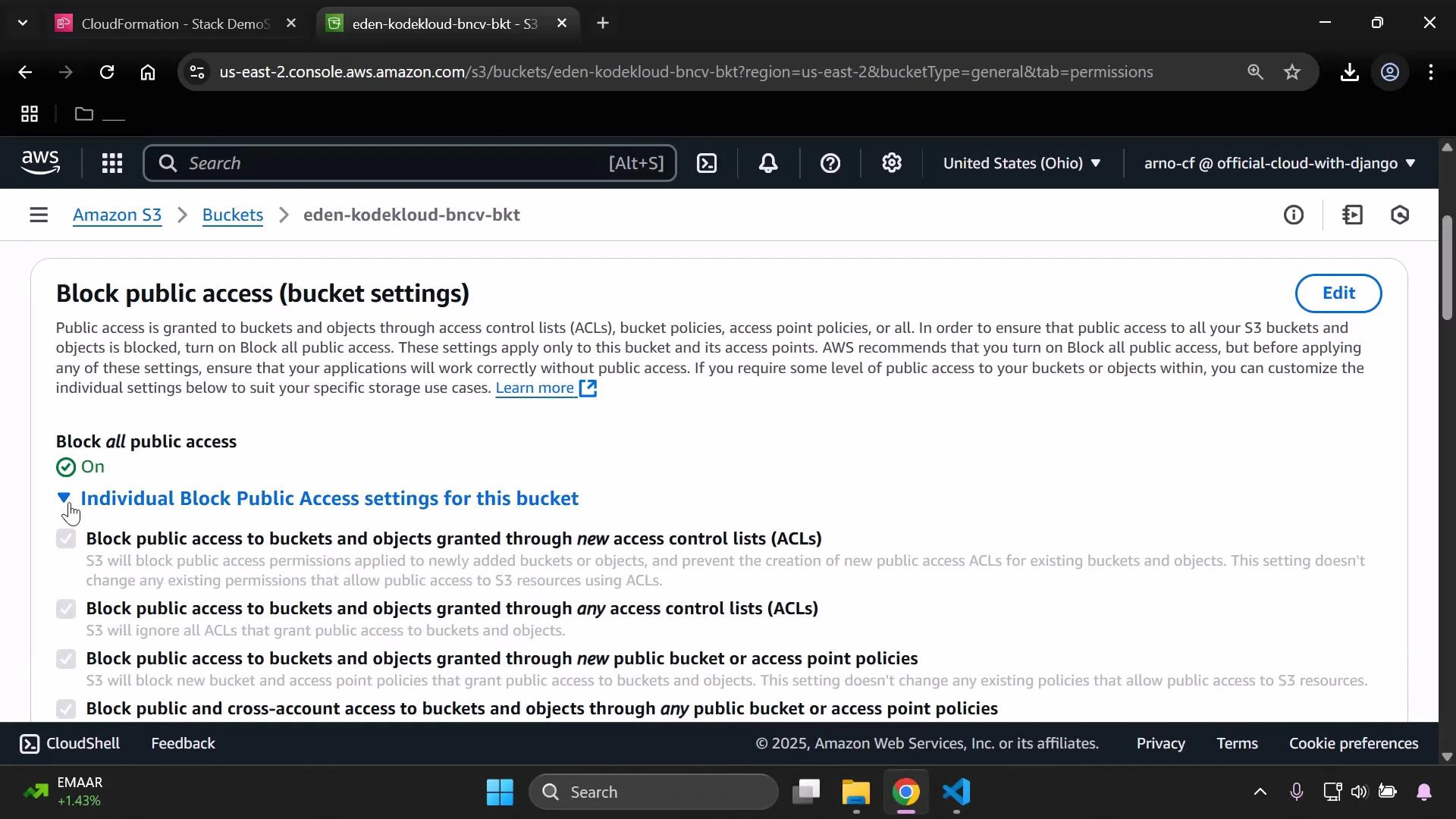
This template demonstrates two conditional behaviors:- Property-level conditional selection using !If for PublicAccessBlockConfiguration on the S3 bucket.
- Resource-level conditional creation using Condition on the S3 bucket policy, so the policy exists only when IsProd is true.
Note: The Condition on MyPublicReadPolicy prevents CloudFormation from creating the bucket policy unless IsProd is true. The PublicAccessBlockConfiguration uses !If to apply one of two JSON-style configuration objects; the false branch applies the more restrictive default for non-production environments.
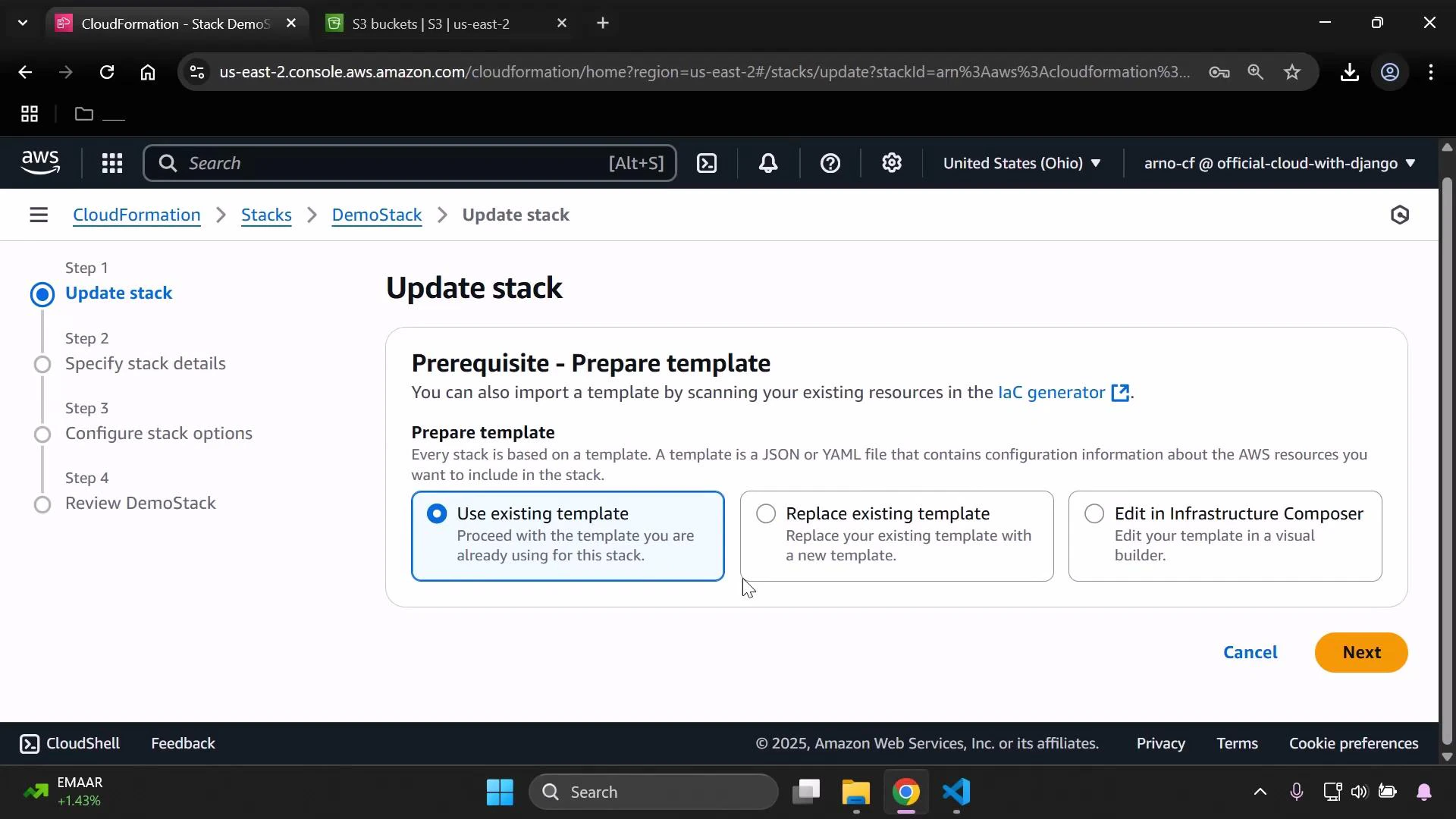
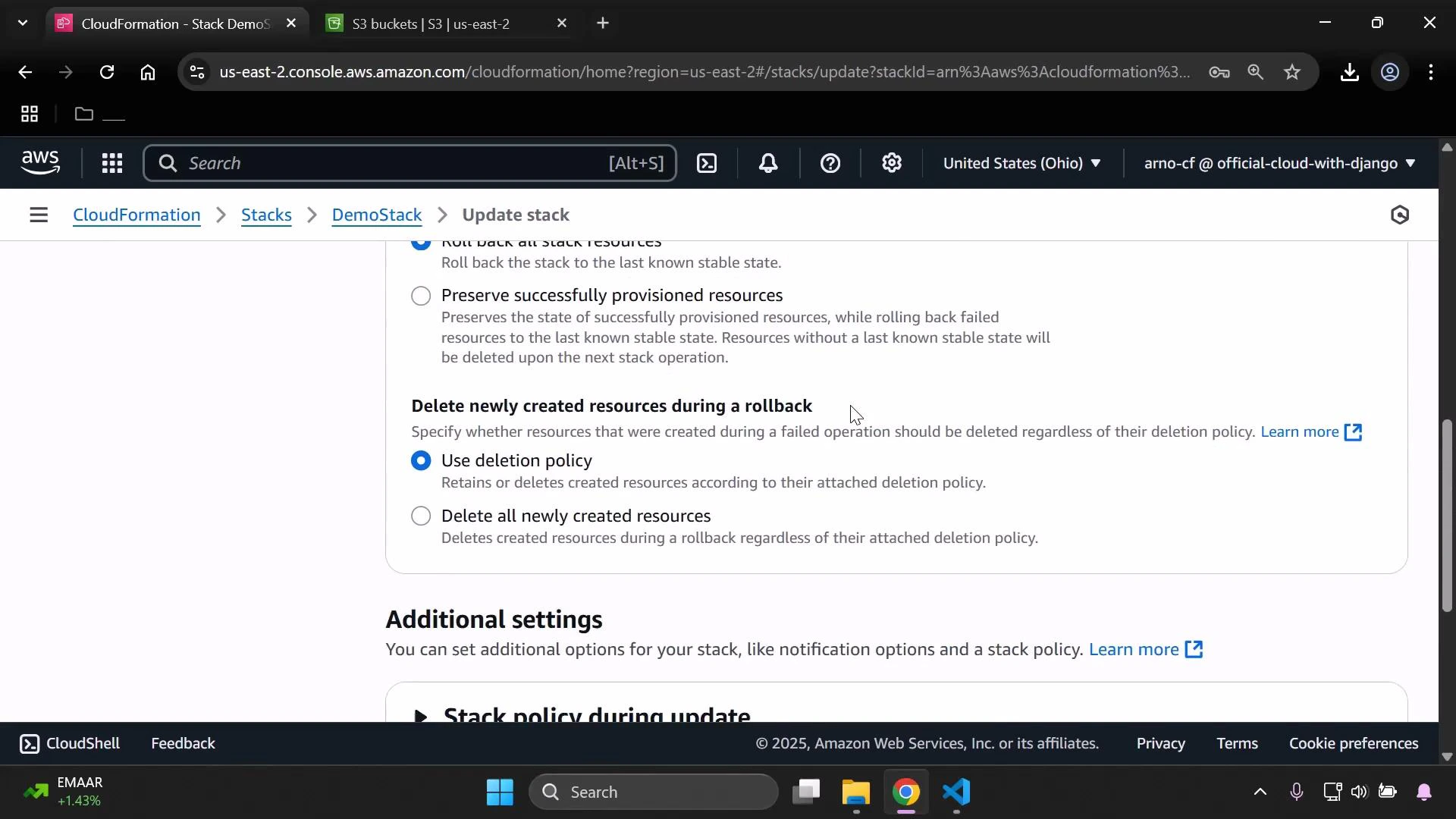
Update the stack in the CloudFormation console
To test the conditional behavior, update the existing stack and change the InputDeveloperName parameter from “Alice” (Production) to “Arno” (Testing/development). Begin by selecting the stack and choosing Update stack.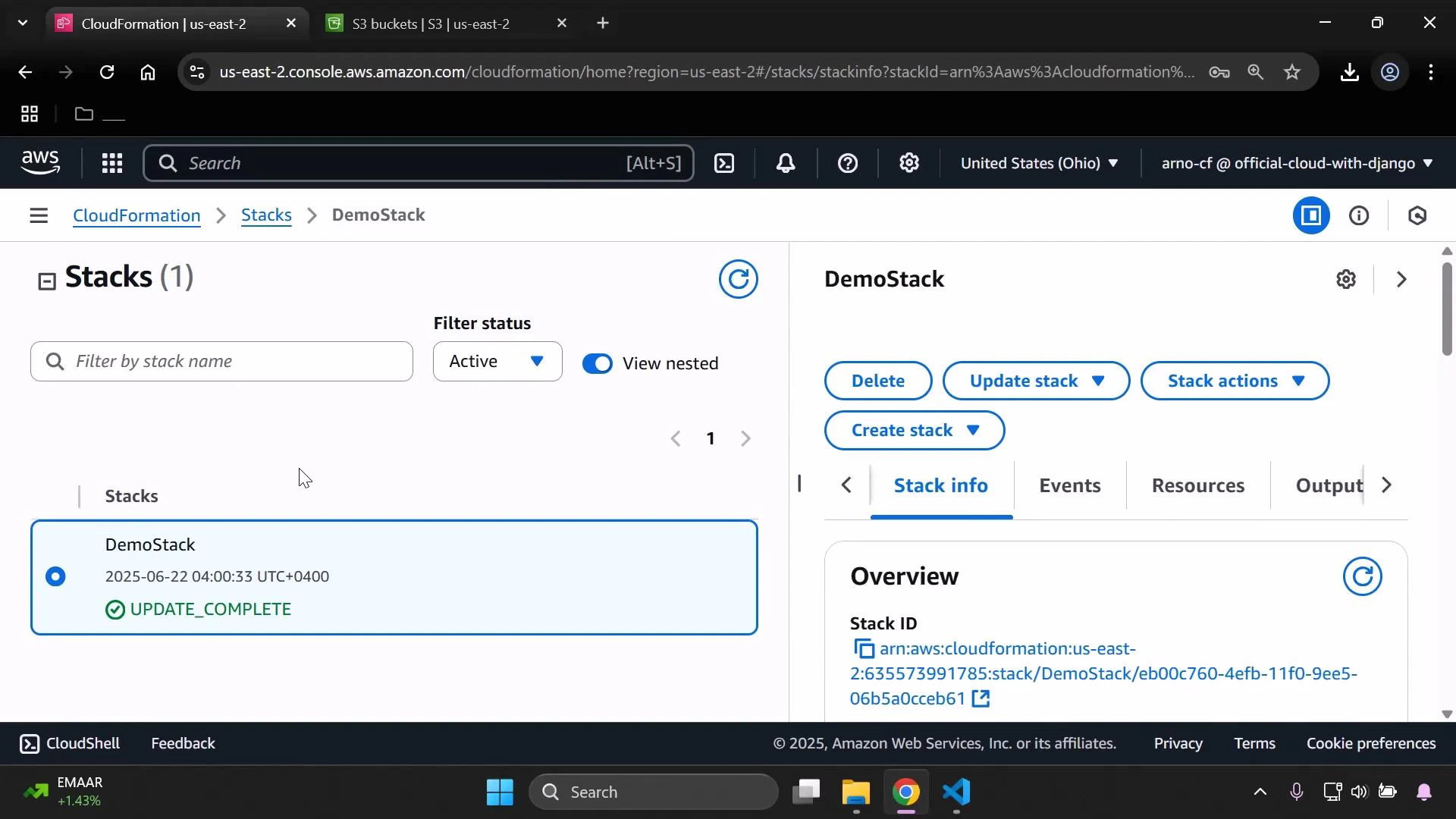
Validate the environment-specific results
After the stack update finishes, open the bucket in the S3 console and confirm the tags. They should reflect the mapping for “Arno”: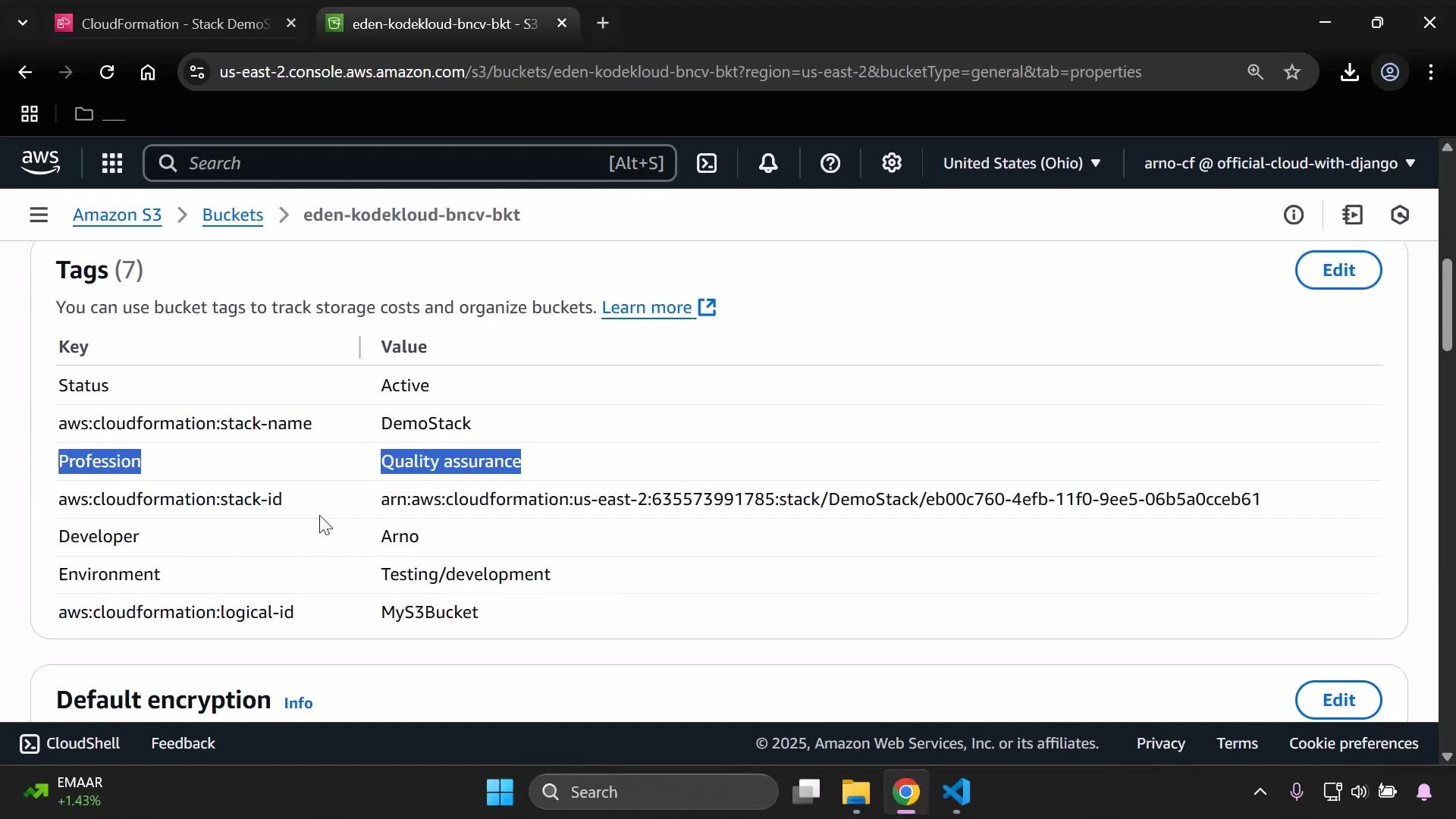
Quick reference: behavior matrix
| IsProd value | PublicAccessBlockConfiguration | MyPublicReadPolicy created? | Expected anonymous GET result |
|---|---|---|---|
| true | Non-restrictive (public allowed) | Yes | 200 (if objects are public) |
| false | Restrictive (all public blocked) | No | AccessDenied |
Summary and best practices
This example demonstrates a common, reusable pattern in CloudFormation:- Select environment-specific metadata via FindInMap.
- Evaluate environment identity with a Condition.
- Use !If to choose property-level configuration.
- Use Condition at the resource level to control creation of sensitive resources (like a public bucket policy).
- Keep mappings and allowed parameter values in sync to avoid misconfiguration.
- Use Conditions to avoid creating risky resources in non-production accounts.
- Use tags to record the chosen environment and owner metadata for easier auditing.
Links and references
- AWS CloudFormation Conditions documentation
- AWS S3 Block Public Access documentation
- AWS::S3::BucketPolicy documentation