In this lesson we cover AWS CloudFormation StackSets: a feature that lets you deploy and manage identical CloudFormation stacks across multiple AWS accounts and regions from a single central operation. StackSets are ideal when you need the same infrastructure deployed consistently across environment tiers (development, test, production) or across multiple AWS accounts and regions. Instead of manually recreating a stack in each account/region, you define one StackSet with its template and parameters, then target the accounts and regions where stack instances should be created.Documentation Index
Fetch the complete documentation index at: https://notes.kodekloud.com/llms.txt
Use this file to discover all available pages before exploring further.
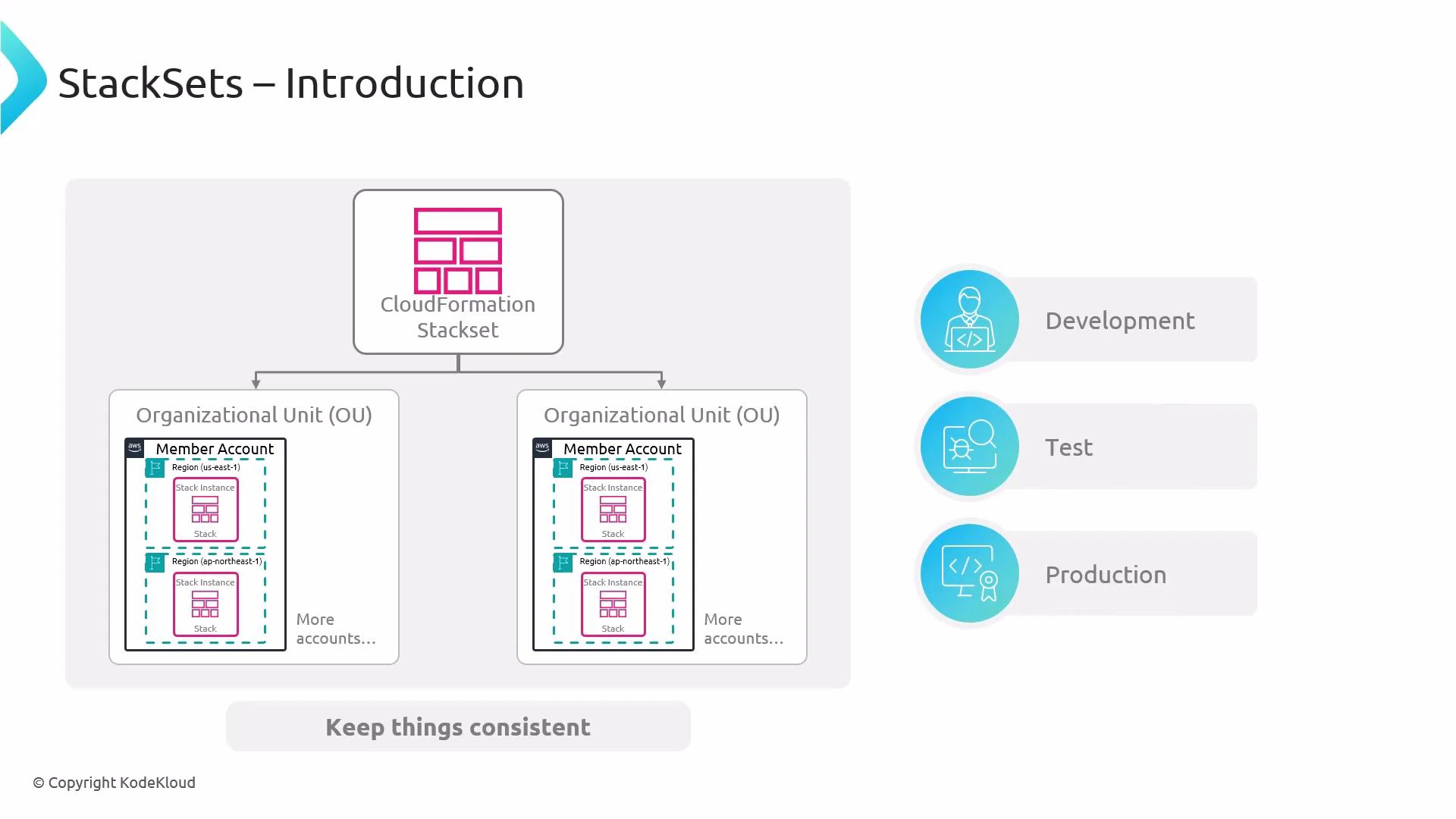
- Centralized operations: create, update, and delete stacks across many accounts and regions from a single administrator (management) account.
- Consistency: ensure identical templates and parameter values are applied across targets.
- Scale: efficiently deploy infrastructure at organization scale using Organizational Units (OUs) or explicit account lists.
Before deploying StackSets at scale, confirm your deployment permission model: service-managed permissions or self-managed permissions. With self-managed permissions, you must create an administrator IAM role in each target account that the management account can assume.
| Term | Meaning | Example / Note |
|---|---|---|
| StackSet | The CloudFormation construct that stores the template, parameter values, and target accounts/regions. | The central definition you manage from the administrator account. |
| Stack instance | A standard CloudFormation stack created from the StackSet in a specific account and region. | Each stack instance appears in the target account’s CloudFormation console. |
| Targets | Where the StackSet deploys stack instances — can be specific accounts, a list of accounts, or OUs, plus regions. | Use OUs to target all member accounts in an organizational unit. |
- Management scope: StackSets are created and controlled from an administrator (management) account, but the resulting stack instances are deployed into target member accounts and regions.
- Visibility: To inspect resources created by a stack instance, open the CloudFormation console in the target account and region where the instance was provisioned.
- Create — deploys stack instances across the specified accounts and regions based on the StackSet definition.
- Update — modifies the StackSet template or parameters and propagates changes to existing stack instances.
- Delete — removes stack instances and, when no instances remain, allows deletion of the StackSet itself.
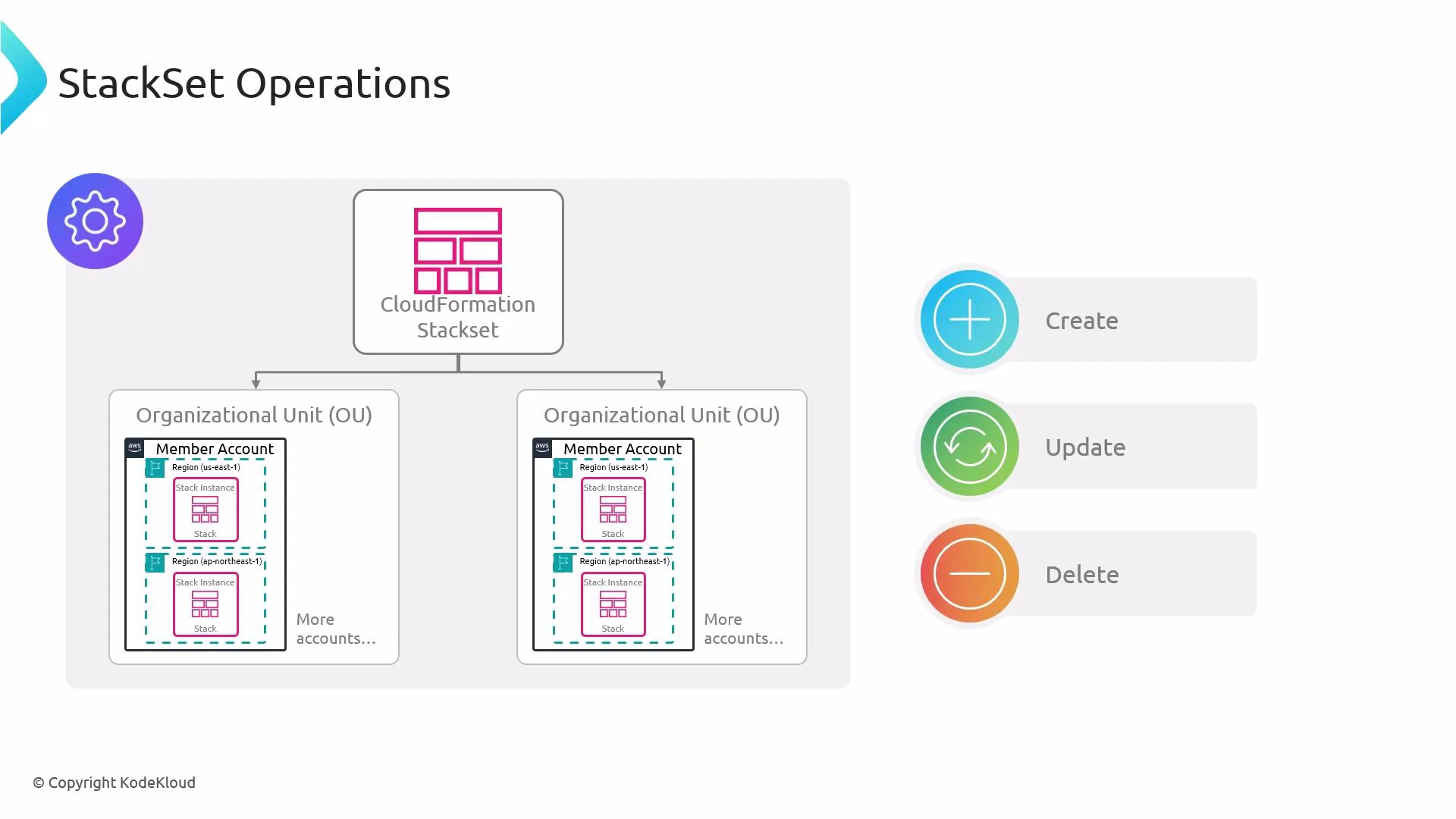
- A StackSet cannot be deleted while it still has associated stack instances. Remove all stack instances first (either individually or via the StackSet delete-instances operation), then delete the StackSet itself.
- Consider resource dependencies and deletion order across accounts and regions to avoid orphaned or dependent resources being left behind.
When deleting stack instances across accounts and regions, review cross-account and cross-region dependencies. Deleting in the wrong order can leave orphaned resources or cause failures that require manual remediation.
- Choose permission model: service-managed (recommended for AWS Organizations) or self-managed.
- Prepare IAM roles: for self-managed, create administrator roles in target accounts; for service-managed, confirm organization permissions.
- Test in a small set of accounts/regions first before large-scale deployments.
- Monitor stack instance drift, failures, and stack events in each target account/region.
- AWS CloudFormation — StackSets (AWS Docs)
- AWS Organizations (overview)
- AWS IAM documentation
- CloudFormation course on KodeKloud