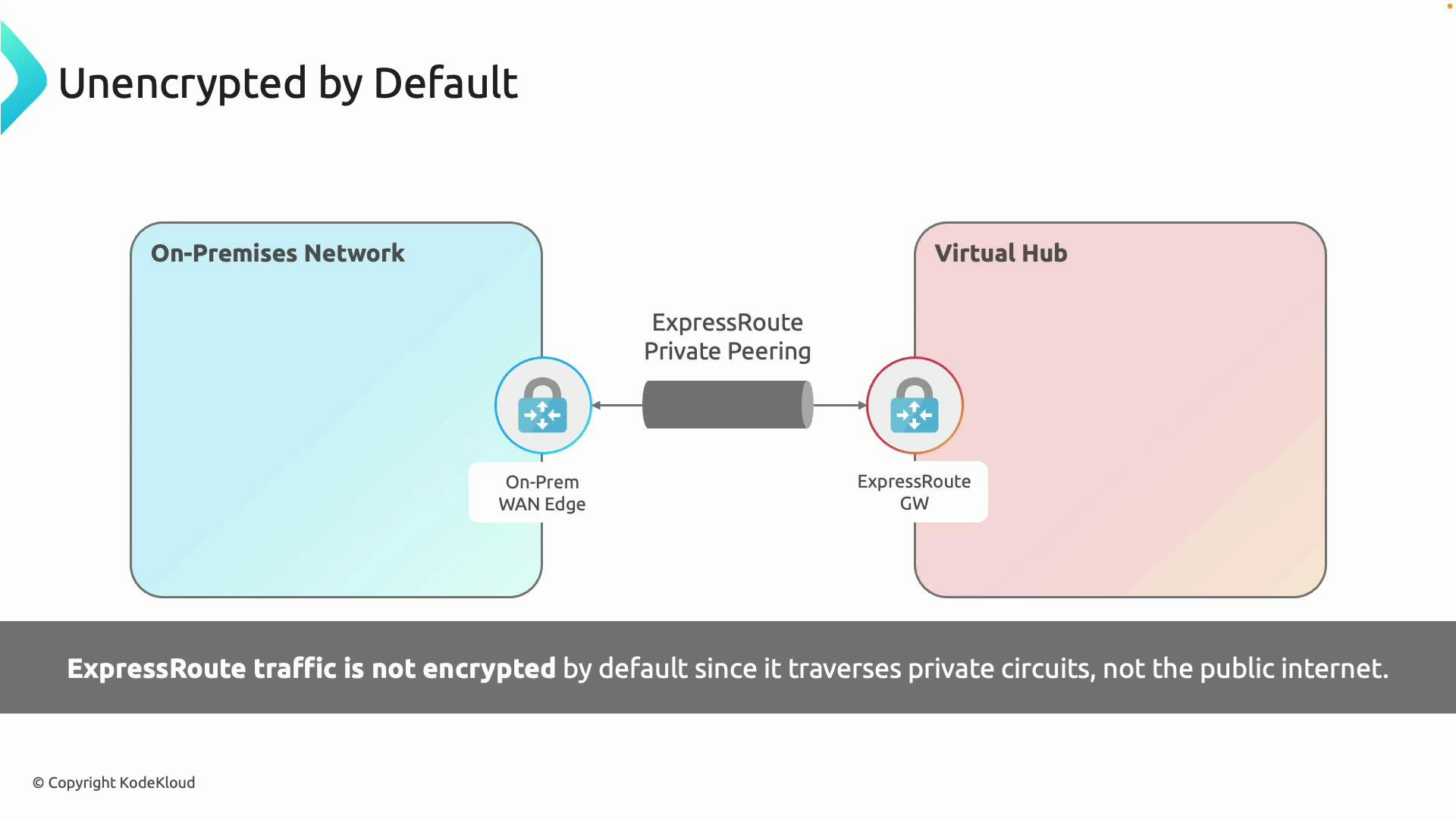
ExpressRoute gives private connectivity but does not automatically encrypt traffic. If your policies require encryption in transit, enable MACsec on the physical interconnect (when supported) or deploy customer‑managed IPsec to secure end‑to‑end traffic.
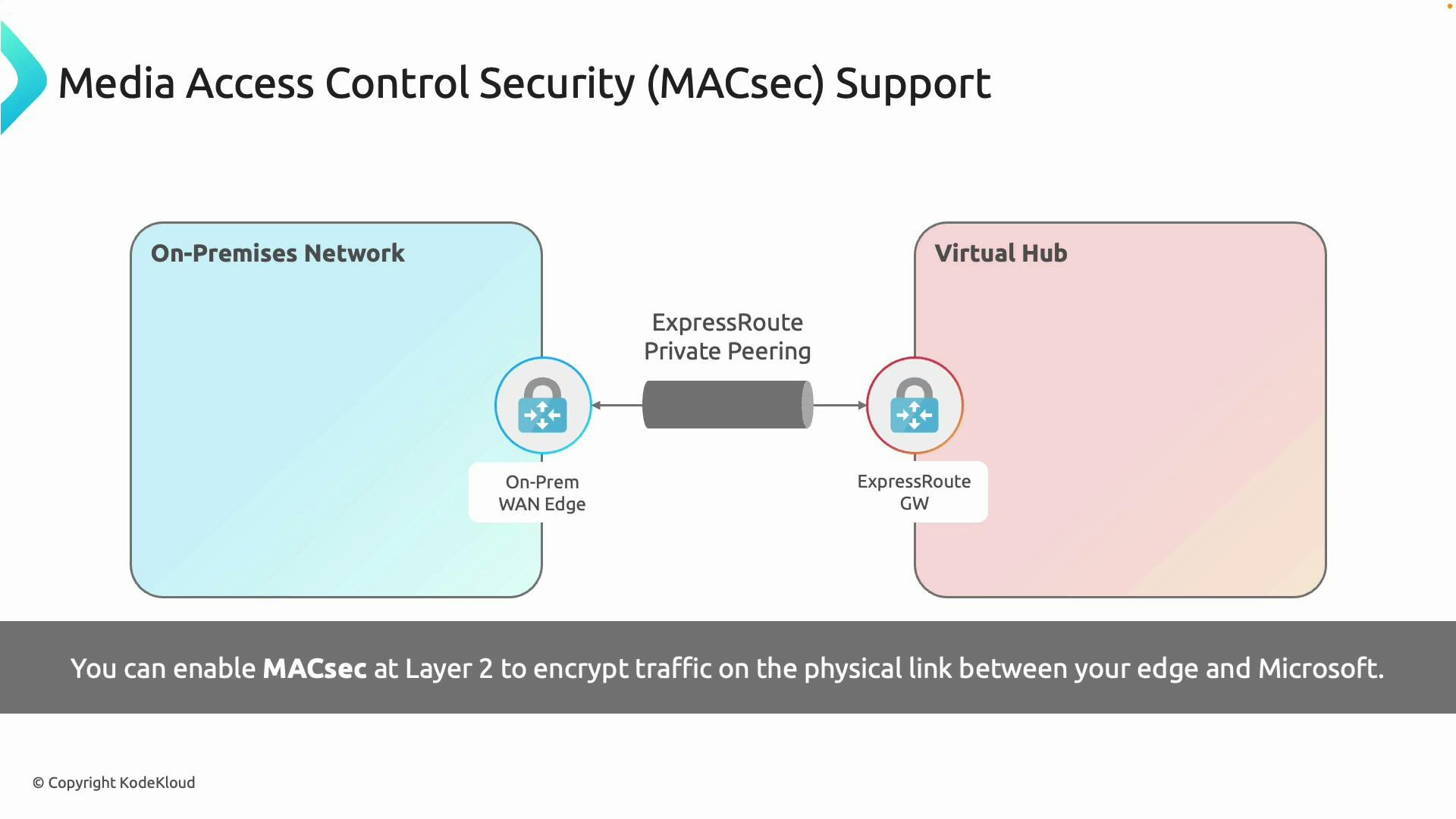
- MACsec — encrypt the physical (Layer 2) link between your on‑premises WAN edge and Microsoft’s edge.
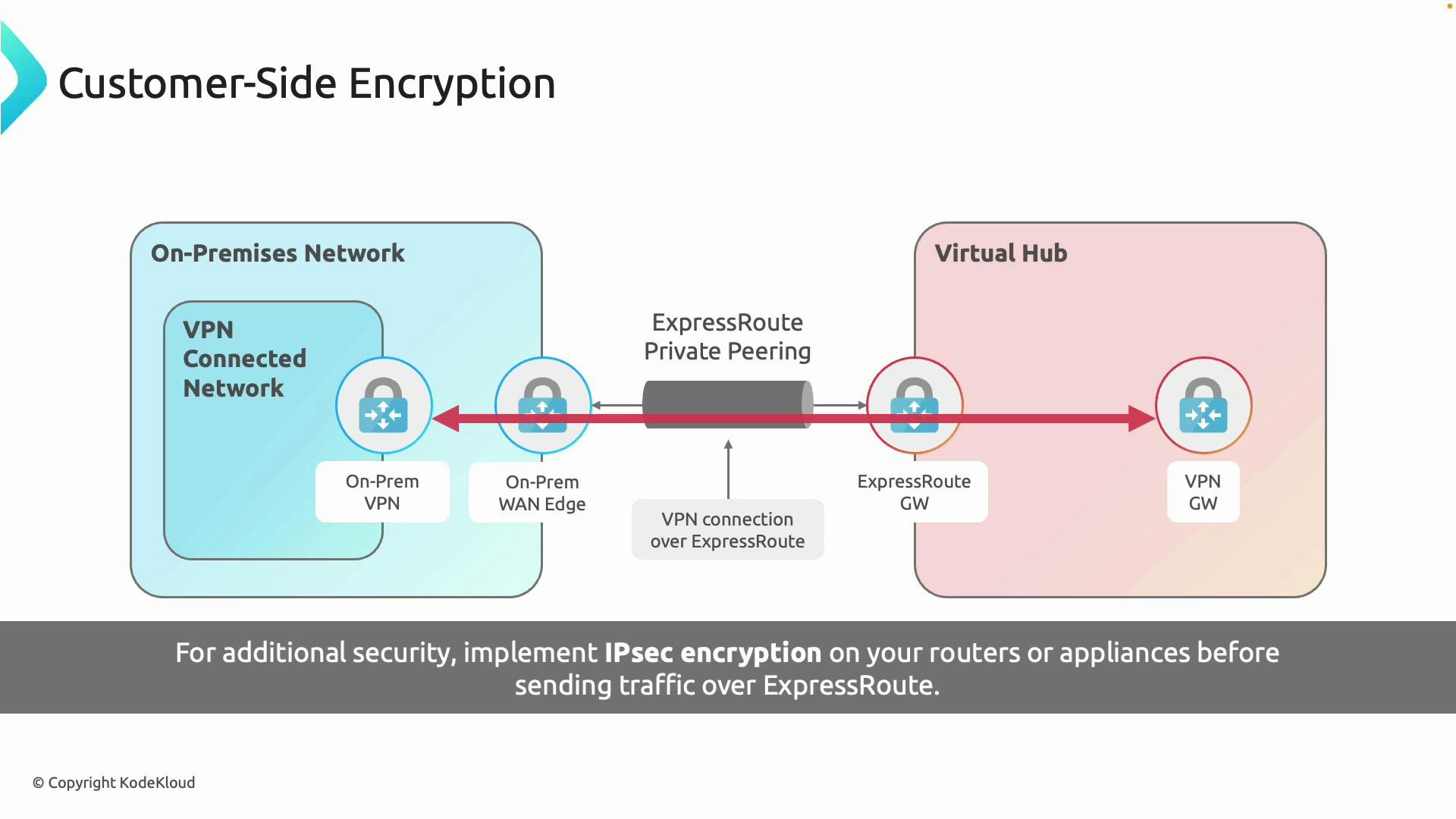
- Customer‑managed IPsec — place an IPsec tunnel over the ExpressRoute private circuit for end‑to‑end encryption under your control.
MACsec (Media Access Control Security)
MACsec is a Layer 2 protocol that provides hop‑by‑hop encryption on the physical link between your WAN/edge device and Microsoft Edge. It protects against a physical tap on the cable, ensuring frames traversing the interconnect are encrypted. Key points:- MACsec encrypts all Layer 2 traffic on the physical interconnect.
- It must be supported and enabled on your WAN edge device, the carrier, and on Microsoft’s side at the peering/interconnect location.
- Use MACsec when regulations or your security posture require encryption of the physical link itself (common in finance, government, and healthcare).
- Check hardware compatibility and firmware versions for MACsec support on routers/switches.
- Verify your ExpressRoute circuit and carrier support MACsec at your chosen exchange/colocation point.
- MACsec is transparent to higher‑level routing and does not change IP addressing or routing behavior.
Customer-side IPsec (End-to-end encryption)
If you need encryption from an on‑premises endpoint all the way to a specific Azure resource, deploy a customer‑managed IPsec tunnel and route it over the ExpressRoute circuit. This creates an encrypted overlay (IPsec) that runs on top of the private circuit, delivering end‑to‑end confidentiality and integrity. Key points:- IPsec provides end‑to‑end encryption between two IP endpoints (for example, on‑premises gateway and Azure VPN gateway or an NVA in Azure).
- You can run IPsec over the ExpressRoute private peering; the underlying path remains private while payloads are encrypted.
- Customer‑managed IPsec gives you control over algorithms, key management, tunnel endpoints, and lifetime, but introduces CPU overhead and potential additional latency.
- Decide where the tunnel terminates: Azure VPN Gateway, a VPN-capable virtual appliance (NVA), or a hybrid design.
- Ensure routing works as expected (BGP, UDRs) so encrypted traffic traverses the ExpressRoute circuit.
- Monitor throughput and CPU usage on the on‑premises device and the Azure tunnel endpoint; IPsec encryption increases resource use.
MACsec vs Customer‑side IPsec — Comparison
| Feature | MACsec (Layer 2) | Customer‑side IPsec (Layer 3) |
|---|---|---|
| Encryption scope | Physical link between edges | End‑to‑end between IP endpoints |
| Typical use case | Protect the physical interconnect (regulatory, anti‑tamper) | Protect application payloads across the private circuit |
| Hardware dependency | Requires MACsec‑capable devices and provider support | Requires IPsec-capable gateway/NVA; vendor agnostic |
| Control over keys/ciphers | Keys typically managed by carrier/MS collaboration | Full customer control of keys, ciphers, and tunnel endpoints |
| Performance impact | Minimal (hardware offload) | CPU/latency overhead depending on endpoint resources |
| Implementation complexity | Carrier + vendor coordination | Configuration at customer gateways and Azure tunnel endpoints |
When to choose which option
-
Choose MACsec when:
- Your compliance requirements mandate protection of the physical link.
- You want transparent encryption with minimal impact on IP routing.
- Your carrier and on‑premises hardware support MACsec.
-
Choose customer‑managed IPsec when:
- You need full end‑to‑end encryption between application endpoints.
- You require control over cipher suites, key rotation, and termination points.
- You accept the tradeoffs of additional latency and computational overhead.
MACsec availability depends on your router/switch hardware, the carrier, and the interconnect location. Verify support with your network equipment vendor and ExpressRoute provider before planning. Customer‑managed IPsec introduces CPU and latency overhead — test performance impact on your workloads.
Implementation checklist
- Verify ExpressRoute circuit type and interconnect location support for MACsec.
- Confirm your WAN edge (router/switch) firmware and models are MACsec compatible.
- Decide tunnel termination for IPsec (Azure VPN Gateway vs NVA) and validate routing (BGP, UDR).
- Plan key management and rotation for IPsec tunnels.
- Benchmark throughput and latency with encryption enabled to confirm SLA/requirements.
- Coordinate with carrier and Microsoft support for MACsec activation and testing if applicable.
Links and references
- Azure ExpressRoute documentation
- Azure VPN Gateway documentation
- IPsec and IKE overview (Microsoft Learn)
- Consult your network hardware vendor and ExpressRoute provider for device‑specific MACsec instructions and carrier requirements.
- ExpressRoute provides private connectivity but is not encrypted by default.
- Use MACsec to encrypt the physical interconnect when supported.
- Use customer‑managed IPsec to achieve end‑to‑end encryption and full control over keys and ciphers.
- Consider combining both approaches for a layered security model that meets performance and compliance needs.