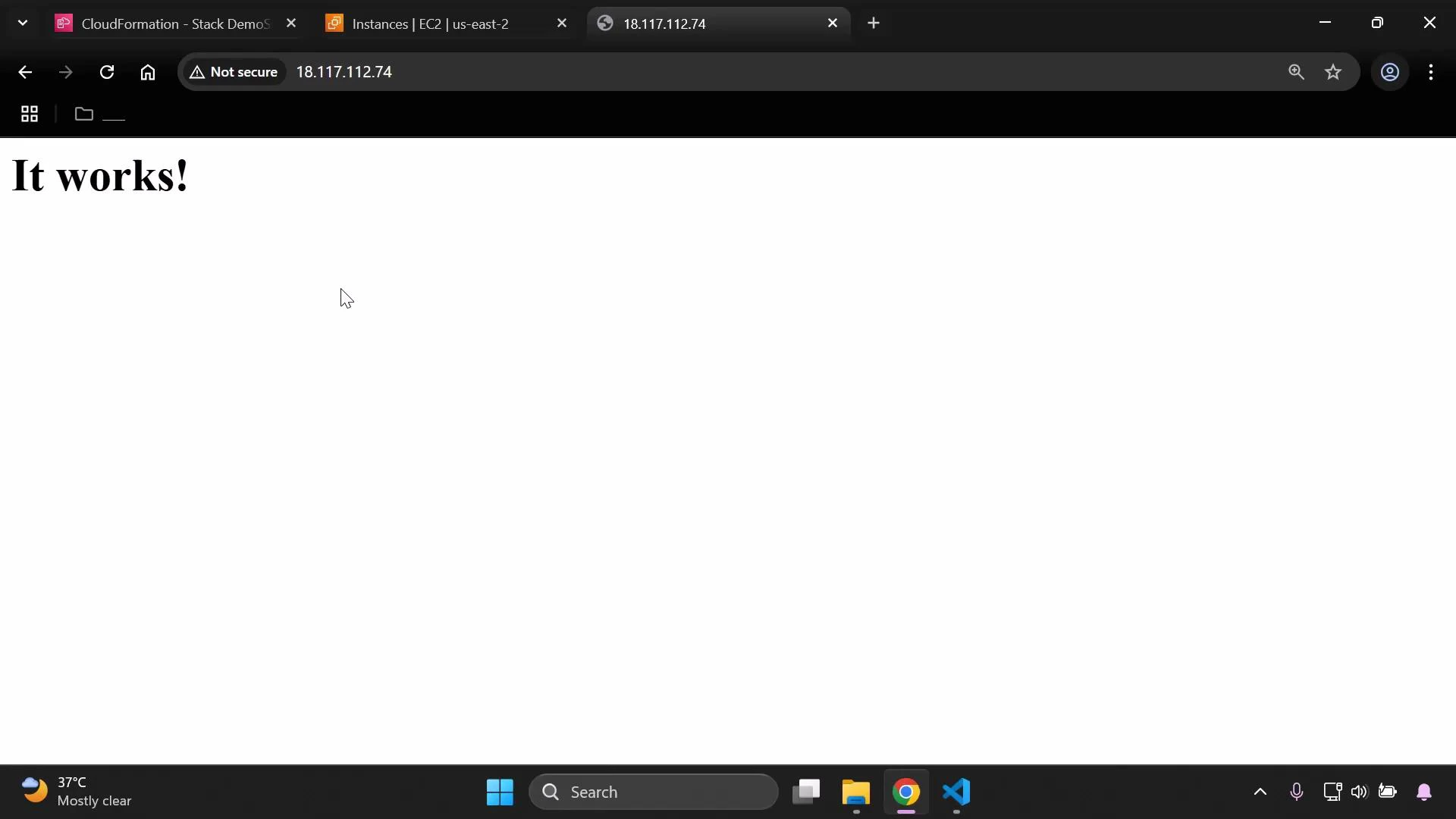
In this lesson you’ll provision a simple Amazon EC2 web server using an AWS CloudFormation template. The template adds a UserData script so the instance boots with Apache (httpd) already installed and running. This approach makes it easy to automate server provisioning and verify that the instance is serving HTTP traffic after creation. What we’ll doDocumentation Index
Fetch the complete documentation index at: https://notes.kodekloud.com/llms.txt
Use this file to discover all available pages before exploring further.
- Add a Base64-encoded UserData script to the EC2 instance so it runs on first launch.
- Create a security group that allows HTTP (port 80) and optionally SSH.
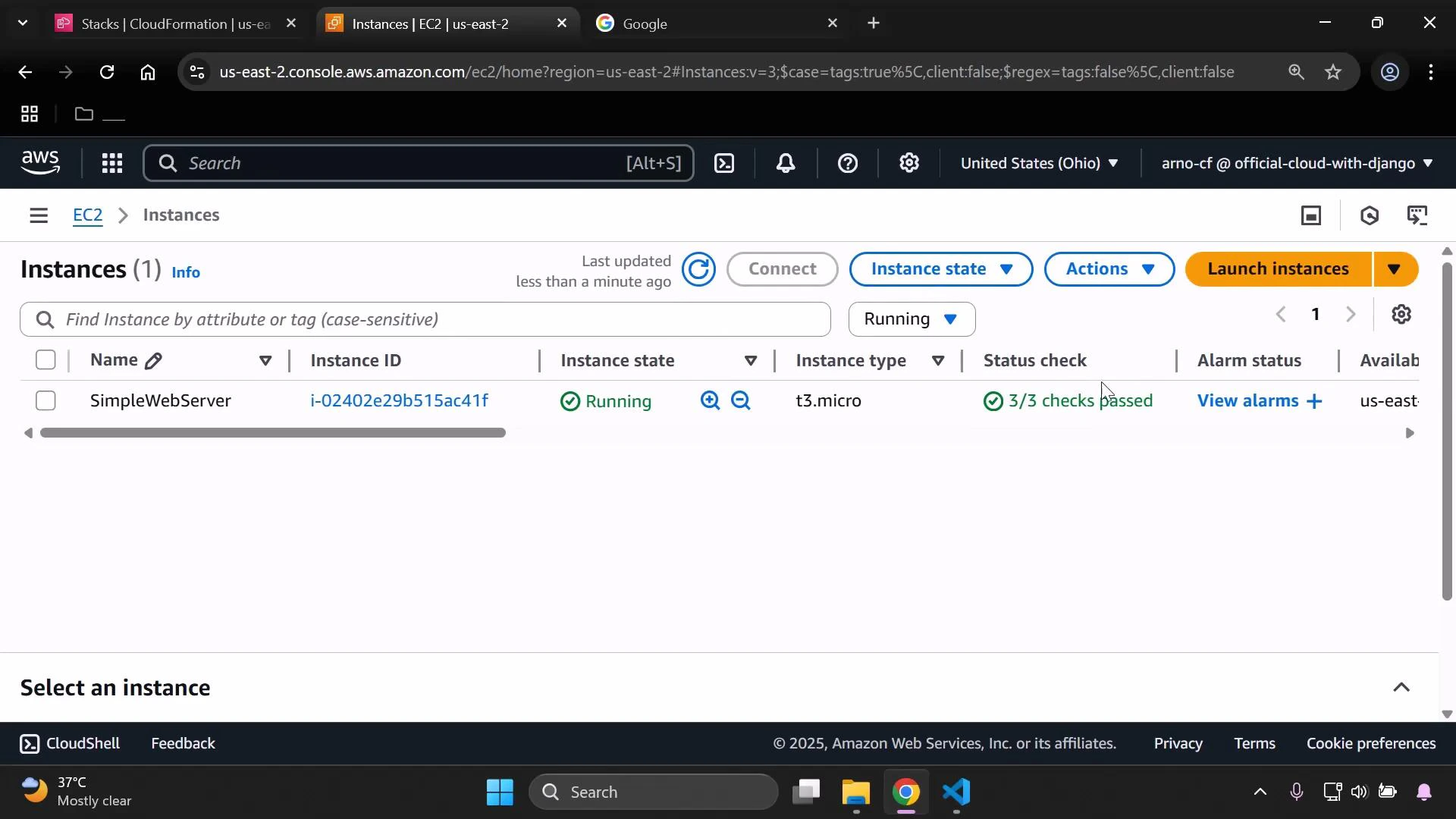
- Deploy the stack, confirm the instance is running, and retrieve the public IP to visit the web server.
What is UserData (and why Base64)?
UserData is a script that automatically runs the first time an EC2 instance boots. It’s commonly used to install packages, configure services, or run commands that prepare the instance for its role. CloudFormation expects UserData to be Base64-encoded; use Fn::Base64 (or !Base64) so CloudFormation encodes the script for you. Example: EC2 resource with UserData- The shebang (#!/bin/bash) ensures the script runs with bash.
- The commands update packages, install httpd, start it, and enable it to run on boot.
Configure the security group
Ensure the security group allows inbound HTTP (port 80). If you need SSH access, add a rule for port 22 — but restrict its source CIDR to known IP addresses for security. Security group example:| Protocol | Port | Example CIDR | Purpose |
|---|---|---|---|
| TCP | 80 | 0.0.0.0/0 | Public HTTP (web) access |
| TCP | 22 | 203.0.113.0/24 | SSH access — restrict to known IPs |
Full example template (core parts)
This concise CloudFormation template demonstrates Metadata, Parameters, Resources, and Outputs. It provisions an EC2 instance with the UserData script and a security group, and exposes the instance ID and public IP as outputs.- Replace the AMI (
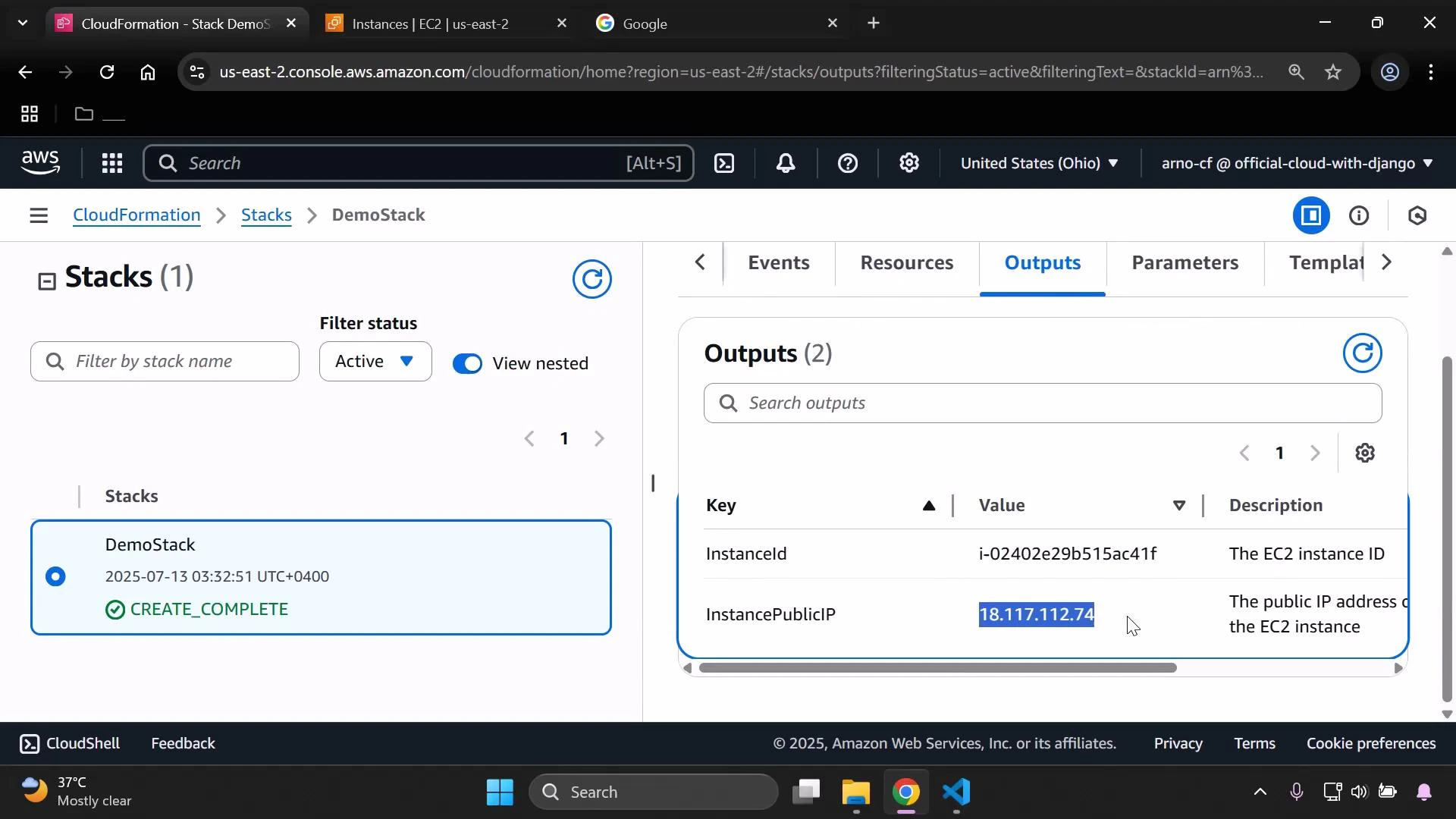
ImageId) andVpcIdwith values appropriate to your region/account. - The Outputs section makes it easy to retrieve the public IP from the CloudFormation console.
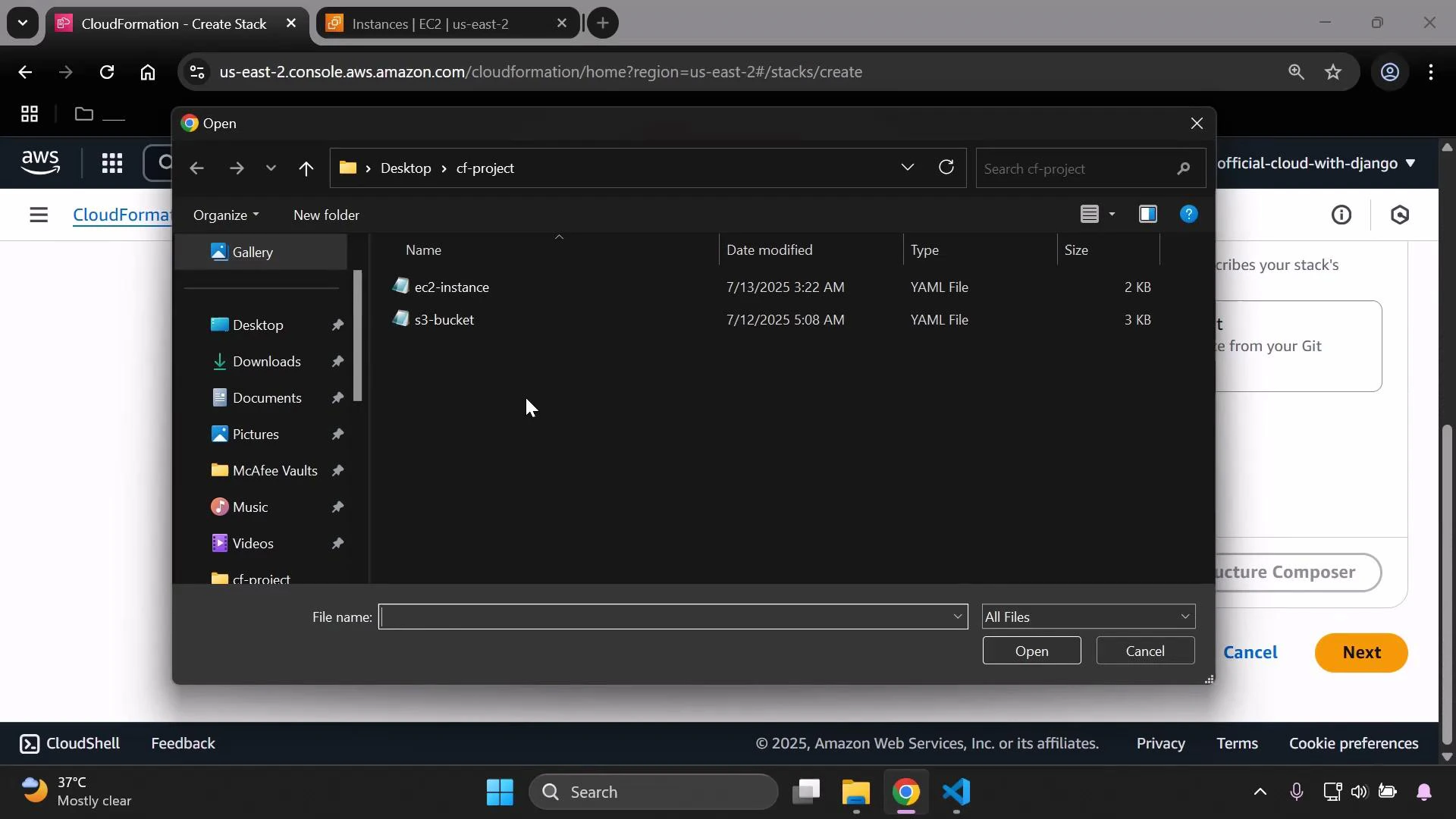
Deploy the CloudFormation stack
- Upload this template when creating the stack in the CloudFormation console, or provide an S3 URL.
- Choose an instance type (for example, t3.micro) and create the stack.
Find the instance public IP
You can locate the instance public IPv4 address via:- EC2 console: select the instance and view the Public IPv4 address, or
- CloudFormation console: open the stack’s Outputs (InstancePublicIP).
Notes and best practices
UserData scripts run only once—on the instance’s first boot. To apply a changed UserData script to an existing instance, you must recreate the instance (for example, delete and re-create the CloudFormation stack) or use a configuration management tool (like Cloud-init, UserData-managed scripts that re-run, or systems such as Ansible) that can enforce configuration changes after boot.
Avoid leaving SSH (port 22) open to the entire internet in production. Restrict SSH access to known IP ranges or use AWS Systems Manager Session Manager for secure, auditable shell access: https://docs.aws.amazon.com/systems-manager/latest/userguide/session-manager.html
Links and references
- AWS CloudFormation: https://docs.aws.amazon.com/cloudformation/
- Amazon EC2: https://docs.aws.amazon.com/ec2/
- AWS Systems Manager Session Manager: https://docs.aws.amazon.com/systems-manager/latest/userguide/session-manager.html