- Provides a deterministic outbound IP address (or a set of IPs) for resources in a subnet.
- Keeps VMs private (no public IPs required) while allowing outbound internet access.
- Eliminates the need for custom outbound user-defined routes (UDRs) for typical internet-bound traffic.
- Scales to support many concurrent outbound connections (with planning for SNAT ports).
| Step | Purpose | Notes |
|---|---|---|
| Create NAT gateway | Provision the NAT resource in your Azure region | Choose single public IP or public IP prefix based on scale needs |
| Assign outbound IP(s) | Ensure deterministic outbound address(es) | Use public IP prefix for high concurrency to avoid SNAT exhaustion |
| Attach to subnet(s) | Route outbound traffic from target subnets through NAT | A NAT gateway can be attached to multiple subnets (within same VNet) |
| Adjust TCP idle timeout (optional) | Tune idle connection lifetime for your workload | Default 4 min; configurable 4–120 minutes |
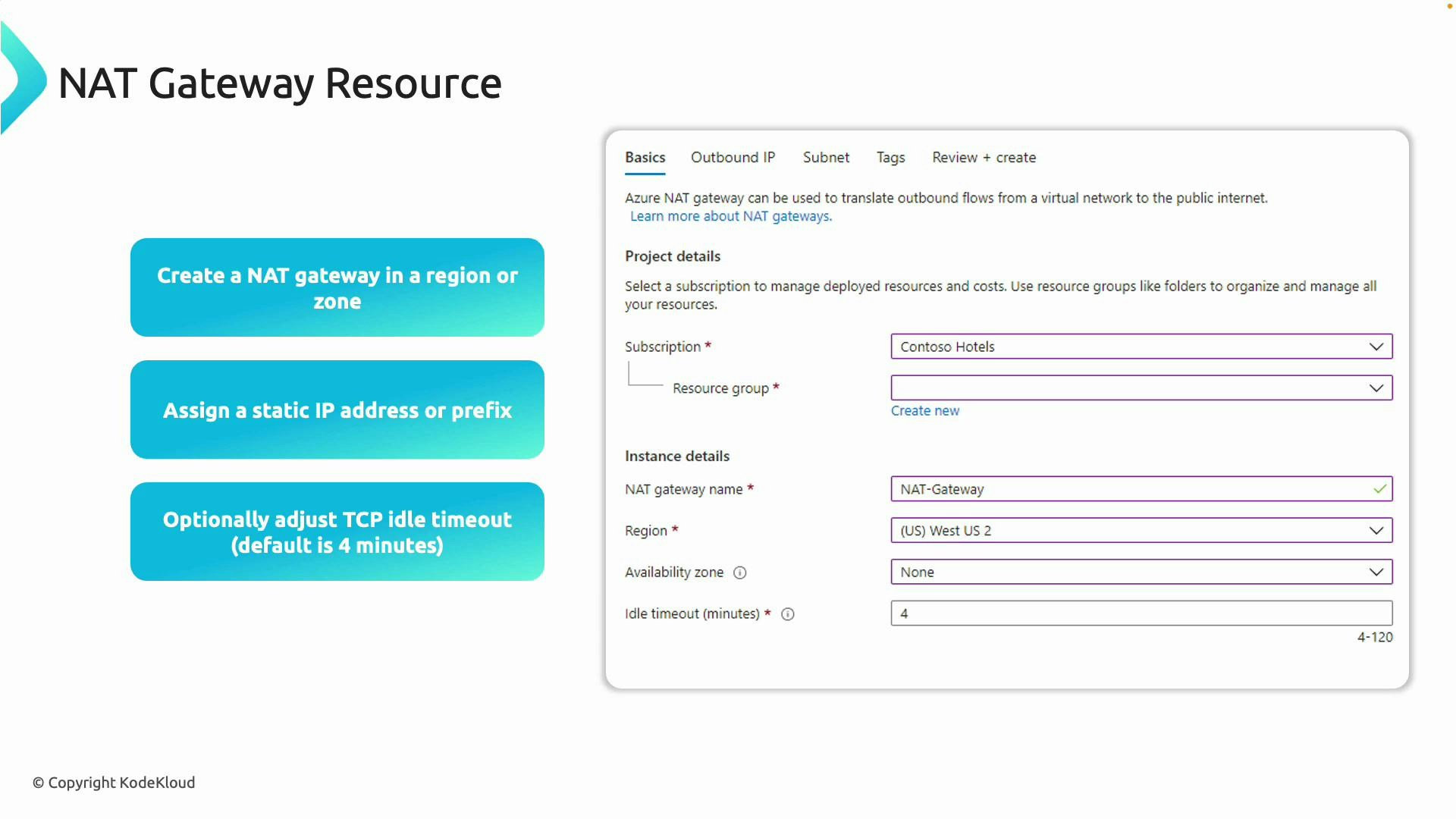
The TCP idle timeout determines how long Azure keeps an idle TCP connection open. Default is 4 minutes; you can set it between 4 and 120 minutes. Increase this value for workloads that maintain long-lived idle connections (e.g., persistent database connections or long polling).
- Attach the NAT gateway to a subnet (or multiple subnets) inside the same VNet.
- All resources (VMs, scale sets) in an attached subnet will use the NAT gateway for outbound Internet traffic.
- No outbound UDRs are required — Azure automatically routes outbound traffic from the subnet to the NAT gateway.
- A single NAT gateway may be attached to several subnets in the same VNet, but you cannot attach more than one NAT gateway to the same subnet.
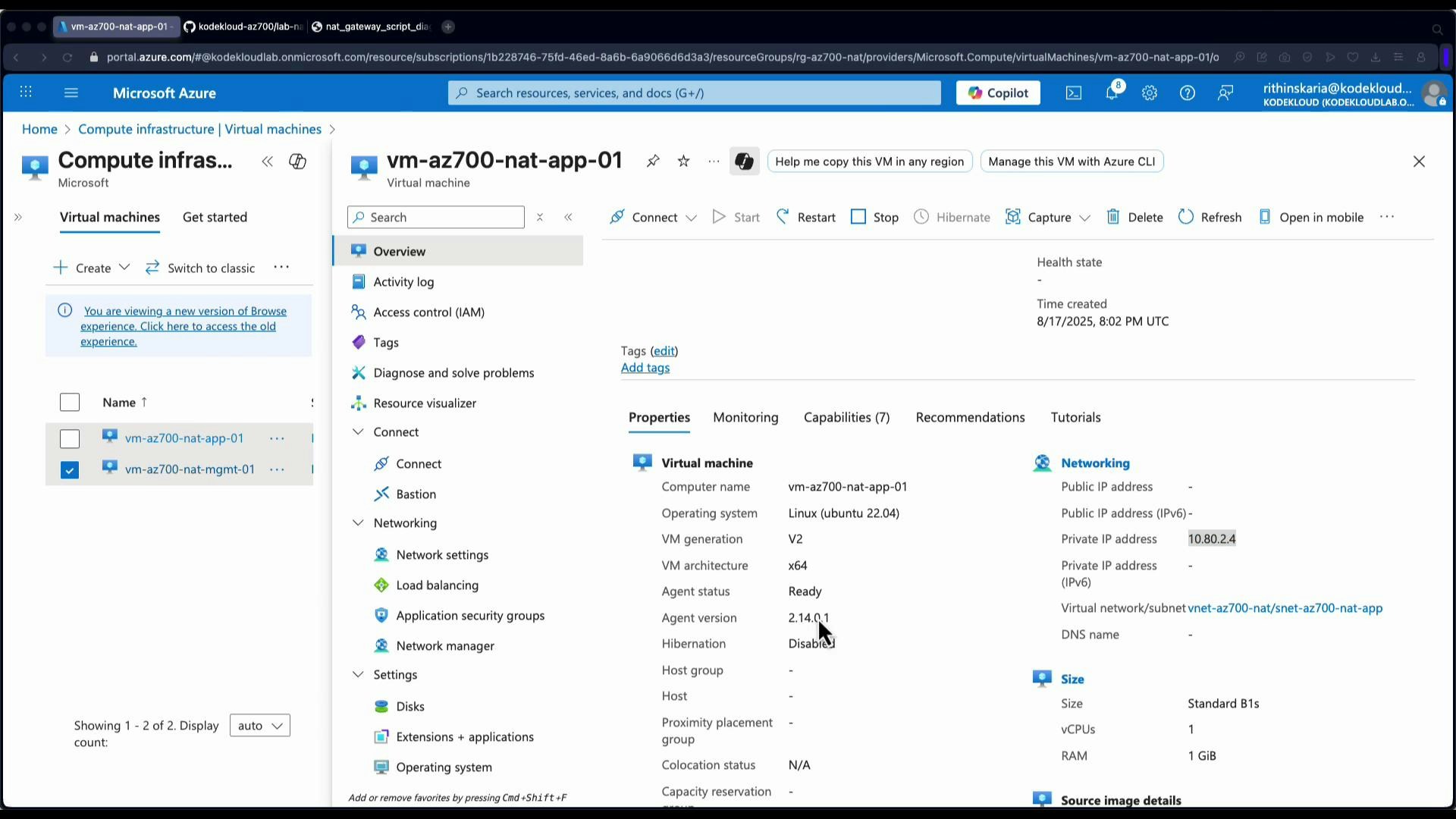
- Management subnet: management VM with a public IP (used as a jumpbox).
- App subnet: app VM without a public IP (will use NAT gateway for outbound traffic).
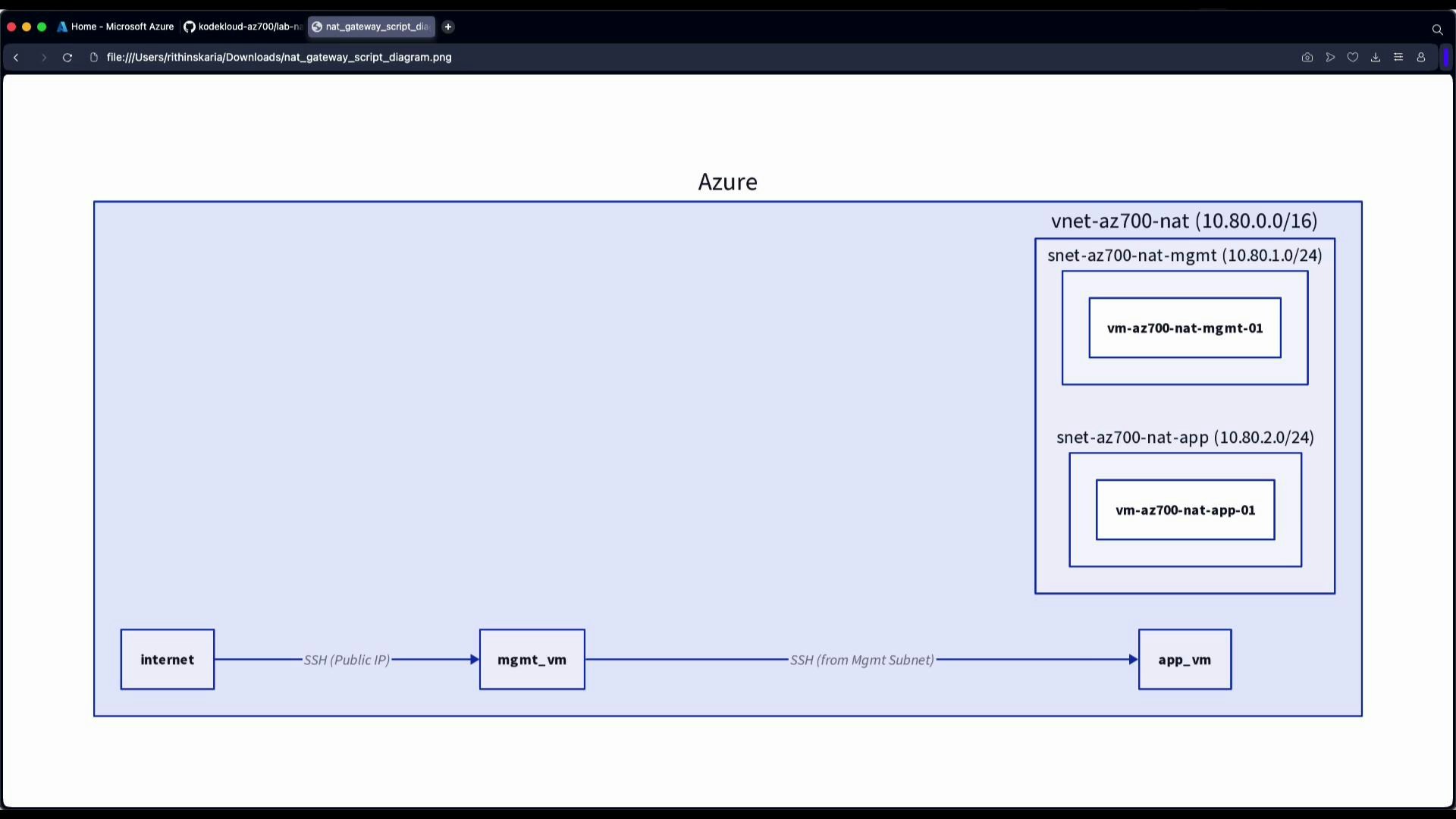
- SSH to the management VM (has a public IP):
- From the management VM, verify its outbound public IP:
- From the management VM, SSH to the app VM using its private IP (example 10.80.2.4):
- On the app VM (no public IP), check the outbound IP:
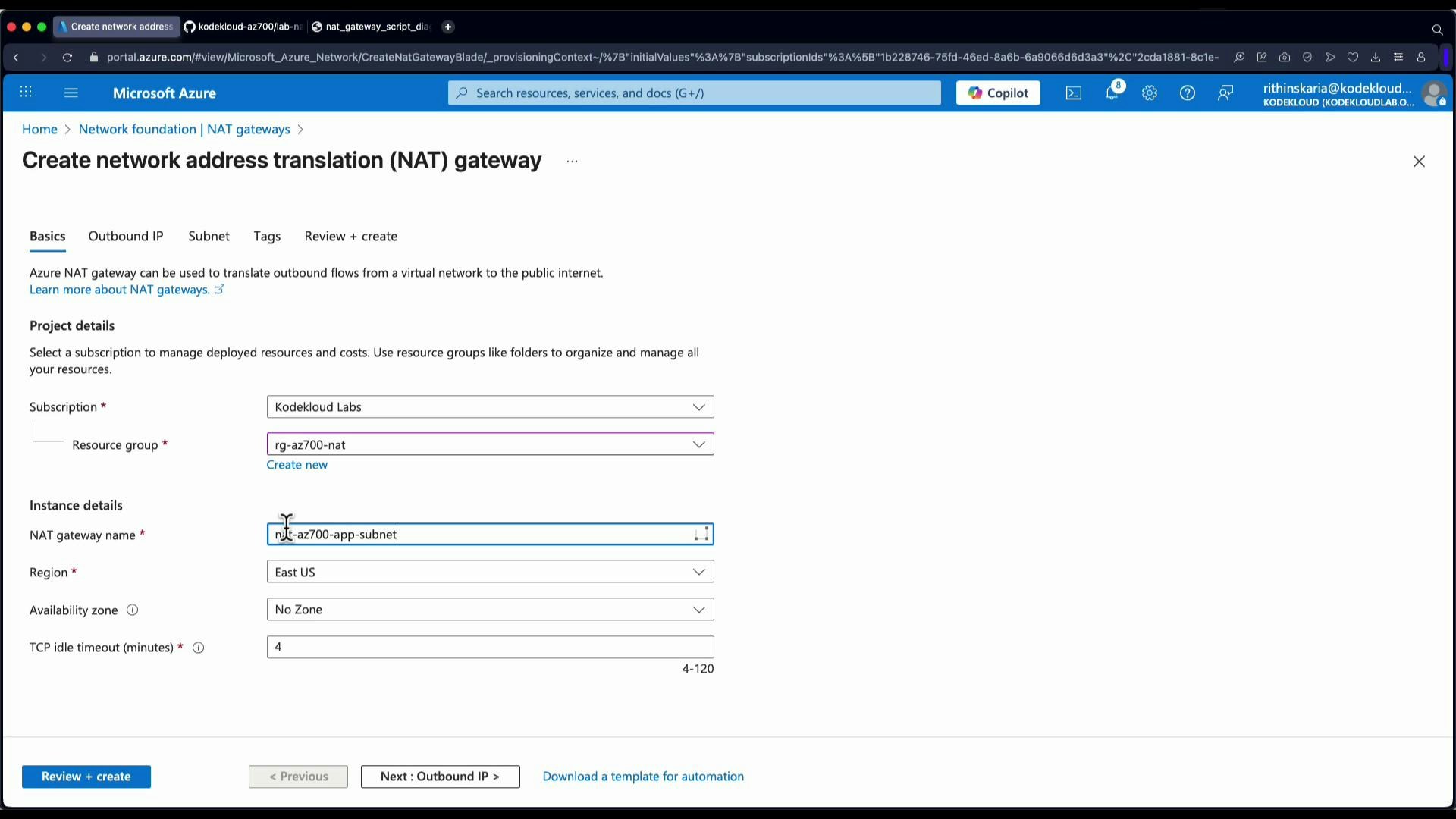
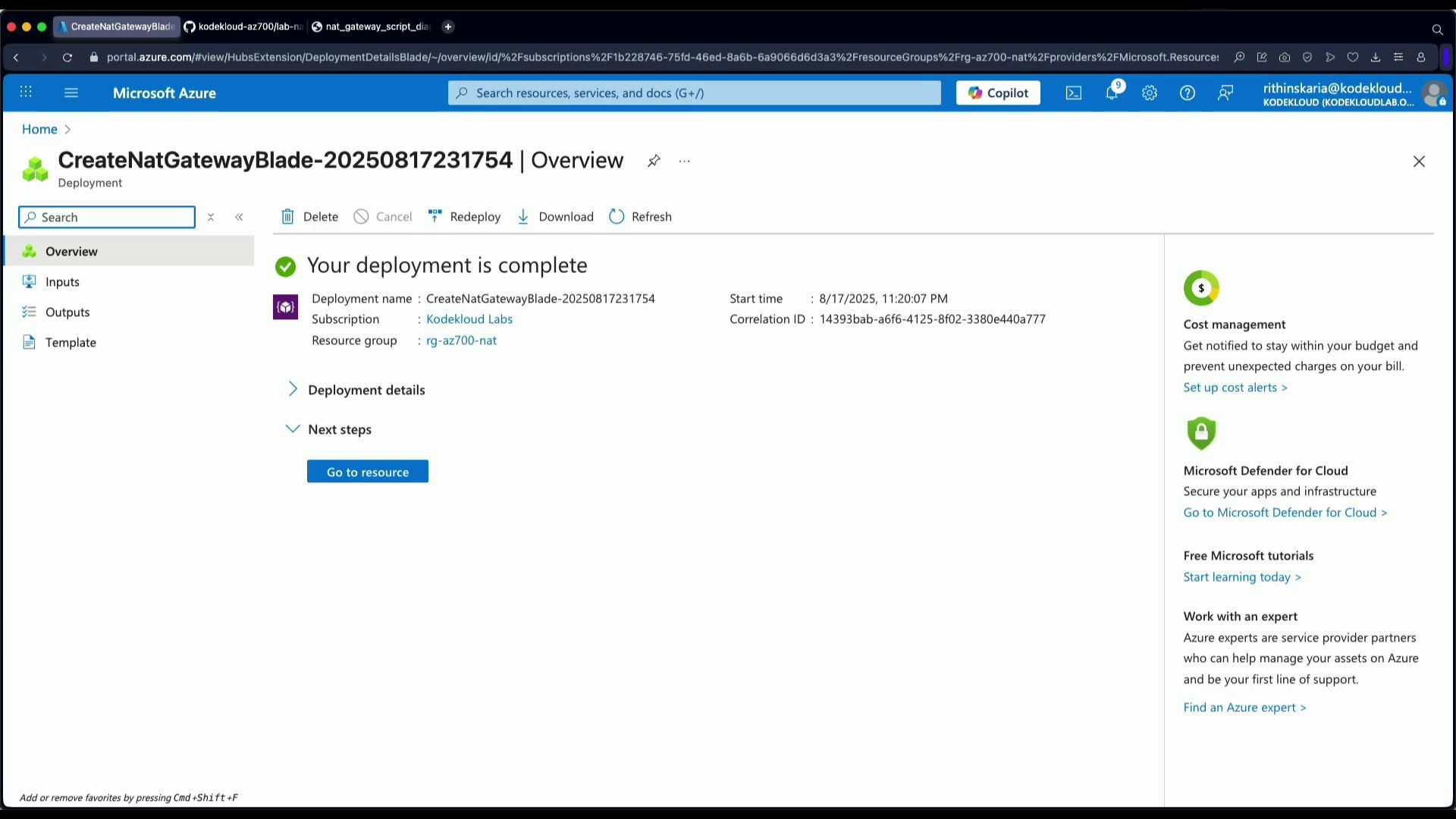
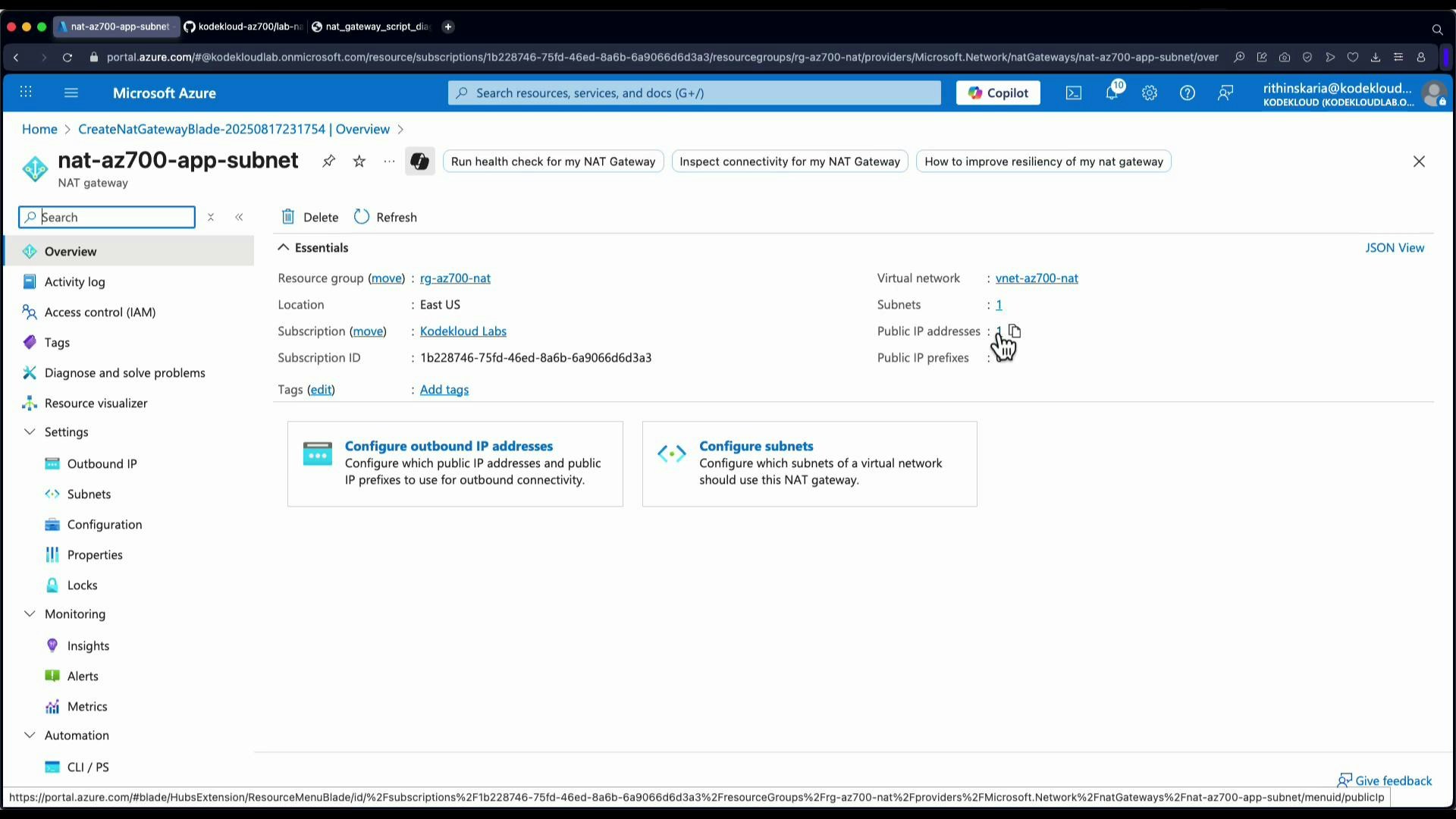
- In the Azure portal, search for and create a NAT gateway resource:
- Choose subscription and resource group (e.g., rg-az700-nat).
- Select a region (East US in this example).
- Choose either a single outbound Public IP or a Public IP Prefix (multiple IPs).
| Resource | Consideration |
|---|---|
| Single Public IP on NAT gateway | ~64,000 SNAT ports available — may be exhausted with many concurrent connections |
| Public IP Prefix (multiple IPs) | Provides multiple outbound addresses and increases available SNAT ports |
If your workload makes many concurrent outbound connections, provision a public IP prefix (multiple IPs) for the NAT gateway or design to distribute connections across multiple IPs to avoid SNAT port exhaustion.
- During creation attach outbound public IP(s) (single IP for labs; public IP prefix for production/high-scale). After creation, attach the NAT gateway to the app subnet:
- Option A: Open the NAT gateway → Subnets → Select the app subnet → Save.
- Option B: Open the VNet → Subnets → Select the app subnet → Associate NAT gateway → Save.
- Return to the app VM (SSH via management VM).
- Check the app VM outbound IP:
- Verify the outbound IP shown in the NAT gateway resource’s Overview → Outbound IP addresses to confirm the public IP in use.
- Deterministic outbound IP(s) for whitelisting and audit logs.
- Azure handles outbound routing automatically — no custom outbound UDRs required.
- Improved security posture: VMs can remain private (no public IPs) while still accessing the internet.
- Azure NAT gateway overview: https://learn.microsoft.com/azure/virtual-network/nat-overview
- Azure public IP and public IP prefix: https://learn.microsoft.com/azure/virtual-network/public-ip-address
- SNAT port considerations and troubleshooting: https://learn.microsoft.com/azure/load-balancer/load-balancer-outbound-connections