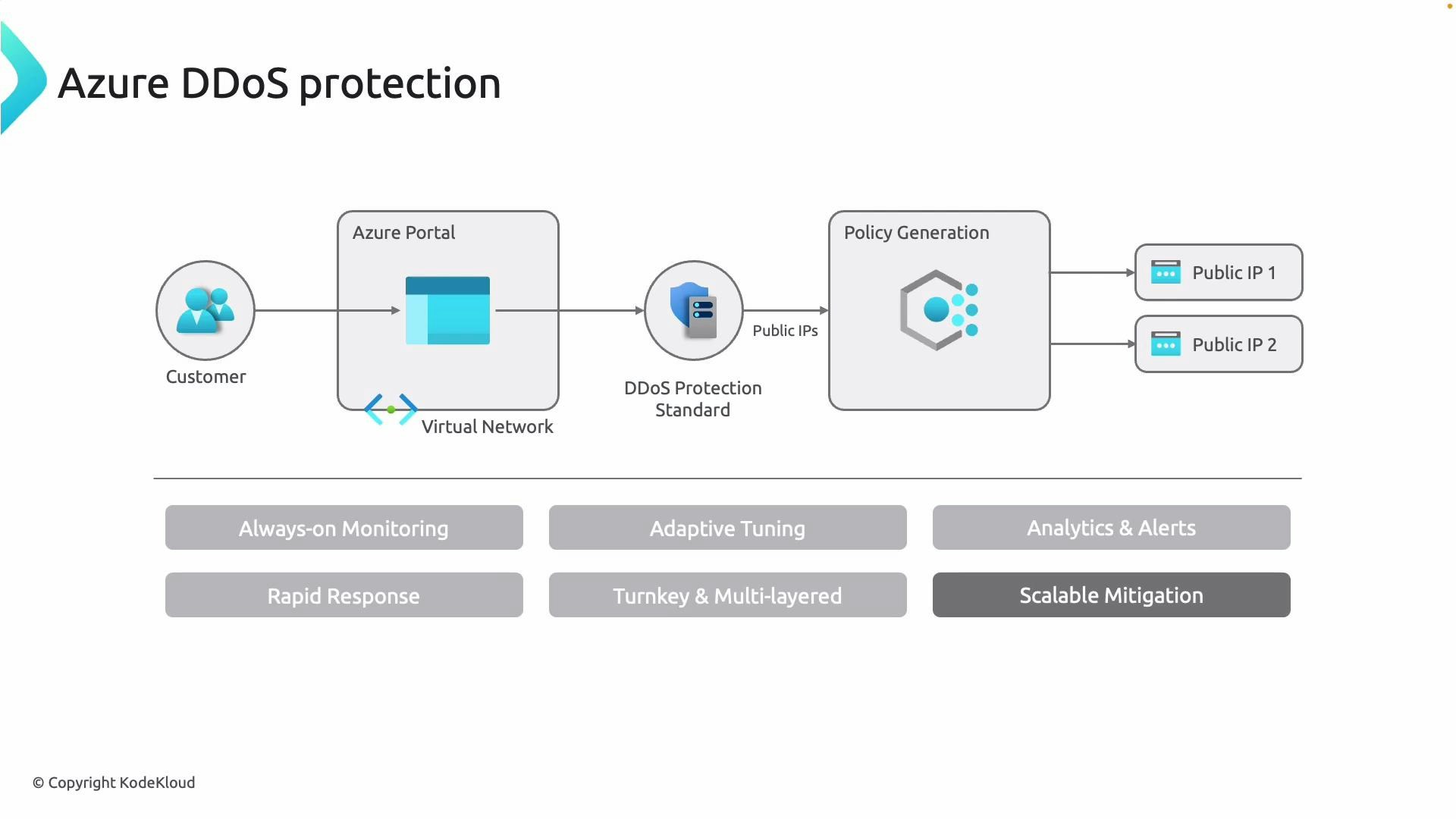
Protection models: network-level vs per-IP
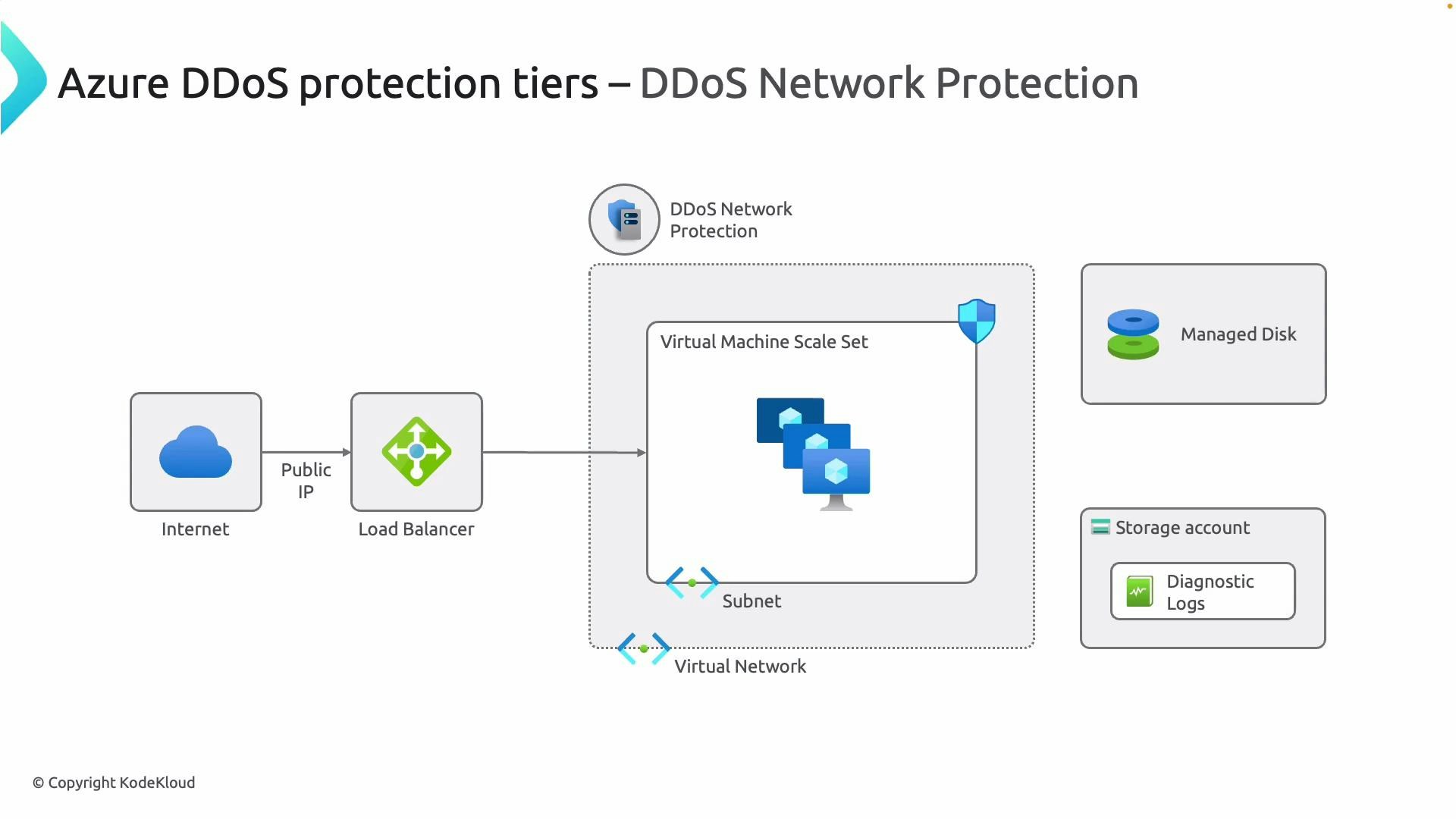
Azure offers two primary DDoS protection models—each fits different operational needs:- DDoS Network Protection (Plan-level): Attach a protection plan to one or more virtual networks (VNets). Traffic is filtered upstream before reaching resources that rely on public IPs inside the VNet (virtual machines, load balancers, Application Gateway, Azure Firewall, Bastion, etc.).
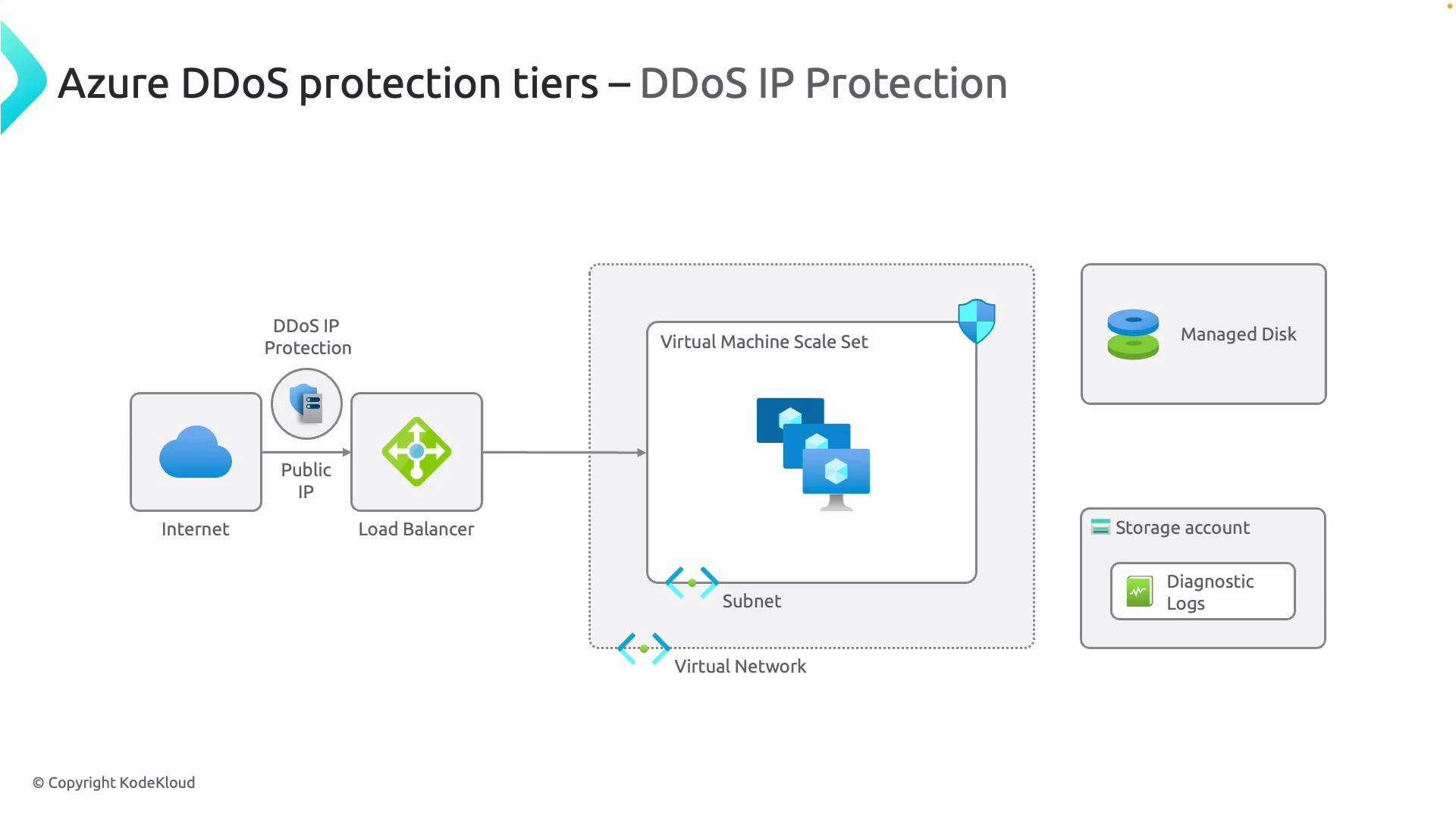
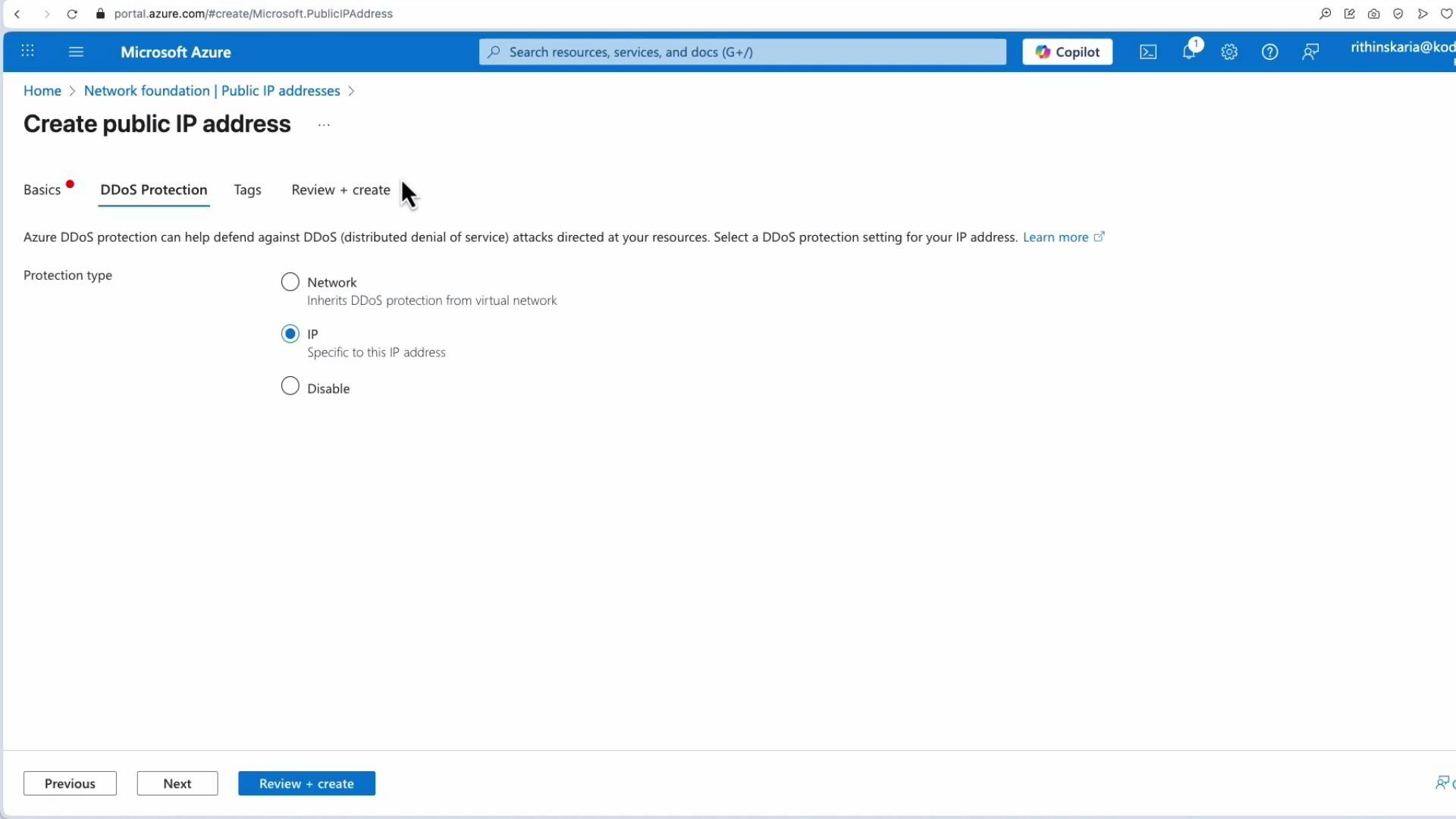
- DDoS IP Protection (Per-IP): Protect individual public IP addresses (standalone public IPs or those associated with a load balancer). Onboarding and billing are per protected IP.
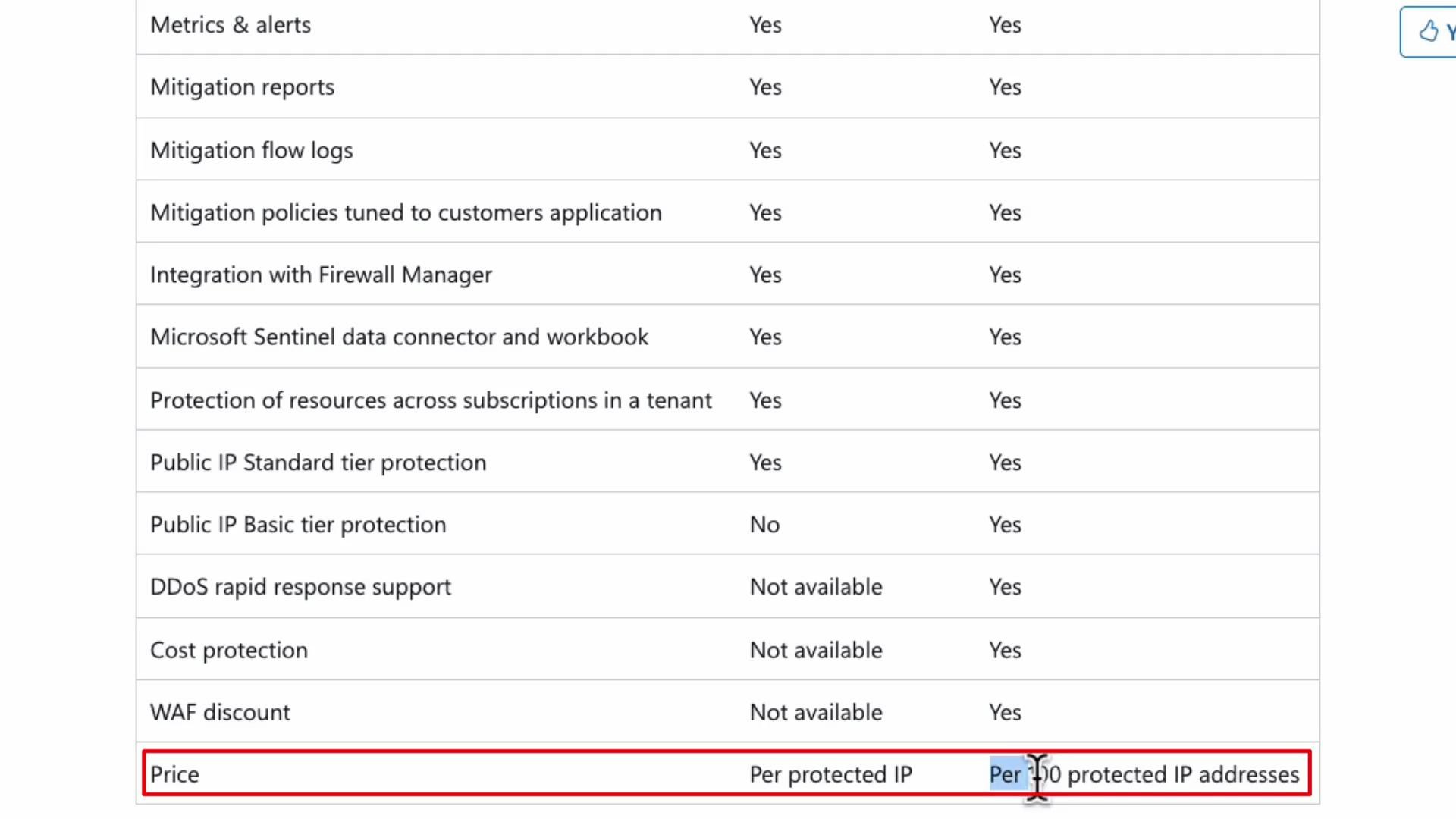
| Capability | DDoS Network Protection (Plan-level) | DDoS IP Protection (Per-IP) |
|---|---|---|
| Scope | Virtual networks (many resources) | Individual public IP addresses |
| Billing | Fixed monthly fee (covers a bundle/block of IPs) | Per protected IP |
| Common use cases | Hub-and-spoke, multi-resource VNets | Single critical public endpoint |
| Rapid Response & SLA | Priority support often included | Available per-IP, depends on SKU |
| Mitigation reporting & flow logs | Included (when enabled) | Included (when enabled) |
Operational best practices
- Enable diagnostics (flow logs and metrics) and send telemetry to a storage account, Log Analytics workspace, or Event Hub for monitoring and forensic analysis. See:
- Log Analytics workspace: https://learn.microsoft.com/azure/azure-monitor/logs/log-analytics-workspace
- Azure Event Hubs: https://learn.microsoft.com/azure/event-hubs/
- Configure Azure Monitor alerts to notify security/on-call teams about mitigation actions, thresholds, or anomalous traffic patterns:
- Azure Monitor alerts overview: https://learn.microsoft.com/azure/azure-monitor/alerts/alerts-overview
- For planned attack simulation or testing, coordinate with Microsoft support to avoid unintended service disruption and to ensure tests are performed safely.
When a DDoS protection plan is attached to a virtual network, the VNet’s resources that use public IPs (load balancers, Application Gateway, and VMs with public IPs) automatically inherit protection. For per-IP protection, you must onboard each public IP individually.
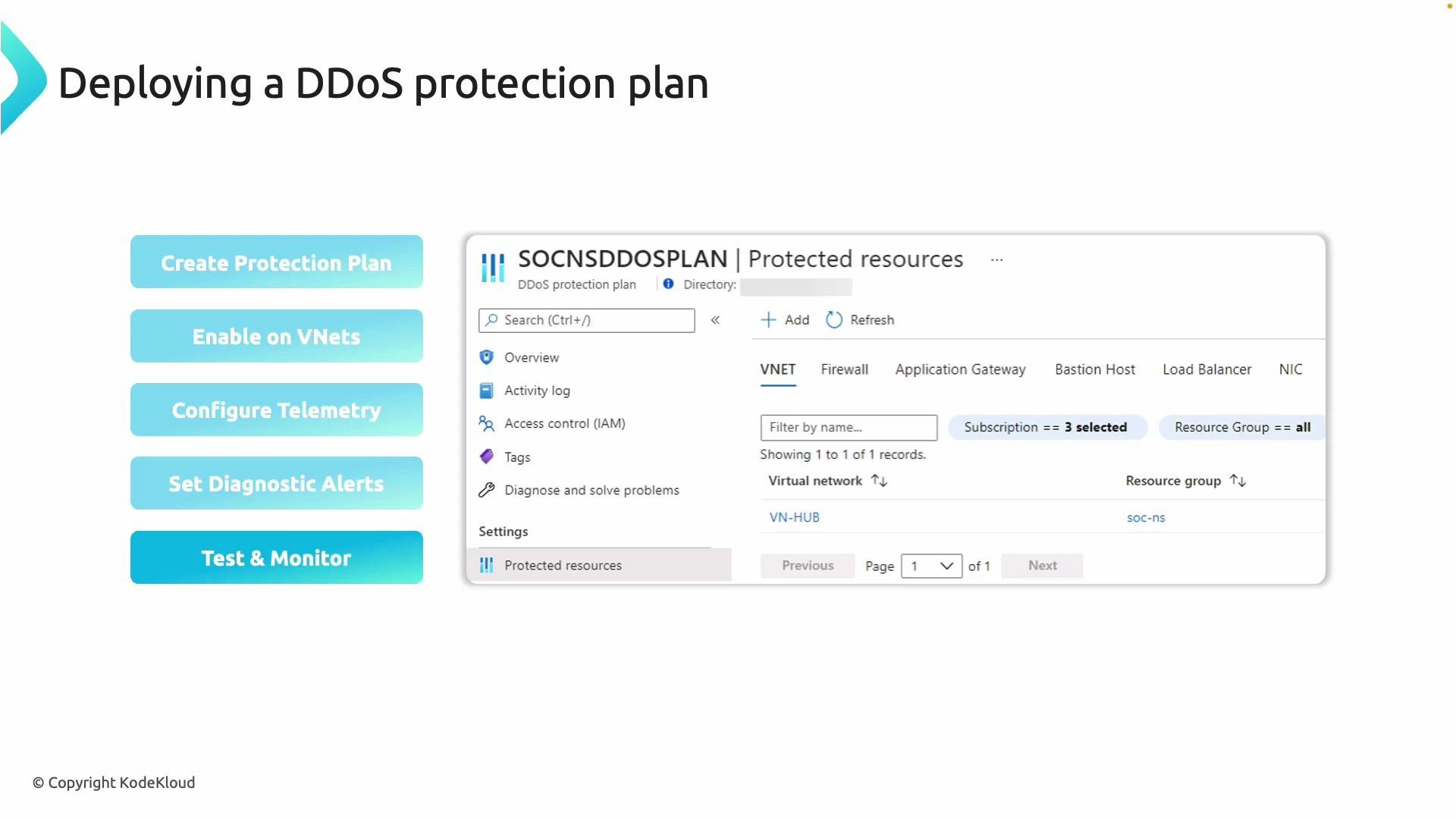
Deployment checklist and workflow
Follow these steps to deploy and operate DDoS protection effectively:- Create a DDoS protection plan resource.
- Attach the plan to the virtual networks you want to protect.
- Enable telemetry/diagnostics (send flow logs and metrics to storage or Log Analytics).
- Configure diagnostic alerts in Azure Monitor to notify security teams.
- Test and monitor the behavior—coordinate tests with Microsoft if you plan simulated attack traffic.
- Create a DDoS protection plan via Azure CLI (example):
CLI
- Attach a VNet to the plan:
CLI
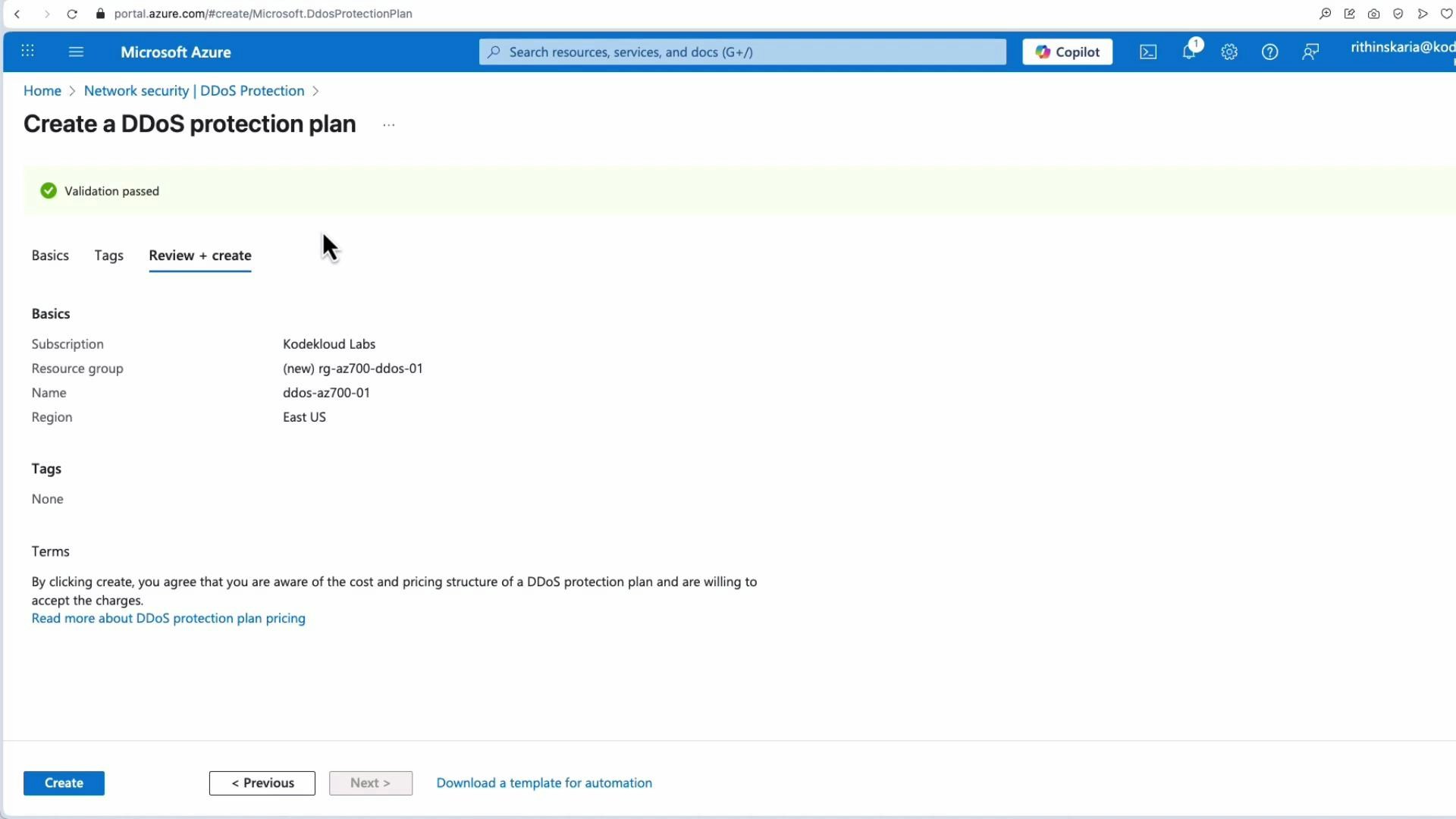
DDoS protection plans and per-IP protection incur charges. Review the pricing page (https://azure.microsoft.com/pricing/details/ddos-protection/) and confirm billing impact before provisioning resources in production.
Additional resources
- Azure DDoS Protection documentation: https://learn.microsoft.com/azure/ddos-protection/
- Azure Monitor and diagnostics: https://learn.microsoft.com/azure/azure-monitor/
- Azure pricing: https://azure.microsoft.com/pricing/