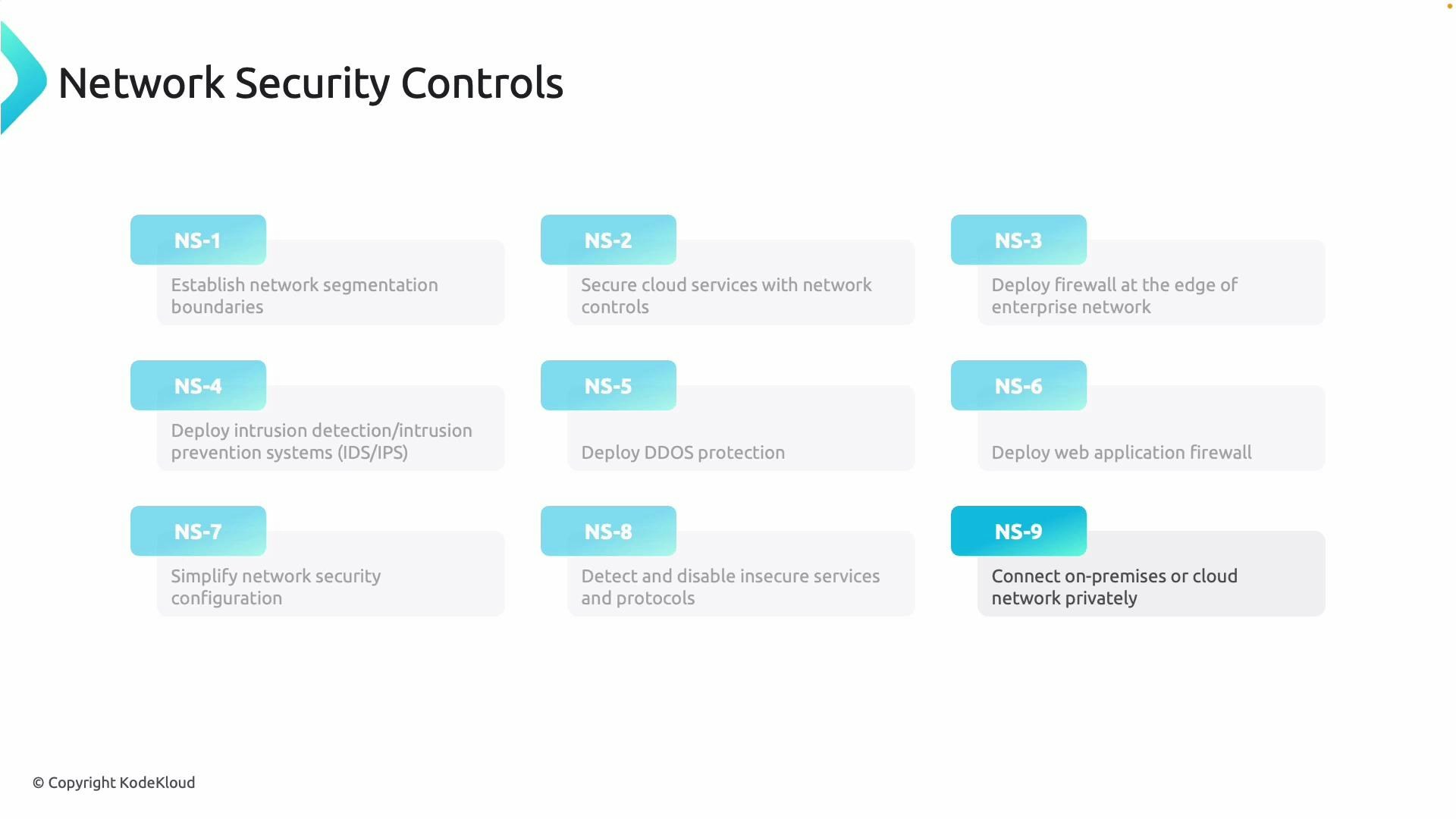
- Reduce the attack surface
- Contain lateral movement
- Protect workloads (VMs, PaaS services, containers)
- Enforce consistent, auditable configurations
| Control | Purpose | Example / Implementation |
|---|---|---|
| Network segmentation | Reduce attack surface and contain lateral movement | Use subnets, VLANs, NSGs, and Azure Firewall to separate zones (web, app, DB) |
| Cloud network controls | Enforce least privilege connectivity and secure access to cloud resources | Network Security Groups (NSGs), Azure Firewall, Private Endpoints |
| Edge firewalls | Filter and inspect inbound/outbound traffic at network boundaries | Perimeter firewall clusters (stateful inspection, application rules) |
| IDS/IPS | Detect and (optionally) block suspicious traffic | Deploy IDS/IPS appliances or hosted services to alert and block threats |
| DDoS defenses | Protect against volumetric and application-layer attacks | Use cloud DDoS protection plans and rate limiting |
| Web Application Firewall (WAF) | Block common web exploits and protect application layer | WAF in front of web apps and API gateways to stop SQLi, XSS, etc. |
| Policy and tooling | Standardize configurations and enable automated enforcement | Azure Policy, security automation, and centralized logging |
| Vulnerability hygiene | Remove or patch unnecessary services; reduce attack vectors | Vulnerability scanning, patching cadence, and hardening baselines |
| Private connectivity | Protect sensitive traffic and avoid the public internet | ExpressRoute, VPN, and encrypted tunnels for private peering and transit |
Microsoft Defender for Cloud maps network and platform controls to built-in security recommendations, simplifying continuous compliance monitoring and remediation planning.
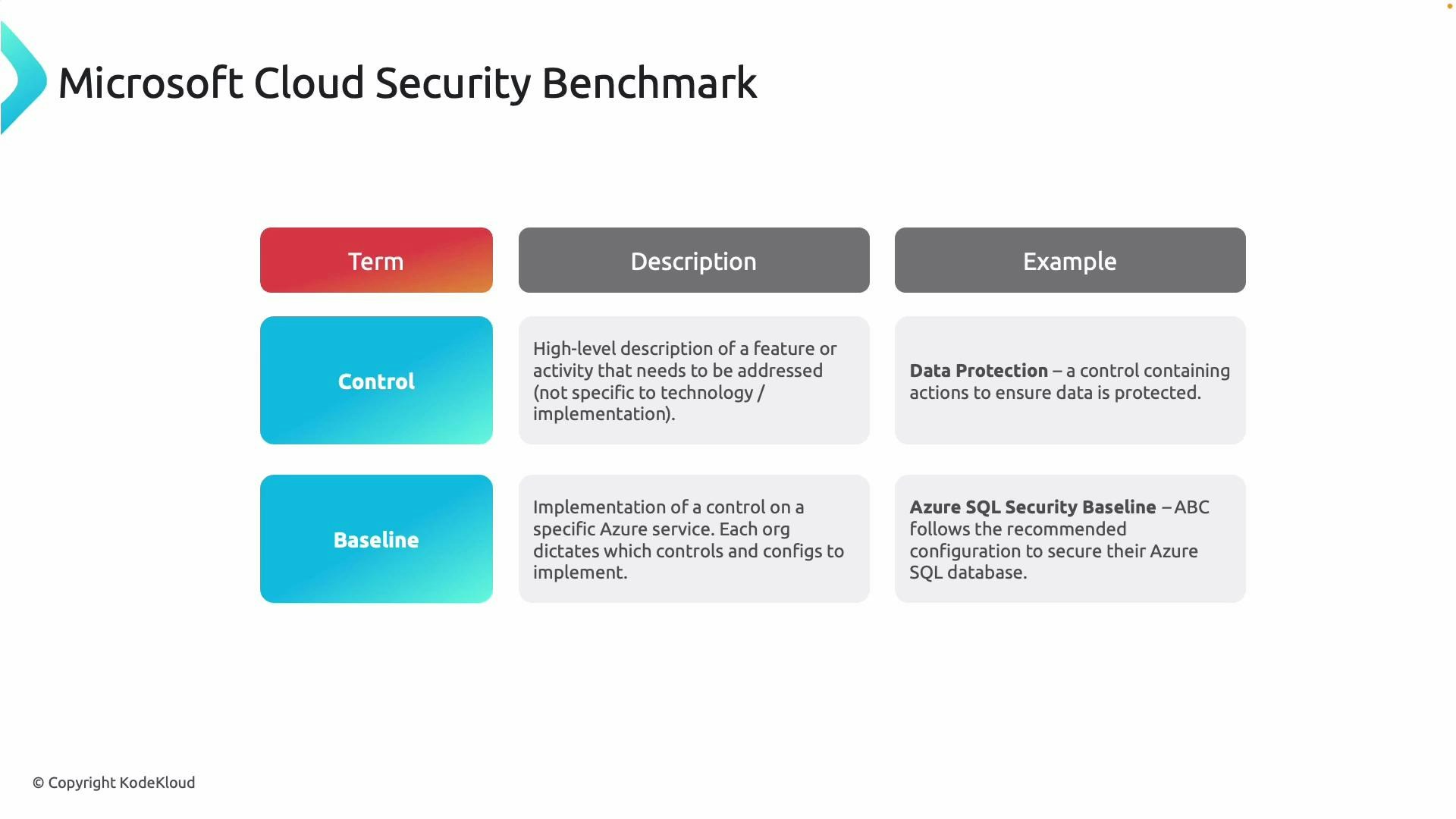
- Control = the high-level requirement (for example, Data Protection).
- Baseline = the exact configuration checks and settings for a service (for example, Azure SQL Security Baseline).
- Control: A high-level security requirement (what to protect).
- Baseline: The service-specific implementation and checks that satisfy the control (how to configure).
- Interpret recommendations in a business context
- Identify responsible stakeholders for remediation
- Implement consistent, repeatable configurations across services
- Microsoft Defender for Cloud — Overview
- Microsoft Cloud Security Benchmark (MCSB)
- Azure ExpressRoute — Private connectivity
- Azure Firewall documentation
- Azure Web Application Firewall (WAF)
Start by mapping high-impact MCSB controls to your most critical services (e.g., databases, web apps, identity systems). Then use Defender for Cloud recommendations and service baselines to implement and automate those controls.