Public vs Internal load balancers
- Public load balancer: receives traffic from the internet using a public IP and distributes it to backend virtual machines. Use when a workload requires external access (for example, public-facing web apps or APIs).
- Internal load balancer: balances traffic privately inside a virtual network. Use for services that must remain internal (for example, backend APIs, databases, or microservices not exposed to the internet).
| Load Balancer Type | Typical Use Cases | How it Appears on the Network |
|---|---|---|
| Public Load Balancer | External web apps, public APIs, CDN front-ends | Exposes a public IP; internet consumers connect directly |
| Internal Load Balancer | Backend tiers, internal APIs, database access | Uses private IPs within a VNet; only reachable from within the VNet or via peering/VPN/ExpressRoute |
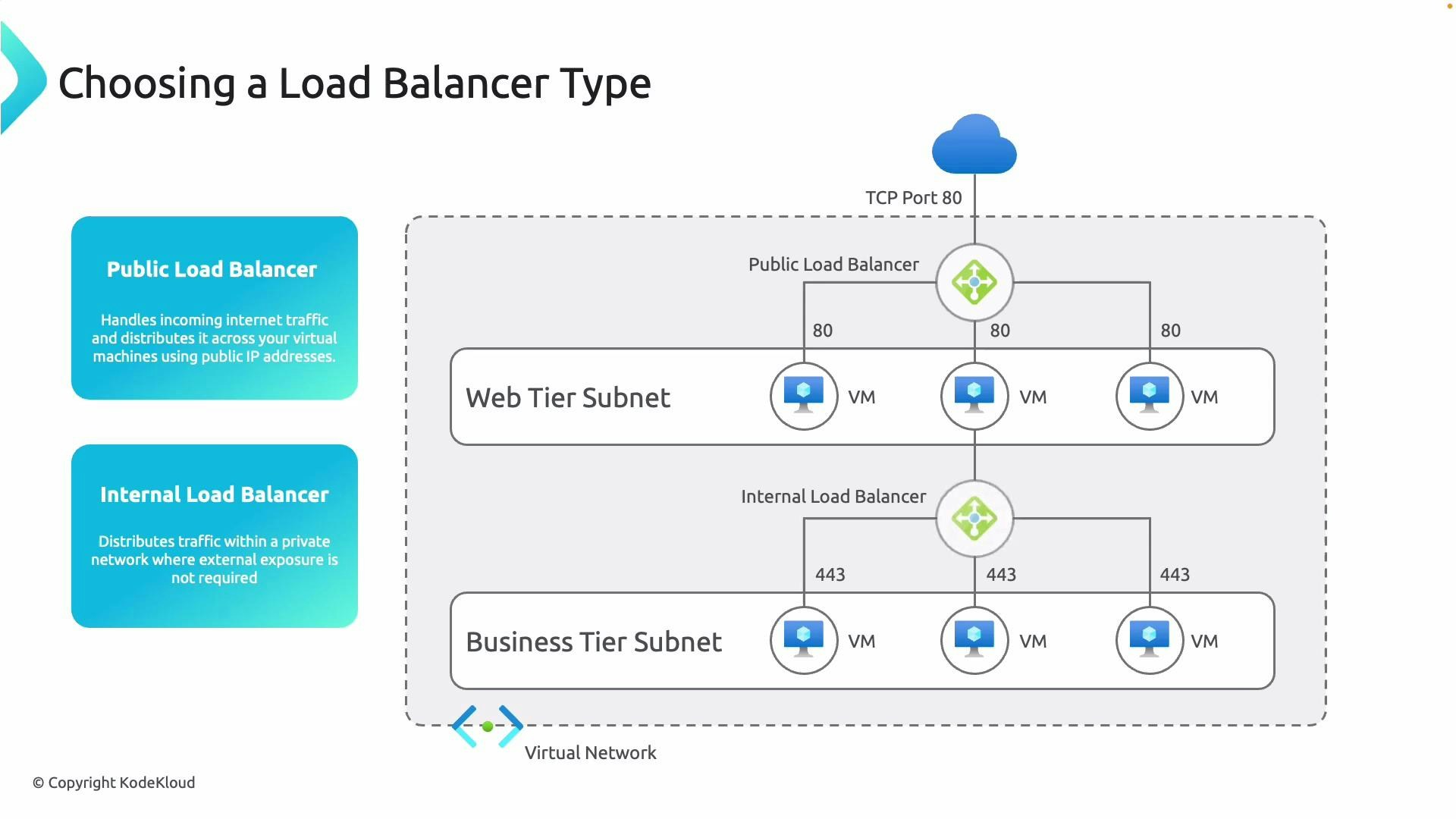
- Limit external exposure and reduce attack surface
- Apply security controls (NSGs, firewalls) per tier
- Optimize routing, scaling, and performance for each layer
Gateway Load Balancer (GWLB)
Gateway Load Balancer is designed to insert third-party Network Virtual Appliances (NVAs) — such as virtual firewalls, IDS/IPS, or other security appliances — into your traffic path. It preserves flow affinity, supports transparent inspection, and enables chaining multiple NVAs while providing high availability and throughput. In typical GWLB deployments, unfiltered traffic from the internet (or between networks) is routed through the gateway load balancer to provider NVAs for inspection. NVAs apply filtering and policies, then forward the filtered traffic to application endpoints.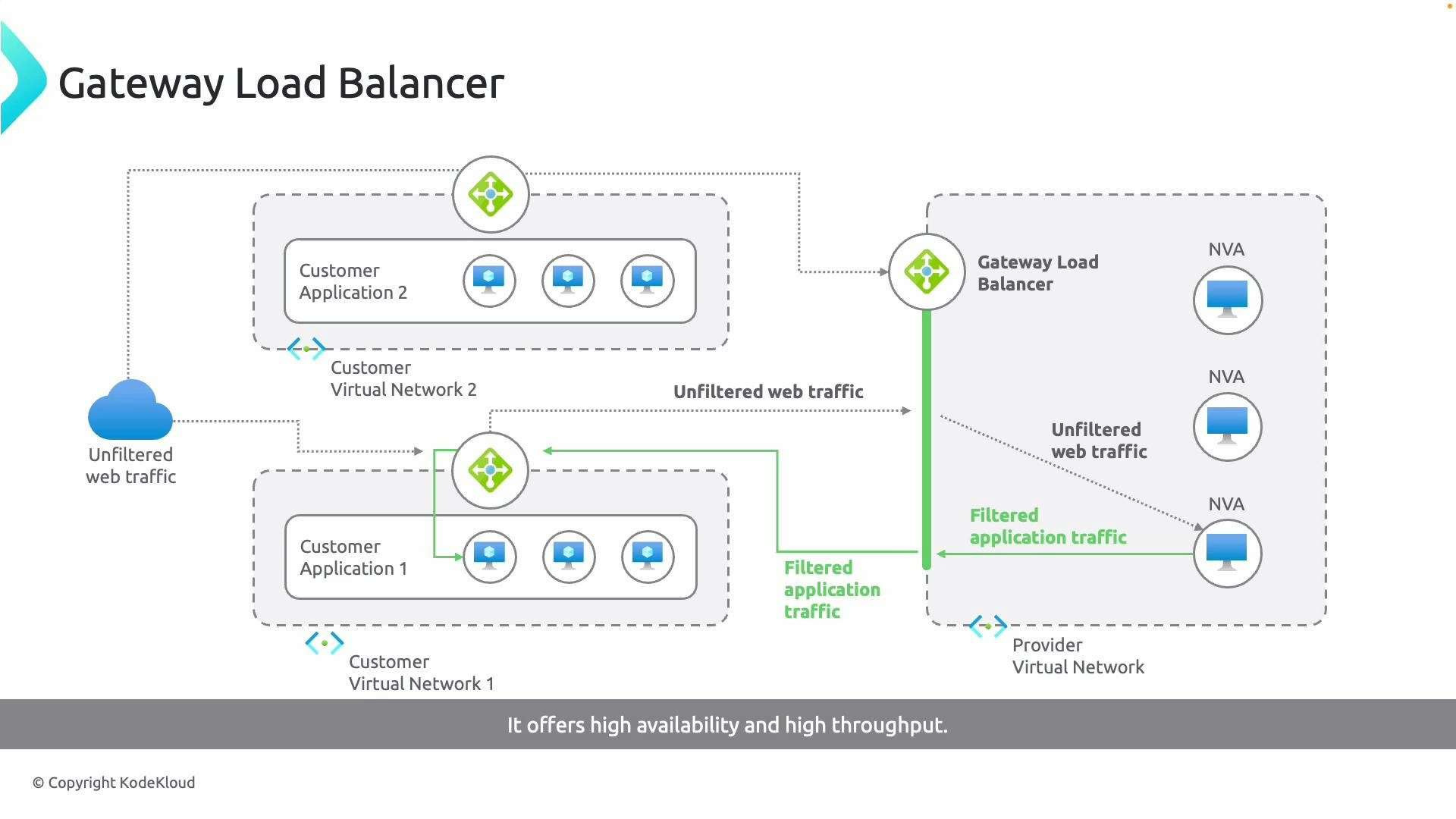
Gateway Load Balancer adds operational complexity and cost: you must deploy, manage, and license NVAs. Ensure routing, encapsulation (tunnels), and health checks are tested end-to-end. GWLB is ideal when you require inline inspection, third‑party security features, or service chaining.
- Front-end IP: receives incoming traffic from consumers.
- Load-balancing rules: define packet distribution to backend pools.
- Backend pools (backend resources): the NVAs or instances that inspect traffic.
- Tunnel interfaces: encapsulate traffic to deliver it directly to NVAs.
- Chaining: route traffic through multiple NVAs in sequence for layered inspection.
Load Balancer SKUs: Basic vs Standard
Azure Load Balancer comes in two SKUs: Basic and Standard. Each SKU differs in scale, features, availability, and default security posture. Choose the SKU that matches your workload requirements for throughput, resiliency, and security.| Capability | Basic SKU | Standard SKU |
|---|---|---|
| Backend pool size | Up to 300 IP configurations | Up to 5,000 backend instances |
| Health probes | TCP, HTTP | TCP, HTTP, HTTPS |
| Availability | No zone redundancy / limited availability guarantees | Zonal and zone‑redundant deployments supported |
| Multiple frontends | No | Yes — multiple front-end IP configurations |
| Security defaults | Less restrictive; NSGs optional | Secure by default: inbound flows blocked unless NSG allows; internal VNet flows allowed |
| SLA | None | 99.99% SLA for supported configurations |
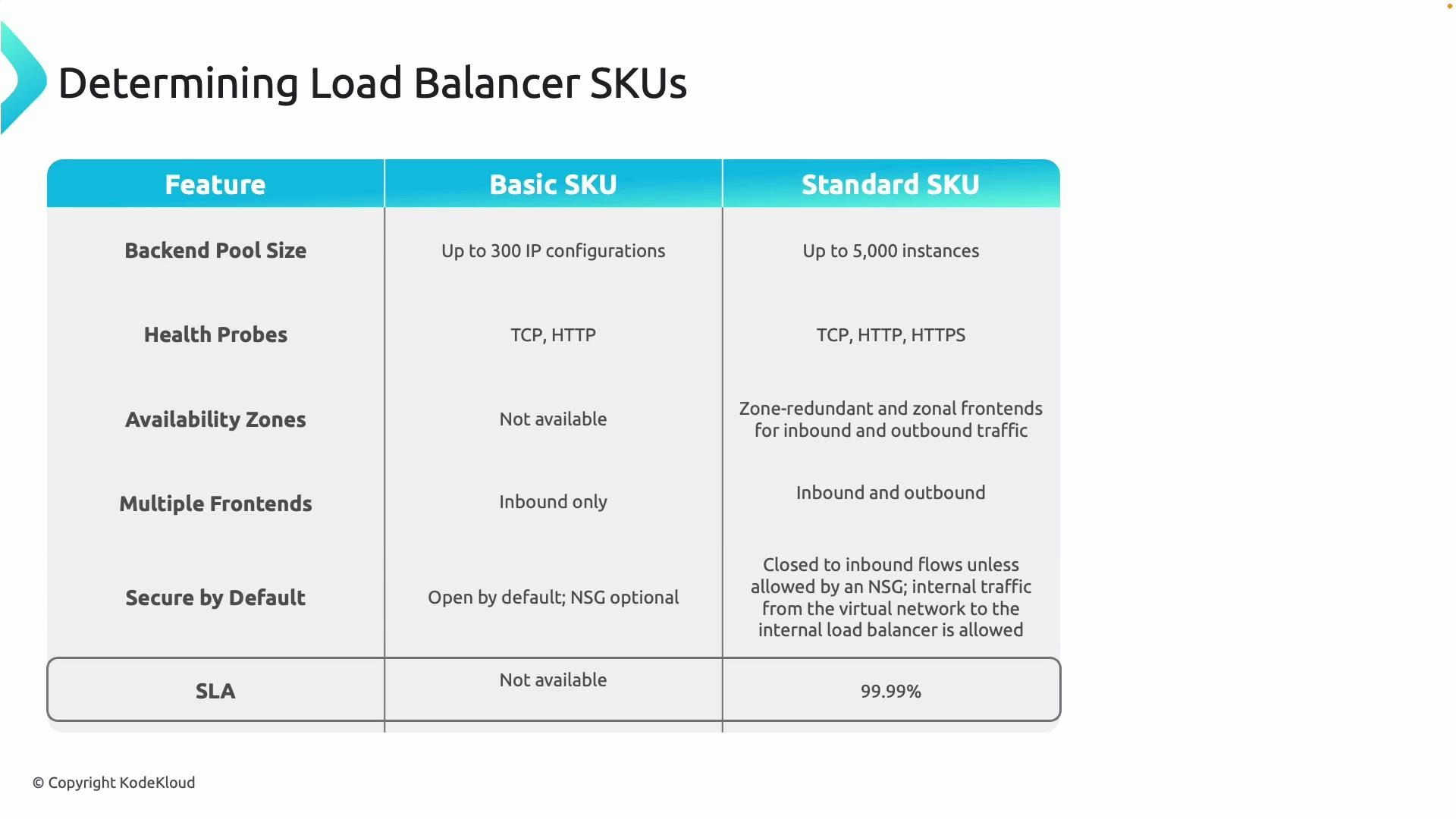
For production workloads requiring scale, zone resiliency, and a supported SLA, the Standard SKU is strongly recommended. Use Basic only for small-scale, non-production, or legacy scenarios where limited features are acceptable.
- SKU (Basic or Standard)
- Region and availability options (zonal vs zone‑redundant)
- Type (Public or Internal)
- Front-end IP configuration(s)
- Backend pools and health probes
- Load‑balancing rules and optional NAT rules
Design checklist
- Use Public load balancer for internet-facing front ends; Internal load balancer for private backend tiers.
- Prefer Standard SKU for production for SLA and zone resilience.
- Use Gateway Load Balancer when you need inline NVAs for inspection or service chaining.
- Plan NSGs and route tables explicitly when using Standard SKU (default inbound flows are blocked).
- Validate health probes and failover behavior across zones in zone-redundant setups.