Welcome to the AWS CloudFormation course by KodeKloud. I’m Arno Pretorius, and I’ll guide you through Infrastructure as Code (IaC) using AWS CloudFormation. This course is designed for cloud engineers, DevOps practitioners, and anyone expanding their AWS skill set. You’ll gain hands-on experience defining, deploying, and maintaining cloud infrastructure using CloudFormation templates. Understanding CloudFormation is essential for automating scalable, secure, and repeatable deployments. Organizations such as Netflix and Samsung rely on CloudFormation to manage large-scale, complex infrastructure reliably. In this lesson you’ll learn what CloudFormation is, how it works, and how to start using its documentation, features, and best practices.Documentation Index
Fetch the complete documentation index at: https://notes.kodekloud.com/llms.txt
Use this file to discover all available pages before exploring further.
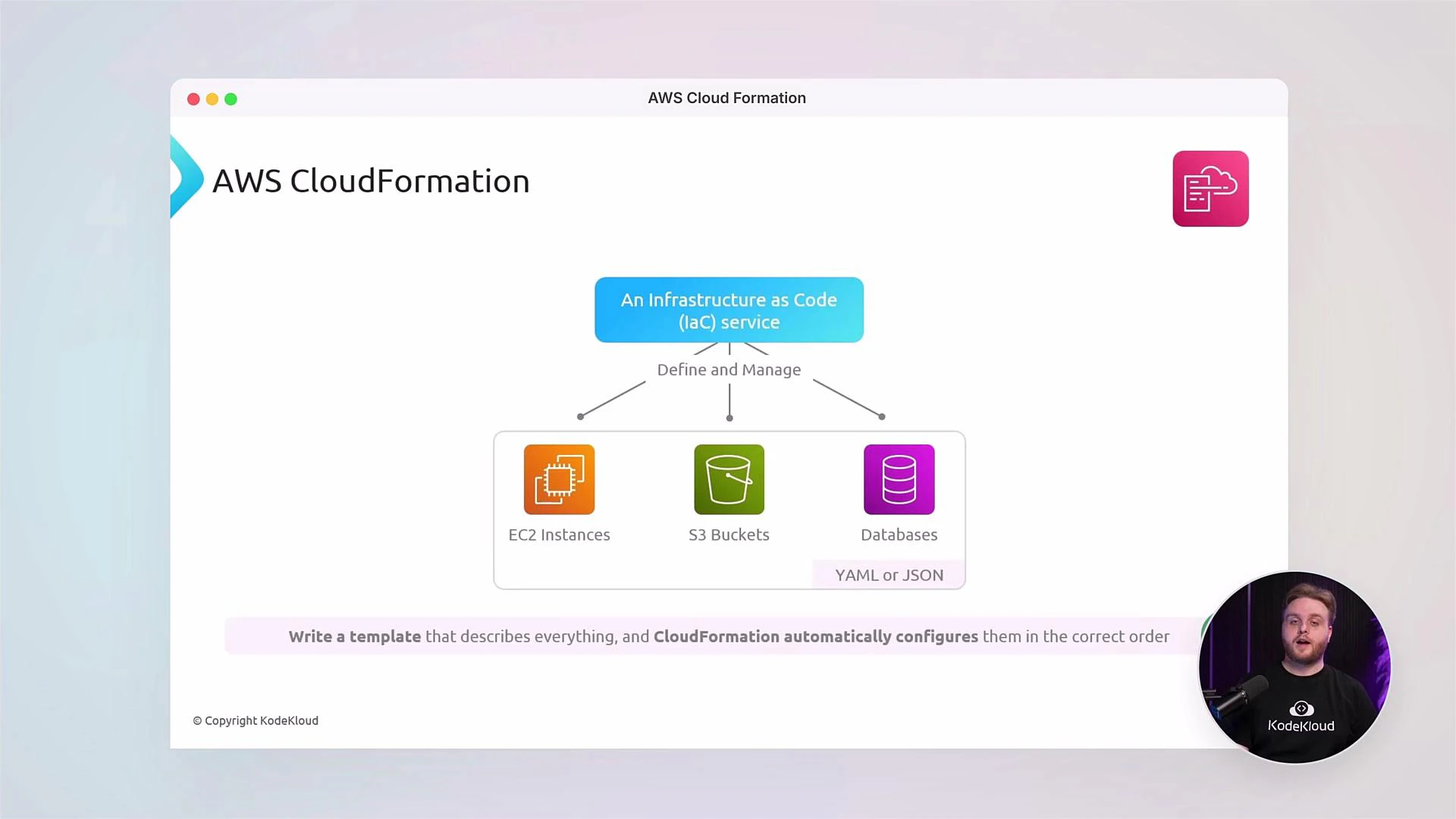
CloudFormation templates can be authored in JSON or YAML. Throughout this course we’ll use YAML for readability, conciseness, and easier maintenance of complex templates.
- Core CloudFormation concepts: templates, stacks, change sets, and StackSets.
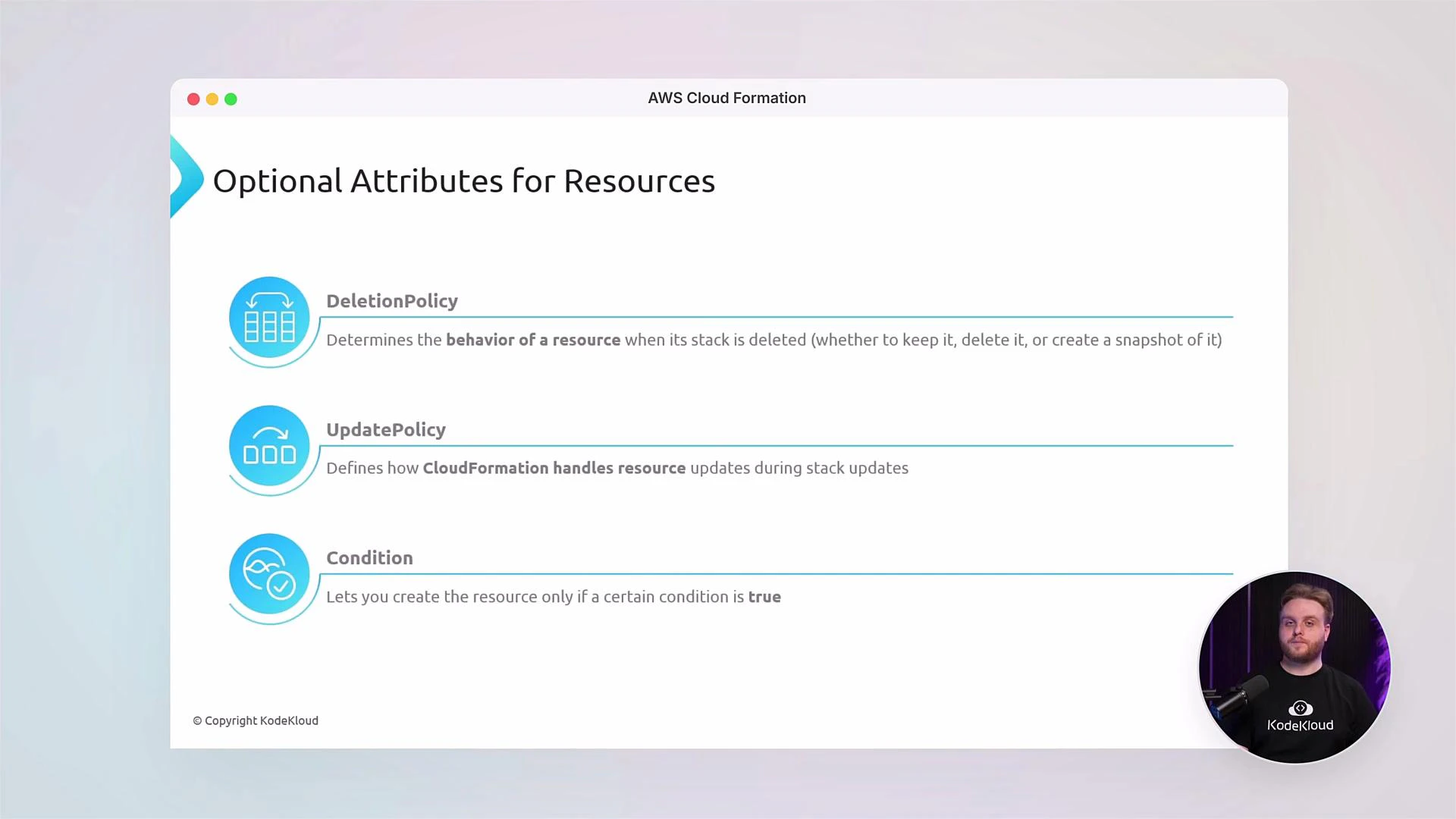
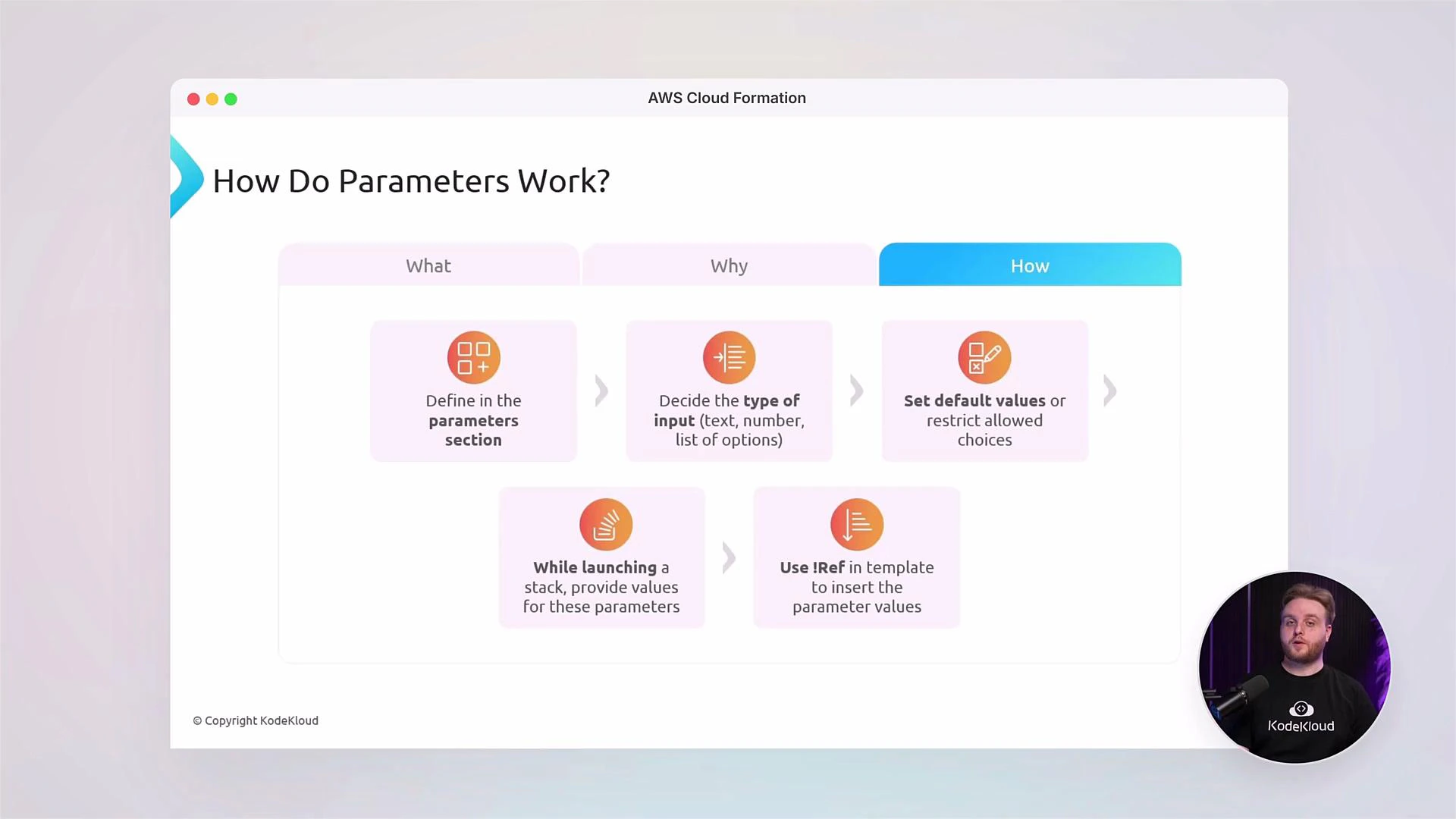
- How to author resources, metadata, parameters, mappings, conditions, and outputs in YAML templates.
- Policies and drift detection to manage stack lifecycle and configuration integrity.
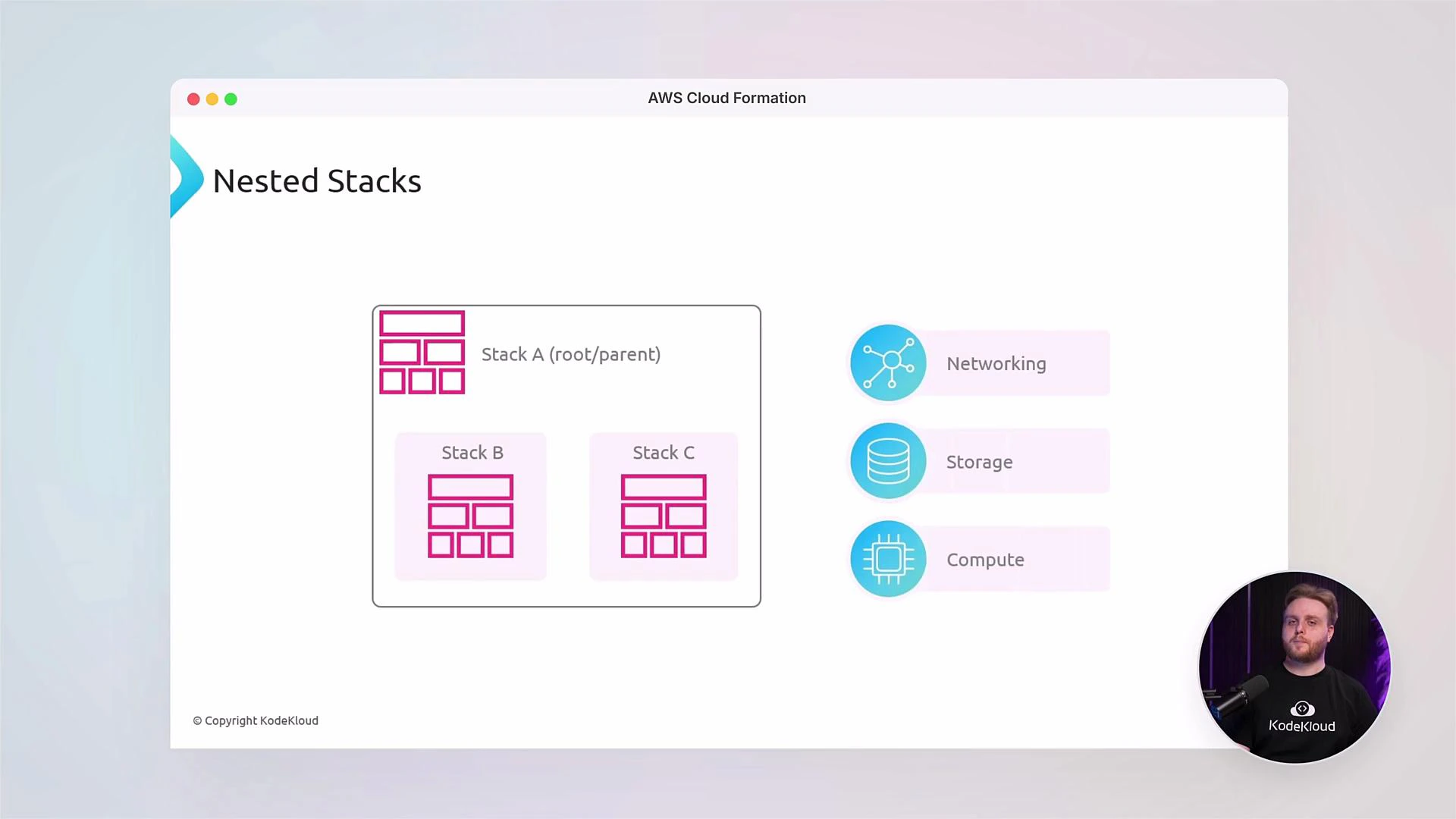
- Best practices for modular templates (nested stacks), cross-stack references, and multi-account deployments.
- Declarative IaC: Describe the desired state, and CloudFormation provisions resources.
- Repeatability: Recreate environments consistently across regions and accounts.
- Integration: Works with IAM, AWS Organizations, CI/CD pipelines, and other AWS services.
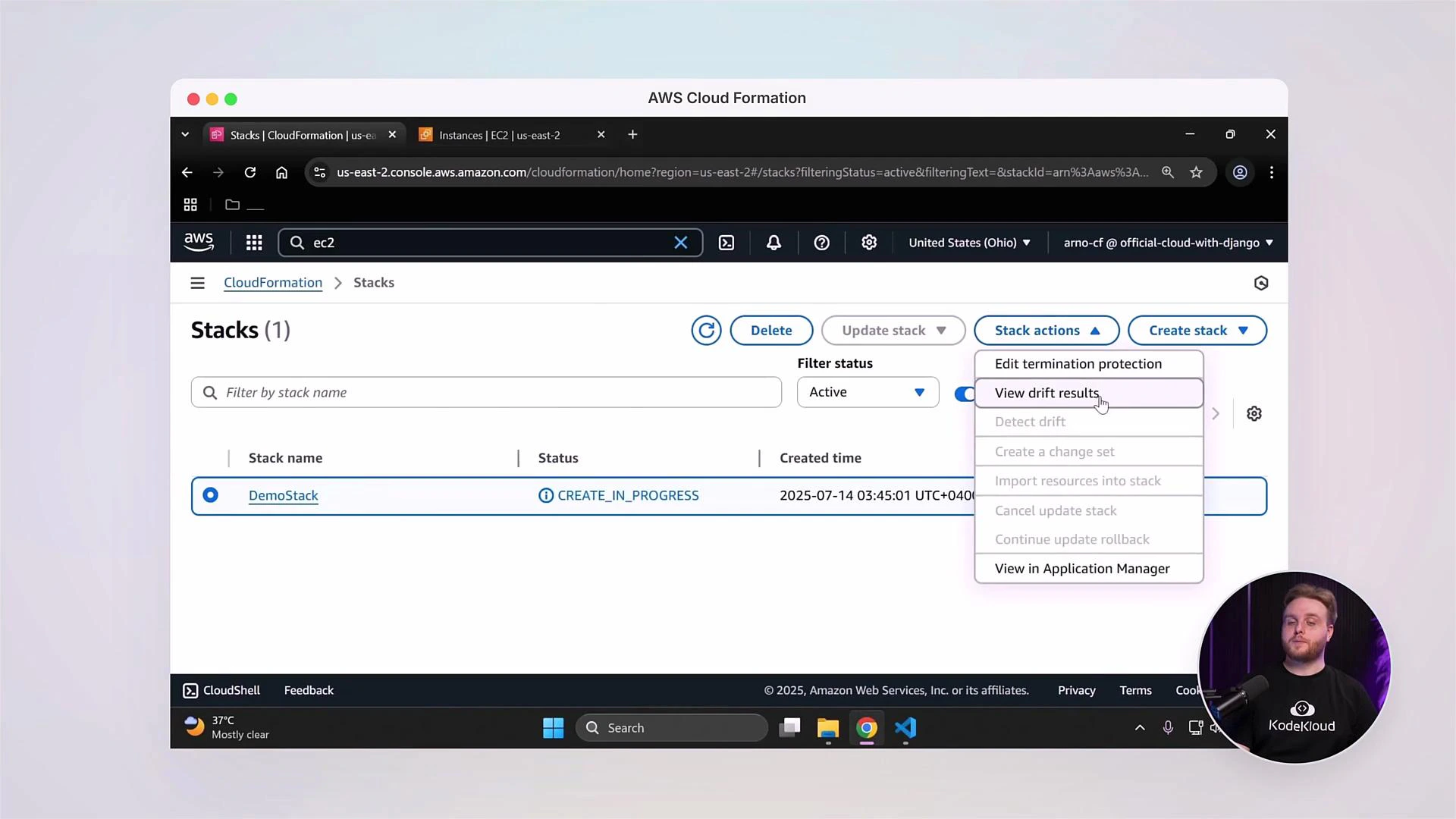
- Auditable change control: Use change sets and drift detection to track modifications.
- Keep templates modular and use logical names for resources.
- Validate templates with tools like cfn-lint and the CloudFormation validate-template API.
- Use Change Sets before applying updates to production stacks.
S3 bucket names must be globally unique across all AWS accounts and regions. Avoid hardcoding names in production templates unless you control the naming scheme. Consider using parameters or generated names instead.
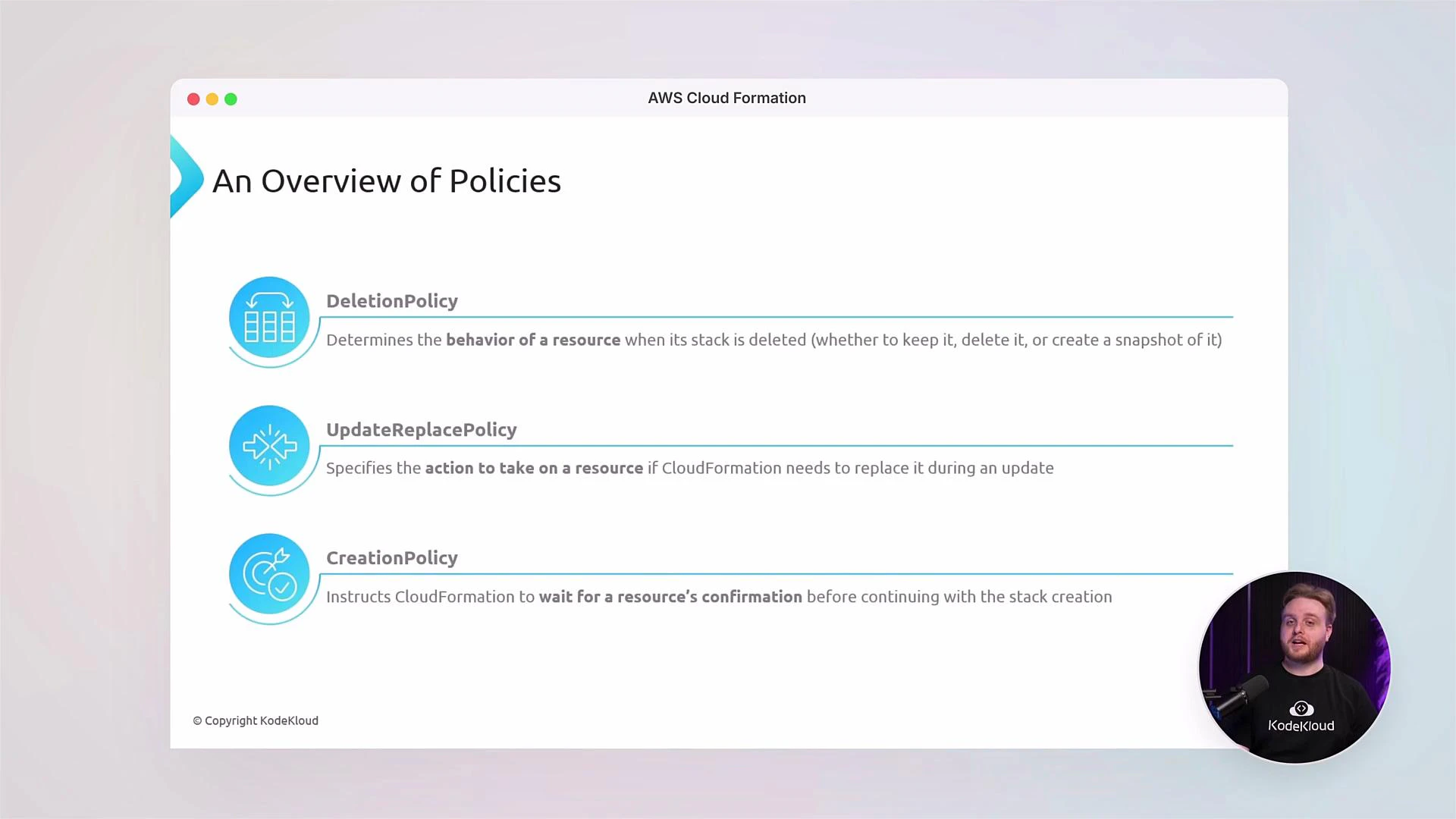
| Policy Attribute | Purpose | Example use case |
|---|---|---|
| DeletionPolicy | Retain or snapshot resource on stack deletion | Keep S3 buckets or DB snapshots when stacks are deleted |
| UpdateReplacePolicy | Control replacement behavior during updates | Prevent accidental data loss on resource replacement |
| CreationPolicy | Delay stack completion until resource signals success | Wait for EC2 instances to finish bootstrapping |
- IAM integration: Attach fine-grained IAM policies to CloudFormation execution role for secure deployments.
- Custom IAM policies: Define least-privilege roles to limit stack actions.
- Drift Detection: Use drift detection to identify resources that diverged from the template and remediate drift through updates and change sets.
- Template validation: Use aws cloudformation validate-template and cfn-lint for syntax and best-practice checks.
- Automation: Integrate CloudFormation with CI/CD pipelines (AWS CodePipeline, GitHub Actions, Jenkins).
- Local testing: Combine SAM for serverless resources and LocalStack for local testing when appropriate.
- AWS CloudFormation User Guide: https://docs.aws.amazon.com/AWSCloudFormation/latest/UserGuide/
- Template reference (intrinsic functions): https://docs.aws.amazon.com/AWSCloudFormation/latest/UserGuide/intrinsic-function-reference.html
- cfn-lint (linting tool): https://github.com/aws-cloudformation/cfn-lint
- AWS CLI (CloudFormation commands): https://docs.aws.amazon.com/cli/latest/reference/cloudformation/index.html
- StackSets documentation: https://docs.aws.amazon.com/AWSCloudFormation/latest/UserGuide/what-is-cfnstacksets.html