- A DNS zone is a container for the DNS records (A, CNAME, MX, TXT, NS, SOA, etc.) for a specific domain or subdomain.
- Example: if you own echovisa.com, the DNS zone stores all records that map names (web, mail, etc.) to IPs or services.
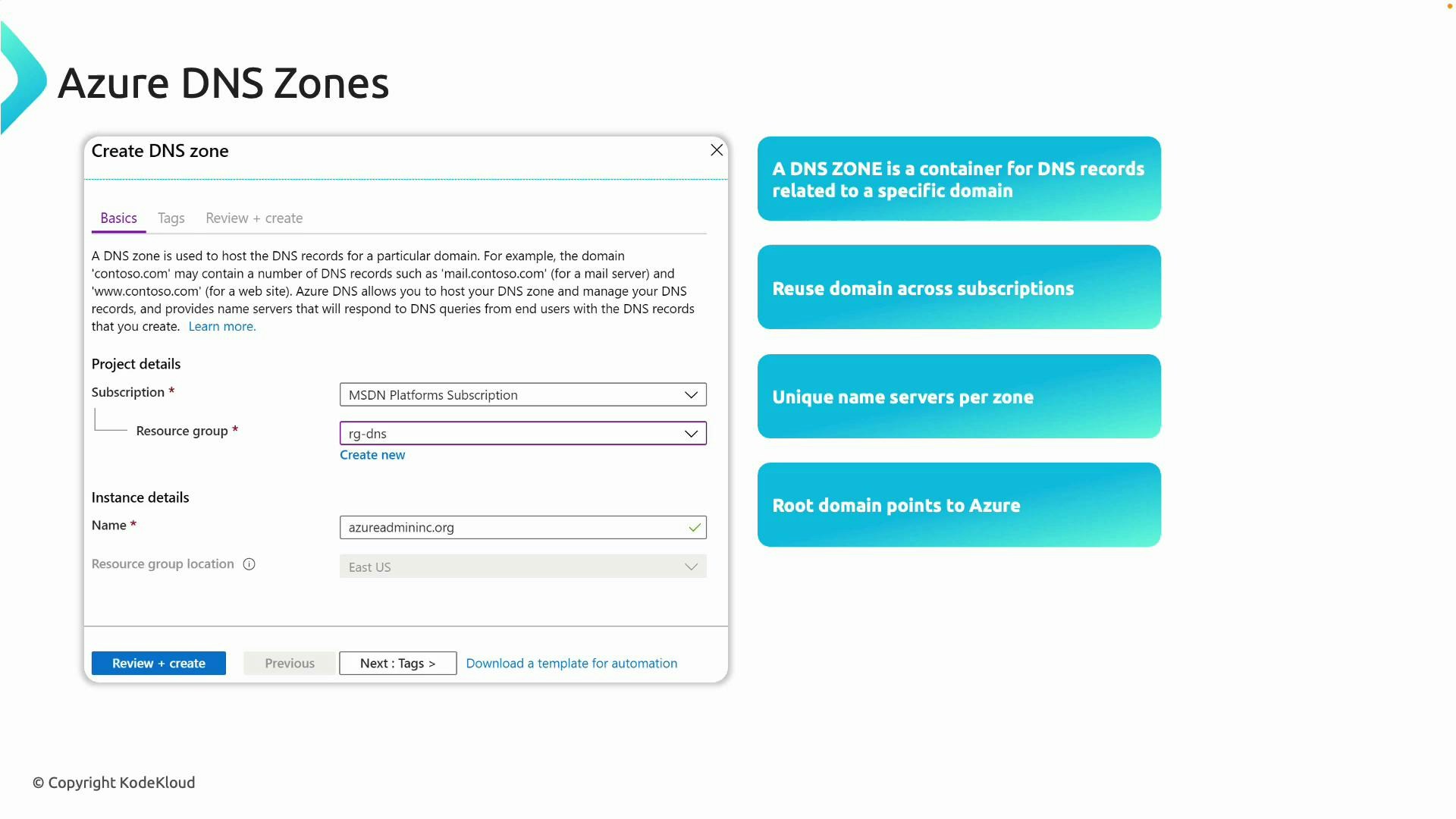
- Azure DNS zones can be created in any supported subscription and resource group; you can manage zones across subscriptions.
- Each public Azure DNS zone is assigned four authoritative name servers — use these values to delegate the domain from your registrar to Azure.
- Creating a DNS zone in Azure does not automatically make Azure authoritative for the domain — you must update delegation at the registrar.
- Create a DNS zone in Azure.
- Copy the Azure-assigned name servers from the zone overview.
- Update the domain’s name servers at your registrar to the Azure name servers.

- A record set groups records that share the same name and type within a zone (for example, multiple A records for the same host to achieve simple round-robin).
- Azure supports standard DNS record types: A, AAAA, CNAME, MX, NS, TXT, PTR, SRV, etc.
- Azure prevents duplicate records within a record set to avoid conflicts.
- The Azure portal’s Add record set form adapts the required fields based on the record type (A requires IPv4 address, CNAME requires a target name, MX requires preference and mail server, etc.).

| Record Type | Use Case | Example |
|---|---|---|
| A | Map a hostname to an IPv4 address | web.echovisa.com → 4.210.189.55 |
| AAAA | Map a hostname to an IPv6 address | www.example.com → 2001:db8::1 |
| CNAME | Alias one name to another canonical name | shop.echovisa.com → shops.azurewebsites.net |
| MX | Mail exchange records for email routing | echovisa.com MX 10 mail.echovisa.com |
| TXT | Miscellaneous text (SPF, DKIM, verification) | echovisa.com TXT "v=spf1 include:..." |
| NS | Delegation of subdomains or the zone itself | echovisa.com NS ns1-09.azure-dns.com |
| SOA | Start of authority, zone metadata | Auto-created by Azure DNS |
- Create a resource group (e.g., RGDNS or 700-domains) and then create a DNS zone named echovisa.com. If you have many existing records, you can import a zone file in BIND format.
- Once the zone is created, Azure assigns four distributed name servers. The new zone contains at least NS and SOA records automatically.
- Add a record set. Example: create an A record for az700.echovisa.com with IP 1.1.1.1.

- If you run nslookup az700.echovisa.com from a machine that still uses the registrar’s DNS servers, you might see the old IPs because public delegation still points to the registrar:

- To confirm Azure is authoritative for the record in your zone, query one of the Azure-assigned name servers directly:
- Make Azure authoritative globally by updating the registrar’s name servers:
- Copy the four Azure name servers from the Azure DNS zone overview.
- In your registrar’s DNS settings (e.g., GoDaddy), replace the current name servers with the Azure name servers. Note: some registrars require removing the trailing dot from the FQDNs displayed by Azure.
- Save changes and wait for delegation propagation. Propagation timing depends on previous TTLs and registrar processing; it can take minutes to hours.
When updating name servers, ensure you copy all four Azure NS records to the registrar. Some registrars strip the trailing dot — that is usually acceptable; just ensure the domain names are entered correctly.



- Example: point a web record to a VM public IP
- Start a VM and note its public IP address.
- In the DNS zone, create an A record such as web.echovisa.com and set the record value to the VM’s public IPv4 address. Choose an appropriate TTL (e.g., 1 hour). Shorter TTLs are useful while troubleshooting.





- Creating a DNS zone in Azure does not automatically make Azure authoritative for the domain — you must update the registrar to delegate the domain to Azure’s name servers.
- Use Azure DNS record sets to manage public DNS records once the domain is delegated.
- TTL controls caching and affects how quickly changes propagate to resolvers.
- For internal-only name resolution, use Azure Private DNS zones or DNS forwarding solutions; do not delegate private domains publicly.
Tip: While testing changes, use short TTLs and query Azure’s authoritative name servers directly with dig or nslookup to confirm the zone contents before updating registrar delegation.
-
Azure Private DNS zones (recommended for most Azure-only scenarios)
- Create a Private DNS zone (for example, corp.internal or contoso.local) in Azure.
- Link the Private DNS zone to one or more virtual networks (VNet links). These links control which VNets can resolve names in the private zone.
- Use virtual network DNS settings (Azure-provided resolver or custom DNS servers) so VMs and PaaS resources in linked VNets resolve private names automatically.
- You can enable automatic virtual machine registration in the zone if you use Azure VMs.
-
Split-horizon / split-brain DNS (public + private view)
- Keep the public DNS zone in Azure DNS (or registrar) for internet-facing records.
- Create a private zone with the same domain inside Azure (or use different internal naming) to serve different answers to internal clients. Note: having identical names for public and private zones requires careful planning to avoid confusion.
-
Conditional forwarding / Azure DNS Private Resolver
- If you have on-premises DNS servers and want centralized resolution, use conditional forwarders to send queries for specific domains to Azure DNS Private Resolver or to on-prem DNS servers.
- Azure DNS Private Resolver (inbound and outbound endpoints) helps bridge between on-premises DNS and Azure’s private zones without exposing private records to the internet.
- This is useful for hybrid environments where on-prem clients must resolve Azure private records and vice versa.
-
Legacy or custom DNS servers
- Run your own DNS servers (VMs) or Active Directory-integrated DNS for complex scenarios or legacy requirements. These can be connected to VNets and used as the DNS servers for your virtual networks or on-prem clients.
- Use Azure Private DNS for name resolution that must stay within your VNets.
- Avoid exposing internal-only domains to public DNS. Never publish private records on public authoritative servers.
- Use conditional forwarding or a private resolver for hybrid environments to avoid split-brain problems.
- Pick sensible TTLs: short TTLs during change windows, longer TTLs for stable records to reduce lookup volume.
- Azure DNS documentation
- Azure Private DNS zones overview
- App Service Domains (buy domain in Azure)
- nslookup documentation
- dig manual page