- How policies are managed and deployed
- Applying a single policy across multiple hubs or VNets
- Cross-subscription and cross-region support
- Layered policy model for central baseline + local refinements
Policy management: flexible tooling and automation
Policies can be created and managed using the Azure Portal, REST API, ARM templates, Azure PowerShell, and Azure CLI. This flexibility enables teams to adopt manual management, Infrastructure as Code (IaC), or automation pipelines according to their operational model.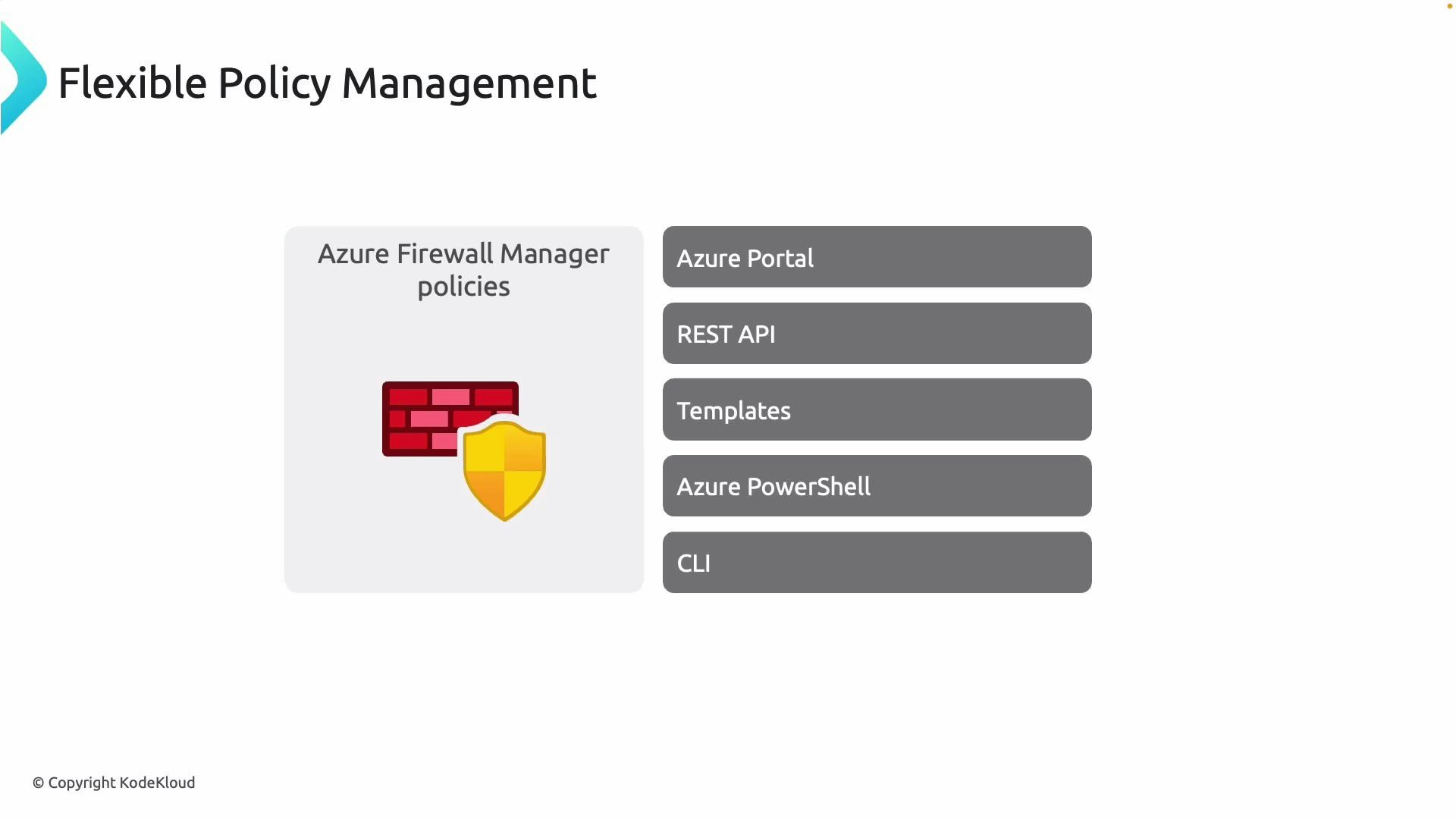
- Quick experiments or small deployments: Azure Portal
- Automated, repeatable deployments: ARM templates, PowerShell, CLI
- Integration in pipelines: REST API and IaC workflows
Association with multiple hubs or VNets
A single firewall policy can be applied to many firewall instances, vHubs, or virtual networks. This lets you enforce a consistent security baseline across environments without duplicating configurations per subscription or region.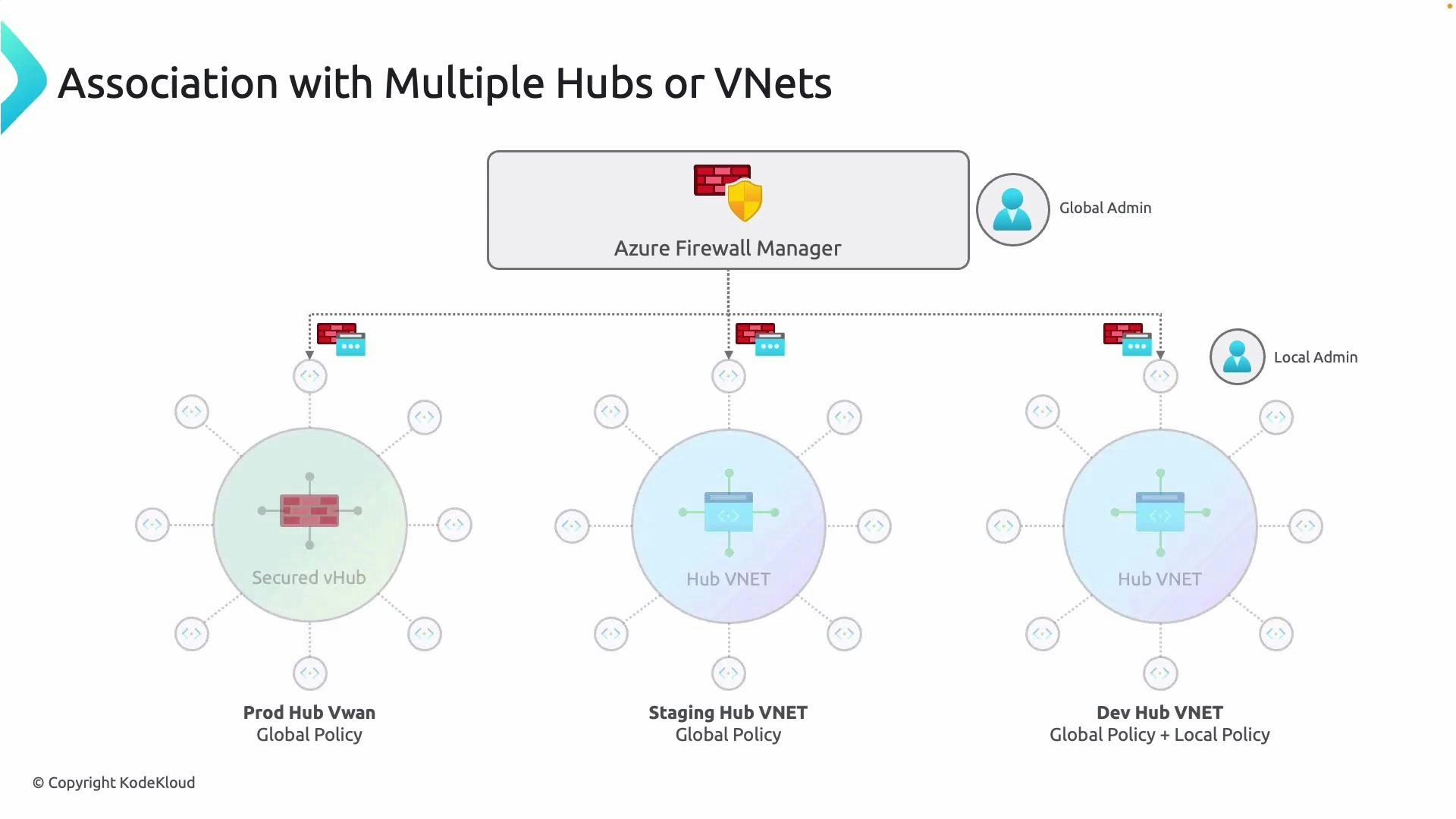
- Apply shared baseline policies centrally to reduce configuration drift.
- Use targeted local policies only where environment-specific controls are required.
Cross-subscription and regional support
Within the same Azure AD tenant, Firewall Manager policies can span subscriptions and regions. This makes it straightforward for large organizations to maintain consistent controls across different business units, subscriptions, or geographic locations. Benefits:- Centralized governance and auditing
- Reduced administrative overhead
- Consistent compliance posture across environments
Layered policy model (central baseline + local refinement)
Firewall Manager supports a layered model where global (central) policies provide a baseline and local policies add environment-specific rules. This balances centralized control with the flexibility local teams need.Global (central) policies are typically used for baseline enforcement. Local policies allow environment-specific additions or refinements. When multiple policies apply (for example a child/local policy and its base/global policy), rules in the child (local) policy are evaluated before the base (global) policy; within each policy, rule collection priorities determine the order in which rules are processed.
- Define high-level deny/allow baselines and logging at the central level.
- Let local admins add allow rules for approved services or refine priorities to meet local needs.
- Carefully design rule collection priorities to avoid unintended shadowing of critical rules.
Quick reference: Firewall Manager policy capabilities
| Capability | What it does | Recommended usage |
|---|---|---|
| Multi-tool management | Create/manage policies via Portal, REST API, ARM templates, PowerShell, CLI | Choose Portal for ad-hoc changes; use IaC and API for automation and CI/CD |
| Multi-hub/VNet association | Apply one policy to many firewall instances or hubs | Use a single policy for baseline controls across environments |
| Cross-subscription & regional | Policies span subscriptions & regions within the same tenant | Centralized governance for large estates |
| Layered policy model | Combine global baseline with local child policies | Central enforcement + limited local customizations |
| Rule collection priorities | Determine processing order within a policy | Plan priorities to ensure expected rule evaluation and avoid conflicts |
Design considerations and best practices
- Use a central policy to enforce logging, threat intel, and broad deny rules.
- Keep local policies minimal and scoped—avoid duplicating central rules.
- Test policy changes in a staging environment before deploying broadly.
- Automate deployments with ARM templates or CI/CD for repeatability and traceability.
- Monitor rule hit counts and logs to iteratively refine priorities and reduce unnecessary rules.