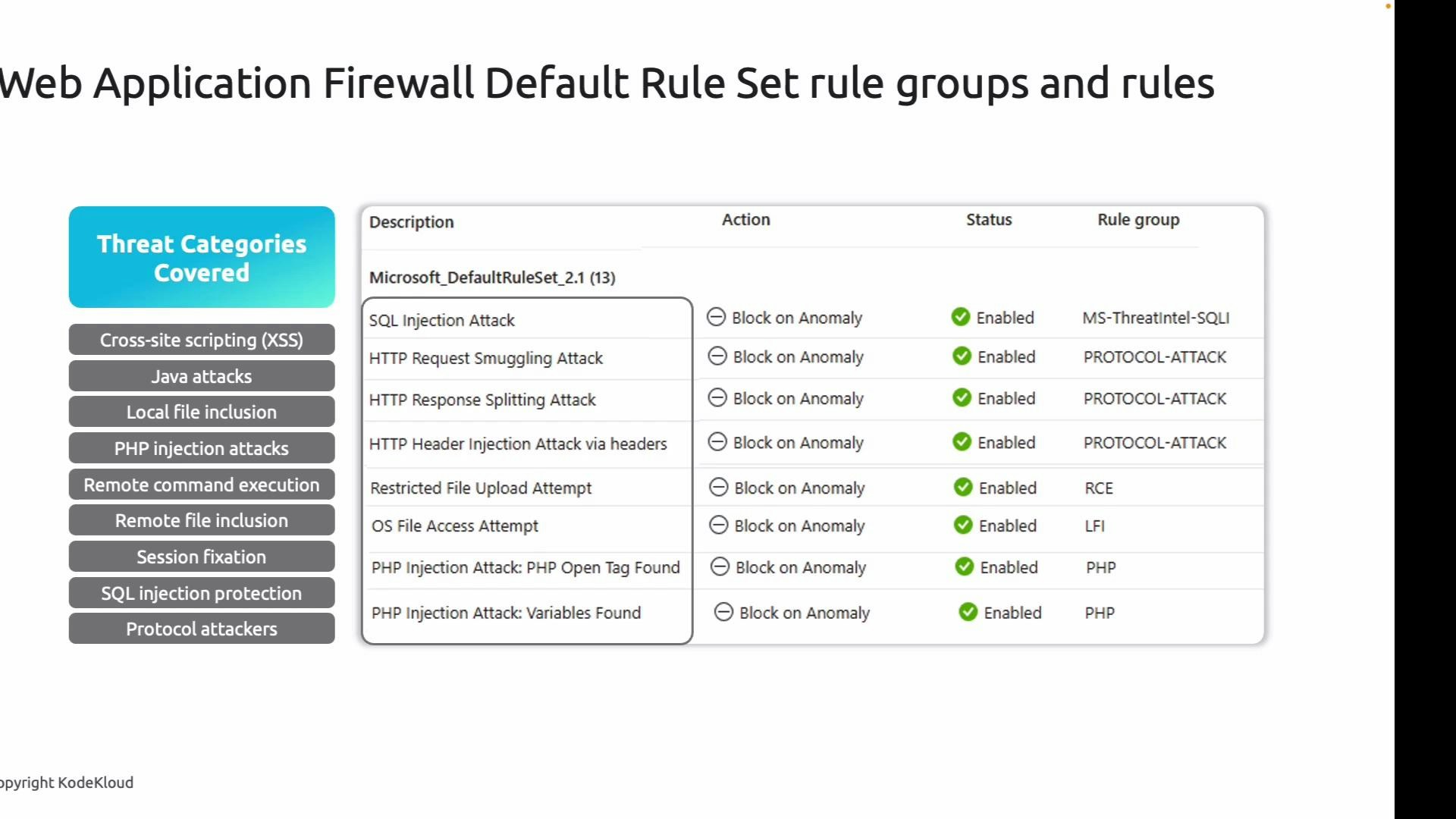
- Cross-site scripting (XSS)
- SQL injection (SQLi) and PHP injection
- Remote code execution (RCE)
- Local file inclusion (LFI) and remote file inclusion
- Java-specific attacks
- Protocol-level attacks such as HTTP request smuggling and response splitting
- Session fixation and other session-related attacks
App setup and vulnerable application
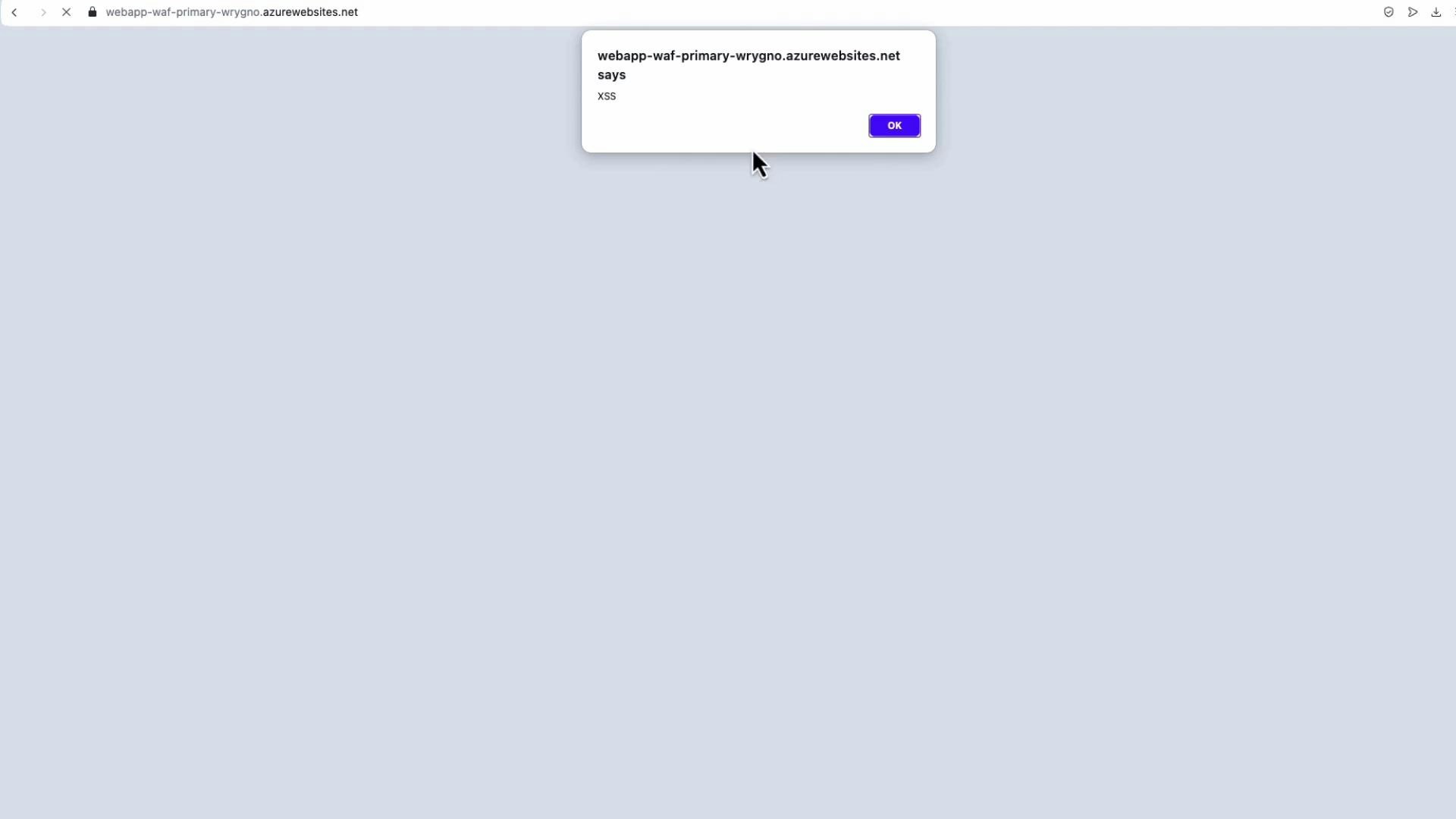
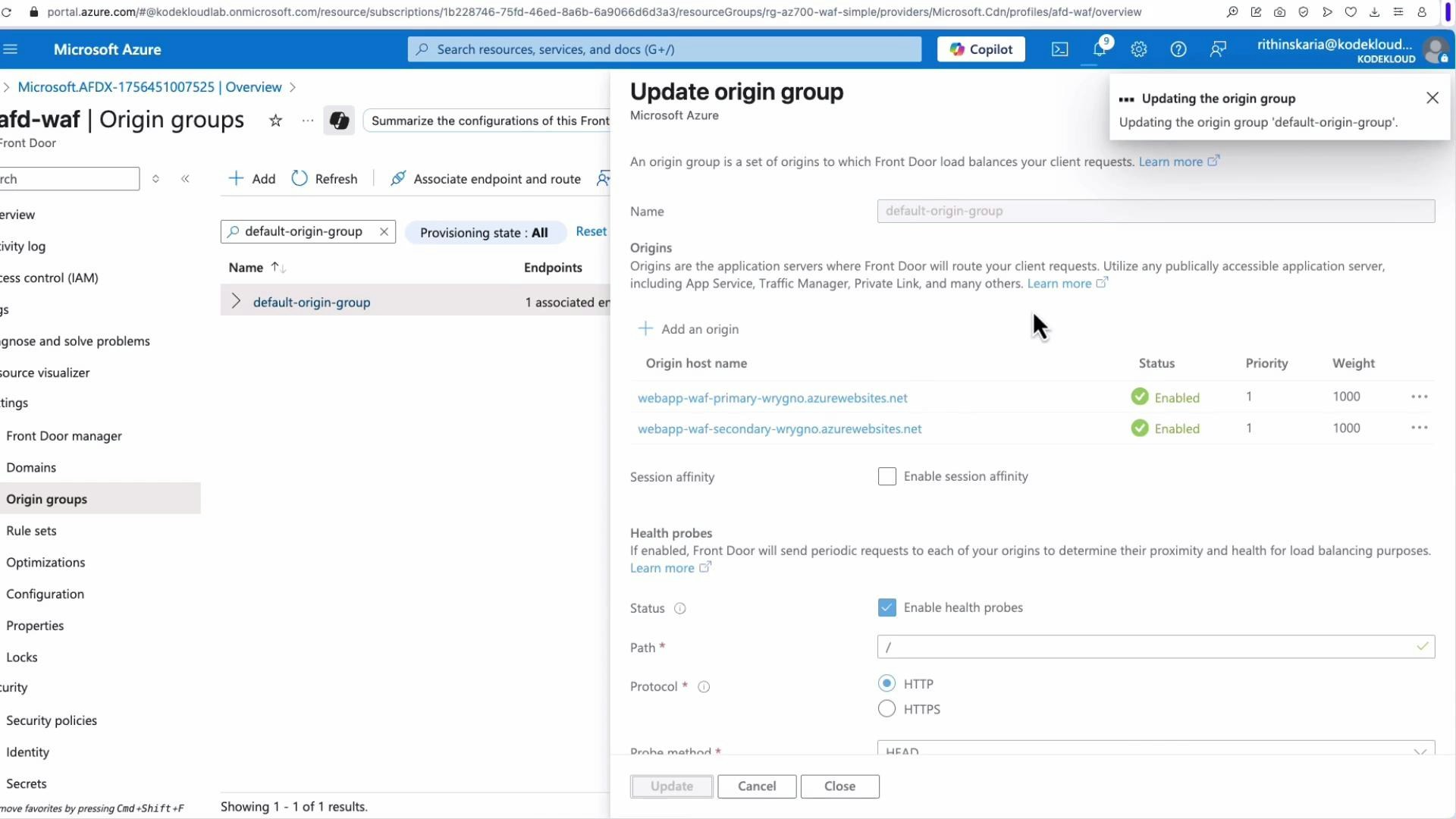
For this demo we use two simple Azure App Services that intentionally contain an XSS vulnerability. Both apps accept text fields (for example, “name” and “comment”) and do not sanitize input, so injecting script payloads executes in the browser. The apps are deployed to two regions (primary in East US and secondary in West Europe) so we can validate global routing and origin failover via Front Door.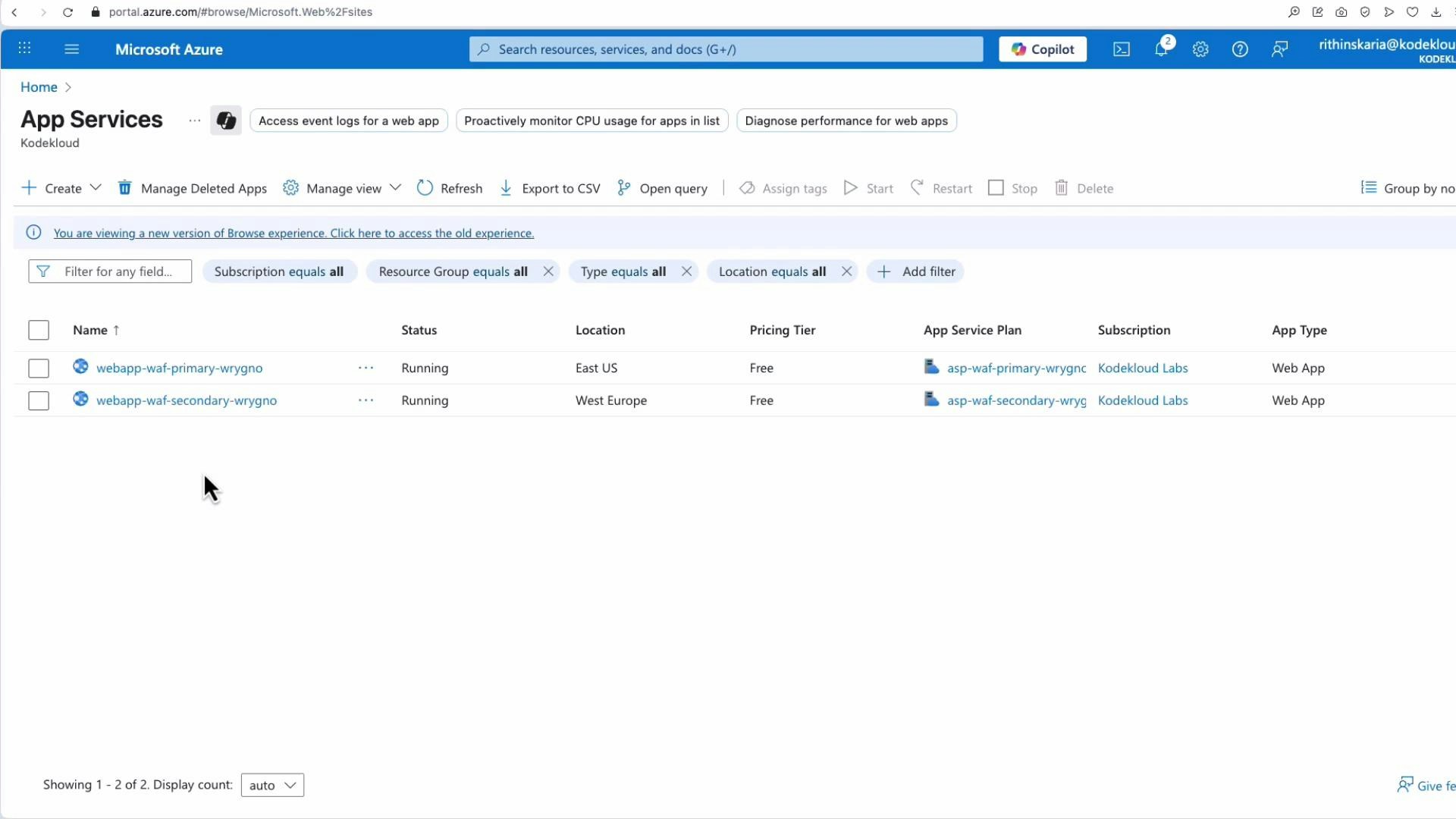
- Use these payloads in the app’s input fields to verify XSS behavior.
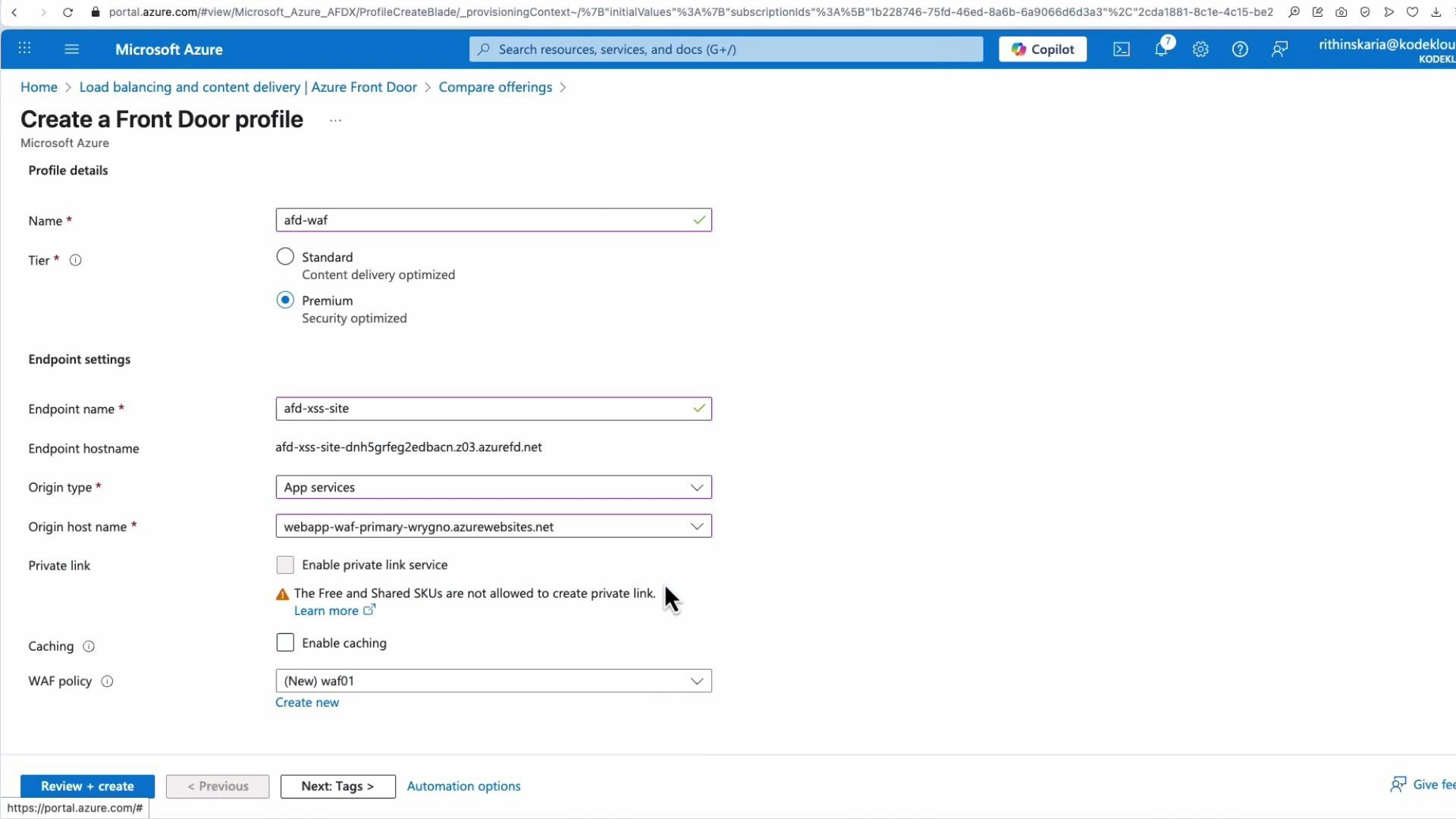
Deploying Front Door with WAF
To protect these apps, create an Azure Front Door (Premium) profile and add the App Services as origins. You can attach an existing WAF policy during Front Door creation or create a WAF policy as a separate resource and associate it with multiple Front Door endpoints for centralized control. When using the Quick Create experience for Front Door:- Choose the Premium tier for WAF and advanced security features.
- Set origin type to “App services” and select your primary web app.
- Optionally create a new WAF policy and attach it during deployment.
WAF policy, associations, and managed rules
Open the WAF policy resource you attached to Front Door. The WAF policy overview shows whether the policy is Enabled and whether it is in Detection (logs only) or Prevention (actively blocks) mode. The Associations section lists the Front Door profiles and endpoints that the policy protects.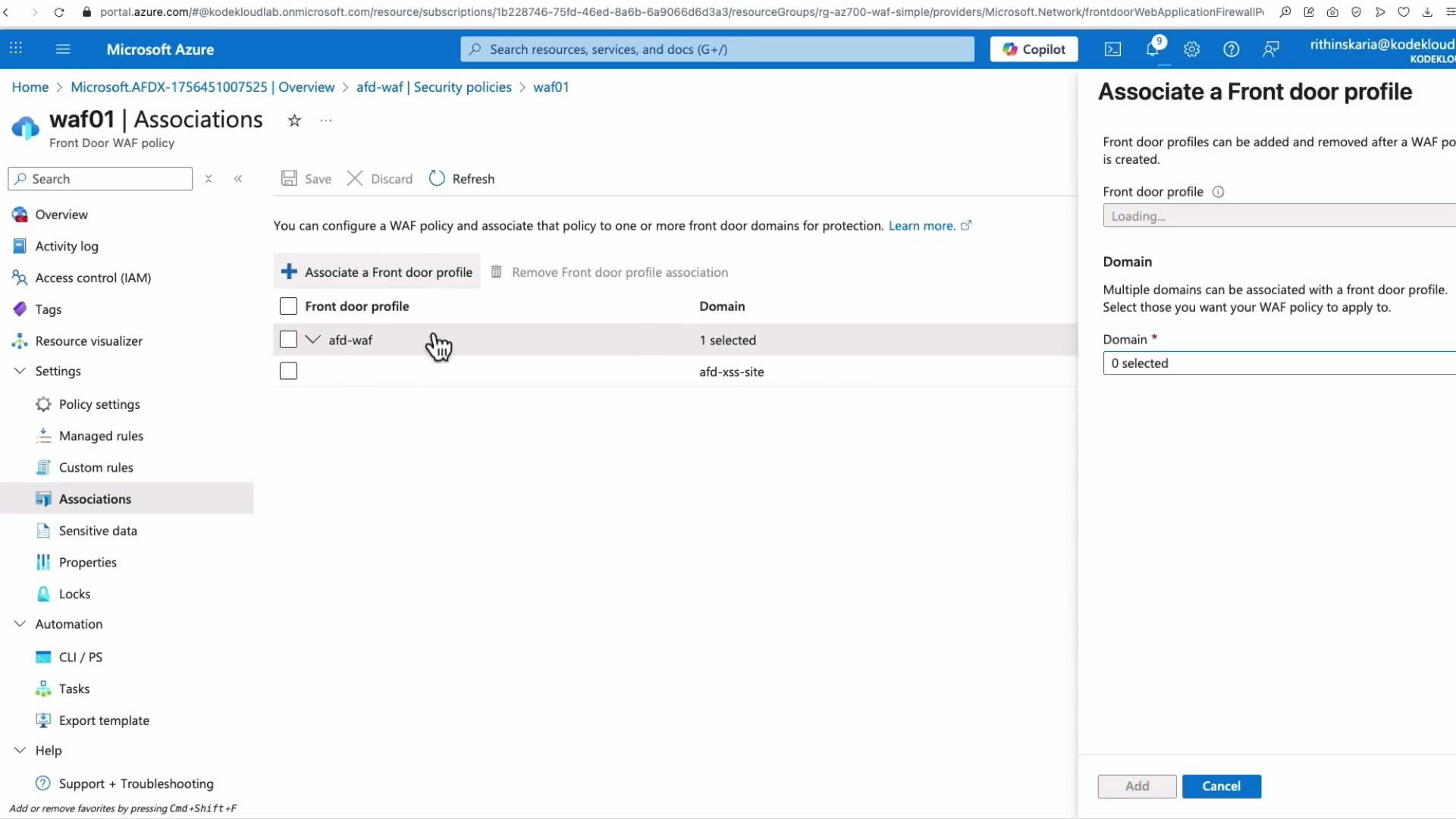
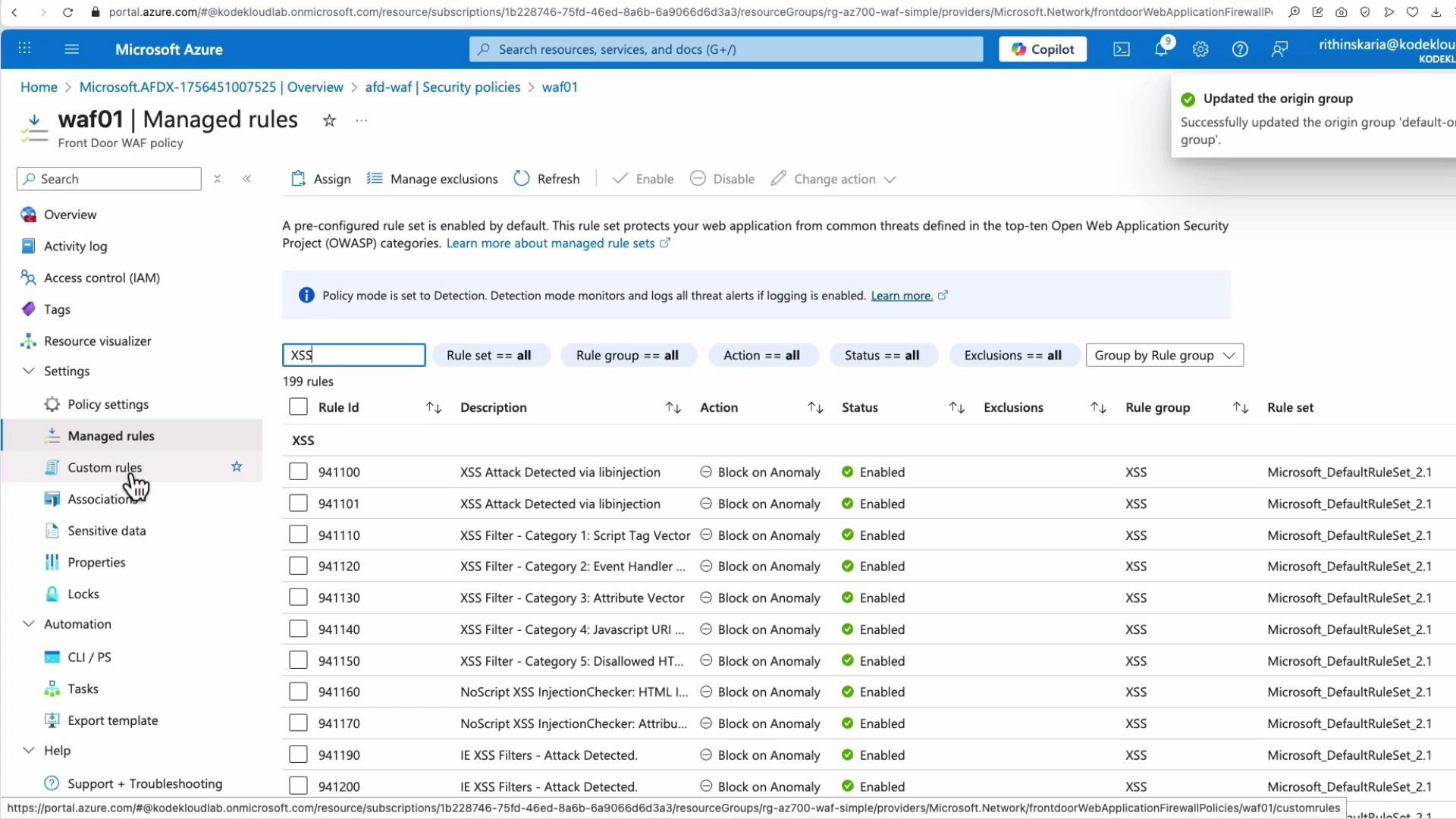
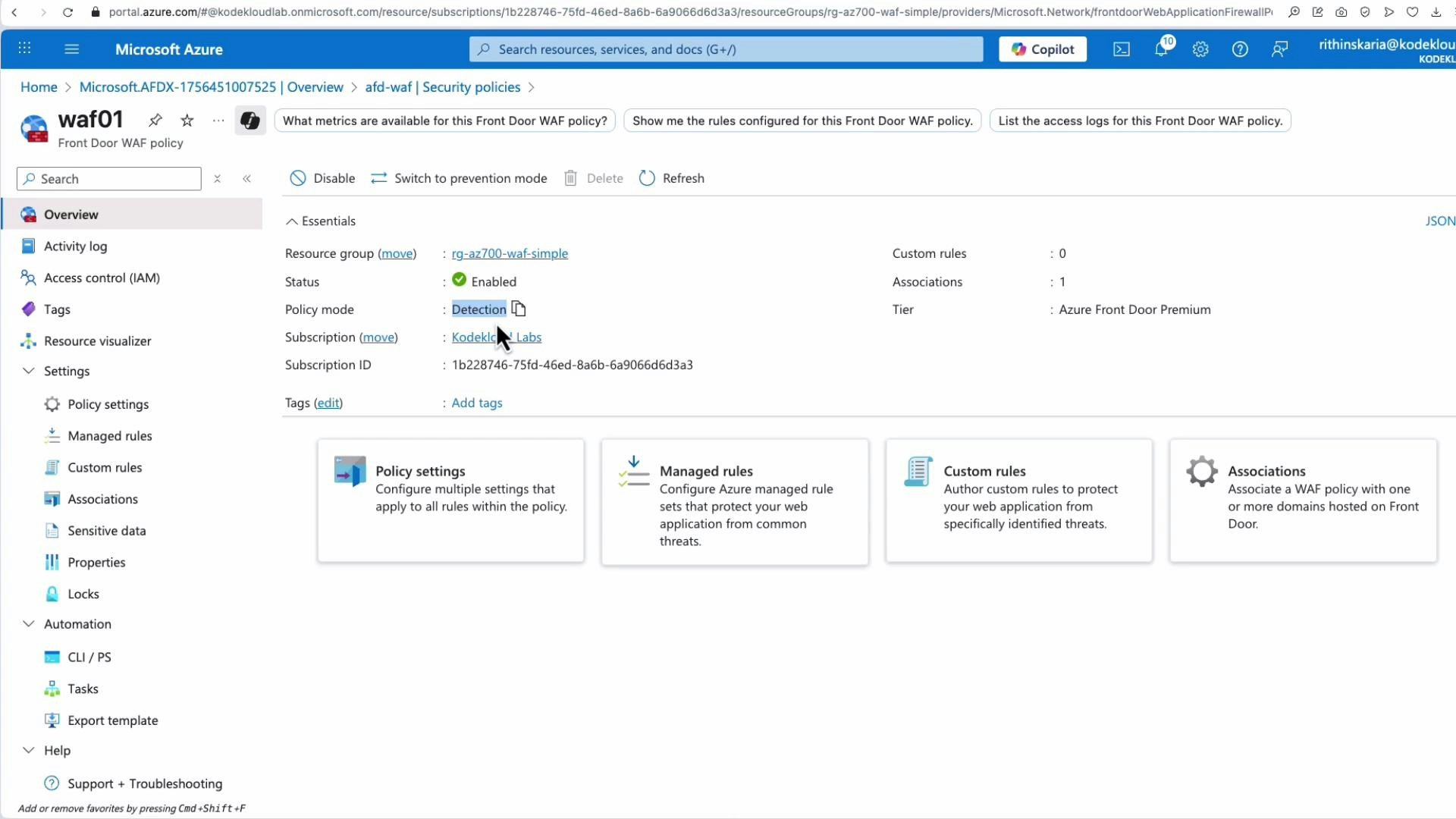
Enable diagnostics (send WAF logs to Azure Monitor/Log Analytics) while in Detection mode to evaluate which managed rules fire against your application before switching to Prevention. This helps avoid false positives impacting legitimate traffic.
- Use this quick reference to understand what the Default Rule Set covers.
| Resource Type | Typical Use Case |
|---|---|
| XSS rules | Block attempts to inject executable script into pages |
| SQLi rules | Detect and block SQL injection payloads |
| RCE / LFI rules | Prevent remote/local file inclusion and code execution patterns |
| Protocol rules | Mitigate HTTP request smuggling, response splitting |
| Language-specific rules | Protect against Java/.NET/PHP-specific vulnerabilities |
| Session rules | Defend against session fixation and related attacks |
Testing the WAF: XSS blocked
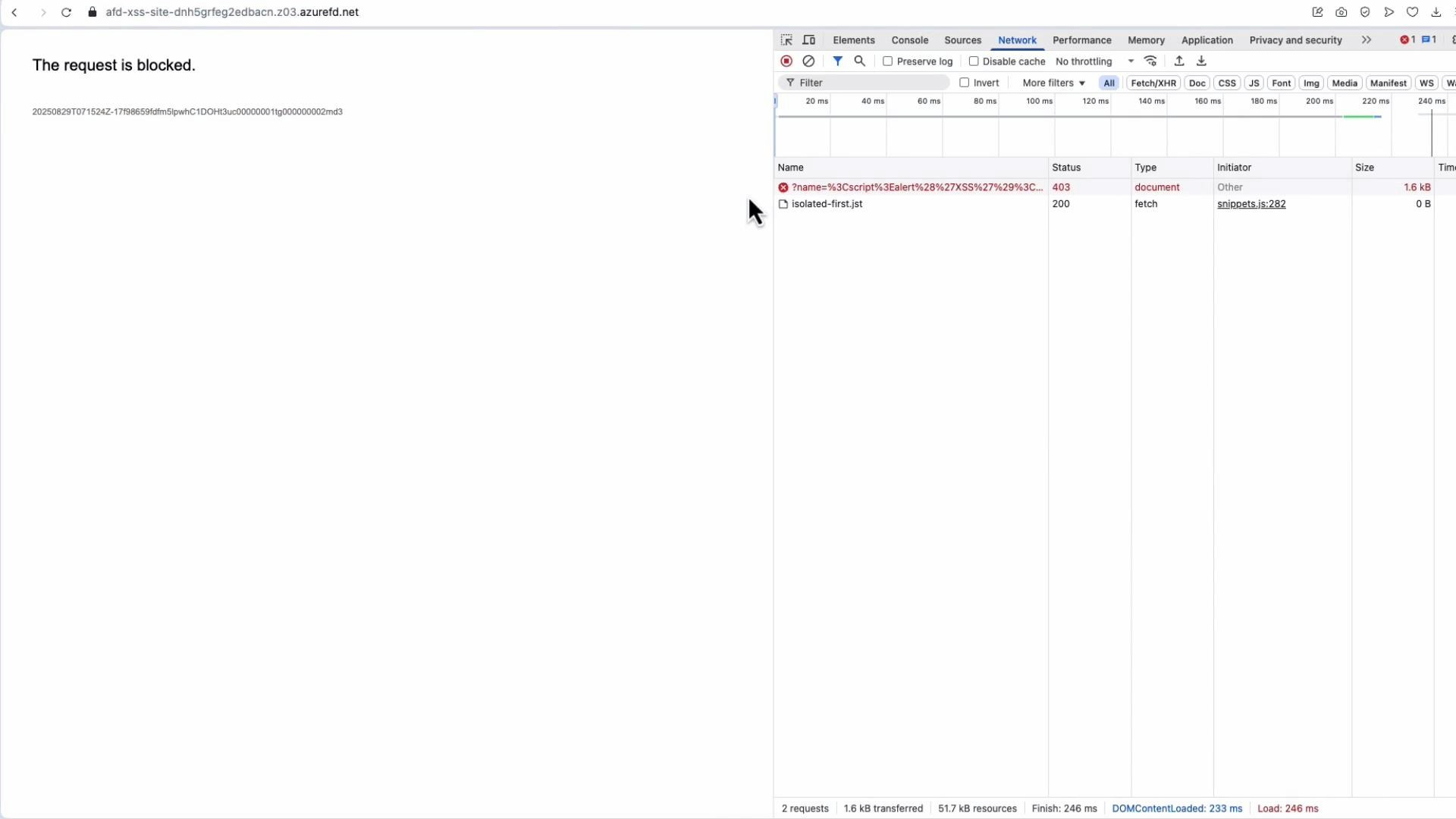
Once Front Door and the WAF policy are associated, and the WAF is set to Prevention mode, submit an XSS payload through the Front Door endpoint to the vulnerable application. The WAF inspects the request and blocks it if it matches an XSS managed rule. When blocked, the browser typically receives an HTTP 403 Forbidden response. Use the browser developer tools (Network tab) to confirm:- The request URL contains the injected payload.
- The response status code is 403.
- Response and request headers indicate the request was intercepted by Front Door/WAF.
Custom rules and other scenarios
Managed rules cover most common threats, but you may need custom rules for scenarios such as:- Geofencing (block or allow traffic by country)
- IP allow/deny lists
- Application-specific exceptions or rate limits
Do not permanently disable certificate validation on origins in production. Disabling certificate validation may be acceptable temporarily for troubleshooting, but it weakens the security of your origin connections and should not be used as a long-term solution.
Summary
- Azure WAF’s Default Rule Set (DRS) provides baseline protections for a wide range of web attacks and is managed and updated by Microsoft.
- Managed rules can be enabled/disabled at both the group and individual rule level to tune security.
- Start in Detection mode with diagnostics to validate which rules fire, then switch to Prevention mode to actively block attacks.
- Use custom rules for specific application requirements (e.g., geofencing or bespoke allowlists). Custom rules take priority over managed rules.
- Deploying Front Door (Premium) + WAF is an effective architecture to protect global web applications (App Services, VMs, and other backends).
- Azure Web Application Firewall: https://learn.microsoft.com/en-us/azure/web-application-firewall/
- Azure Front Door: https://learn.microsoft.com/en-us/azure/frontdoor/
- Azure App Service: https://learn.microsoft.com/en-us/azure/app-service/
- OWASP ModSecurity Core Rule Set: https://owasp.org/www-project-modsecurity-core-rule-set/
- Azure Monitor / Log Analytics: https://learn.microsoft.com/en-us/azure/azure-monitor/logs/log-analytics-overview