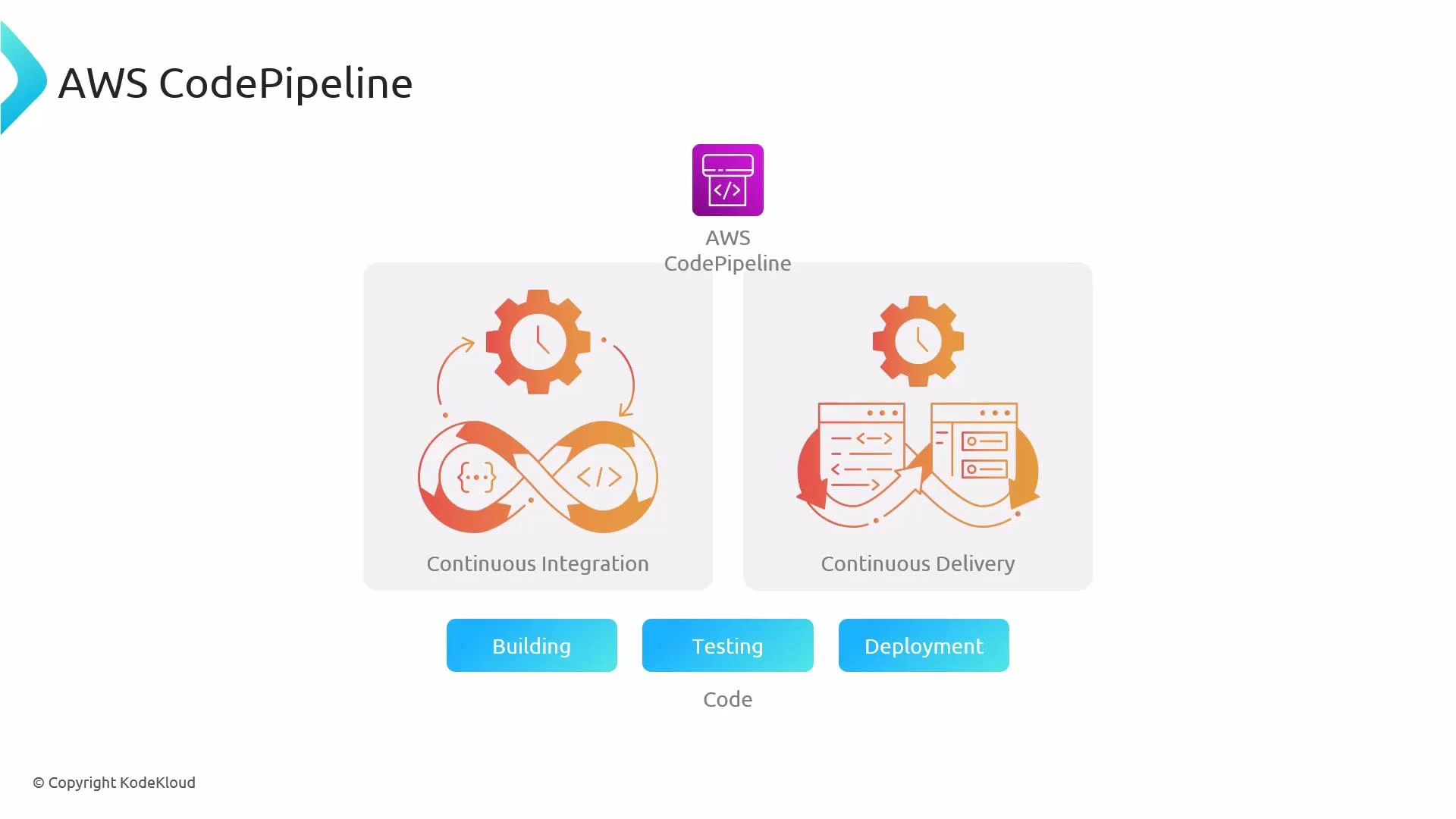
Hi everyone — welcome to this lesson on using AWS CodePipeline (CI/CD Pipeline) together with AWS CloudFormation to implement continuous delivery for infrastructure. Below we explain what CodePipeline does, how it integrates with CloudFormation, and best practices for automating safe, auditable stack deployments. AWS CodePipeline (CI/CD Pipeline) is a managed CI/CD service that models your release process as a sequence of stages (source → build/test → deploy). By automating each stage, CodePipeline helps you deliver infrastructure and application changes more quickly and reliably. CodePipeline integrates with many tools and services: GitHub or CodeCommit for source, AWS CodeBuild for build/validation, and AWS CloudFormation (or CodeDeploy, Lambda, etc.) for deployment. This lets you build a pipeline that validates CloudFormation templates, runs tests, and then creates or updates stacks automatically.Documentation Index
Fetch the complete documentation index at: https://notes.kodekloud.com/llms.txt
Use this file to discover all available pages before exploring further.
- Source control of templates and application code.
- Template validation and automated testing prior to deployment.
- Creation or update of CloudFormation stacks, optionally using change sets for controlled deployments.
- Auditable, repeatable deployments with manual approvals where needed.
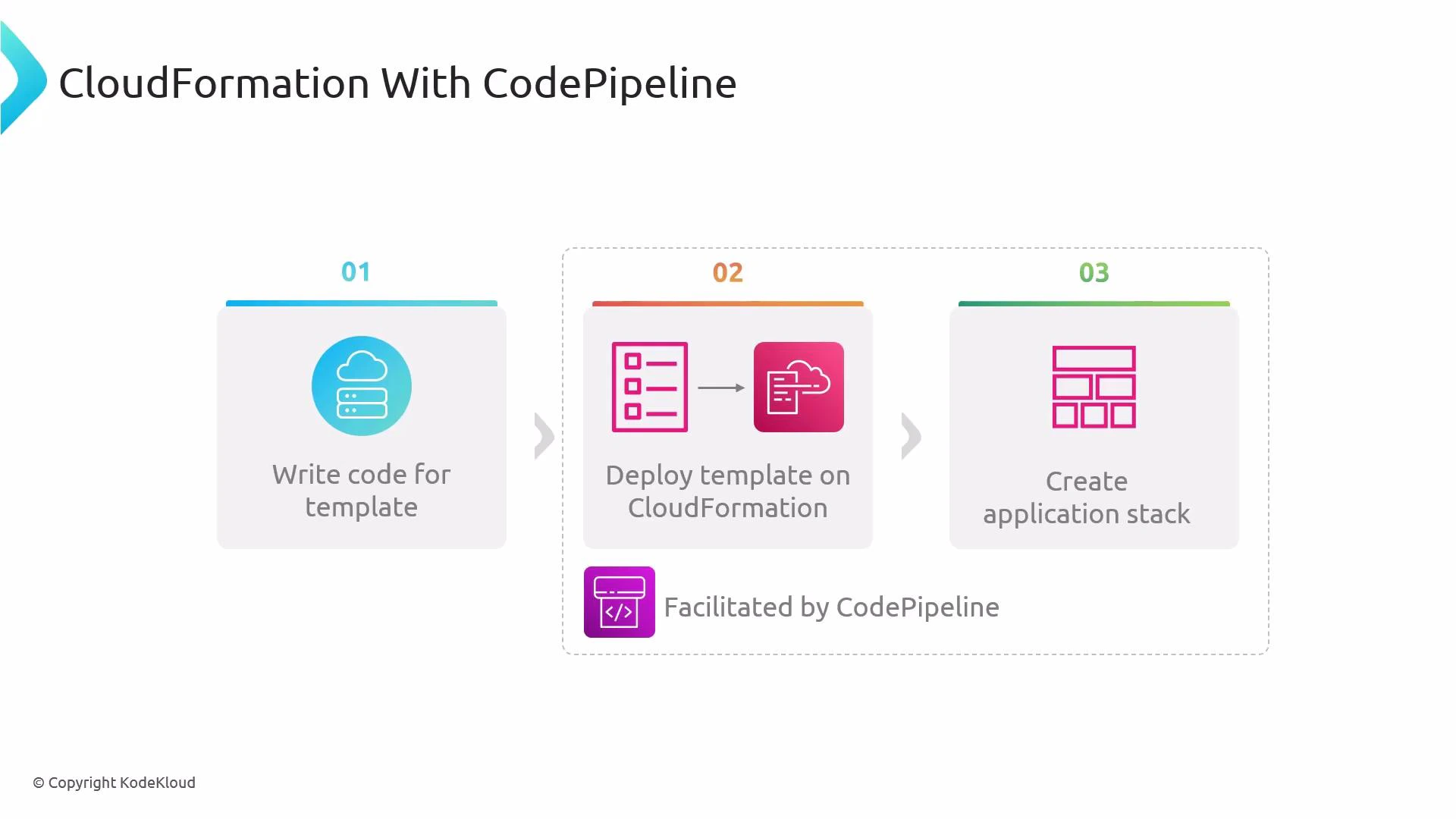
- Write or change a CloudFormation template.
- Push changes to your source repository.
- The pipeline pulls the change, validates/test the template, then triggers CloudFormation to create/update the stack.
- Application runs inside the provisioned resources; pipeline records artifacts and results.
| Stage | Purpose | Typical Tools / Actions |
|---|---|---|
| Source | Retrieve templates and application code | GitHub, CodeCommit, S3 |
| Build / Validate | Lint templates, unit tests, produce artifacts | CodeBuild (cfn-lint, unit tests), CloudFormation validate-template |
| Change-set / Approvals | Prepare safe changes and pause for reviews | CloudFormation CreateChangeSet, Manual approval actions |
| Deploy | Execute change sets or create/update stacks | CloudFormation Action, CodeBuild/Lambda calling CloudFormation API |
| Post-deploy | Integration tests, monitoring, rollback-checks | CodeBuild tests, CloudWatch alarms, automated rollback logic |
- Validate templates and run cfn-lint (in CodeBuild or locally):
- Create a change set:
- Execute the change set after review:
CodePipeline supports native AWS CloudFormation actions such as “Create/Update Stack” and “Create Change Set”. For advanced validation or parameter generation you can add CodeBuild or Lambda steps that call the CloudFormation API before applying changes.
- Automated, auditable deployments of infrastructure changes with versioned artifacts.
- Validation and test stages to catch errors before infrastructure is modified.
- Safe deployment patterns using change sets and manual approvals to reduce risk.
- Integration with IAM and CloudWatch for secure, monitored operations and safe rollbacks.
- Use change sets in pipelines to preview and review resource changes before execution.
- Keep templates modular (nested stacks or modules) and store artifacts in S3 with unique versions.
- Run cfn-lint and unit tests in a build stage (CodeBuild) to catch syntactic and semantic issues early.
- Add a manual approval stage for production deployments and use separate pipelines/environments for dev/staging/prod.
- Restrict pipeline service roles with least privilege to limit the blast radius of a compromised pipeline.
Ensure pipeline roles and CloudFormation execution roles have least-privilege IAM policies. Incorrect permissions can cause failed deployments or unintended privilege escalation. Also plan artifact retention and S3 bucket encryption to meet compliance requirements.
- AWS CodePipeline documentation
- AWS CloudFormation documentation
- cfn-lint: https://github.com/aws-cloudformation/cfn-lint