Zone-redundant virtual network gateways
Azure supports zone-redundant virtual network gateways to protect against zonal failures. When zone redundancy is enabled, VPN Gateway instances are deployed across multiple Availability Zones within a region. If one Availability Zone experiences an outage, the gateway instance in another zone continues handling traffic so connections stay up.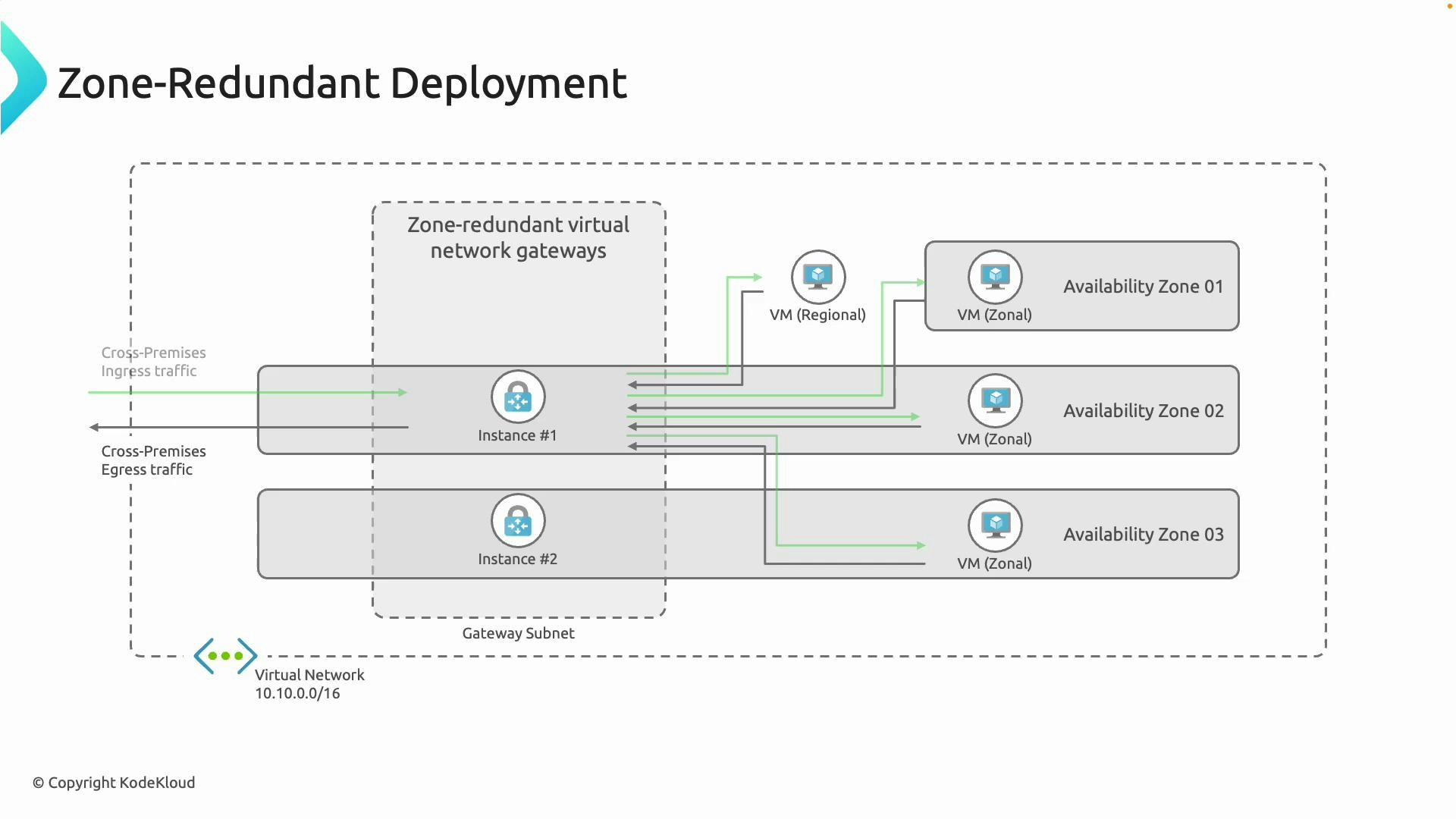
- Zone-redundant deployment places gateway instances in multiple Availability Zones within a single region.
- Protects against a zonal outage by allowing the remaining instance(s) to keep connections alive.
- Useful when minimizing downtime due to hardware or AZ failures is a priority.
Gateway availability modes
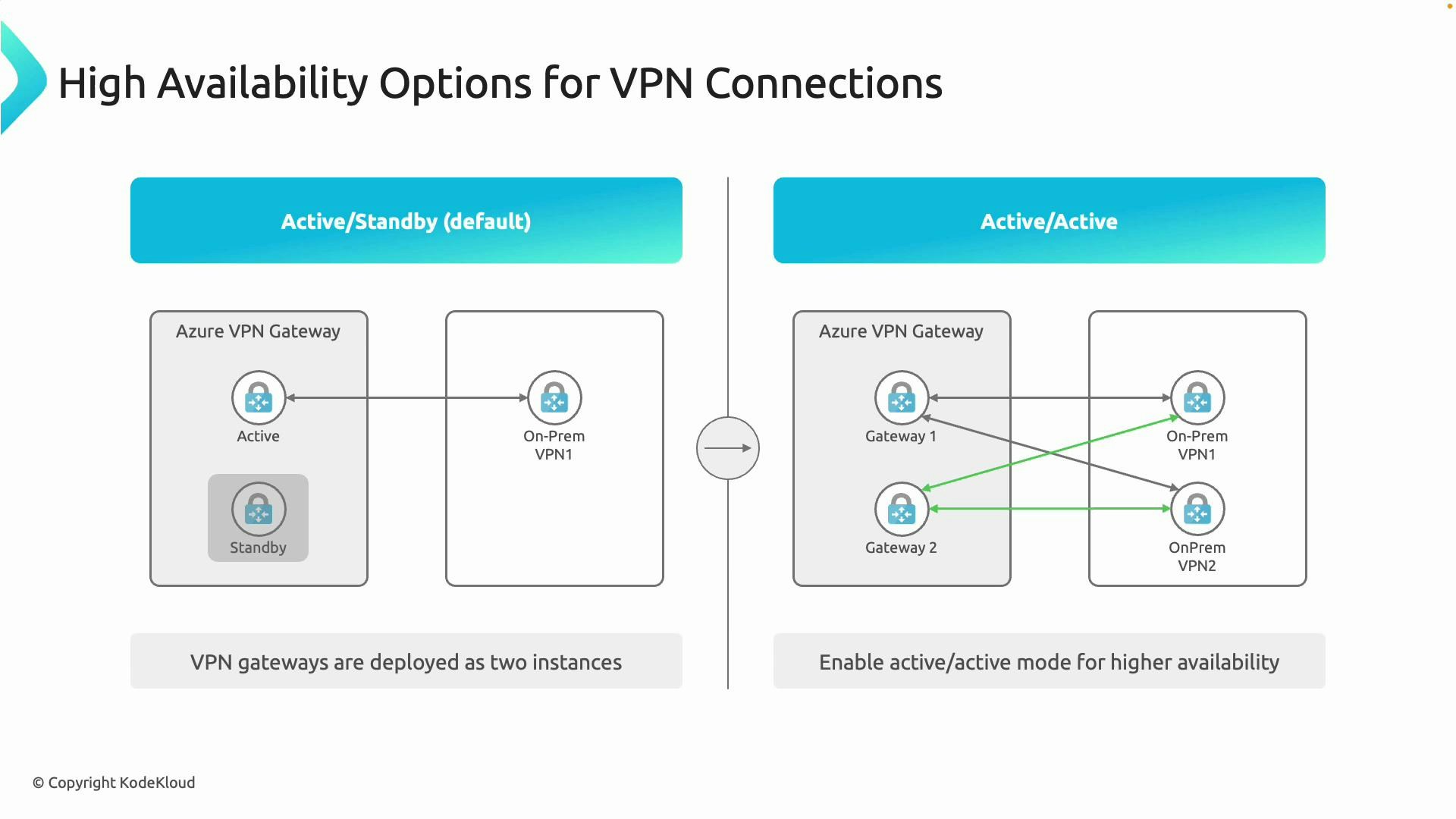
Azure VPN Gateways operate in one of two availability modes: active-standby (the default) and active-active. Each mode offers different resiliency and throughput characteristics.Active-standby (default)
In the default active-standby configuration:- Two gateway instances are present: one active and one standby.
- The active instance handles all traffic; the standby is synchronized and ready to take over.
- Failover to the standby instance is automatic and designed to minimize downtime.
- Disabling active-active does not remove the standby instance — it remains for failover.
- Typical choice when single-instance throughput is sufficient and you want automatic fast failover without extra on-prem configuration.
Active-active
Active-active configures both gateway instances to handle traffic concurrently:- Each instance typically has its own public IP address.
- Both gateways accept connections, increasing resiliency and aggregate throughput.
- On-premises devices should connect to both cloud public IPs. This commonly results in multiple IPsec tunnels (for example, two cloud gateways and two on-prem devices can produce up to four IPsec tunnels).
- Use routing (BGP or static) to manage path selection and failover between instances.
- Required when you need higher available throughput and want no single gateway instance to be a bottleneck.
- Recommended when you can mirror redundancy on the on-premises side.
Comparison at a glance
| Feature | Active-Standby | Active-Active | Zone-Redundant |
|---|---|---|---|
| Number of active instances | 1 active, 1 standby | 2 active (both handle traffic) | 2+ instances across AZs |
| Failover behavior | Automatic to standby | Load-sharing + failover via routing | Survives AZ failure |
| On-prem requirements | Single connection can work | Must configure connections to both public IPs | Recommended to have redundant on-prem devices |
| Throughput | Limited to one instance | Aggregate throughput of both instances | Depends on SKU and AZ placement |
| Typical use case | Simpler deployments, automatic failover | High throughput and resiliency | Protection against zonal outages |
Implementation checklist
- Choose the right gateway SKU for desired throughput and features (consult Azure docs for SKU details).
- For active-active:
- Provision two public IPs (one per gateway instance).
- Configure on-premises devices to establish tunnels to both public IPs.
- Use BGP or static routing to manage path selection and failover.
- For zone redundancy:
- Enable zone-redundant gateway option where supported.
- Confirm the gateway SKU supports zone redundancy.
- Test failover scenarios (cloud-side and on-prem-side) before production cutover.
- Monitor connection metrics and gateway health in Azure Monitor.
Active-active increases availability and aggregate throughput, but requires matching redundancy and correct routing on the on-premises side—configure connections to both cloud public IPs and use BGP or appropriate static routes to control failover.
Additional resources
- Azure VPN Gateway documentation: https://learn.microsoft.com/azure/vpn-gateway/
- VPN Gateway high-availability concepts: https://learn.microsoft.com/azure/vpn-gateway/vpn-gateway-high-availability
- Azure Availability Zones overview: https://learn.microsoft.com/azure/availability-zones/