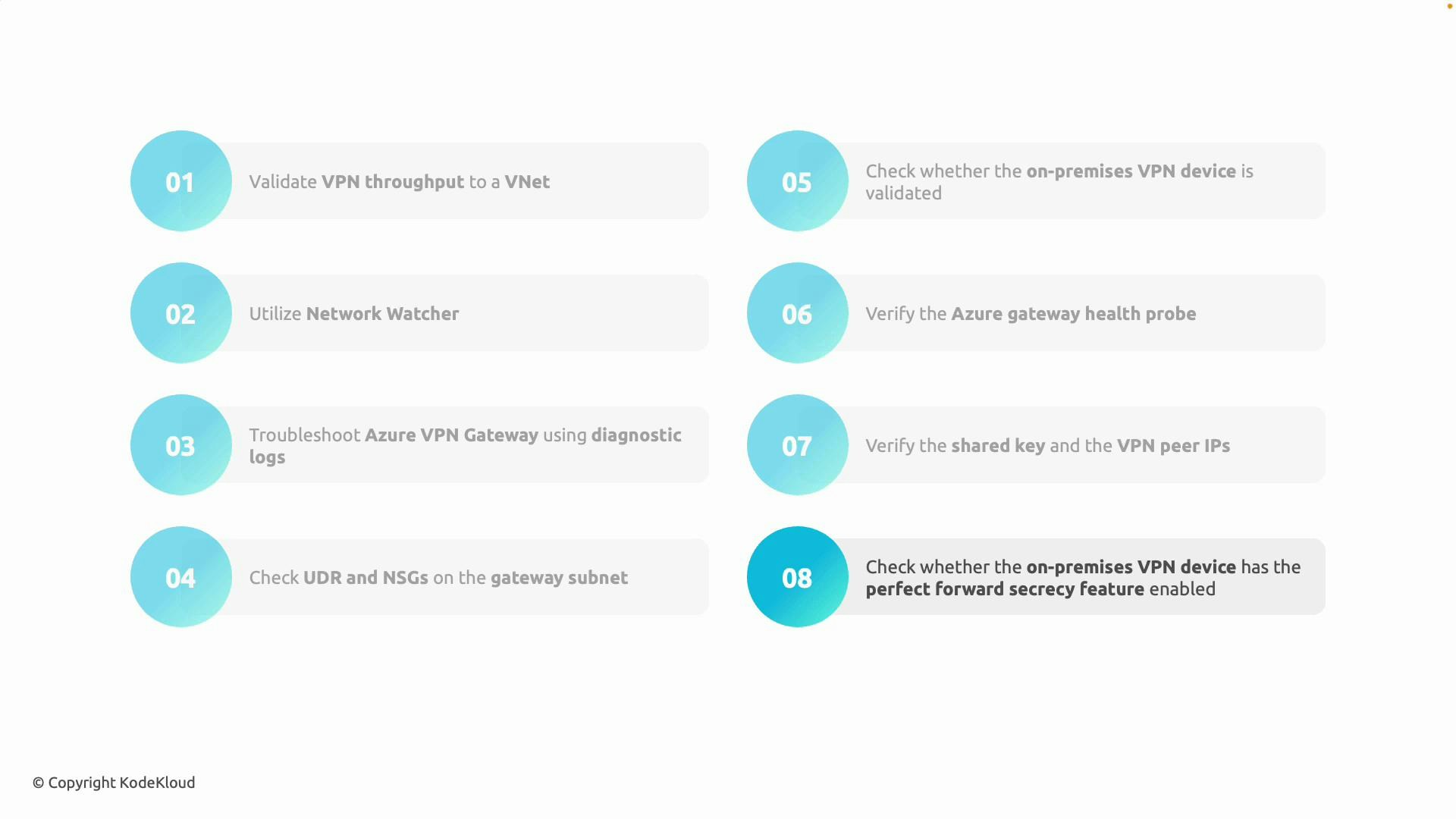
- Validate expected VPN throughput and gateway SKU
- Confirm the chosen gateway SKU supports your required throughput — SKUs have different maximum throughput and concurrent tunnel characteristics. If throughput is lower than expected, measure end-to-end transfer rates between on-premises and Azure (for example, using iperf or similar tools).
- Check for on-premises limitations: proxy devices, intermediate firewalls, ISP or local bandwidth caps, or simultaneous transfers that can affect observed throughput.
- Use Azure Network Watcher to inspect network-level behavior
- Use Azure Network Watcher to validate reachability, run connectivity checks, view next hops, and capture packets (where supported). This helps verify that traffic reaches the gateway and that replies return correctly.
- For packet-level visibility and connection tracebacks, use Network Watcher’s packet capture and connection troubleshoot features:
- Connectivity checks and next hop: validate route decisions and forwarding.
- Packet capture: capture traffic to confirm IKE/IPsec negotiation or to inspect actual traffic flow.
- Enable and analyze VPN gateway diagnostic logs
- Enable diagnostic settings for the virtual network gateway and send logs to a Log Analytics workspace or storage account. Diagnostic logs report tunnel state changes, negotiation events, authentication failures, and rekey activity.
- Analyze logs in Azure Monitor and Log Analytics to spot repeated negotiation failures, IKE Phase1/Phase2 mismatches, or frequent rekeying that indicate misconfiguration or instability.
- Verify routing (UDRs) and network security groups (NSGs)
- Ensure there are no conflicting User-Defined Routes (UDRs) that direct gateway traffic away from the gateway or intercept it unexpectedly. The gateway subnet must not contain UDRs that override the Azure-managed routes required for VPN operation.
- Confirm NSGs do not block essential traffic. Allow the following common protocols and ports (see table below).
| Protocol | Port / Identifier | Use case |
|---|---|---|
| UDP | 500 | IKE Phase 1 (ISAKMP) |
| UDP | 4500 | IPsec NAT-T (encapsulated ESP) |
| ESP | 50 (protocol) | Encapsulated payload (IPsec ESP) |
| ICMP | — | Path MTU discovery and connectivity checks |
GatewaySubnet and is appropriately sized (Microsoft recommends at least /27 for most deployments depending on features).
- Confirm on-premises device compatibility and configuration
- Verify your VPN device model and firmware are supported and that configuration follows Microsoft’s sample templates and validated device list.
- Check public IP addresses of peers — ensure Azure and on-premises sides point to the correct peer IPs. If NAT is used, ensure NAT-T is enabled and configured properly.
- Check shared secret (PSK) and peer IP addresses
- A mismatched pre-shared key (PSK) prevents tunnel establishment. Verify the PSK is identical on both sides and that the peer endpoint addresses match.
- If certificates are used instead of PSK, validate certificate expiration, trust chain, and thumbprints.
- Verify Perfect Forward Secrecy (PFS) and encryption policy agreement
- Ensure both peers agree on the IKE/IKEv2 parameters: encryption algorithm, integrity/hash algorithm, Diffie-Hellman group (PFS), and lifetimes. A mismatch in these parameters will cause IKE to fail during negotiation.
- Confirm the IKE version (v1 vs v2) is compatible with the Azure gateway SKU and configured consistently on both ends.
- Check Azure gateway health and automated probes
- Review the virtual network gateway status in the Azure portal for health warnings or errors. Azure uses internal health probes and will expose statuses for the gateway and tunnels.
- If the gateway is reported unhealthy, review recent configuration changes, route or NSG changes, and diagnostic logs to find correlation with the outage.
| Check | Why it matters | Action |
|---|---|---|
| Gateway SKU & throughput | Ensure capacity meets needs | Validate SKU and run throughput tests (iperf) |
| Network Watcher checks | Confirms reachability and routing | Run connectivity checks and packet captures |
| Diagnostic logs | Shows negotiation failures & rekeys | Enable diagnostics to Log Analytics |
| NSGs & UDRs | May block or reroute VPN traffic | Verify GatewaySubnet is clean and NSGs allow IKE/IPsec |
| PSK & peer IP | Prevents tunnel establishment if wrong | Confirm PSK and peer endpoint addresses |
| IKE/PFS policies | Policy mismatch stops IKE | Align encryption, hashing, DH groups, lifetimes |
| Device compatibility | Unsupported models/configs fail | Use Microsoft-validated configs and firmware |
| Gateway health | Azure-side probe results | Check portal and correlate with logs |
Enable gateway diagnostics as soon as you deploy the gateway. Diagnostic logs combined with Network Watcher captures greatly speed up root-cause analysis and provide historical context for intermittent issues.
Be sure the gateway subnet is named exactly
GatewaySubnet and does not contain NSGs or conflicting UDRs that block IKE/IPsec traffic. Misconfigured subnet rules are a frequent cause of VPN failures.- Enable diagnostics and streaming logs to a Log Analytics workspace.
- Use Network Watcher connection troubleshoot and packet capture to verify traffic flow.
- Configure the pre-shared key, IKE policies, and enable NAT-T or active-active mode if required.
- Active-active is used for high availability and to support multiple concurrent VPN tunnels whereby both gateway instances are active. When planning active-active deployments, ensure:
- You have multiple public IPs and routes configured.
- On-premises devices support multi-tunnel or route-based configurations.
- Load balancing and route advertisements are aligned with your architecture.
- Azure Network Watcher overview: https://learn.microsoft.com/azure/network-watcher/network-watcher-monitoring-overview
- Diagnostic settings: https://learn.microsoft.com/azure/azure-monitor/essentials/diagnostic-settings
- Log Analytics workspace: https://learn.microsoft.com/azure/azure-monitor/logs/log-analytics-workspace-overview
- VPN device guidance and sample configurations: https://learn.microsoft.com/azure/vpn-gateway/vpn-gateway-about-vpn-devices