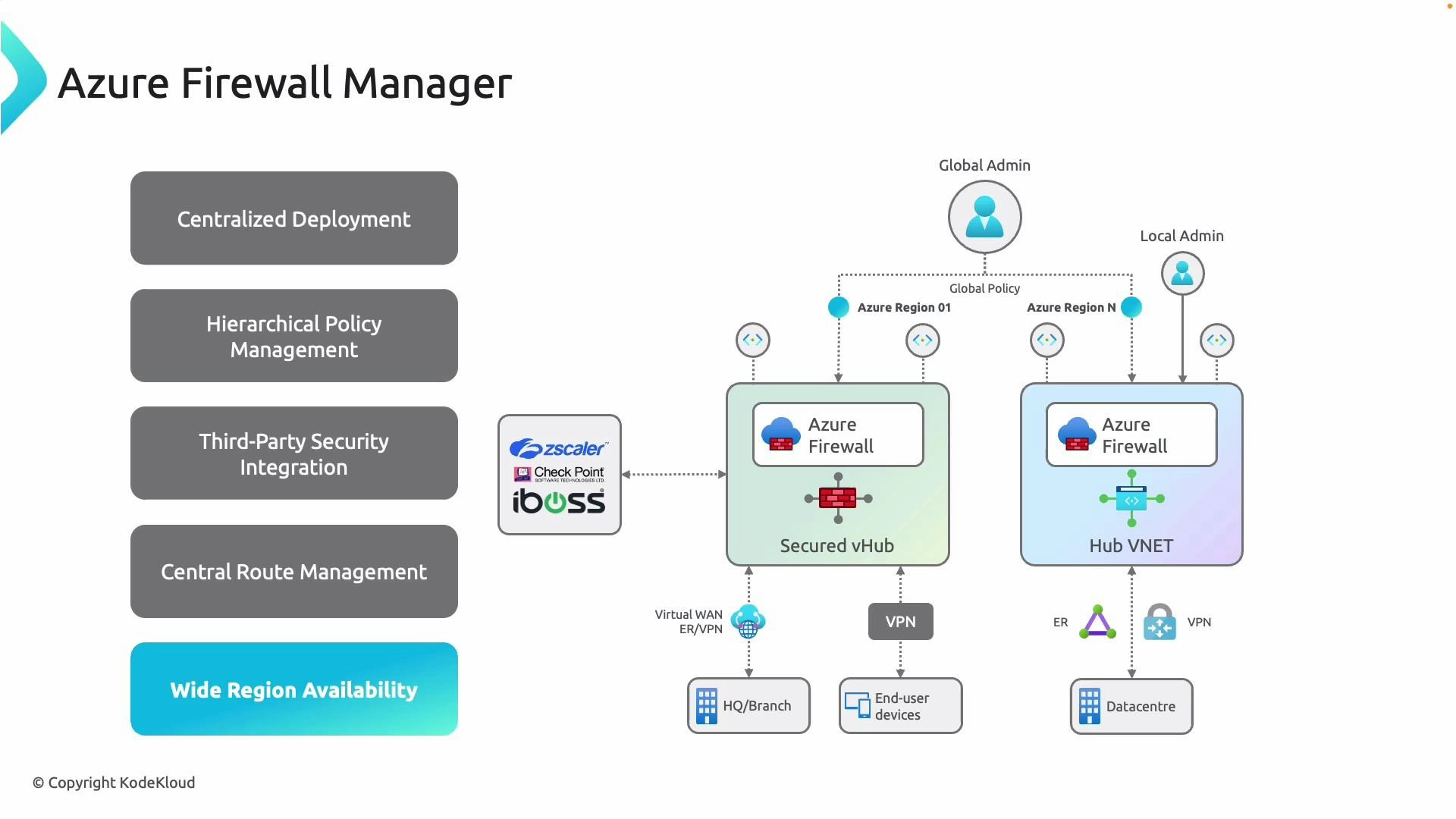
Deployment models shown in the diagram
The architecture diagram below illustrates two primary deployment models you can choose depending on your operational preferences:- Secured Virtual Hub (Microsoft-managed): Firewall Manager manages a secured Virtual Hub (Virtual WAN) that can include integrated third‑party security providers. This model is ideal for organizations that want simplified, global connectivity with partner security integrations.
- Hub VNet (tenant-managed): Firewall Manager manages hub VNets that host Azure Firewall instances you control. This model gives you full lifecycle control of the VNet and firewall instances.
Core capabilities and when to use them
| Capability | Benefit | Example |
|---|---|---|
| Centralized deployment | Deploy and roll out Azure Firewall instances and policies across regions and subscriptions from one place, reducing per-region configuration overhead. | Provision an Azure Firewall and apply a common policy across 5 subscriptions. |
| Hierarchical policy management | Create Azure Firewall Policy objects scoped to management groups, subscriptions, or individual firewalls to enable global baselines and local refinements. | Push a company-wide allowlist and let subscription owners add local DNAT rules. |
| Third‑party security integration | Integrate partner security providers (Zscaler, Check Point, iBoss, etc.) into secured hubs for deeper inspection and filtering. | Forward traffic to an integrated partner appliance in a secured vHub for advanced threat inspection. |
| Central route management | Manage how traffic is steered for inspection (UDRs/forced‑tunneling) so inspection points are enforced consistently across your estate. | Configure route tables to ensure east–west or internet-bound traffic traverses the central firewall. |
| Wide region availability | Apply consistent firewalling and policy enforcement across many regions to protect workloads regardless of geography. | Replicate policies and firewall deployments to multiple regions for redundancy and compliance. |
Secured Virtual Hubs (Virtual WAN) are typically Microsoft-managed and are ideal when you want integrated partner security and simplified global connectivity. Hub VNet deployments are tenant-managed and offer more control over the VNet and firewall instance lifecycle.