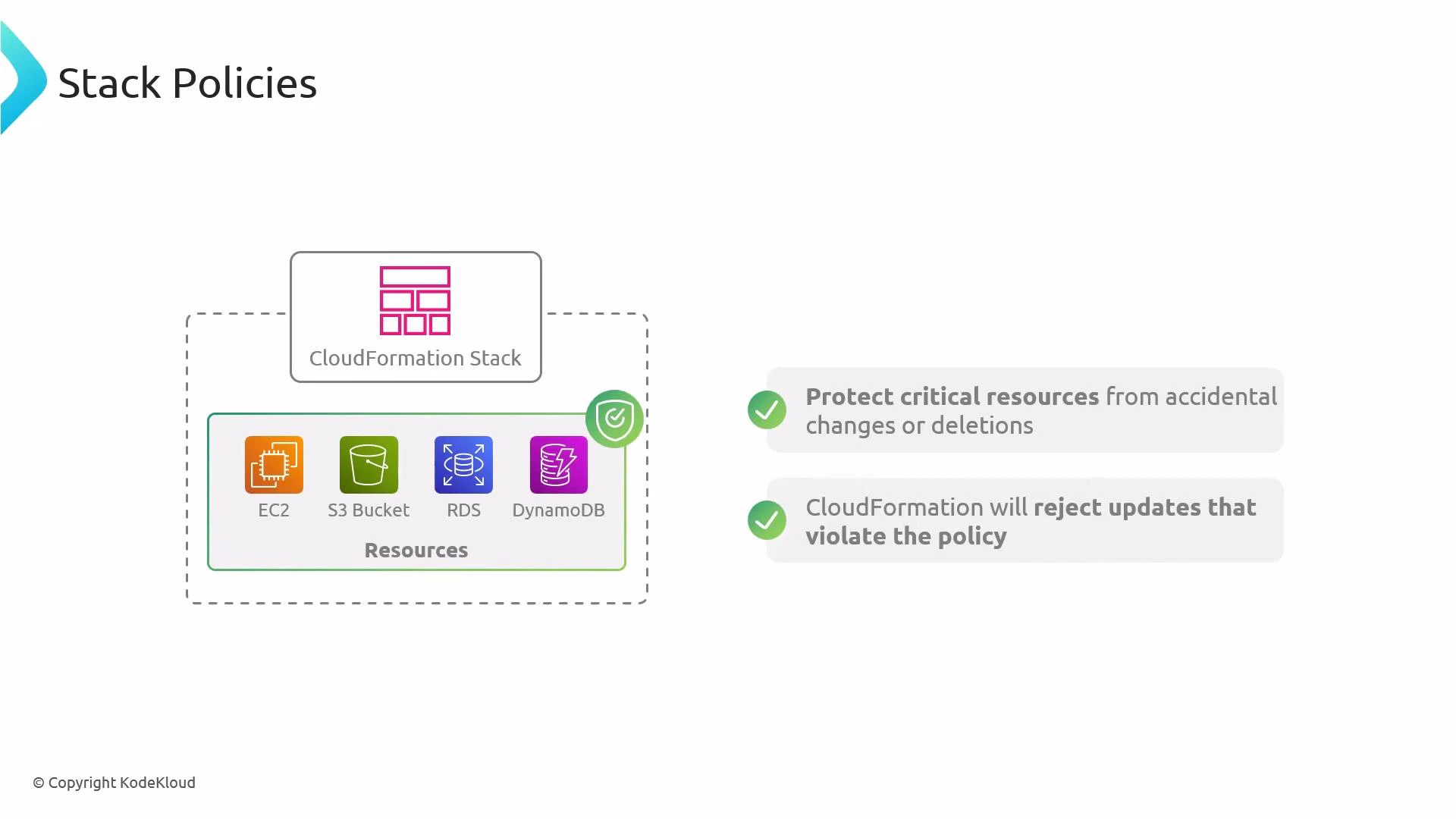
Hi everyone — welcome to this lesson on stack policies for AWS CloudFormation. In this guide you’ll learn what stack policies are, how they protect CloudFormation resources during updates, and how to apply them using the AWS CLI. Stack policies are an important tool to prevent accidental configuration changes to critical resources such as S3 buckets, EC2 instances, RDS databases, or DynamoDB tables. Stack policies are rules that control which resources in an AWS CloudFormation stack can be modified during stack update operations. If an update would change a protected resource in a way that violates the stack policy, CloudFormation rejects that update.Documentation Index
Fetch the complete documentation index at: https://notes.kodekloud.com/llms.txt
Use this file to discover all available pages before exploring further.
| Behavior | Details |
|---|---|
| Evaluation time | Stack policies are evaluated only during stack update operations (for example, UpdateStack and when executing change sets). |
| Allowed vs Denied | A stack policy explicitly allows or denies updates to specified logical resources. Any update that attempts to change a denied resource is rejected. |
| Deletion vs Update | Stack policies control updates, not deletions at the resource level. Use a resource’s DeletionPolicy attribute or other safeguards to protect against deletions. |
| Attachment options | You can attach a stack policy when creating or updating a stack, or set it afterward using the AWS CLI or the CloudFormation console. |
- Prevent accidental configuration changes to critical resources (for example, locking down an S3 bucket or a production RDS instance).
- Enforce permissions during automated deployment pipelines so certain stacks cannot be altered by routine updates.
- Combine with change sets to preview and validate whether proposed changes will be blocked.
- This example denies all update actions on the logical resource
MyS3Bucket, while leaving other resources updatable:
- To apply the above policy to a stack:
- To retrieve the current stack policy for a stack:
| Action | Command |
|---|---|
| Set a stack policy | aws cloudformation set-stack-policy --stack-name my-stack --stack-policy-body file://stack-policy.json |
| Get a stack policy | aws cloudformation get-stack-policy --stack-name my-stack |
| Use change sets | See AWS CloudFormation change sets documentation |
- Limit Deny rules to only the truly critical resources. Overly broad Deny rules can block legitimate and necessary updates.
- Use change sets to preview proposed updates and confirm whether the stack policy will block any changes before applying them.
- Combine stack policies with resource-level DeletionPolicy attributes when you need both update and deletion protection.
- Keep stack policies versioned alongside your infrastructure-as-code to track intent and changes over time.
Use change sets and a CI/CD review step to validate changes against your stack policy before applying updates to production stacks. This reduces the risk of blocked deployments and accidental drift.
Stack policies are enforced only during stack update operations. They do not replace a resource’s DeletionPolicy — if you must prevent deletion, configure the resource’s DeletionPolicy or use other safeguards.
- AWS CloudFormation — Update stacks and change sets
- CloudFormation DeletionPolicy attribute
- AWS CLI — cloudformation set-stack-policy
- Kubernetes Documentation (related infrastructure best practices)