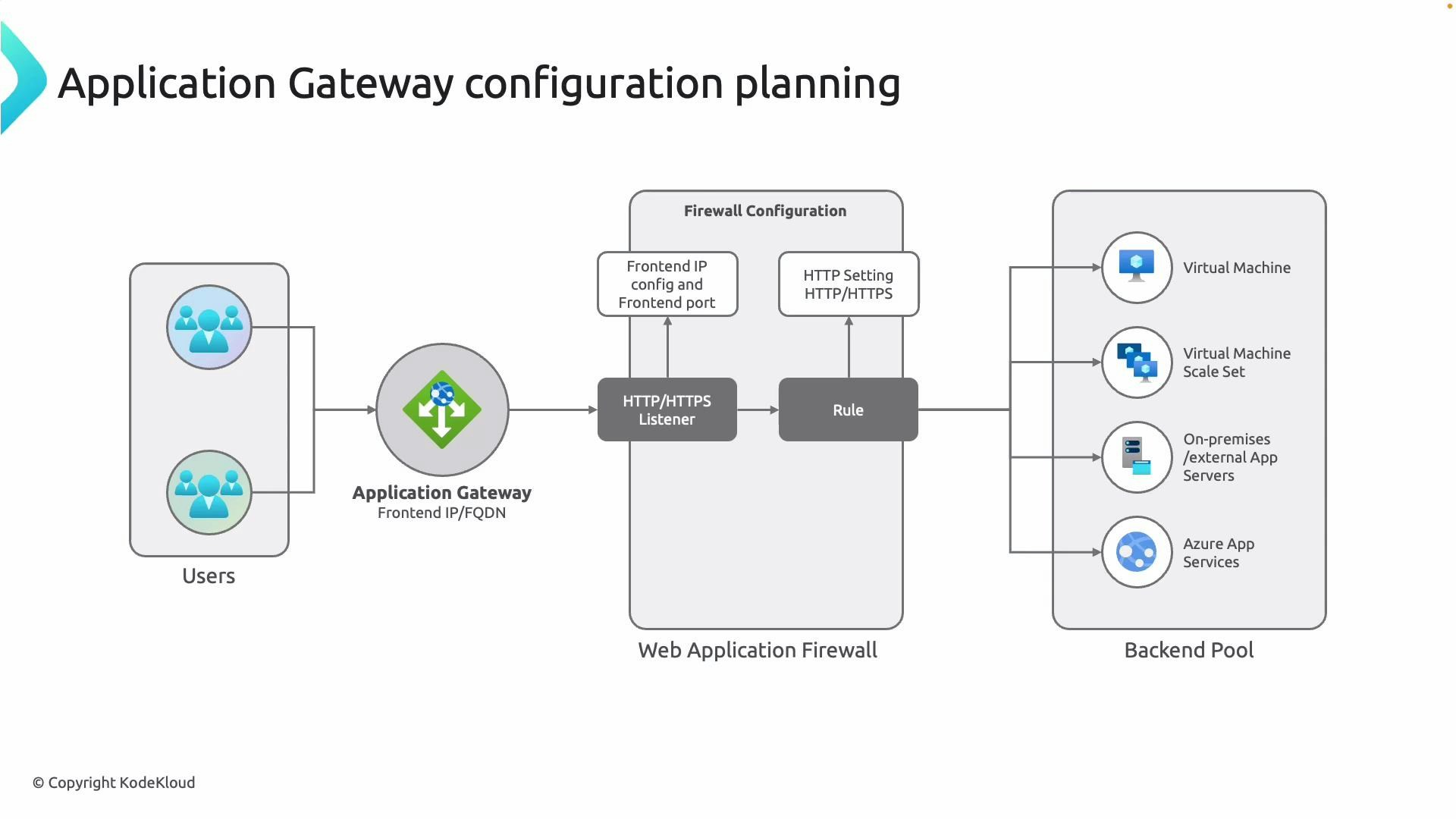
- The request reaches the Application Gateway frontend IP (public or private).
- A configured listener accepts traffic on a specific IP/port/protocol (HTTP/HTTPS).
- The gateway evaluates rules and HTTP settings to decide which backend pool should receive the request.
- Health probes monitor backend instances so traffic is directed only to healthy resources.
- Listener: The endpoint on the gateway that listens on an IP + port + protocol. HTTPS listeners are associated with an SSL certificate.
- Rule: Maps a listener to a backend pool and HTTP settings, defining how traffic should be routed (path‑based, host‑based/multi‑site, or basic).
- HTTP settings: Configure backend port, protocol, host header, cookie-based affinity and other session options.
- Backend pool: Contains targets such as Virtual Machines, VM Scale Sets, Azure App Services (via FQDN), or on‑premises servers.
- Web Application Firewall (WAF): Optional module (WAF_v2 recommended) that detects and blocks common web attacks.
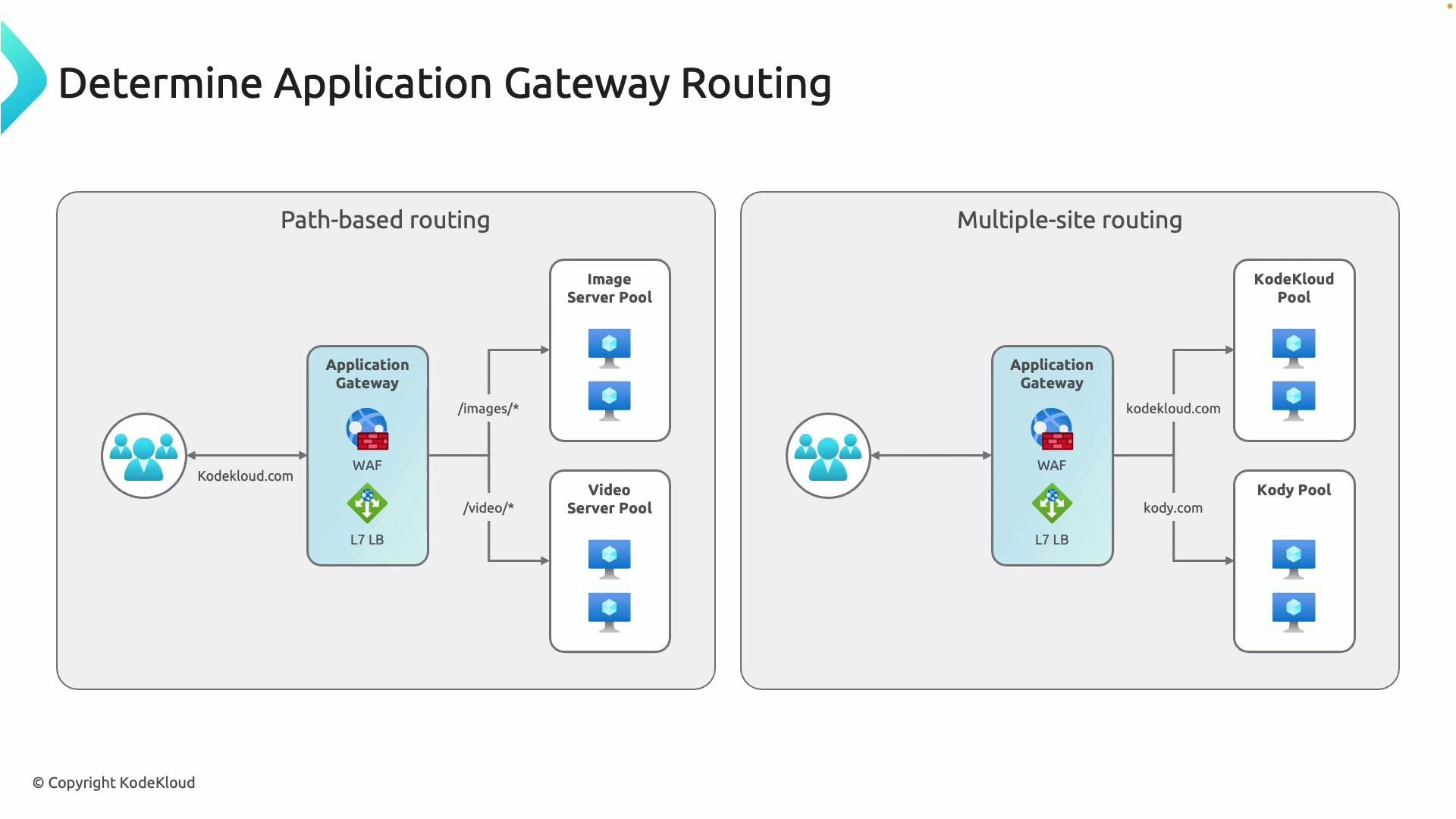
- Path-based routing: Route requests based on URL path (for example, /images/* → image pool, /video/* → video pool).
- Multi-site (host-based) routing: Route requests for different hostnames to separate backend pools using the Host header.
Choosing the right SKU
Selecting the correct Application Gateway SKU is critical for availability, performance and feature requirements. Azure provides several SKUs; the most relevant today are Basic, Standard_v2 and WAF_v2. Standard_v1 and WAF_v1 are legacy SKUs and should be migrated to v2 where possible.| SKU | Best for | Key features |
|---|---|---|
| Basic | Small/test workloads | Lower capacity, limited features, lower SLA |
| Standard_v2 | Production web apps | Autoscaling, zone redundancy, higher SLA, performance improvements |
| WAF_v2 | Production with security needs | All Standard_v2 features + managed WAF for application protection |
- Autoscaling to handle variable traffic
- Zone redundancy for higher availability
- Higher SLA (varies by SKU/version)
- Better integration and performance vs. v1 SKUs
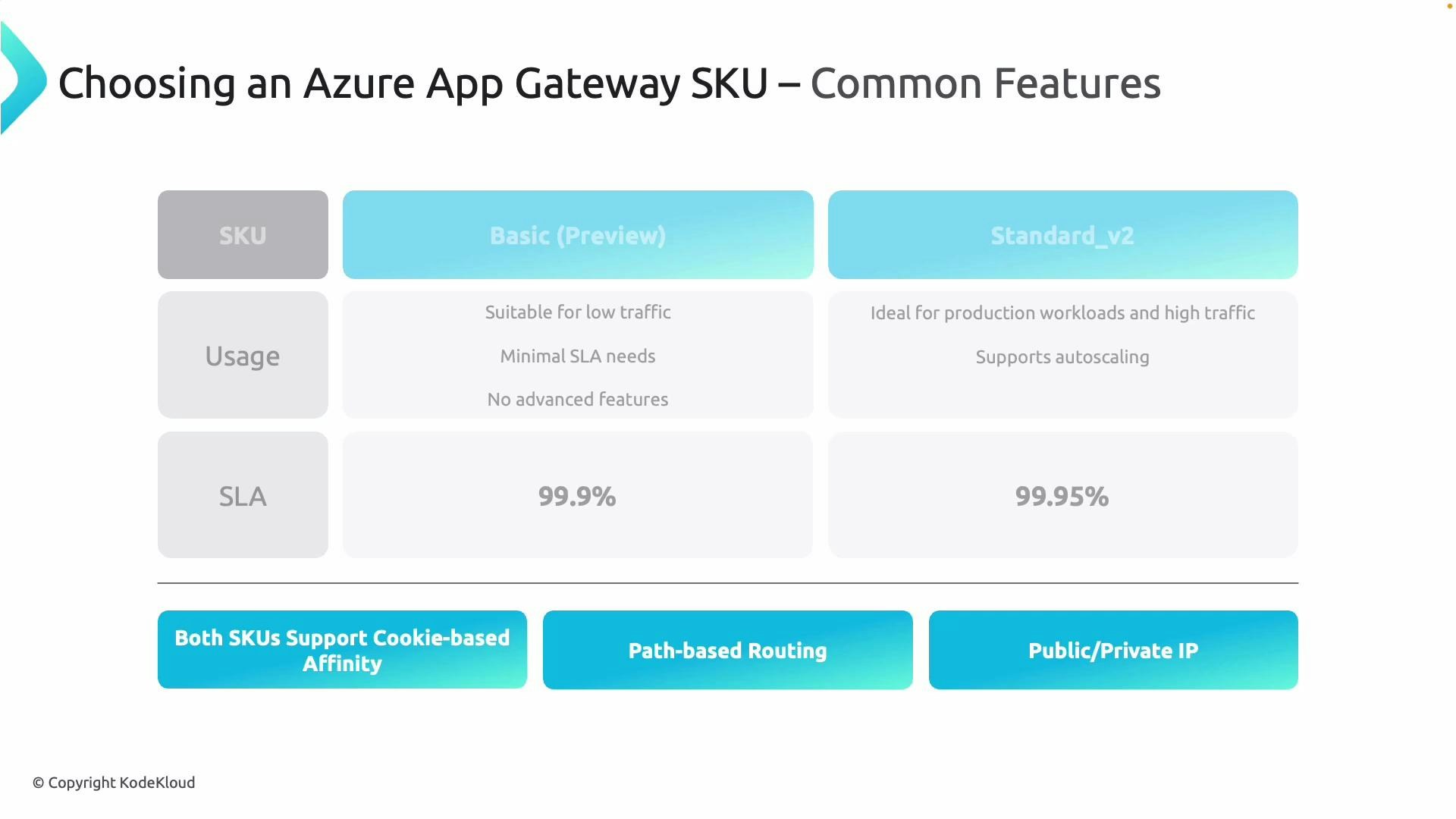
- Estimate connection counts and throughput for your workloads — Standard_v2 supports significantly higher limits than Basic.
- Review regional quota limits and performance guidance in the Azure documentation to size correctly.
- Consider session affinity and cookie settings if backend stateful sessions are required.
Deployment building blocks and request flow
When you deploy an Application Gateway, configure these building blocks in sequence to ensure correct routing and security:- Frontend IP
- Choose public (internet-facing) or private (internal) frontend depending on access requirements.
- Listener
- Define protocol (HTTP/HTTPS), port and attach SSL certificates for HTTPS.
- Rule
- Connects listener → backend pool + HTTP settings. Choose basic, path-based or multi-site rules.
- HTTP settings
- Set backend protocol/port, override host headers if needed, and configure cookie-based affinity.
- Backend pool
- Add targets: Virtual Machines, VM Scale Sets, Azure App Services (by FQDN), or on‑premises servers (via VPN or ExpressRoute).
- Web Application Firewall (optional)
- Enable WAF_v2 for managed rule sets and advanced protection.
Choose the SKU that matches your availability and security needs. Use Standard_v2/WAF_v2 for production workloads to get autoscaling, zone redundancy and managed WAF. If using a third‑party firewall (for example, Palo Alto Networks or FortiGate), design placement so traffic flows through the firewall and Application Gateway in the correct order.
Summary
Azure Application Gateway is the Layer 7 entry point for web apps that provides:- Application-aware routing (path- and host-based)
- SSL offload and certificate management
- Cookie-based session affinity
- Integration with a managed WAF (WAF_v2 recommended)
- Autoscaling and zone redundancy with Standard_v2/WAF_v2
Links and references
- Azure Application Gateway documentation
- Azure Web Application Firewall (WAF)
- Palo Alto Networks
- Fortinet FortiGate