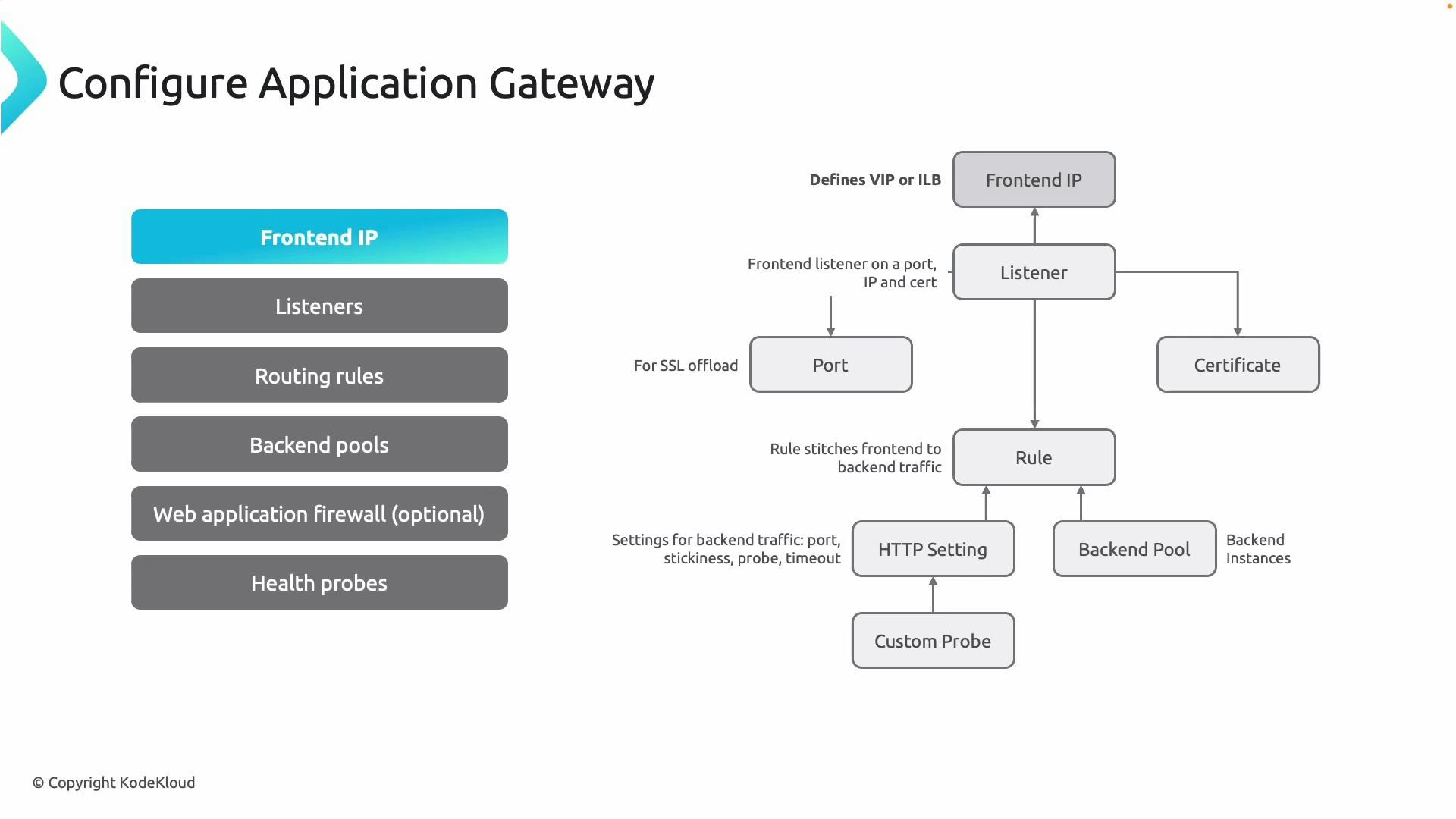
High-level component responsibilities
Use this table to quickly understand each component’s purpose when designing or documenting an Application Gateway deployment.| Component | Responsibility | Typical configuration notes |
|---|---|---|
| Front-end IP | Receives client traffic (Public or Private) | Assign a Public IP for internet-facing apps or a Private IP for internal-only access |
| Listener | Entry point binding (frontend IP + port + optional TLS cert) | Use port 80 for HTTP, 443 for HTTPS; SNI/host headers supported for multi-site routing |
| Routing rule | Routes request from listener to backend pool + HTTP settings | Choose basic, path-based, or host-based rules to direct traffic |
| Backend pool | Collection of backend targets (VMs, VMSS, IPs, App Services) | Backend targets are referenced by NIC, IP, or App Service resource |
| HTTP settings | How gateway communicates with backends (port, protocol, timeouts, affinity) | Attach health probes and configure cookie affinity or connection draining as needed |
| Health probe | Verifies backend health before sending traffic | Use default or custom probes (path, host header, intervals, match criteria) |
| Web Application Firewall (WAF) | Optional protection from common web vulnerabilities | Available on WAF SKU (WAF_v2), apply managed or custom rules |
WAF is optional — deploy Application Gateway with the Standard_v2 SKU if WAF features are not required. Choose WAF_v2 when you need built-in OWASP protections and custom rule support.
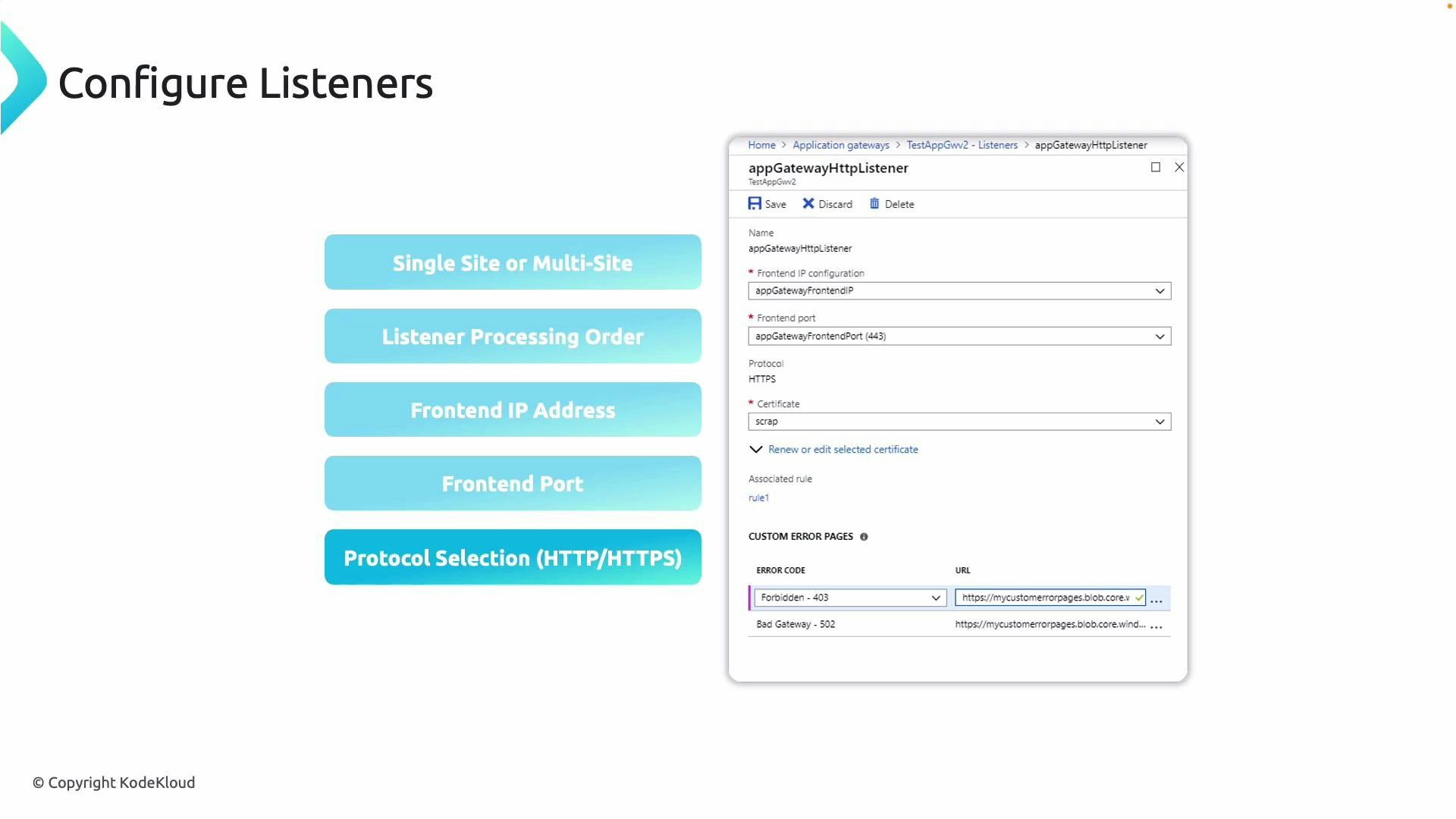
Front-end IP and listeners
The front-end IP and listeners define how clients connect to the gateway and initiate requests that the gateway will route.- Front-end IP: Exposes either a Public IP (internet-facing) or a Private IP (internal) to receive traffic.
- Listener: Binds a front-end IP, port, and optionally a TLS/SSL certificate. It is the match target for incoming requests.
- Use port 80 for HTTP and port 443 for HTTPS.
- For HTTPS, upload the TLS certificate to the listener for SSL/TLS termination (offload), or configure end-to-end encryption (re-encryption) if the backend requires TLS.
- Listener types:
- Single-site (basic) listener — serves one site or host.
- Multi-site listener — uses host headers (SNI) to host multiple domains on the same frontend.
- Listener processing: The gateway matches incoming requests to listeners by front-end IP, port, and host name. When multiple listeners could match, the most specific match is selected (for example, a listener that specifies a host name). URL path maps and routing rules then determine the backend selection.
Listeners connect to backends via routing rules
Routing rules are the bridge between what the gateway receives and where it forwards requests.- A routing rule ties a listener to:
- A backend pool (the targets that will receive traffic)
- HTTP settings (how the gateway communicates with those targets)
- Routing rule types:
- Basic rule — maps one listener to one backend pool.
- Path-based rule (URL path map) — routes different URL paths (for example /images, /api) to different backend pools.
- Host-based routing — used with multi-site listeners to route based on host headers.
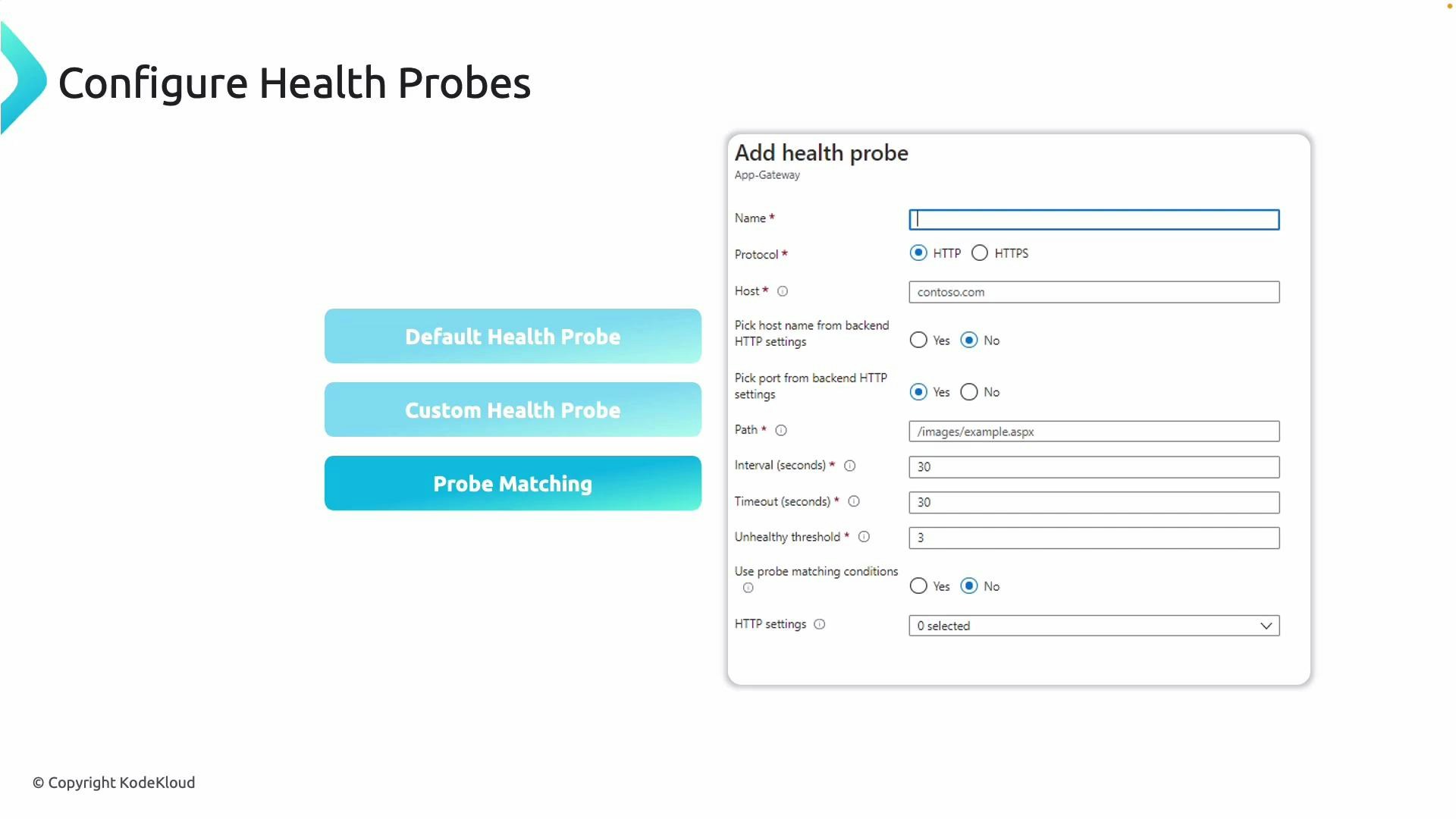
Health probes
Health probes ensure the gateway only sends traffic to healthy backend endpoints.- Use either the default probe or create a custom probe tuned to your application’s health endpoint.
- Custom probe options:
- Protocol: HTTP or HTTPS
- Host header: specify the host to send in the probe request
- Path: the URL path to check (for example /health or /status)
- Interval: time between probes
- Timeout: probe response timeout
- Unhealthy threshold: number of failed probes before marking unhealthy
- Match criteria: status codes or response body match conditions considered healthy
- Associate probes with HTTP settings that are used by your routing rules to ensure probe logic matches actual application behavior.
Configuration sequence — recommended steps
Follow this sequence when creating or updating an Application Gateway to ensure a predictable, testable deployment:- Create or select the front-end IP (Public for internet-facing, Private for internal).
- Add listeners; upload TLS certificates if terminating TLS at the gateway.
- Create backend pools and reference your targets (VMs, VMSS, App Services, or IPs).
- Configure HTTP settings and associate a health probe that matches your application endpoints.
- Create routing rules (basic, path-based, or multi-site) to map listeners to backend pools and HTTP settings.
- Optionally enable WAF and attach WAF policies if web protection is required.
- Validate with health probe status, gateway diagnostic logs, and end-to-end functional tests.
Useful links and references
- Azure Application Gateway documentation
- Application Gateway v2 SKU and features
- Web Application Firewall on Application Gateway (WAF)
- Configure health probes for Application Gateway