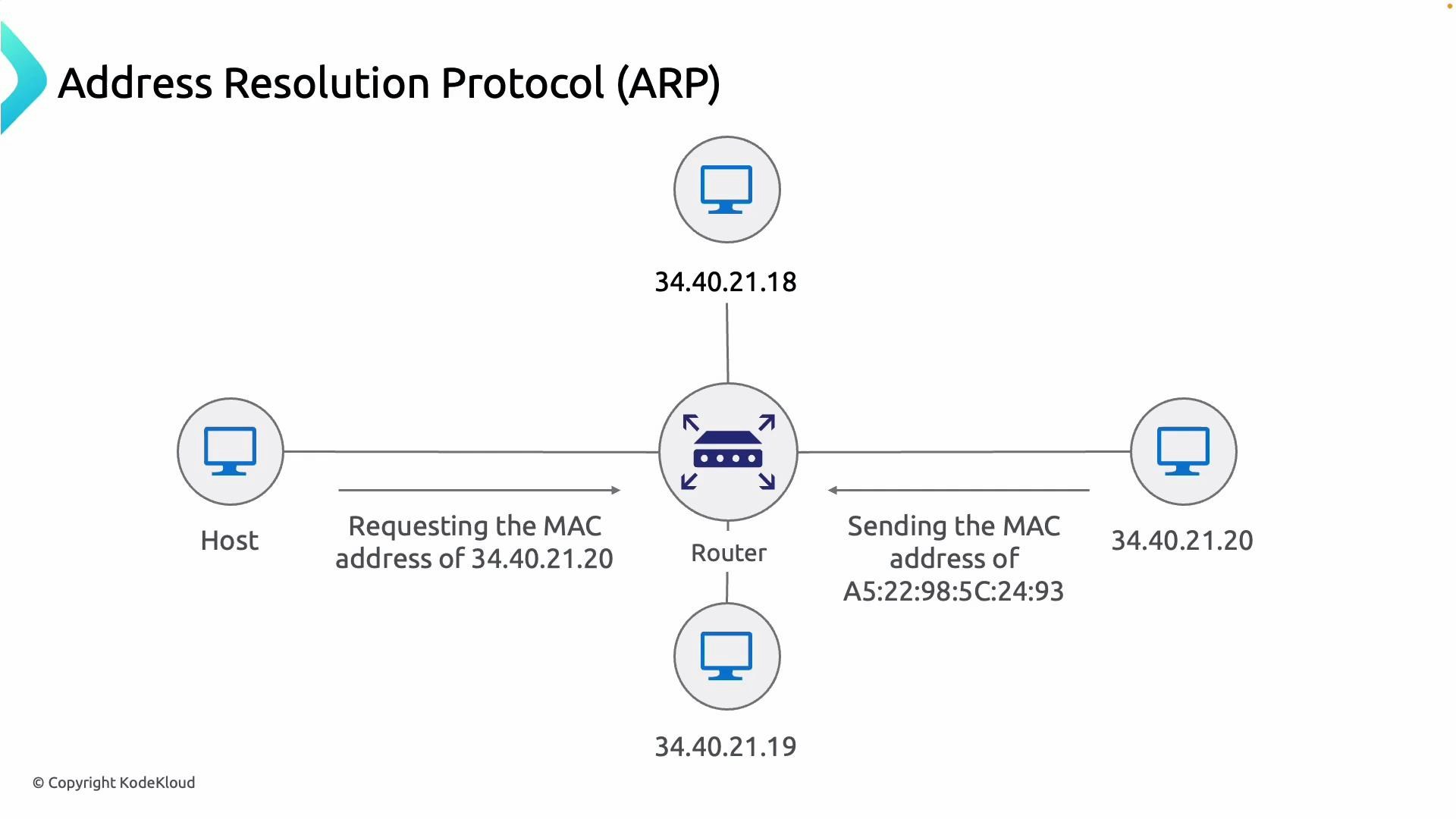
- ARP operates at Layer 2 and is required for local delivery of packets on the same subnet/VLAN used by ExpressRoute peering.
- Both the on‑prem peer and the Azure (Microsoft) peer must be able to resolve each other’s MAC addresses for traffic to pass.
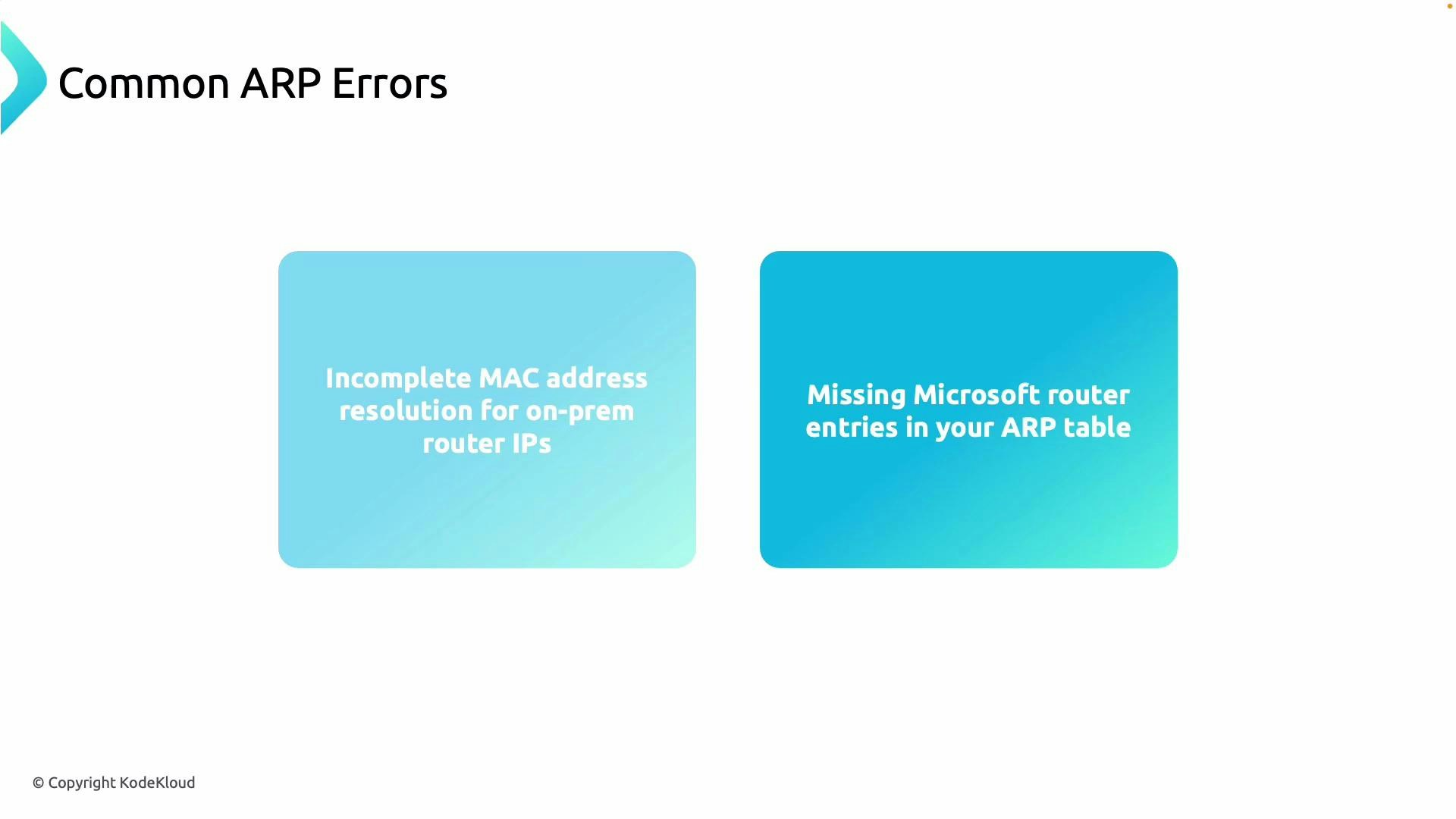
- Missing or stale ARP entries typically indicate Layer‑2 issues: cabling, VLAN/tag mismatch, switch MAC learning problems, or security features blocking ARP.
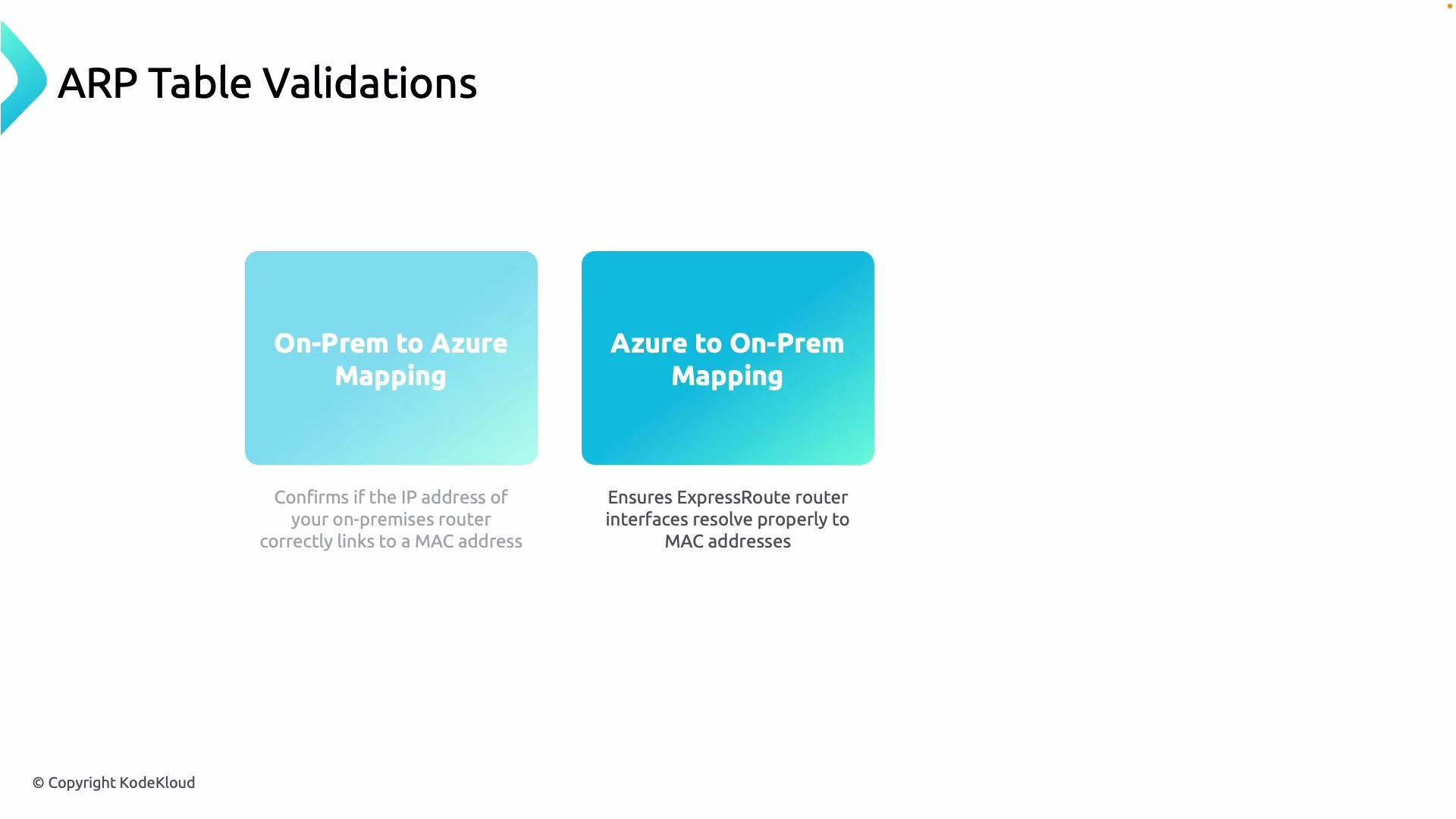
- Verify the ARP table on your on‑prem router for the Azure peer IP and confirm it maps to the expected Microsoft/Azure MAC.
- Verify the ARP table on the Azure-facing device (on‑prem edge or virtual network gateway) resolves your on‑prem router IP to the expected on‑prem MAC.
- Confirm both sides can ARP for each other — that ARP requests are sent and ARP replies are received.
- Look for stale entries, missing Microsoft/Azure router entries, or duplicate MACs that could indicate L2 problems.
| Platform | Command |
|---|---|
| Windows | arp -a |
| Linux | ip neigh show or arp -n |
| Cisco IOS | show ip arp (or show arp | include <ip-address>) |
| Junos | show arp |
- Windows:
- Linux:
- Cisco IOS:
- Junos:
| Symptom | Likely cause | Recommended action |
|---|---|---|
| Incomplete MAC resolution for on‑prem router IPs | VLAN mismatch, incorrect interface, or switch learning issue | Verify VLAN tags, check interface configuration, inspect switch MAC table |
| Missing Microsoft/Azure router entries in your ARP table | Azure side not reachable at L2 or ARP responses blocked | Confirm peering VLAN, check ACLs/port security, verify Azure peer is up |
| Duplicate or rapidly changing MACs | Multiple devices using same MAC, VM migration, bridging/loop | Inspect for bridging loops, check virtualization/migration events, validate MAC address consistency |
- Physical link state and cabling between the on‑prem edge and the provider/switch.
- VLAN and trunk configuration — ensure the peering VLAN/tag matches on both sides (provider and customer).
- Switch MAC address table to confirm the port where the MAC is learned.
- Port security, MAC limiting, or ACLs that might restrict or drop ARP/broadcast traffic.
- ARP cache issues — clear ARP carefully to force re-resolution from endpoints.
- Virtual routers or firewalls that might block broadcast/ARP traffic in the path.
- Find which switch port learned a MAC (Cisco example):
- Clear ARP entries (use caution in production):
- Cisco IOS:
- Linux:
- Cisco IOS:
- ExpressRoute overview — https://learn.microsoft.com/en-us/azure/expressroute/overview
- RFC 826 (ARP) — https://datatracker.ietf.org/doc/html/rfc826
- Microsoft troubleshooting resources for ExpressRoute — https://learn.microsoft.com/en-us/azure/expressroute/
When validating ARP for ExpressRoute, always check both sides (on‑prem and Azure) and verify the MACs correspond to the expected peer interfaces. Confirming IP-to-MAC mappings quickly distinguishes L2 issues from L3/routing problems.
Clearing ARP entries or flushing neighbor caches can temporarily disrupt traffic. Perform these actions during maintenance windows when possible or on a single test device before making broader changes.