- Create a dedicated subnet named GatewaySubnet in your virtual network.
- Deploy the VPN Gateway resource into that subnet.
- Configure the appropriate connections (site-to-site or point-to-site) depending on your scenario.
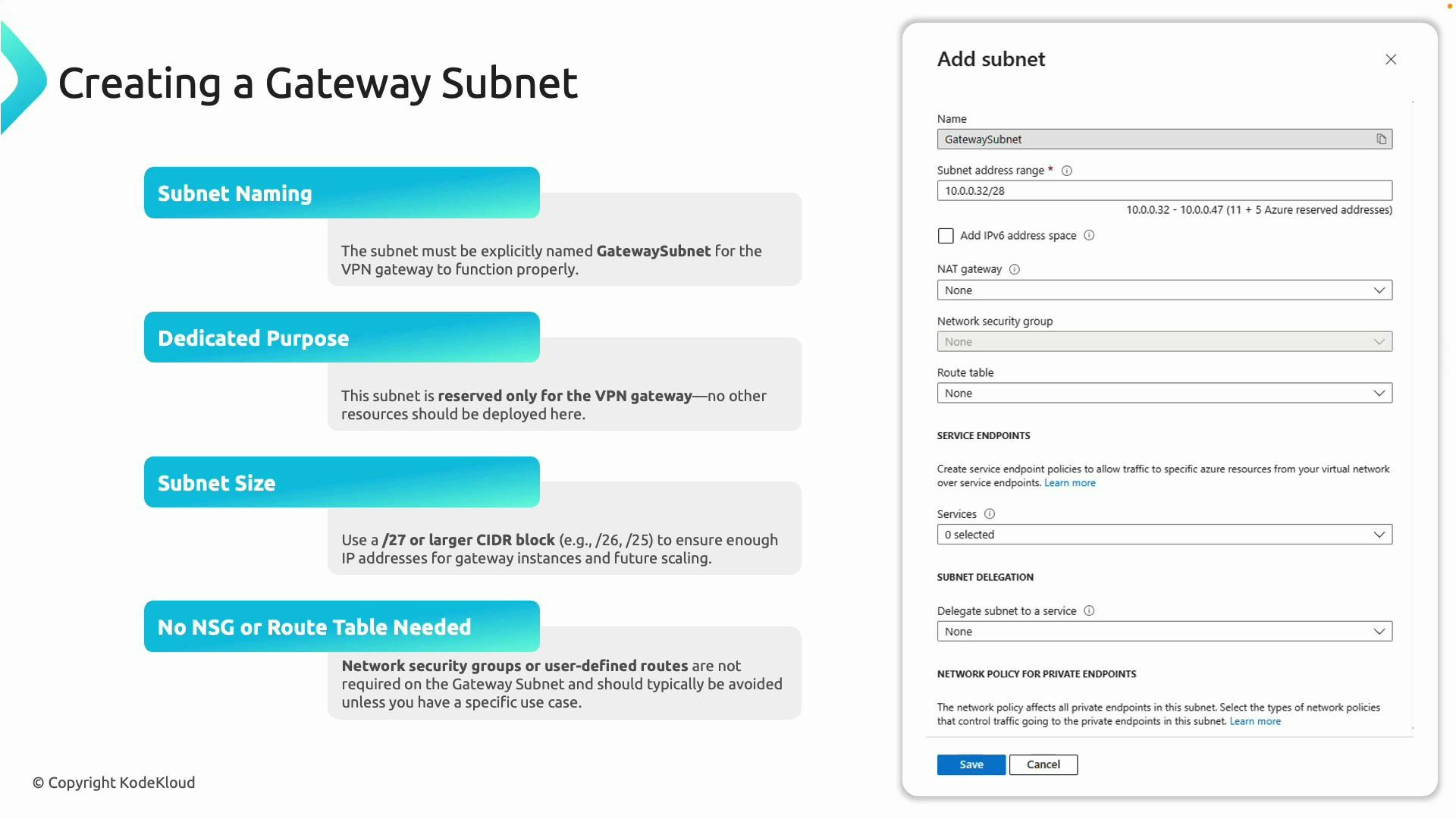
1) Create the GatewaySubnet (required)
The GatewaySubnet is mandatory for any Azure VPN Gateway. Follow these rules when creating it:- Name the subnet exactly GatewaySubnet (case-insensitive, no spaces). Azure requires this exact name to host the gateway.
- Reserve this subnet solely for the VPN Gateway; do not deploy virtual machines or other resources into it.
- Size the subnet large enough for scaling. Microsoft recommends at least a /27 prefix to allow multiple gateway instances.
- Do not attach Network Security Groups (NSGs) or user-defined route (UDR) tables to the GatewaySubnet — Azure manages the gateway network rules.
Name the subnet exactly “GatewaySubnet” and reserve it solely for the VPN Gateway. Avoid attaching NSGs or custom route tables to this subnet.
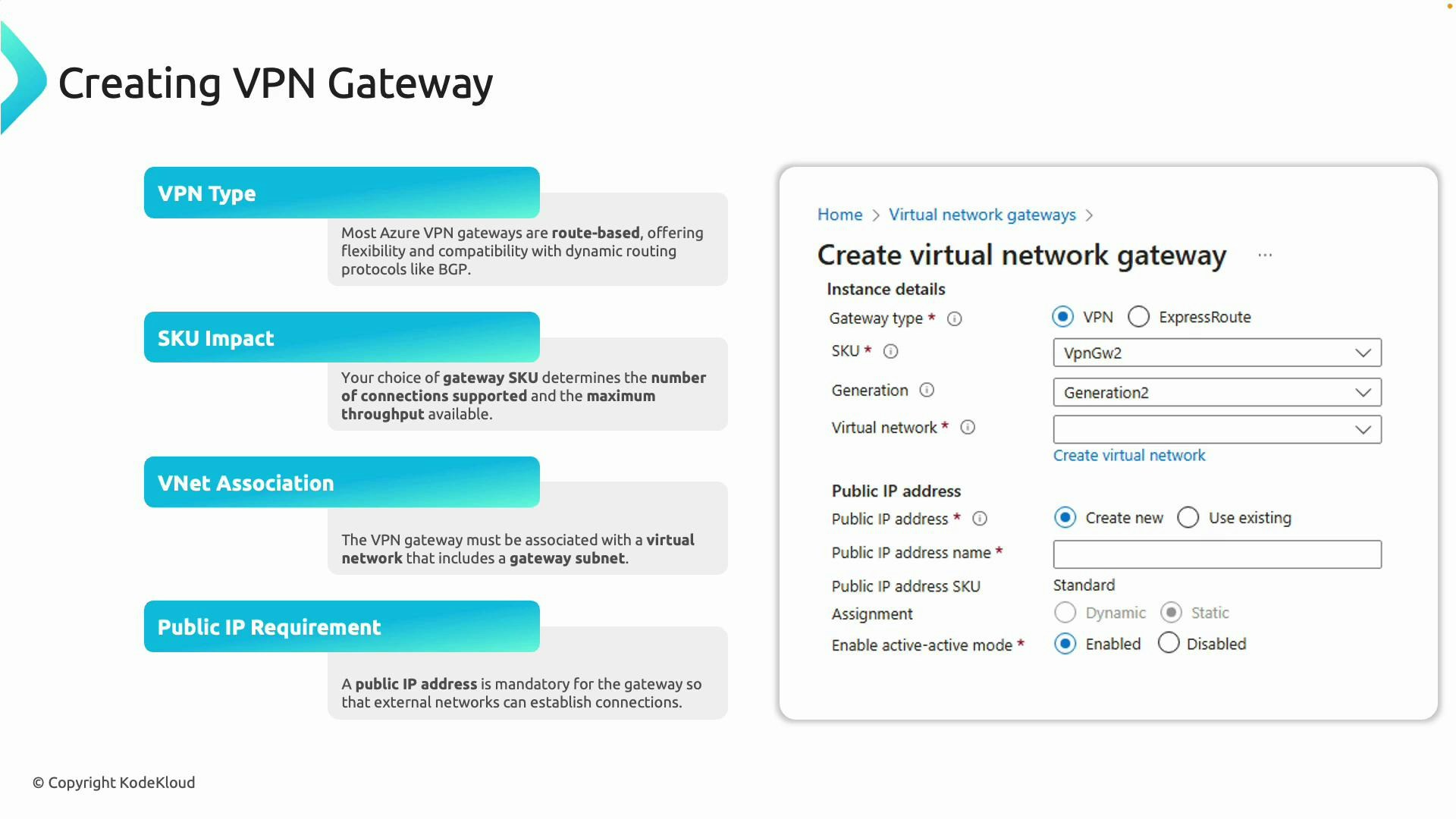
2) Create the VPN Gateway resource
When you create the VPN Gateway, choose options that match your connectivity and scale requirements. Key configuration decisions:- VPN type: route-based (recommended) or policy-based (legacy). Route-based supports dynamic routing (BGP) and is required for features like Azure Route Server integration.
- SKU: Select a gateway SKU (for example, VpnGw1, VpnGw2, VpnGw3). SKU determines tunnel count and throughput — pick based on expected traffic and the number of concurrent tunnels.
- Virtual Network: The gateway must be deployed into the VNet that contains the GatewaySubnet.
- Public IP: The VPN Gateway requires a public IP address for receiving connections from the internet.
- ExpressRoute/Private scenarios: For private connectivity you may use ExpressRoute or combine ExpressRoute + VPN; most S2S/P2S tunnels will use the public internet.
- Provisioning time: Expect up to ~45 minutes for provisioning — do not cancel or repeatedly redeploy during this time.
| Option | When to choose | Notes |
|---|---|---|
| Route-based VPN | Most scenarios, dynamic routing, BGP, Azure Route Server | Recommended for flexibility and BGP support |
| Policy-based VPN | Legacy static routing scenarios | Limited; fewer features and scalability |
| VpnGw1 / VpnGw2 / VpnGw3 | Increasing performance and tunnel capacity | Choose based on throughput and tunnel count needs |
Deploying a VPN Gateway can take up to 45 minutes. This is expected — do not retry or redeploy while the gateway is provisioning.
After the gateway is deployed
You can create:- Site-to-site (S2S) connections to on-premises devices — requires a Local Network Gateway resource in Azure.
- Point-to-site (P2S) connections for individual clients — requires client configuration and certificate or other authentication methods.
- Configure Local Network Gateway(s) and connections (S2S).
- Configure P2S authentication and client profiles (certificates or Azure AD authentication).
- Use the gateway in hub-and-spoke topologies by peering VNets and enabling gateway transit.
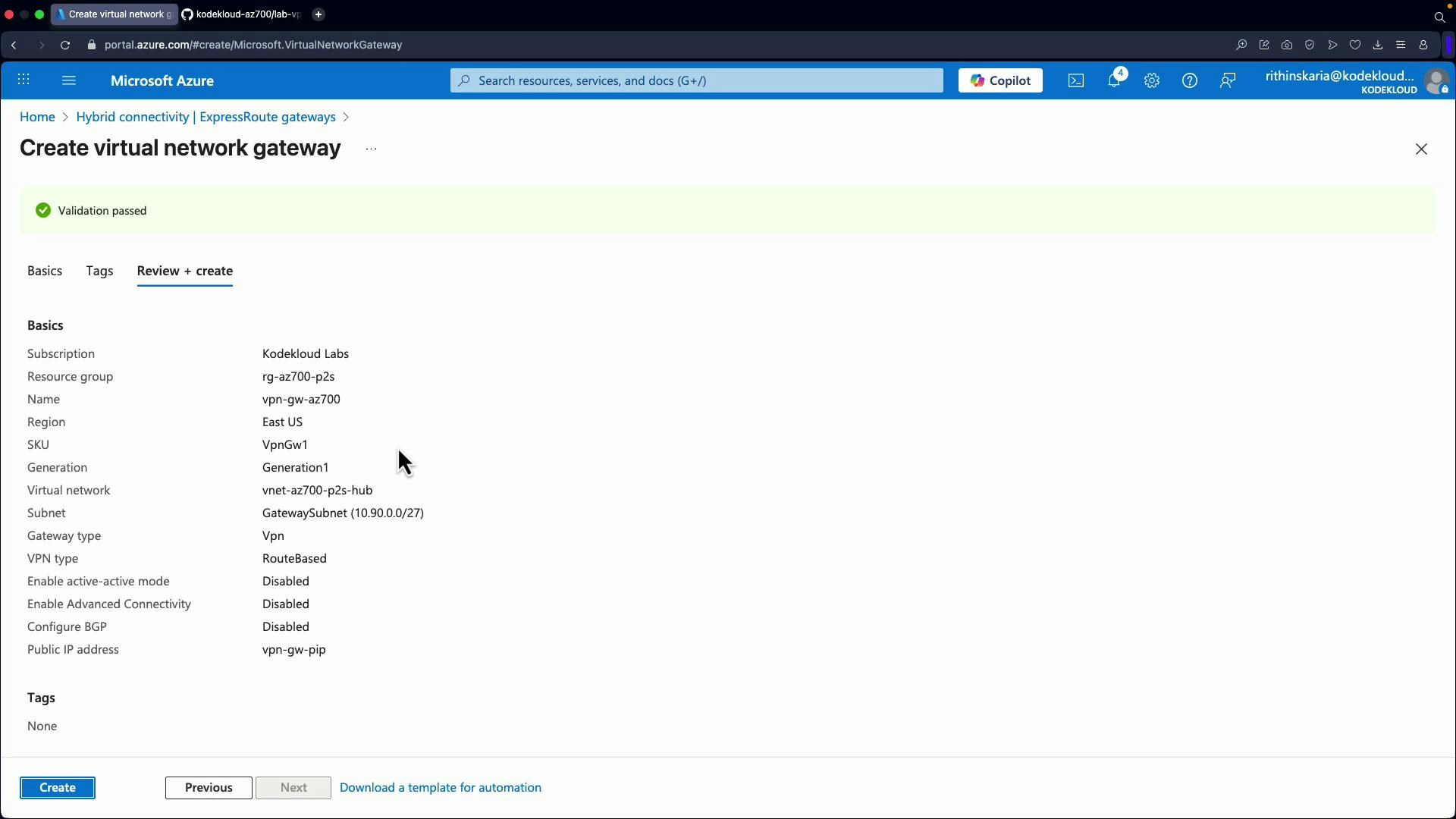
Demo context — Deploying a P2S gateway via the portal
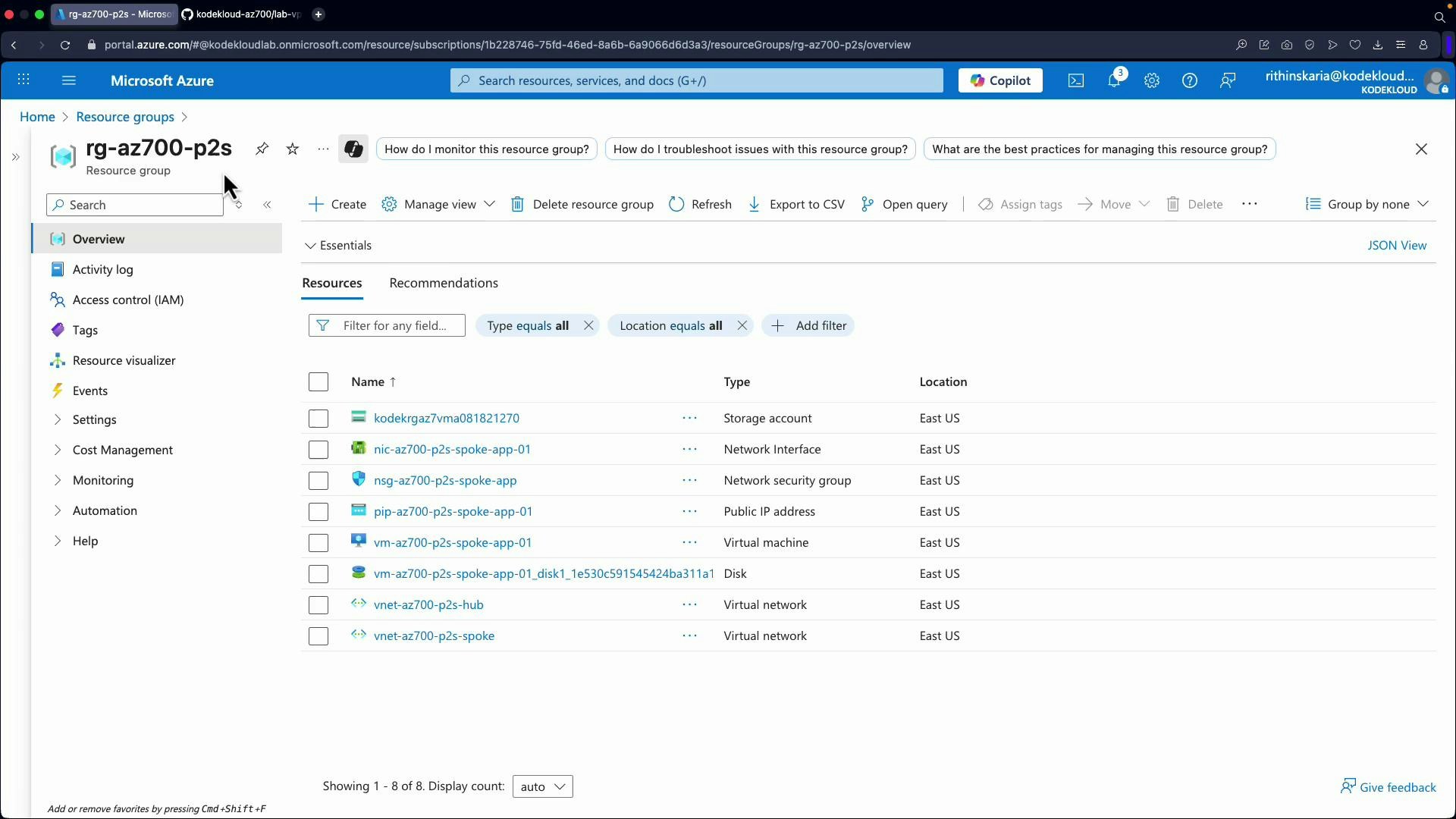
The following demo deploys a VPN Gateway intended for Point-to-Site (P2S) use. The environment already contains:- A resource group.
- A hub VNet and a spoke VNet.
- A test VM in the spoke to validate connectivity through the hub gateway using gateway transit.
- Hub VNet (vnet-az700-p2s-hub) — where the gateway will be deployed.
- Spoke VNet (vnet-az700-p2s-spoke) — with a subnet and a VM for testing.
- The demo then peers the VNets and enables gateway transit so the spoke VM can route to on-premises via the hub gateway (once the gateway and connections are configured).
Portal deployment steps (summary)
- Search for “Virtual network gateways” and click Create.
- Select your subscription and resource group.
- Enter a name (e.g., VPNGateway-AC700) and select the region (e.g., East US).
- Gateway type: VPN.
- SKU: select an appropriate SKU (e.g., VpnGw1 for lab/testing).
- Virtual Network: select the hub VNet containing GatewaySubnet.
- If GatewaySubnet doesn’t exist, create it from the VNet → Subnets blade. When you choose subnet purpose “Virtual network gateway” the name defaults to GatewaySubnet. Use at least /27.
- Public IP address: create a new public IP (for example, vpnGatewayPIP).
- Configure Active-Active, BGP, Key Vault access, etc., only if required. For a minimal lab, leave defaults (Active-Active off, BGP off).
- Review and Create. Wait for the deployment to complete (up to ~45 minutes).
After provisioning completes
- Create Site-to-Site connections: Add a Local Network Gateway resource to represent on-premises address spaces, then create a connection to the VPN Gateway.
- Configure Point-to-Site: Upload or configure certificate/authentication and generate client profiles for users to connect to Azure resources.
- Use with hub-and-spoke: Peer VNets and enable gateway transit so spokes can route to on-premises through the hub gateway.
Links and references
- Azure VPN Gateway overview: https://learn.microsoft.com/azure/vpn-gateway/
- GatewaySubnet details: https://learn.microsoft.com/azure/vpn-gateway/vpn-gateway-about-gateway-subnet
- VPN types (route-based vs policy-based): https://learn.microsoft.com/azure/vpn-gateway/vpn-gateway-about-vpn-types
- VPN Gateway SKUs: https://learn.microsoft.com/azure/vpn-gateway/vpn-gateway-about-vpngateway-skus
- Point-to-site overview: https://learn.microsoft.com/azure/vpn-gateway/point-to-site-about
- Local Network Gateway: https://learn.microsoft.com/azure/vpn-gateway/vpn-gateway-about-local-network-gateway-resource
- Hub-and-spoke architecture: https://learn.microsoft.com/azure/architecture/reference-architectures/networking/hub-spoke
- Azure Route Server: https://learn.microsoft.com/azure/route-server/overview