Effective rules are the authoritative view for what security rules are applied to a particular network interface — use them first when troubleshooting connectivity issues involving NSGs.
How Azure evaluates NSG rules
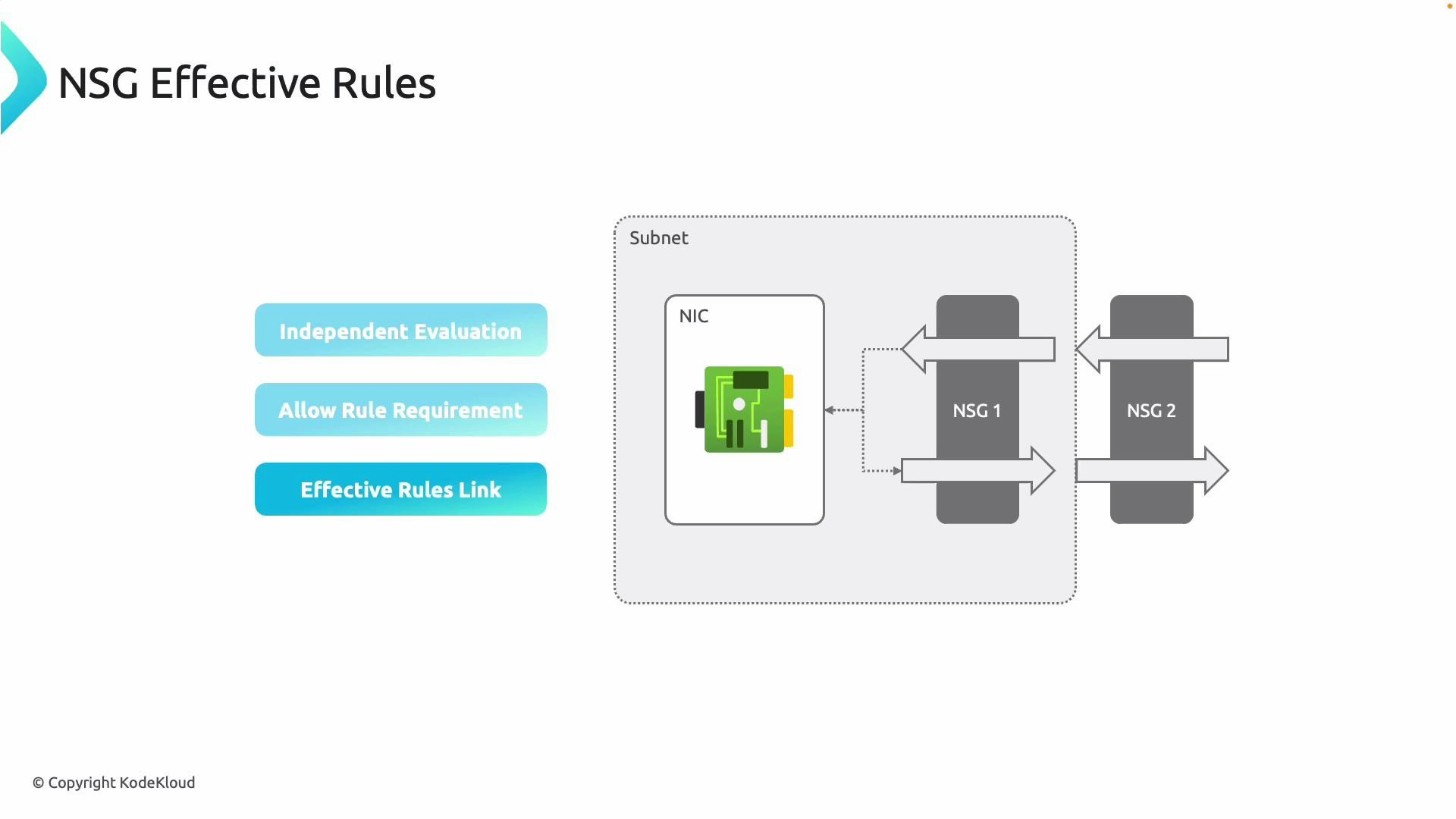
- NSGs are evaluated independently at each scope (subnet and NIC).
- For a packet to be admitted, an allow rule must exist at both scopes. If either scope denies the packet, the packet is blocked.
- Rules are matched by priority (lowest priority number is evaluated first) and stop on the first match per NSG scope. The effective result is the combination of the NIC and subnet evaluations.
Rule evaluation summary (quick reference)
| Scope | What is evaluated | Notes |
|---|---|---|
| Subnet NSG | Rules applied to the entire subnet | Controls traffic for all NICs in that subnet unless overridden/restricted by NIC NSG |
| NIC NSG | Rules applied to the individual network interface | Can further restrict or allow traffic; both NIC and subnet must allow a flow for it to succeed |
| Effective rules | Combined, authoritative view for a NIC | Shows which allow/deny decisions are applied after merging the two scopes |
Viewing effective rules in the Azure portal
To quickly determine why traffic is permitted or blocked for a VM, inspect the effective security rules for the VM’s NIC:- Open the Azure portal.
- Navigate to the Virtual machine and select the VM.
- In the VM blade, select Networking and click the NIC name, or directly open the Network interfaces resource for the target NIC.
- On the NIC resource page, open “Effective security rules” (often under Support + troubleshooting). Azure displays the merged rules that apply to that NIC (including both subnet and NIC NSG rules).
If a deny rule exists at either the subnet or NIC scope, the traffic is blocked even if the other scope contains an allow rule. Always check both the NIC and subnet NSGs (or use the Effective security rules view) before changing rules.
Troubleshooting checklist
- Confirm the VM’s NIC is attached to the expected subnet and that the correct NSGs are associated at both NIC and subnet scopes.
- Open Effective security rules for the NIC to see exactly which rules are in effect (including source/destination, protocol, ports, action, and priority).
- Verify there are no higher-priority deny rules that match the traffic.
- Remember default/system rules exist and may affect flows (the Effective security rules view includes system rules).
- If expected rules aren’t shown, ensure you’re viewing the correct NIC and that any recent NSG changes have propagated.
Best practices
- Prefer simpler rule sets and group related VMs into subnets with shared NSGs to reduce per-NIC complexity.
- Use application security groups (ASGs) to avoid many IP-based rules and keep rules human-readable.
- Audit and document NSG rules and priorities to simplify troubleshooting.
- Use the Effective security rules view as your first step in diagnostics — it reveals the final, evaluated set of rules.
References and further reading
- Azure Network Security Groups overview
- Azure Network Watcher overview — Network Watcher features help with connectivity and NSG diagnostics
- For step-by-step portal screenshots and additional troubleshooting commands, see Azure documentation linked above.