Planning checklist
Plan these items before deploying a site-to-site VPN. Proper planning reduces downtime and avoids common pitfalls such as routing conflicts or insufficient throughput.| Consideration | What to decide | Why it matters |
|---|---|---|
| Address spaces | Ensure Azure VNet and on‑premises networks do NOT overlap (e.g., Azure: 10.1.0.0/16, On‑Prem: 192.168.3.0/24) | Overlapping prefixes will prevent correct routing across the VPN. |
| Gateway SKU & performance | Choose a VPN Gateway SKU (VpnGw1, VpnGw2, VpnGw3, etc.) based on throughput, features (BGP, active/active) and SLA needs | SKU determines supported bandwidth, concurrent tunnels, and feature availability. |
| Encryption & authentication | Agree on PSK, IKE version (IKEv2 recommended), encryption (AES‑256), integrity, DH group, and lifetimes | Incompatible settings will prevent tunnel establishment; choose modern algorithms. |
| On‑prem device compatibility | Verify vendor model/OS is supported by Azure and can be configured with required IPsec/IKE parameters | Unsupported devices may require a firmware upgrade or replacement. |
| High availability & routing | Decide active/active or active/standby gateways, and whether to use BGP or static routes | HA and routing affect failover behavior and route distribution. |
| Compliance & key management | Ensure encryption, logging, and key handling meet regulatory obligations | Data‑in‑transit requirements (e.g., FIPS, audit logs) may mandate specific controls. |
| Post‑deployment testing | Define verification steps and monitoring (ping tests, TCP tests, Network Watcher, VPN logs) | Confirms tunnel stability and correct traffic flows after setup. |
Overlapping IP address ranges between Azure and on‑premises will break routing. Always plan and validate address prefixes before creating VNets or Local Network Gateways.
Use strong pre-shared keys (PSKs), modern encryption (AES‑256 where possible), and IKEv2 (preferred). Ensure both sides match on encryption, integrity, Diffie‑Hellman group, and SA lifetimes. Avoid weak or default keys and document configuration for future troubleshooting.
High-level setup steps
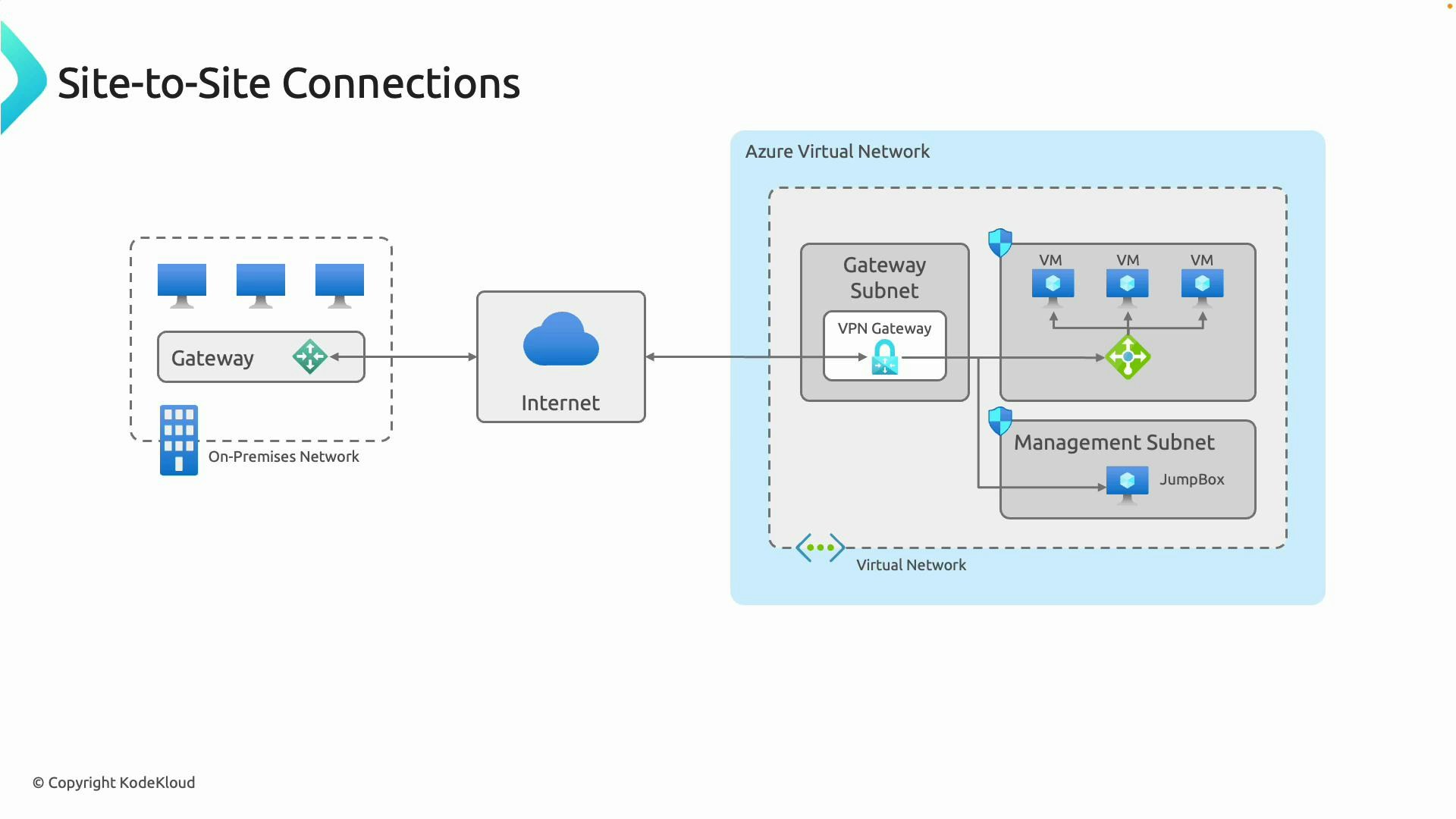
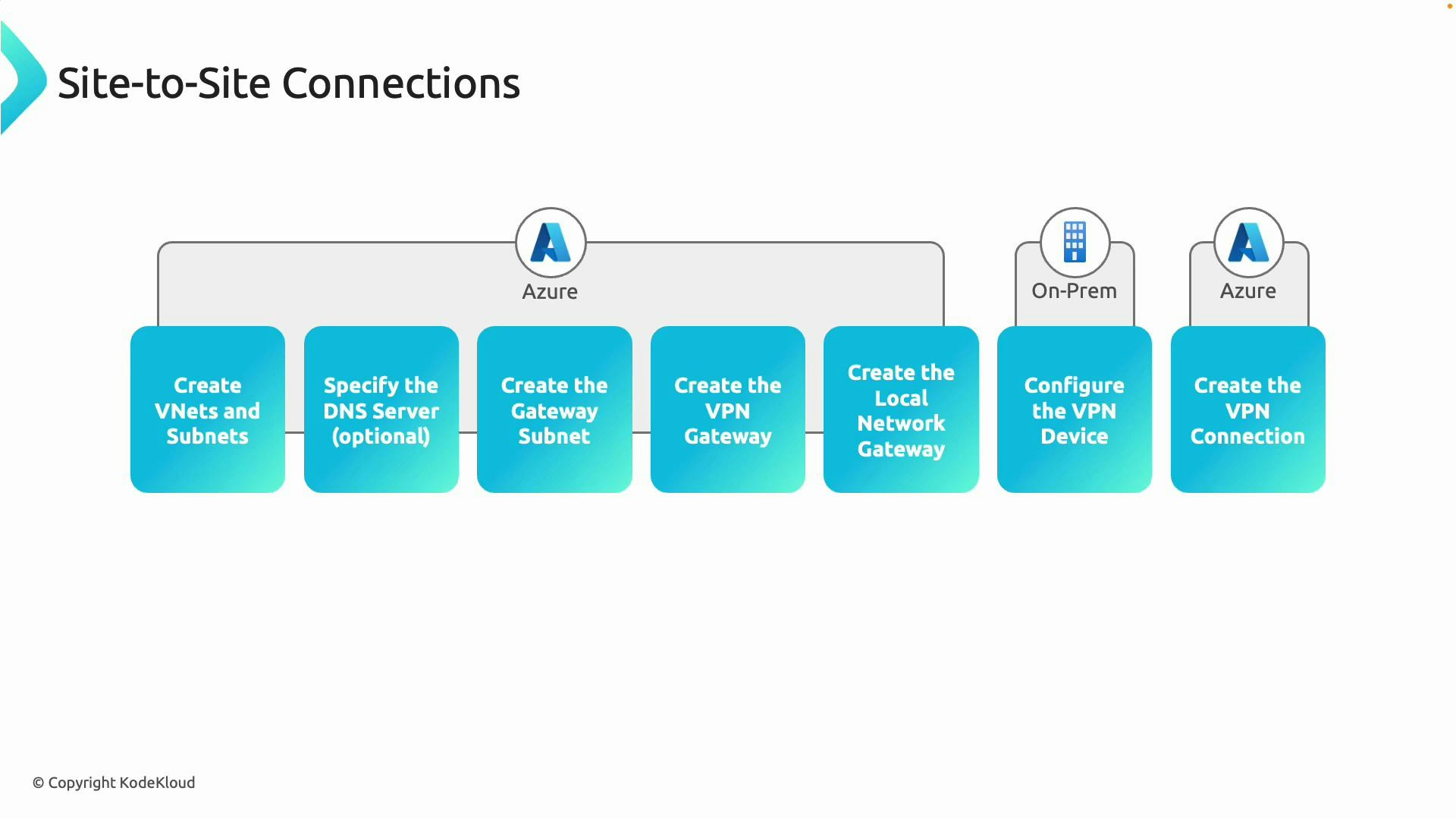
Typical sequence for deploying a site-to-site VPN:- Create the Azure VNet and required subnets for workloads.
- Create a GatewaySubnet named exactly “GatewaySubnet” and allocate an appropriate range (recommended /27 or larger depending on gateway SKU).
- Provision the VPN Gateway in the GatewaySubnet (select the VPN gateway SKU and type: RouteBased for most modern scenarios).
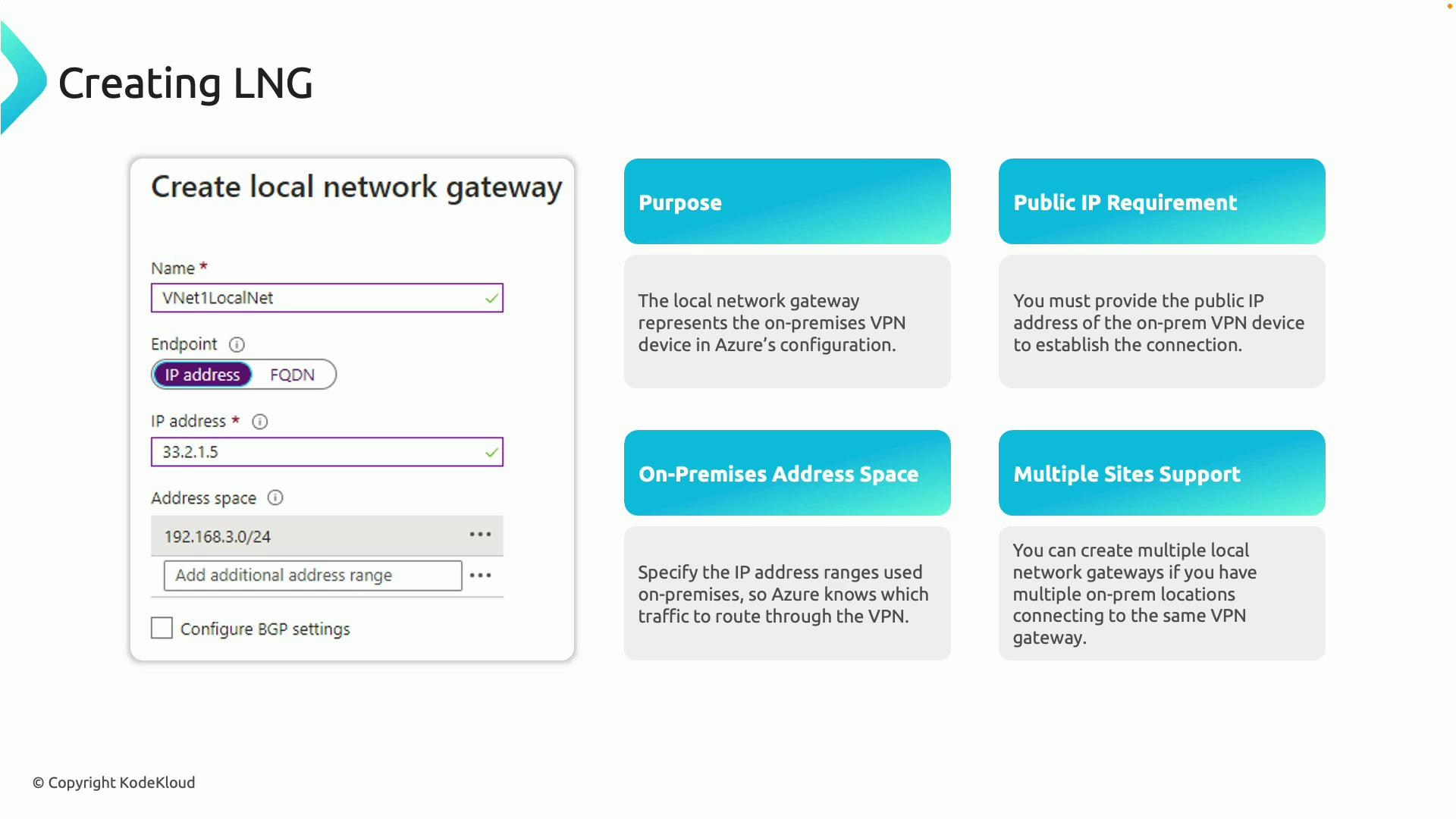
- Create a Local Network Gateway (LNG) in Azure that represents your on‑premises public IP/FQDN and on‑premises address prefixes.
- Configure the on‑premises VPN device with the Azure VPN Gateway public IP, shared key, and matching IPsec/IKE parameters.
- Create the site‑to‑site VPN connection in Azure linking the VPN Gateway and the LNG (specify PSK and BGP if used).
- Verify tunnel status and test connectivity between Azure VMs and on‑premises hosts. Monitor and adjust as needed.
Example Azure CLI commands (illustrative)
The following az CLI examples demonstrate one common deployment flow. Replace resource names, prefixes, locations, and the PSK with values for your environment. Create a resource group:Local Network Gateway (LNG)
A Local Network Gateway (LNG) is a logical Azure object that represents your on‑premises VPN endpoint and its reachable address prefixes. It contains:- The public IP address (or FQDN) of the on‑premises VPN device.
- The on‑premises IP address ranges that Azure should route to the LNG.
- Configure your on‑premises VPN device with:
- Azure VPN Gateway public IP
- The agreed pre‑shared key
- Matching IPsec/IKE parameters (algorithms, DH group, lifetimes)
- Create the site‑to‑site connection in Azure (if not created already).
- Verify that the tunnel establishes and routes traffic correctly.
Post-deployment verification and monitoring
Verify connection and troubleshoot using the az CLI: Check connection status:Links and references
- Azure VPN Gateway overview: https://learn.microsoft.com/azure/vpn-gateway/
- Configure a site‑to‑site VPN using the Azure portal: https://learn.microsoft.com/azure/vpn-gateway/vpn-gateway-howto-site-to-site-resource-manager-portal
- Azure CLI reference for VPN Gateway: https://learn.microsoft.com/azure/cli/reference/topic/vpn
- IPsec / IKE background: https://en.wikipedia.org/wiki/IPsec
- IKEv2 details: https://en.wikipedia.org/wiki/Internet_Key_Exchange#IKEv2