- Virtual network workloads that use Azure-provided DNS (no custom DNS servers).
- On-premises clients that cannot reach Azure’s internal DNS IP and therefore require a DNS resolver or forwarding solution.
acsql1.database.windows.net resolve to the private endpoint IP and that clients communicate privately over the Azure backbone or site-to-site connectivity.
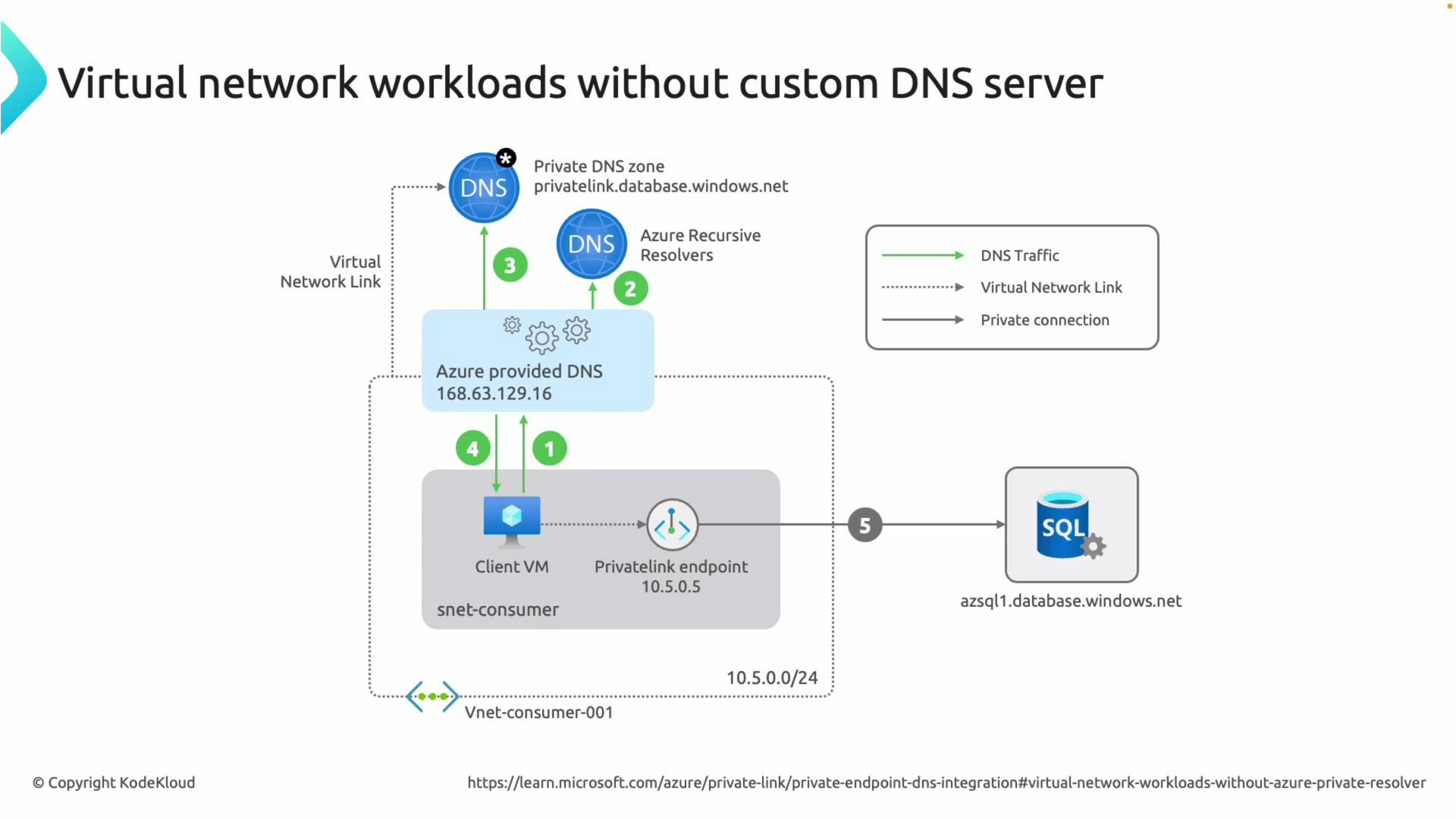
Scenario A — Virtual network workloads (Azure-provided DNS)
When a VM or other resource inside an Azure virtual network uses Azure-provided DNS (the default), DNS resolution for private endpoints follows this flow:- The client sends the DNS query to the Azure-provided DNS server (clients inherit this DNS setting from the VNet).
- Azure DNS checks the Private DNS zones linked to that VNet (for example,
privatelink.database.windows.net). - If a matching record exists (for example,
acsql1inprivatelink.database.windows.net), Azure DNS returns the private response. - The client receives the private name (a CNAME to the
privatelinkzone plus an A record to the private endpoint IP) and connects directly to the service via the private endpoint.
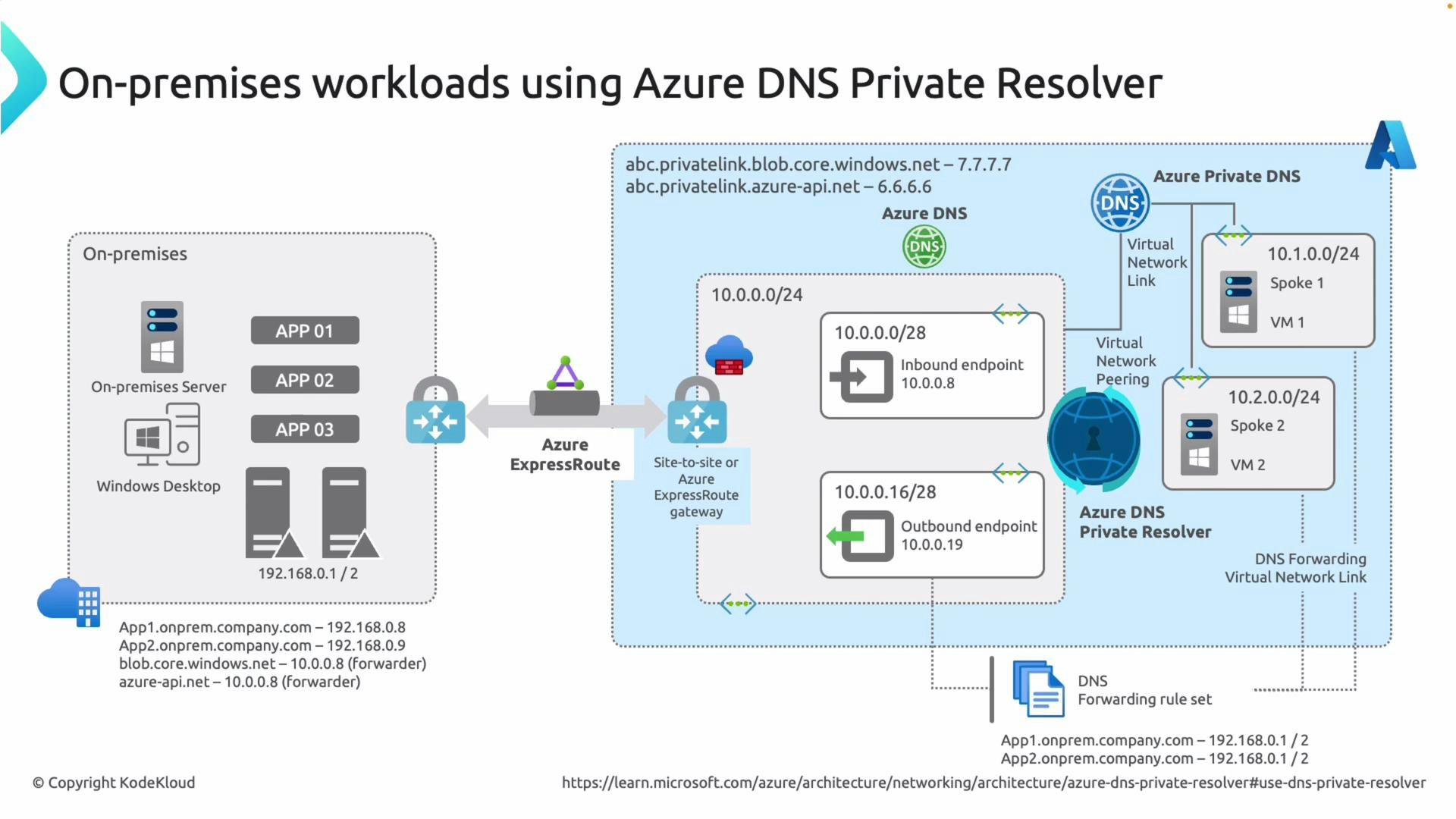
Scenario B — On-premises clients (need a DNS resolver/forwarder)
On-premises clients cannot query the Azure internal DNS IP address (168.63.129.16) because it is not reachable outside Azure. To allow on-premises systems to resolve Private Link names to private IPs, use an Azure Private DNS Resolver or deploy your own DNS servers inside Azure and configure conditional forwarding. Key components of the resolver-based approach:- Azure Private DNS Resolver is deployed into an Azure VNet and exposes:
- Inbound endpoints: where on-premises or external DNS servers forward queries.
- Outbound endpoints: used by the resolver to query recursive DNS servers as needed.
- Link the resolver’s VNet to the Private DNS zones that contain
privatelinkrecords. - Configure a conditional forwarder on your on-premises DNS servers to forward queries for Azure service domains (e.g.,
database.windows.net,blob.core.windows.net) to the resolver’s inbound endpoint. - The resolver answers requests for
privatelinkrecords and returns private IPs across your VPN or ExpressRoute connection.
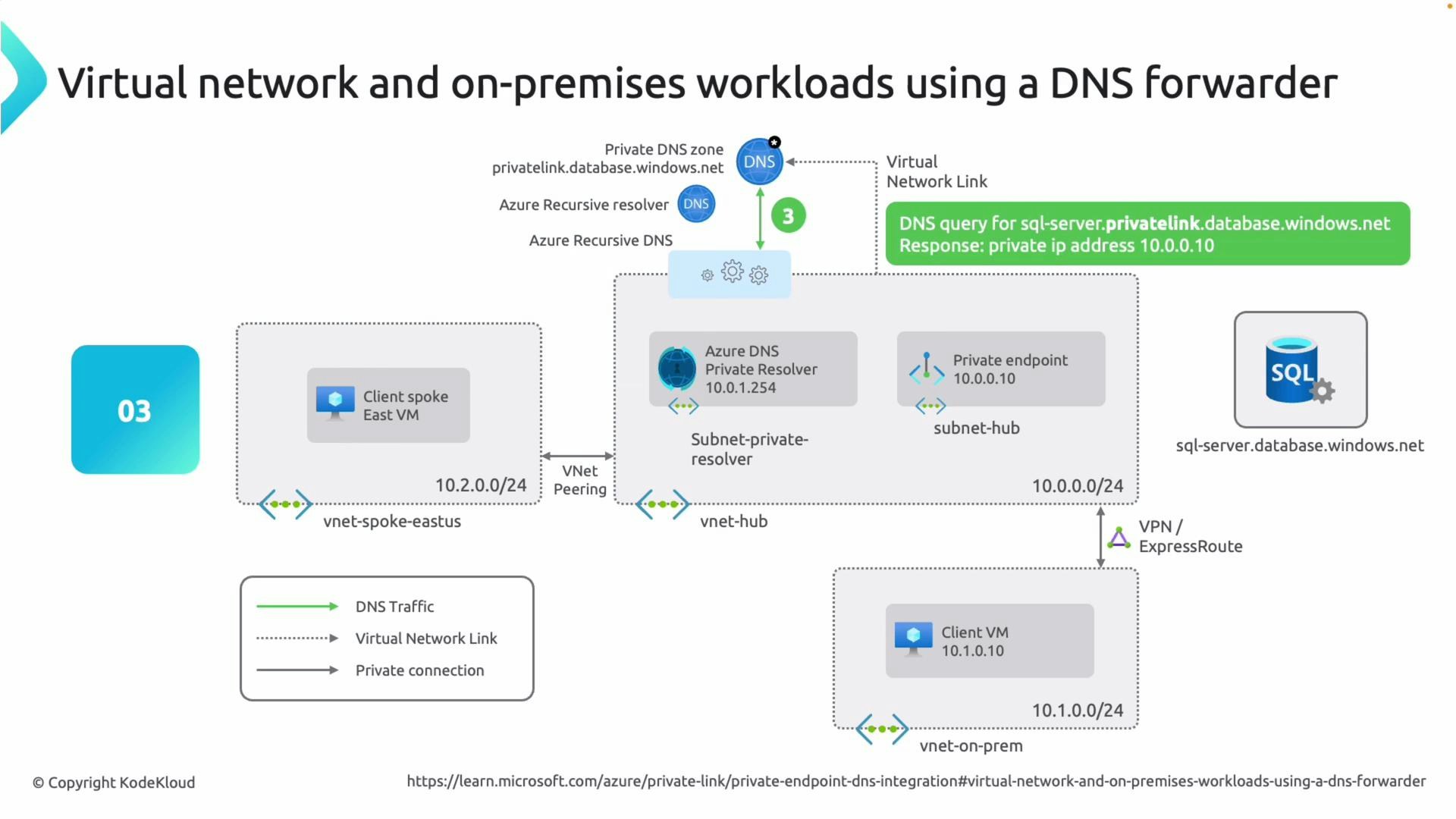
How the resolver-based flow works (step-by-step)
- An on-premises or Azure client issues a DNS request; on-premises DNS servers forward relevant queries to the Azure Private DNS Resolver via a conditional forwarder.
- The resolver checks its linked Private DNS zones for a matching
privatelinkrecord (for example,acsql1.privatelink.database.windows.net). - If the record exists, the resolver returns the private answer to the client. If not, the resolver forwards the query to recursive DNS servers using its outbound endpoints.
- The client then connects directly to the private endpoint IP returned in the DNS response via VPN/ExpressRoute or within Azure.
Quick comparison
| Scenario | When to use | Key configuration |
|---|---|---|
| Virtual network (Azure-provided DNS) | Resources inside Azure VNets that use default Azure DNS | Link Private DNS zone to VNet; Azure-provided DNS resolves privatelink records |
| On-premises (DNS resolver/forwarder) | On-prem clients that cannot reach 168.63.129.16 | Deploy Azure Private DNS Resolver or Azure DNS-forwarding VMs; configure conditional forwarders from on-prem DNS to resolver; link resolver VNet to Private DNS zone |
Links and references
- Azure Private Link overview
- Azure DNS Private Resolver documentation
- Azure Private Endpoint DNS configuration guidance
Use a conditional forwarder on your on-premises DNS servers to forward queries for Azure service domains (for example, database.windows.net or blob.core.windows.net) to the Azure Private DNS Resolver. Also ensure the resolver’s virtual network is linked to the appropriate Private DNS zones.
Remember: the Azure internal DNS address 168.63.129.16 is only reachable from within Azure VNets. On-premises systems cannot query it directly — use a resolver or DNS forwarder instead.