Overview
Three common P2S authentication methods:- Certificate-based authentication (device-level trust)
- Microsoft Entra ID (cloud-based, modern identity)
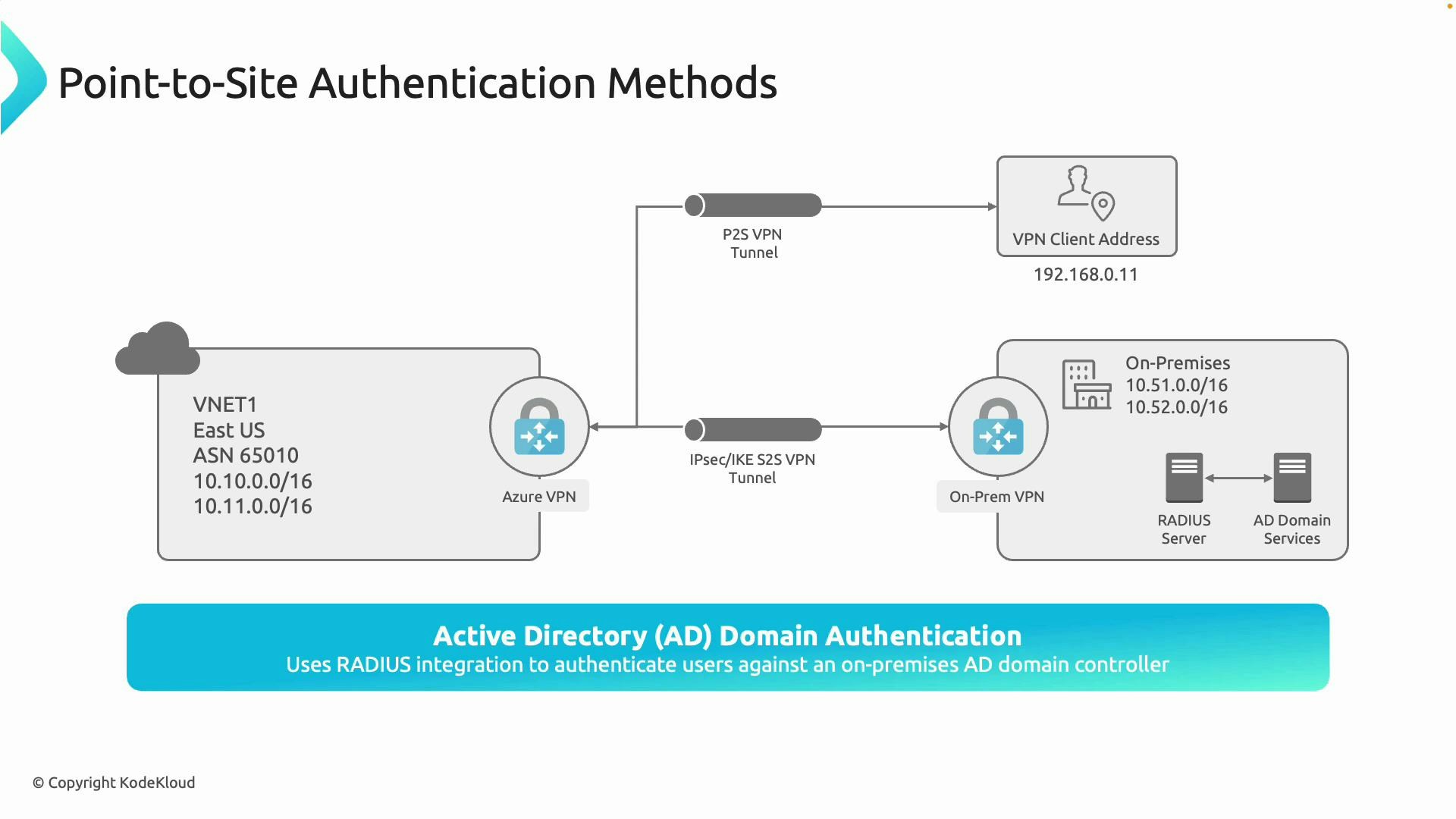
- Active Directory Domain (via RADIUS) (on‑premises credential validation)
Azure certificate authentication
How it works- A trusted root certificate (public key) is uploaded to the Azure VPN gateway.
- Client certificates, issued (signed) by that root certificate, are installed on each client device.
- When a client connects, the VPN gateway validates the client certificate. Only devices with a valid signed client certificate are allowed to connect.
- You need device-level assurance (ensuring only managed devices connect).
- You operate your own PKI or can centrally issue and manage certificates.
- You want a solution that does not depend on online authentication services for each connection.
- Pros: strong device authentication, resilient to password-based attacks, good for controlled device fleets.
- Cons: certificate lifecycle and distribution overhead, revocation management, less convenient for end users than username/password or cloud SSO.
- Azure documentation: certificate-based P2S VPN authentication
- Consider combining with Intune or other device management for certificate distribution.
Microsoft Entra ID authentication (modern, cloud-based)
How it works- Users authenticate with their Microsoft Entra ID (formerly Azure AD) work accounts.
- The VPN gateway redirects authentication to Entra ID; Entra evaluates identity and any configured conditional access policies (MFA, device compliance).
- Supports modern controls such as multifactor authentication (MFA) and conditional access.
- Centralized identity in the cloud with no on‑premises authentication servers required.
- Good user experience—users sign in with familiar credentials.
- Enables conditional access and MFA for VPN access, improving security posture without additional infrastructure.
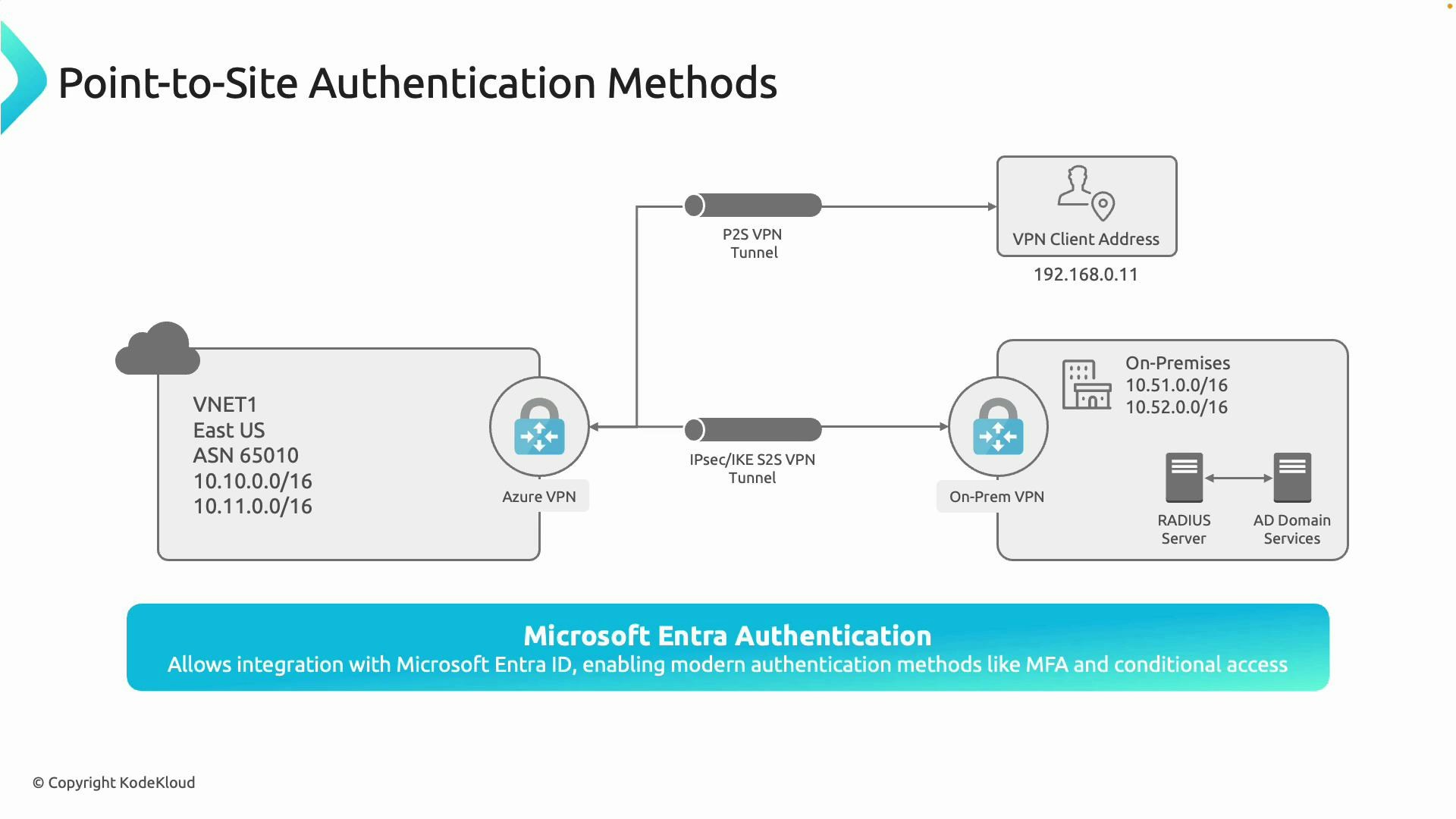
- Pros: centralized administration, integrates with MFA and conditional access, simpler for cloud-first organizations, no on‑prem RADIUS servers required.
- Cons: requires Entra ID accounts and configuration; organizations with strict on‑prem-only policies may prefer other methods.
Active Directory Domain (RADIUS) authentication
How it works- VPN clients authenticate using their on‑premises domain credentials.
- The VPN gateway forwards credentials to a RADIUS server (deployed on‑prem), which validates them against Active Directory Domain Services (AD DS).
- RADIUS can also integrate with secondary controls like MFA solutions (if deployed in your environment).
- You have an existing on‑premises AD environment and want to reuse domain users and passwords.
- You want to keep authentication processing within your on‑prem infrastructure (hybrid scenarios).
- Pros: leverages existing AD accounts and policies, familiar admin model.
- Cons: requires RADIUS infrastructure and connectivity from the VPN gateway to the RADIUS servers; higher on‑prem operational overhead.
Quick comparison
| Method | Authentication flow | Best for | Pros | Cons |
|---|---|---|---|---|
| Certificate-based | Client certificate validates to VPN gateway | Managed device fleets, strict device assurance | Strong device-level trust; not password-dependent | Certificate issuance & lifecycle management |
| Microsoft Entra ID | Entra ID SSO/OAuth + optional MFA & conditional access | Cloud-first organizations | Centralized identity, MFA & conditional access, good UX | Requires Entra accounts & cloud integration |
| AD Domain (RADIUS) | VPN gateway -> RADIUS -> AD DS | Hybrid environments reusing on‑prem credentials | Reuses existing AD accounts; familiar admin model | Requires RADIUS servers and reliable connectivity |
Summary and guidance
- Certificate authentication: choose when you control a PKI or need strict device-based assurance.
- Microsoft Entra ID authentication: a modern, scalable option that integrates with MFA and conditional access—recommended for cloud-first environments.
- AD Domain (RADIUS) authentication: the right choice for hybrid deployments that must validate credentials against on‑premises AD.
Choose the P2S authentication method that matches your environment: use Microsoft Entra ID for cloud-integrated identity and conditional access, certificates for strict device authentication, and RADIUS/AD for hybrid setups that rely on on‑premises domain credentials.