How internal name resolution works
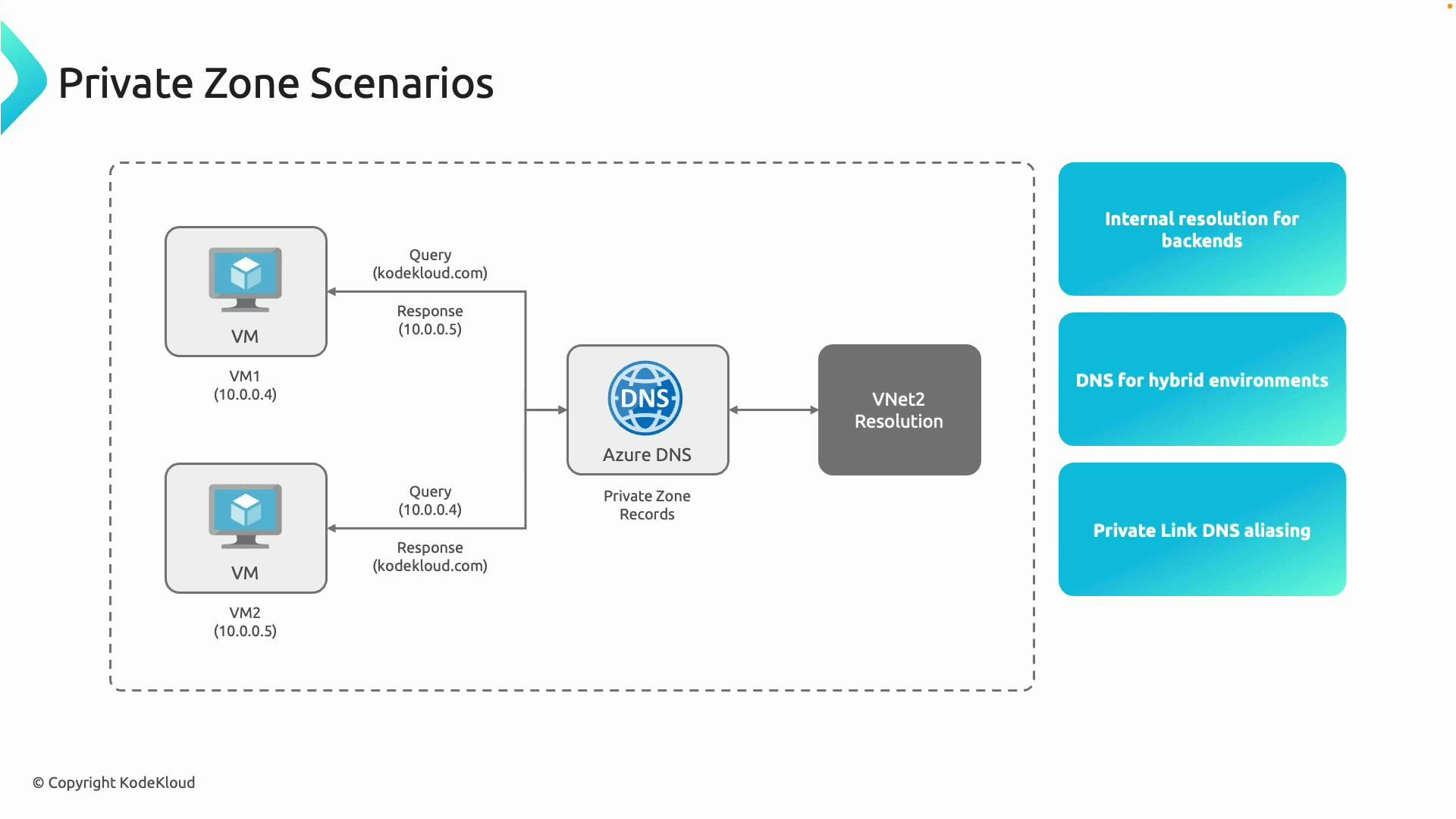
- A VM inside your virtual network issues a DNS query for a name such as
sql.kodekloud.com. - Azure DNS checks the appropriate Private DNS Zone for that record and returns the corresponding private IP (for example,
10.0.0.4). - The VM connects to the resource using the returned private IP, keeping traffic internal to Azure.
- Applications and VMs receive the correct internal addresses automatically, so you don’t need to expose internal services with public IPs.
Key scenarios and benefits
| Scenario | Benefit | Example / Action |
|---|---|---|
| Shared resolution across VNets | Centralized name resolution for multiple VNets | Link multiple VNets to a single Private DNS Zone so resources in different VNets can resolve each other’s names. |
| Hybrid DNS integration | On-premises systems can resolve Azure private names | Configure conditional forwarding from on-premises DNS servers to Azure Private DNS Zones. |
| Private Endpoint DNS | Private access to PaaS services with private DNS records | Private Endpoints can auto-create records in your private zone so services stay private and resolvable by name. |
Virtual Network Links are required: a Private DNS Zone must be linked to the virtual networks that need to resolve names from that zone. Without linking, VMs in a VNet cannot resolve records from the Private DNS Zone.
The special Azure reserved IP: 168.63.129.16
Azure exposes a fixed, well-known IP address — 168.63.129.16 — that is reachable from all VMs and platform resources inside Azure (it is not reachable from the public internet). This address is used by several platform services, including:- VM agent communication: the Azure VM Agent reports status and health to the Azure platform via this IP.
- DNS resolution: by default, VMs use this IP for DNS if no custom DNS server is configured at the VNet or NIC level.
- DHCP metadata: VMs obtain private IP and network configuration via DHCP interactions with this address.
- Health probes and load balancer interactions: Azure platform health probes and other services may rely on it.
Never block 168.63.129.16. Blocking this address can break DNS, VM agent reporting, DHCP, health probes, and other core Azure platform services.
Using custom DNS servers
If you prefer not to use the platform DNS at 168.63.129.16, configure a custom DNS server at the VNet or NIC level. Typical options include:- Windows DNS server (Active Directory domain controller)
- BIND (https://www.isc.org/bind/)
- Commercial appliances (for example, Infoblox — https://www.infoblox.com)
Next steps
- Configure DNS settings for your VNets (VNet-level or NIC-level DNS server settings).
- Create Private DNS Zones and link the appropriate VNets.
- Use Private Endpoints to automatically populate DNS records in your Private DNS Zone.
- Implement conditional forwarding between on-premises DNS and Azure for hybrid name resolution.
Links and references
- Azure Private DNS Zones: https://learn.microsoft.com/azure/dns/private-dns-overview
- Private Endpoints and DNS integration: https://learn.microsoft.com/azure/private-link/private-endpoint-dns
- What is IP 168.63.129.16: https://learn.microsoft.com/en-us/azure/virtual-network/what-is-ip-address-168-63-129-16
- Azure Virtual Network documentation: https://learn.microsoft.com/azure/virtual-network