This demo shows how to store an AMI ID in AWS Systems Manager (SSM) Parameter Store and reference it from an AWS CloudFormation template so an EC2 instance uses the value at stack creation. You will:Documentation Index
Fetch the complete documentation index at: https://notes.kodekloud.com/llms.txt
Use this file to discover all available pages before exploring further.
- Create an SSM parameter to hold an AMI ID.
- Use the special CloudFormation parameter type to fetch and validate the AMI ID from Parameter Store.
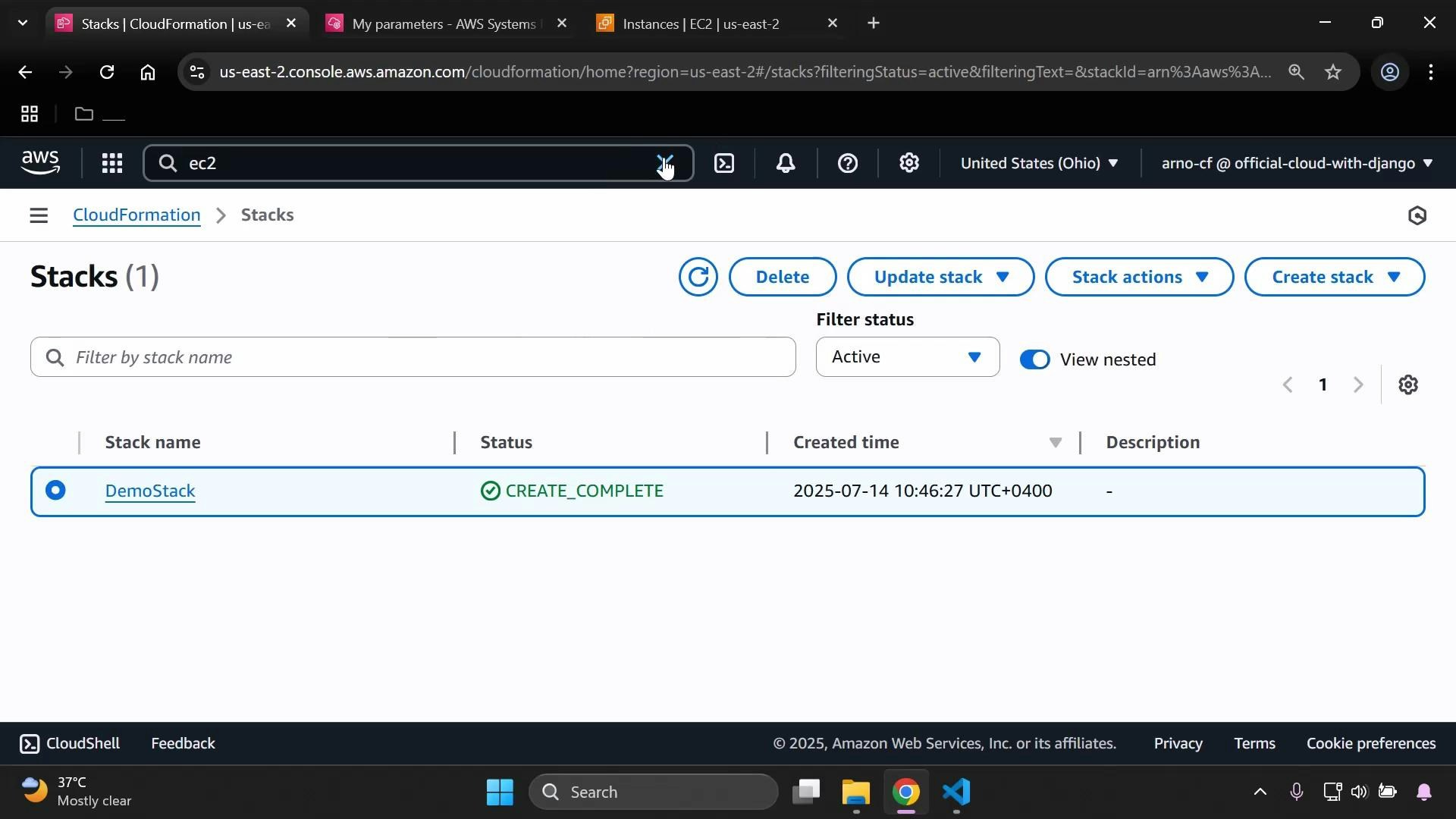
- Launch a CloudFormation stack that provisions an EC2 instance using the SSM-stored AMI.
1) Create an SSM parameter
Open the AWS Console and go to Systems Manager → Parameter Store (search “SSM” to find Systems Manager). Create a new parameter and choose a descriptive path name such as/myapp/dev/ami-id. Optionally provide a description.
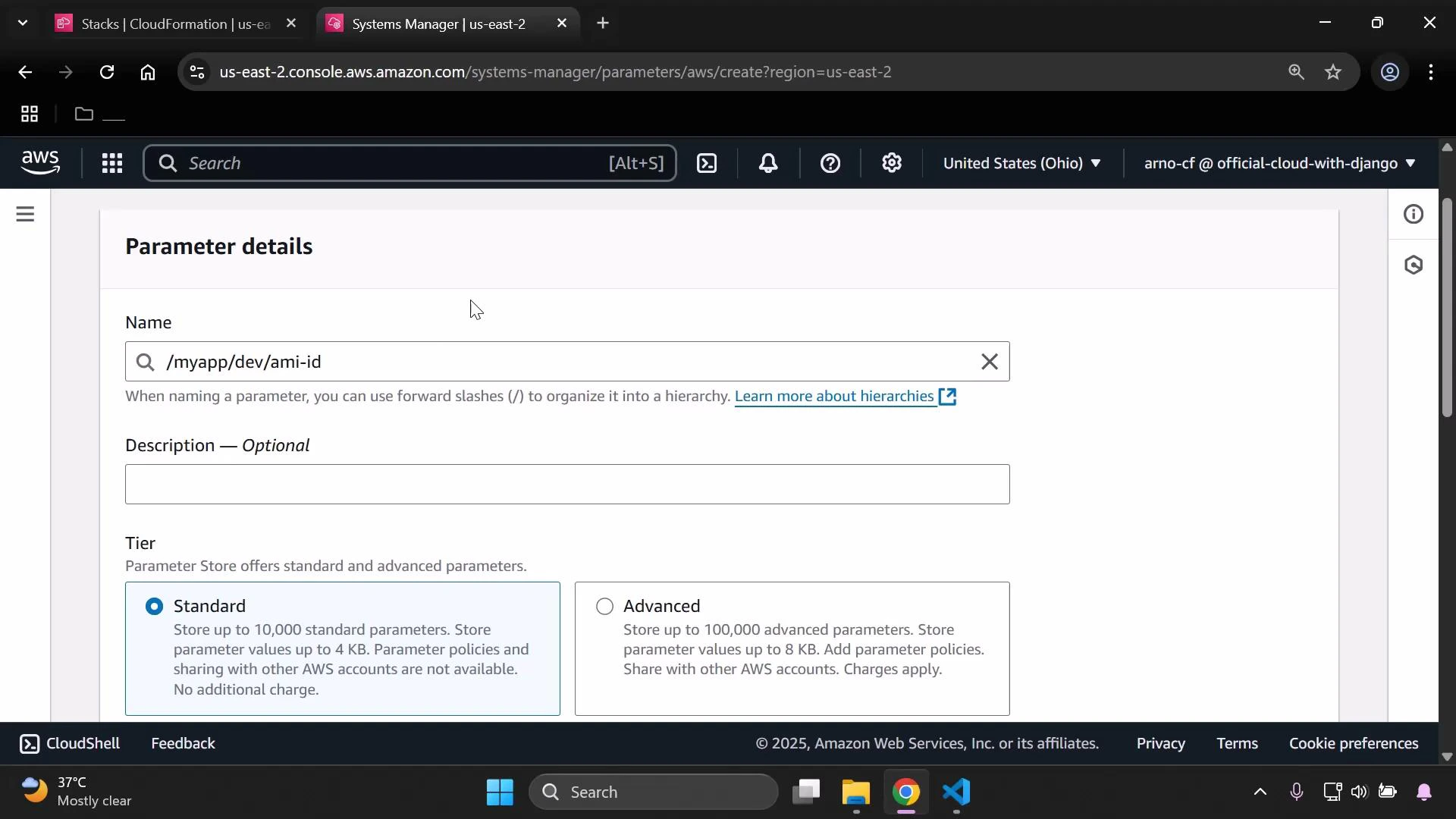
| Type | Use Case | Notes |
|---|---|---|
| String | Single configuration value | Simple, unencrypted text |
| StringList | Comma-separated list | Useful for storing lists such as subnets |
| SecureString | Secrets or credentials | Encrypted with KMS; recommended for secrets |
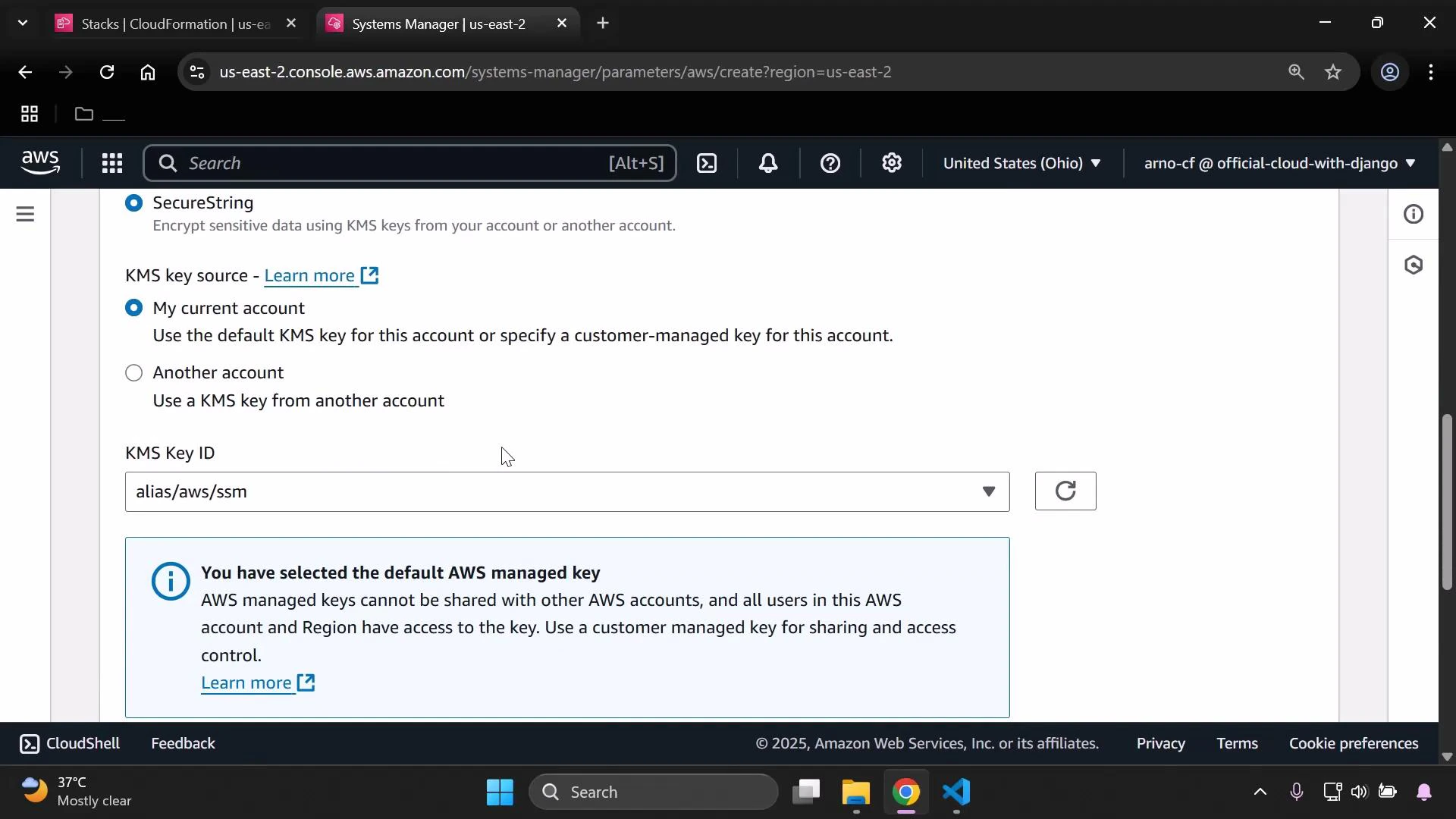
SecureString is recommended for secrets. If you use SecureString, make sure the principal that creates or deploys the stack (for example, CloudFormation’s service role or the IAM user) has
kms:Decrypt permissions on the KMS key used to encrypt the parameter.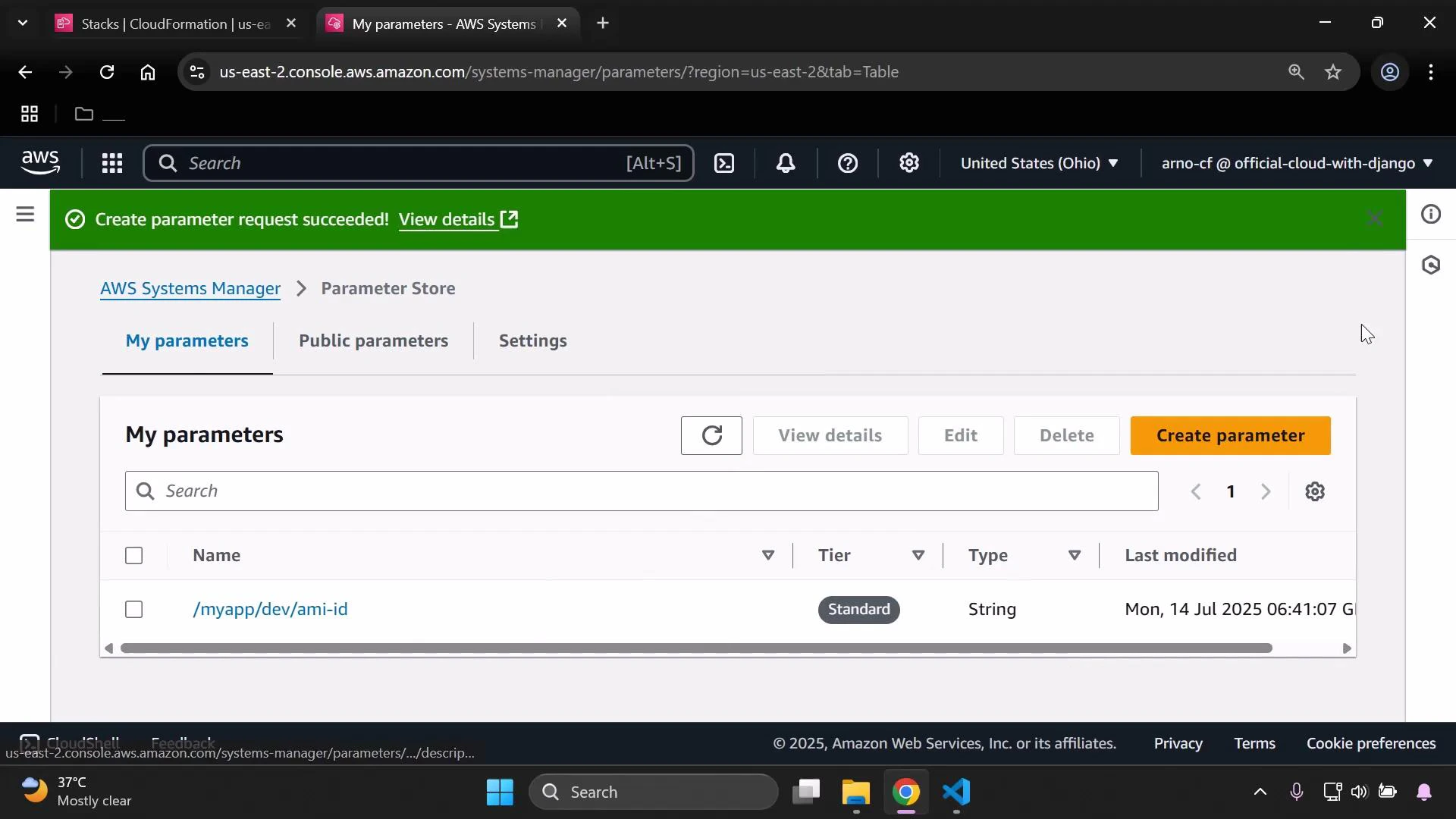
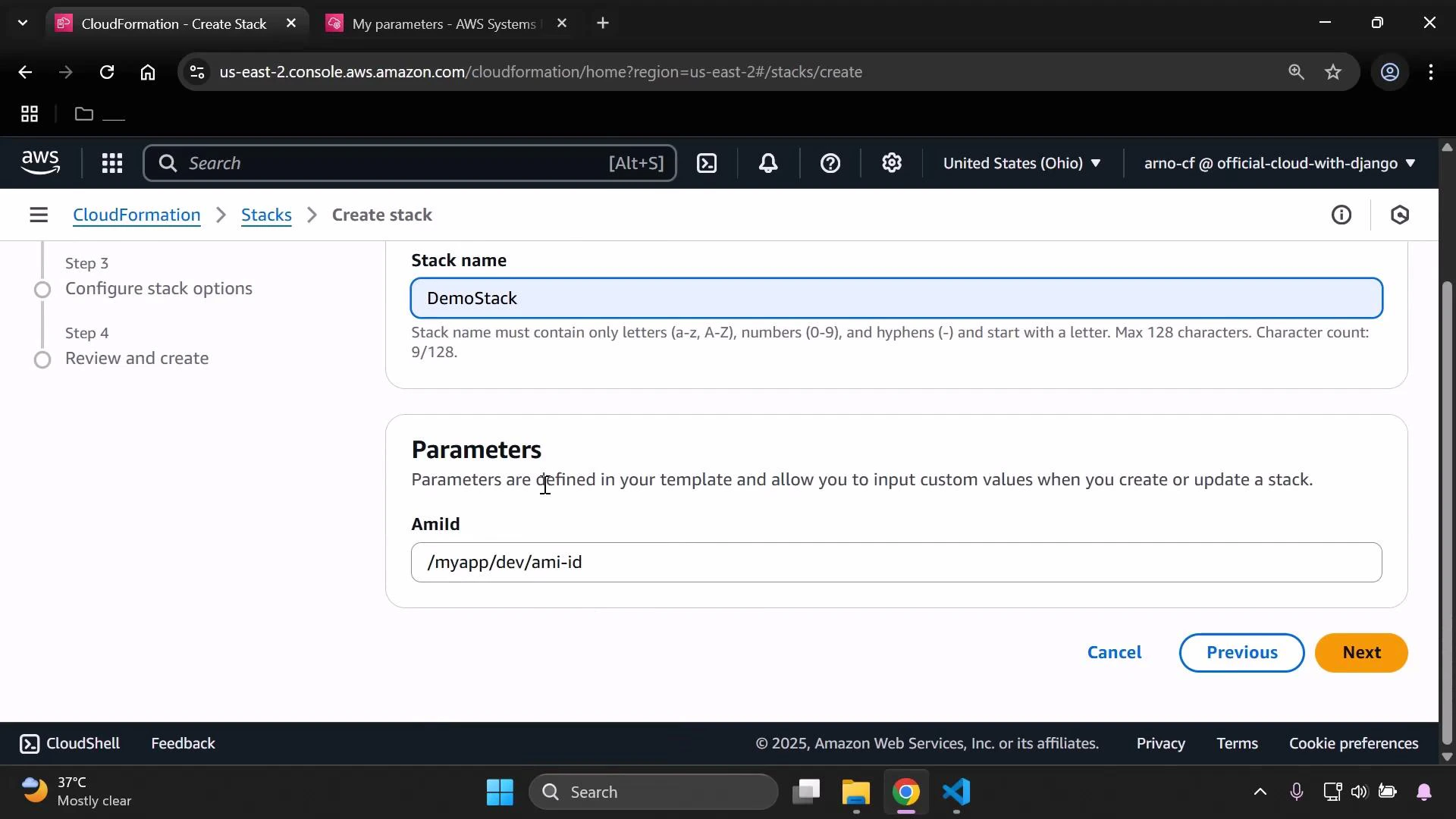
2) Reference the SSM parameter from CloudFormation
CloudFormation supports SSM-backed parameters using a special parameter Type that both retrieves the SSM value and validates its format. For AMI IDs use: Type: AWS::SSM::Parameter::Value<AWS::EC2::Image::Id> Save the example template below asssm.yaml and upload it when creating the stack. The template demonstrates a simple EC2 instance that uses the SSM parameter for ImageId.
- The parameter
AmiIdis declared with CloudFormation typeAWS::SSM::Parameter::Value<AWS::EC2::Image::Id>, so CloudFormation will fetch the value from SSM Parameter Store and validate it as an EC2 AMI ID. Defaultpoints to the Parameter Store path/myapp/dev/ami-id. If the stack creator does not override this parameter, CloudFormation uses that SSM parameter.- The EC2 instance property
ImageIdreferences the parameter with!Ref AmiId, applying the fetched AMI to the instance.
3) Verify resources
After stack creation starts, verify the EC2 instance is launched in the expected region and that it enters the Running state.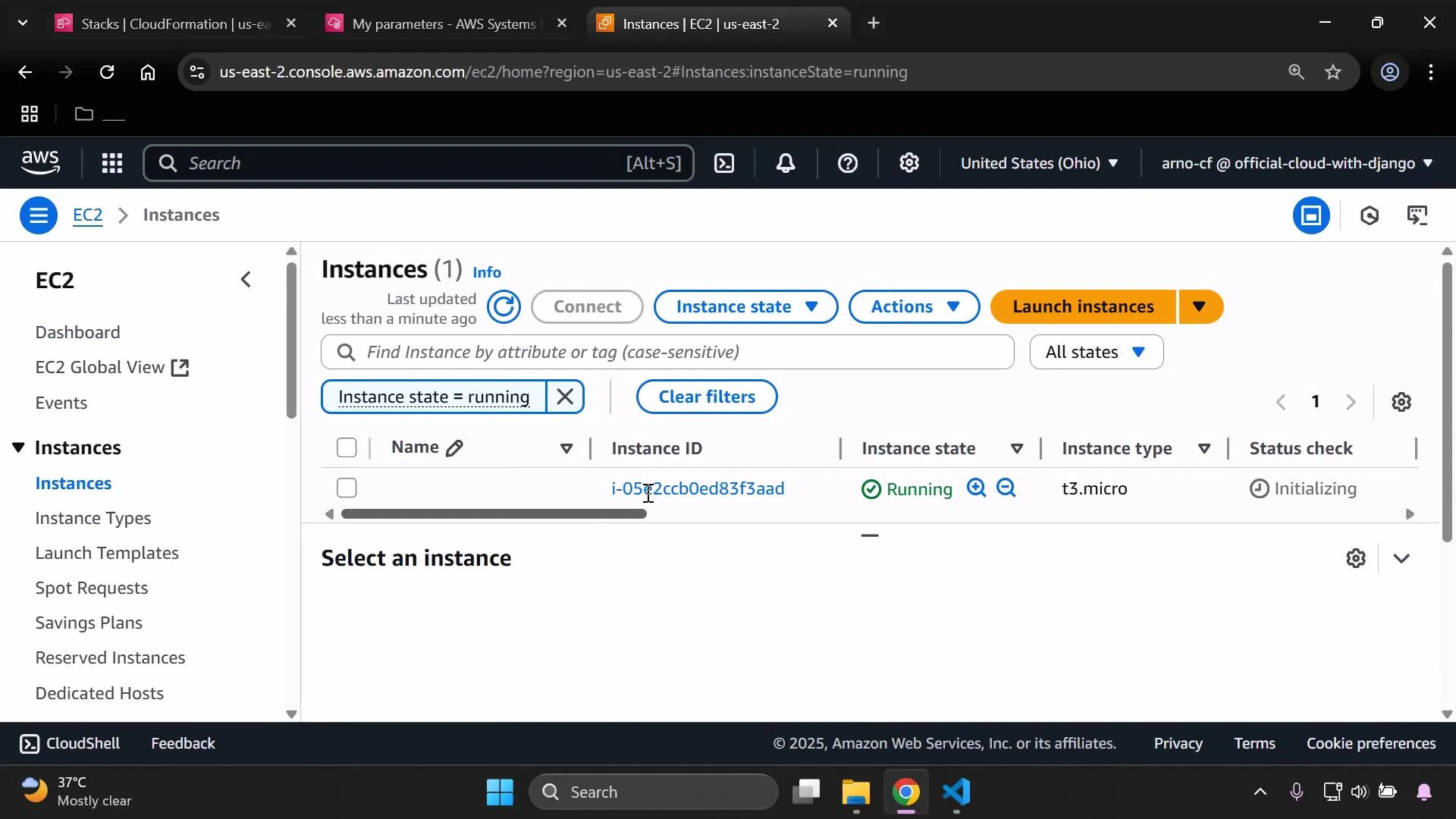
Cleanup
- Delete the CloudFormation stack to remove provisioned resources (this terminates the EC2 instance).
- If the SSM parameter is no longer needed, delete it from Parameter Store.
If you used SecureString, ensure the principals performing read, update, or deletion operations have the necessary KMS permissions (
kms:Decrypt and kms:DescribeKey). Deleting or rotating keys without proper permissions can make SecureString values unrecoverable.