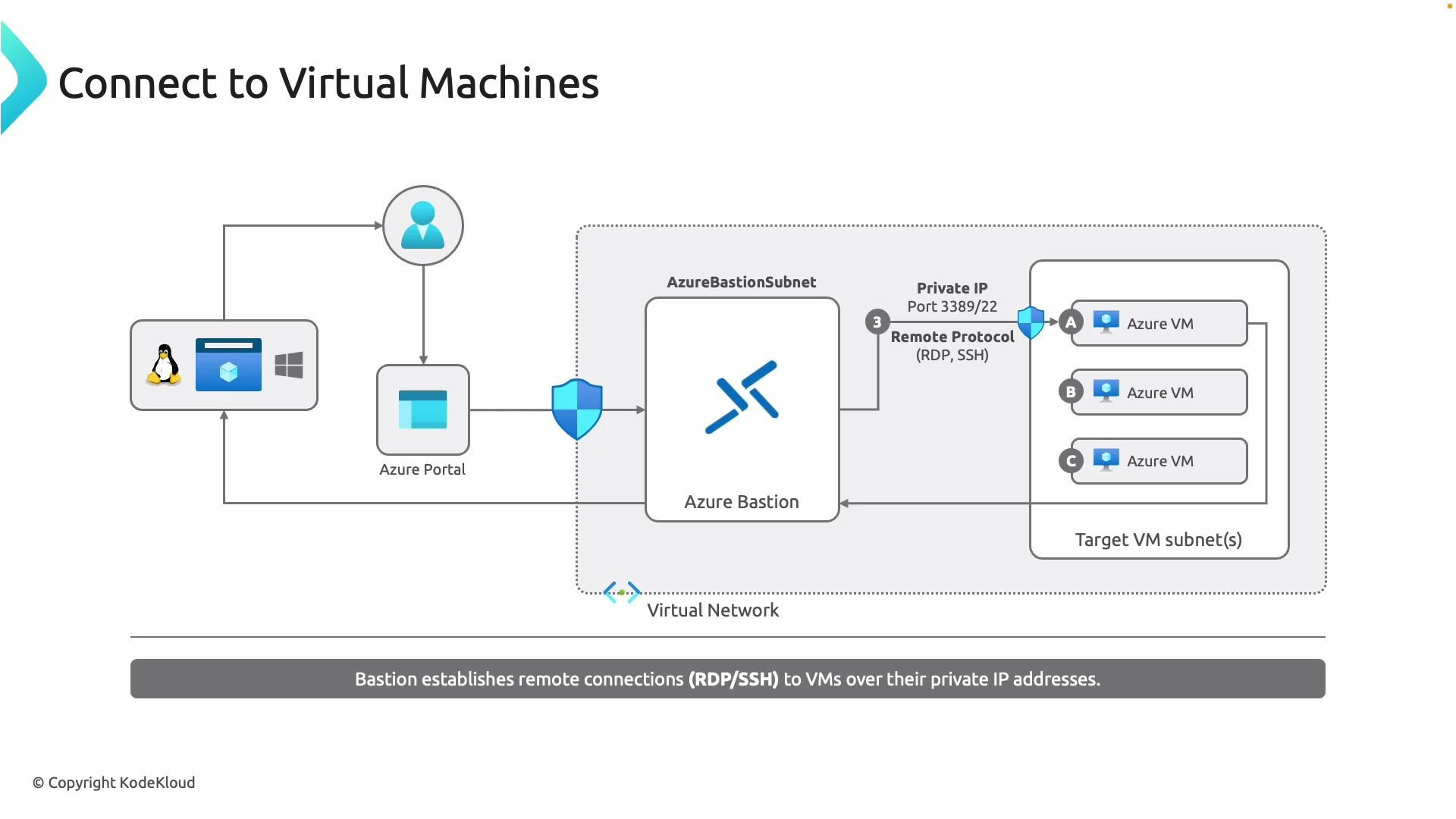
- No public IPs on target VMs — reduces attack surface.
- RDP (Windows) and SSH (Linux) from the portal — no additional client required.
- Connections are encrypted over TLS and use the VM private IP addresses.
- The user signs in to the Azure portal over TLS (443).
- A Bastion host is deployed in a dedicated subnet named exactly AzureBastionSubnet.
- Bastion brokers RDP or SSH connections to target VMs using their private IPs.
Important: The Bastion subnet must be named exactly AzureBastionSubnet and must meet the minimum size requirement (a /27 or larger address range). This subnet must be dedicated to Azure Bastion. If the subnet name is different or the prefix is too small, the Bastion resource cannot be deployed. For full requirements, see the Azure Bastion documentation: https://learn.microsoft.com/azure/bastion/
Deploy Azure Bastion from the Azure portal
Prerequisites:- A virtual network that contains the VMs you want to access.
- A dedicated subnet named AzureBastionSubnet with at least a /27 prefix.
- In the Azure portal, search for and open Azure Bastion, then click Create.
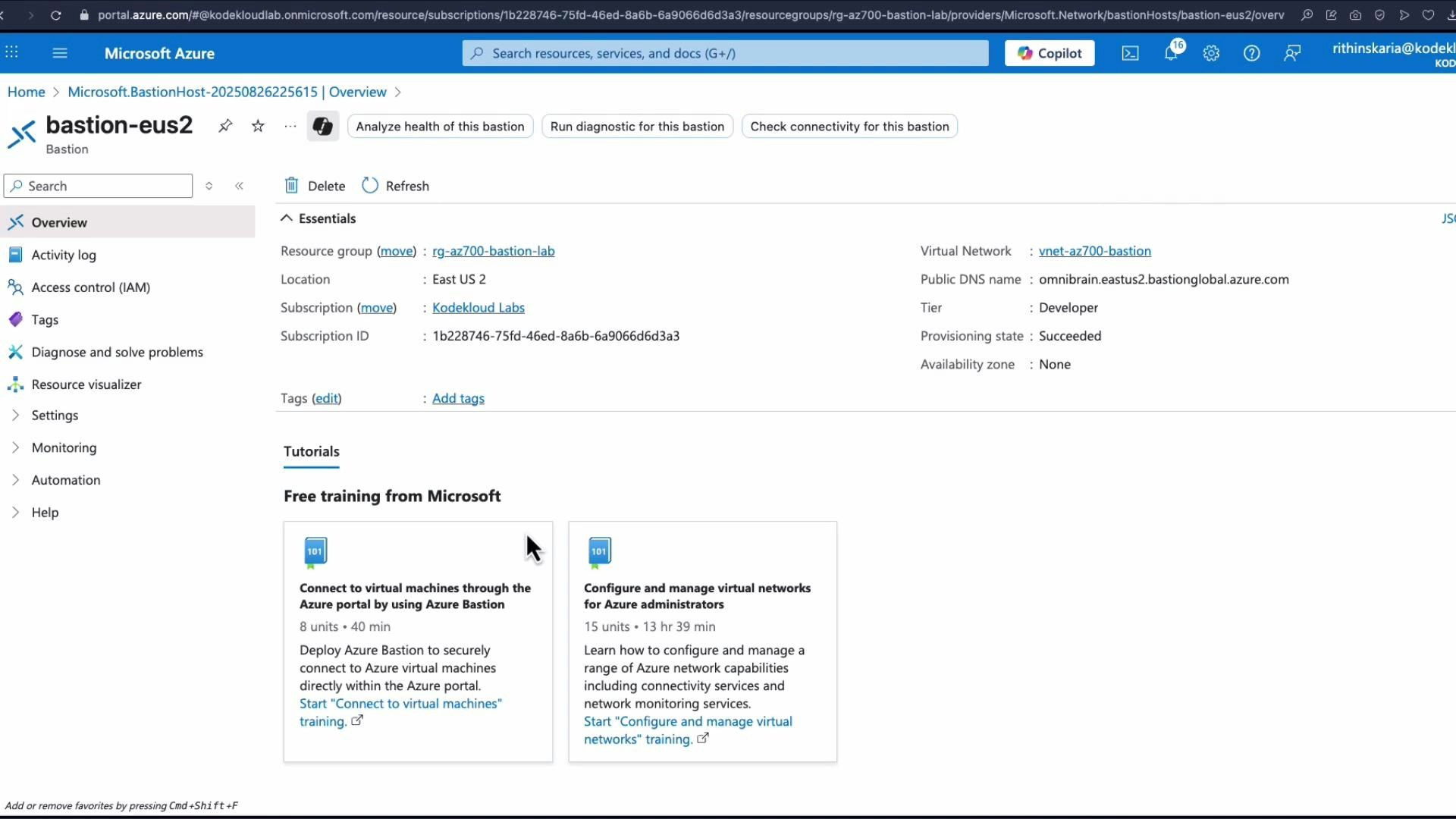
- Select the subscription and resource group, set the Bastion name (for example,
Bastion-US2), and choose the virtual network containing your VMs. - Choose a SKU. For quick testing you can select the Developer SKU, but production scenarios typically use Standard or Premium for higher concurrency and advanced features.
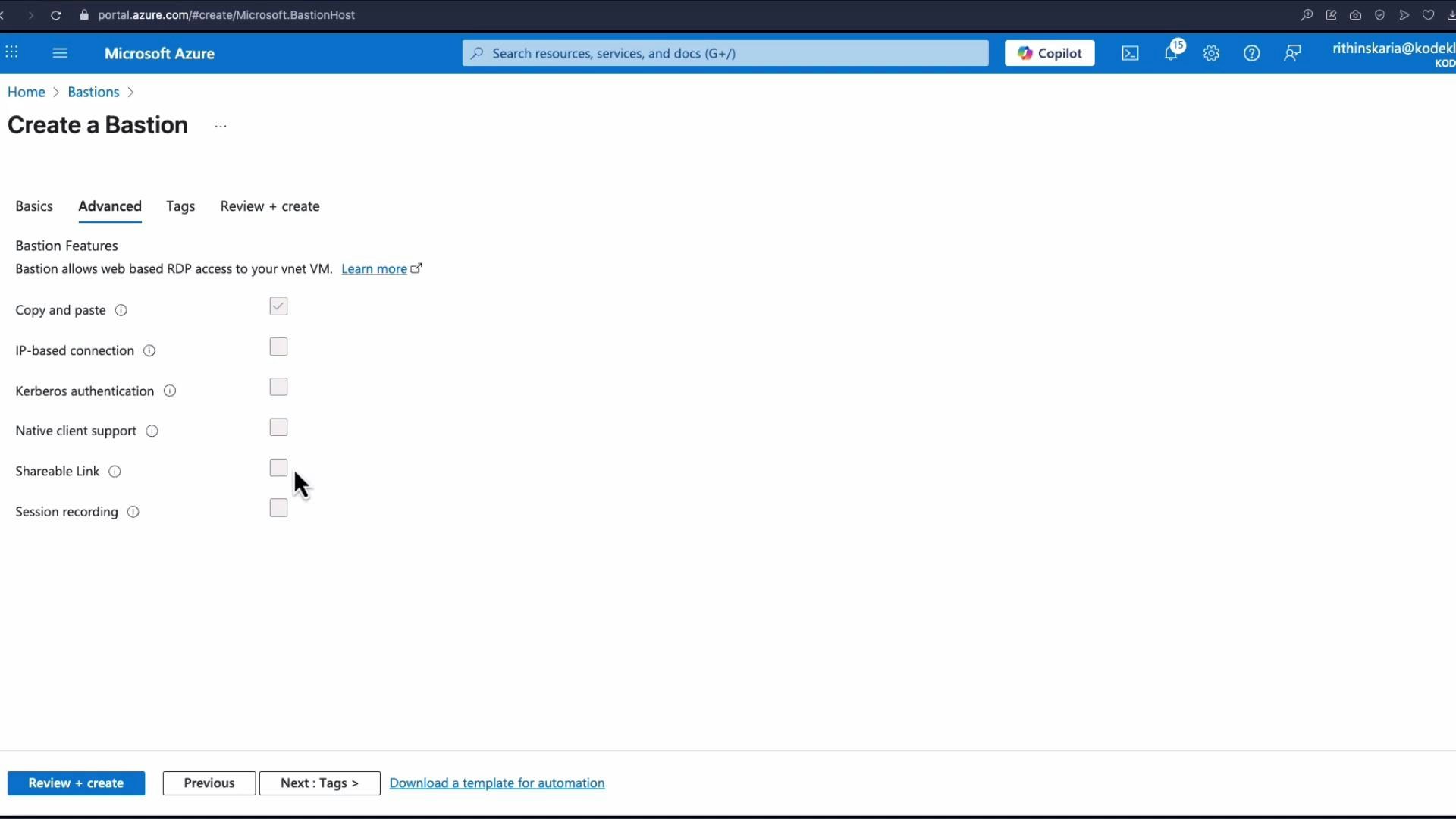
- On the Advanced tab, review optional features (copy & paste, IP-based connection, Kerberos authentication, native client support, shareable link, session recording).
- Complete the deployment: Tags -> Review + Create -> Create.
Connect to a VM using Bastion
To open an RDP or SSH session through Bastion:- In the Azure portal go to Virtual Machines and select the VM you want to connect to.
- Click Connect and choose Bastion.
- Enter the VM credentials (username and password, or appropriate auth method) and click Connect. A new browser tab will open with the session.
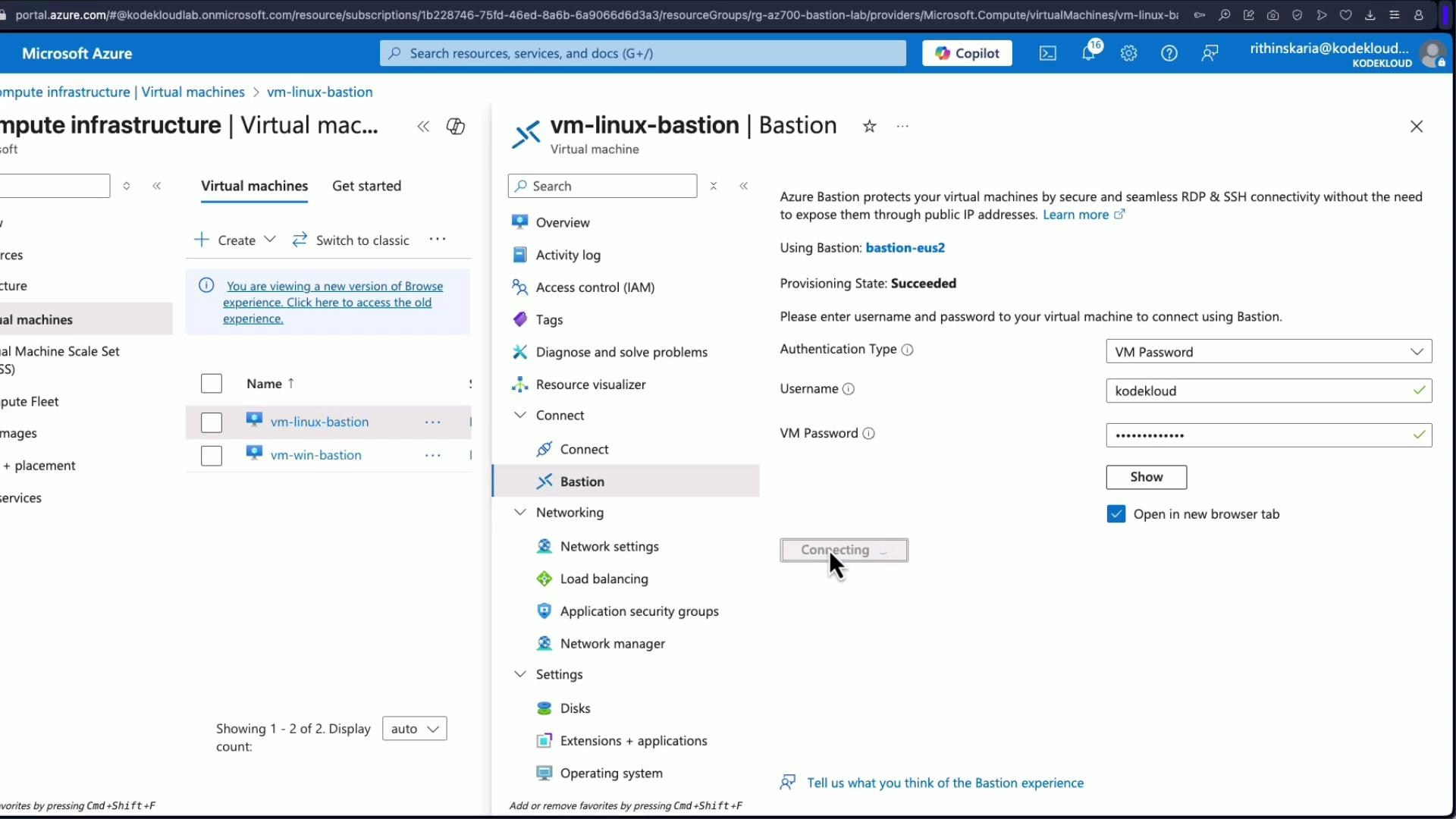
If your browser blocks the new window/tab, you may not see the Bastion session. Allow pop-ups for the Azure portal and retry the connection. Some corporate browsers or extensions may require additional configuration.
Bastion SKUs and concurrency (quick reference)
| SKU | Use case | Typical features / concurrency |
|---|---|---|
| Developer | Testing or lab environments | Single concurrent session; limited features |
| Standard | Production workloads | Multiple concurrent sessions; copy/paste; native client support |
| Premium | High-scale / advanced security | Higher concurrency; session recording; Kerberos integration; shareable links |
Additional resources
- Azure Bastion overview and quickstart: https://learn.microsoft.com/azure/bastion/
- RDP overview: https://learn.microsoft.com/windows-server/remote/remote-desktop-services/welcome-to-rds
- SSH basics: https://www.ssh.com/ssh/