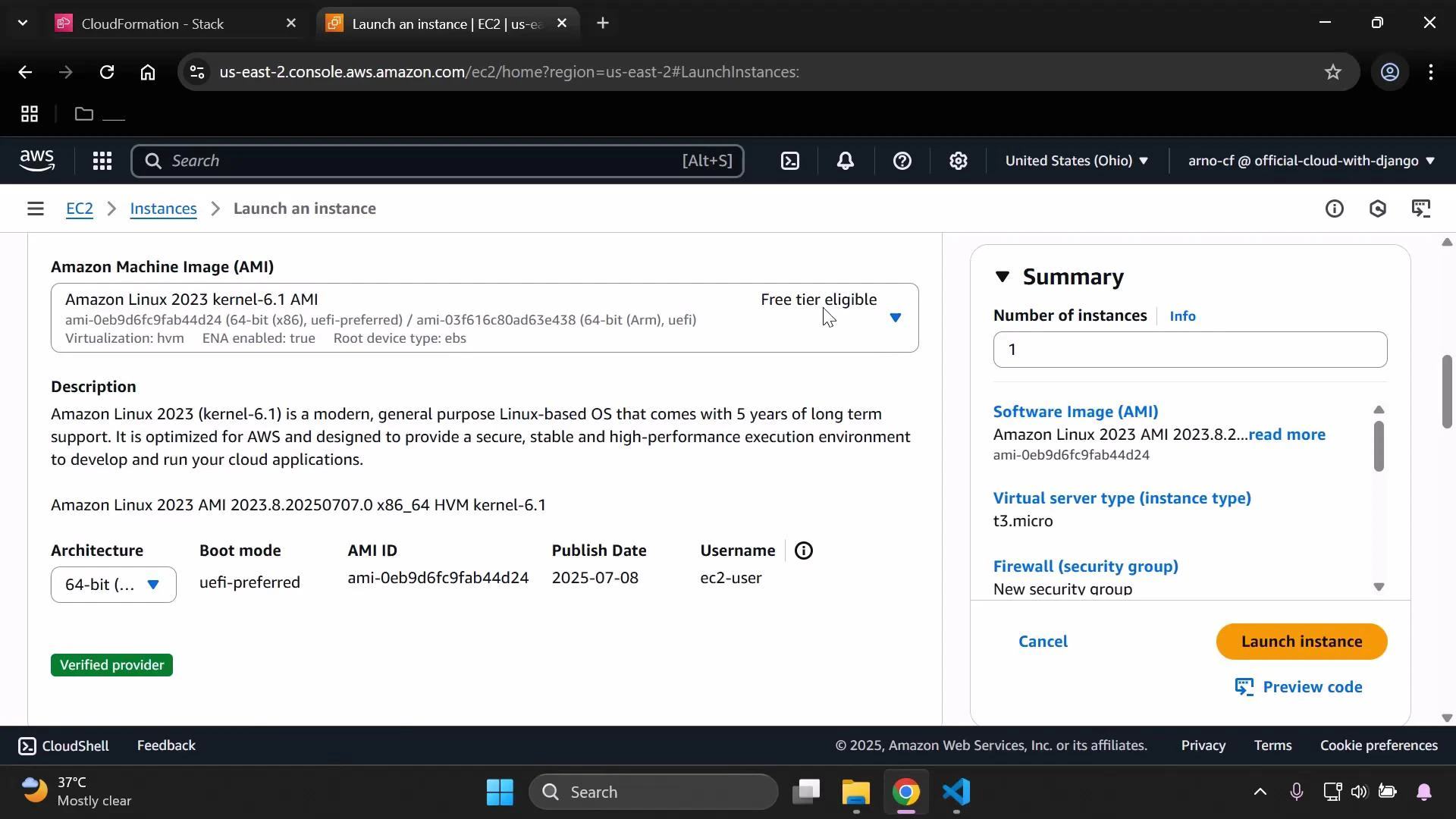
In this lesson you’ll create a minimal AWS CloudFormation template that provisions a single EC2 instance. The goal is to demonstrate the bare minimum properties required to launch an instance, validate the template locally, and deploy it through the CloudFormation console. Before you start, open the EC2 console in the AWS region you want to use. AMI IDs are region-specific, so for reproducibility while following this lesson it’s easiest to use the same region shown in the screenshots because the AMI ID used below will only work in that region.Documentation Index
Fetch the complete documentation index at: https://notes.kodekloud.com/llms.txt
Use this file to discover all available pages before exploring further.
AMI IDs are unique per region. If you change regions, find and use the matching AMI ID for that region (use the EC2 AMIs page to search by name).
ec2-instance.yaml in your CloudFormation project (for example, open the project in Visual Studio Code).
If your project already contains other templates, you might have existing Mappings and Parameters. Below is a corrected, minimal example showing how Mappings and Parameters are structured. This example is optional and not required for the minimal EC2 template that follows:
- The top-level Resources block
- A logical resource name (here: MyInstance)
- Resource Type:
AWS::EC2::Instance - Required properties:
InstanceTypeandImageId
| Element | Purpose | Example |
|---|---|---|
| Resources | Container for all stack resources | Resources: |
| Logical ID | Template-local name for the resource | MyInstance: |
| Type | Resource type identifier | AWS::EC2::Instance |
| Properties | Resource properties (required and optional) | InstanceType, ImageId |
t3.micro EC2 instance using a specific AMI ID (example AMI ID shown in the screenshot). Replace the ImageId value with the correct AMI ID for the region you are using.
ec2-instance.yaml.
Validate the template locally (recommended) with cfn-lint. If you have cfn-lint installed, run:
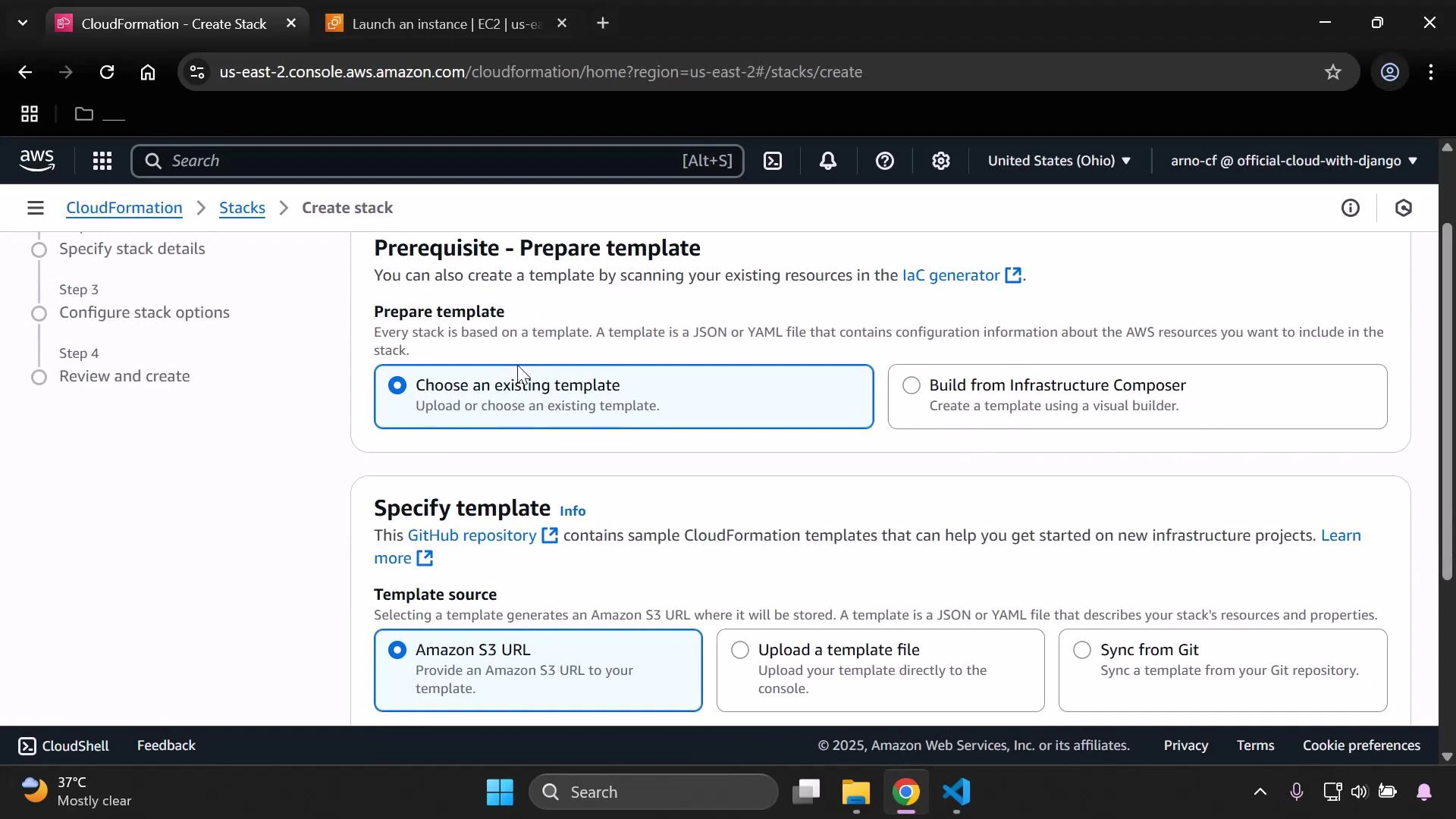
ec2-instance.yaml you just saved) and proceed through the stack creation steps.
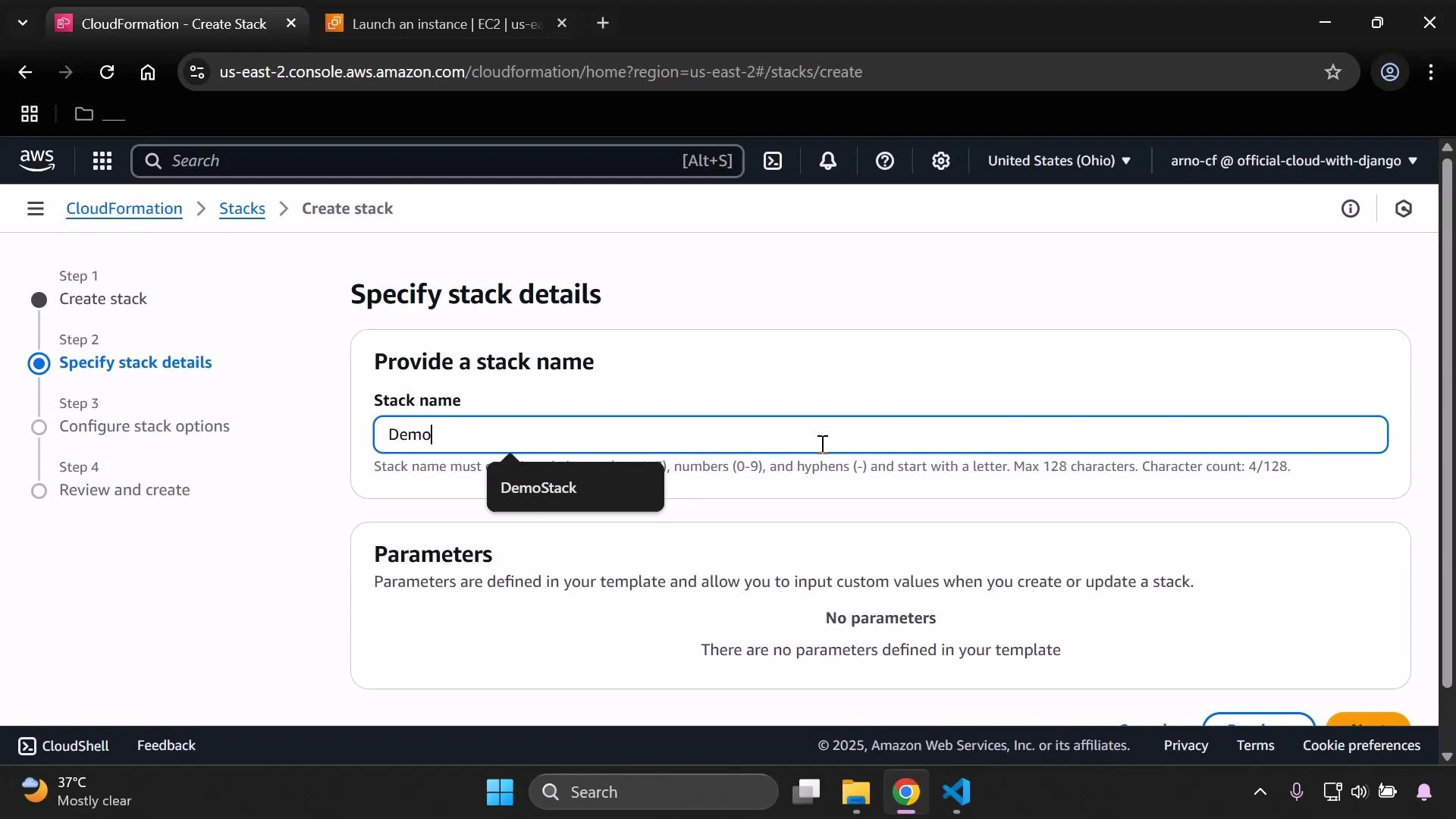
demo-stack) and continue with the default options. Because this minimal template does not define Parameters, the CloudFormation console will display “No parameters” on the Specify stack details step.
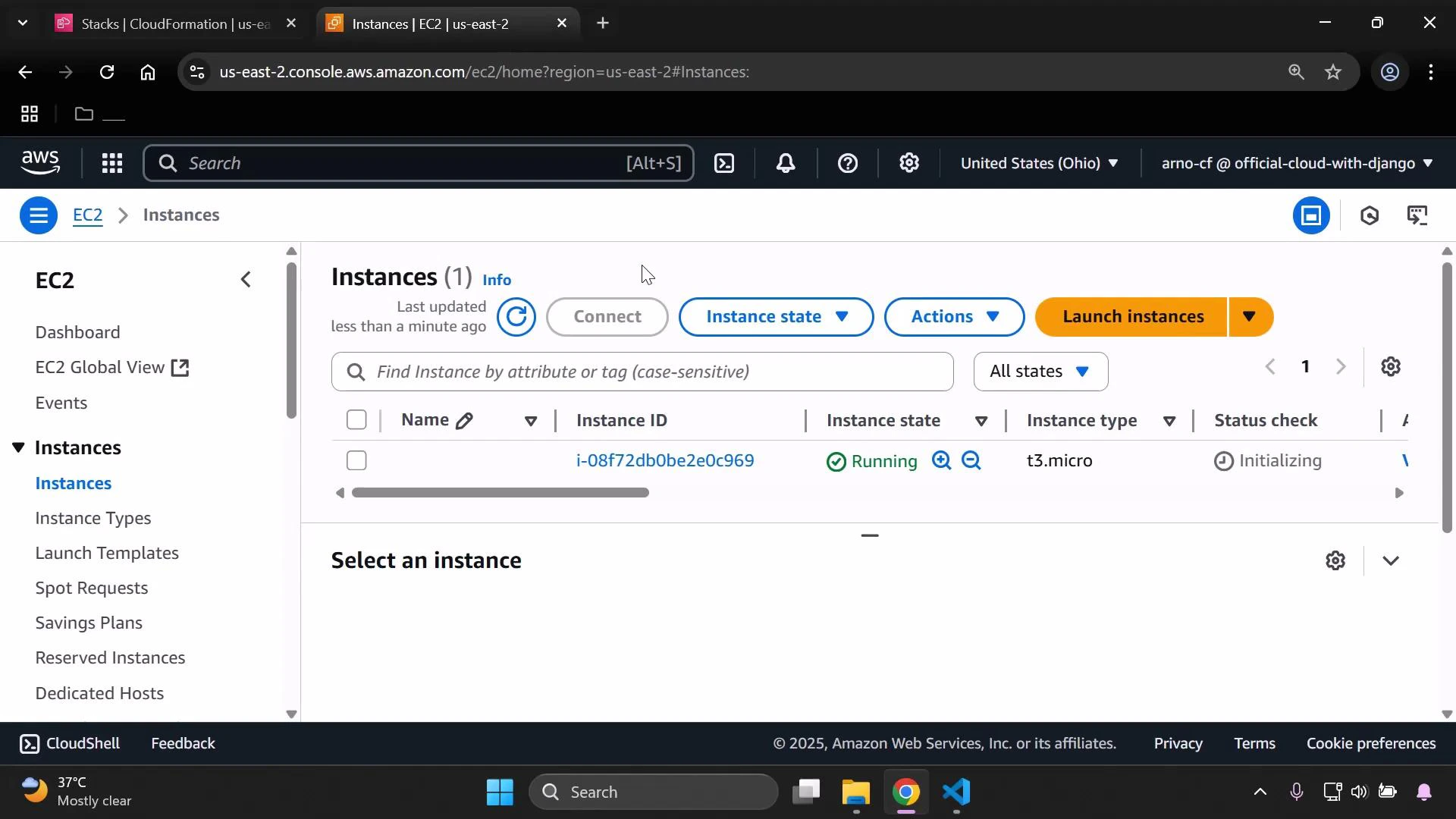
CREATE_COMPLETE, open the EC2 console and view Instances to confirm the instance is running.
You should see the instance launched with the instance type and AMI/platform defined in the template. By default, CloudFormation places the instance into your account’s default VPC and default security group unless you specify otherwise. If you want to control placement, add SubnetId or AvailabilityZone to the resource’s Properties.
This minimal template does not configure SSH key pairs, security groups, or user data. For production or remote access, add a KeyName, security group rules, and UserData to install or configure software at launch. Leaving defaults may expose the instance to restricted access — always follow security best practices.
- Add a KeyPair:
KeyNameproperty for SSH access. - Create or reference Security Groups to allow HTTP/SSH traffic.
- Add
UserDatato bootstrap software (e.g., install and start a web server). - Add Tags for cost allocation and resource identification.
- Specify
SubnetIdorAvailabilityZoneto control placement.