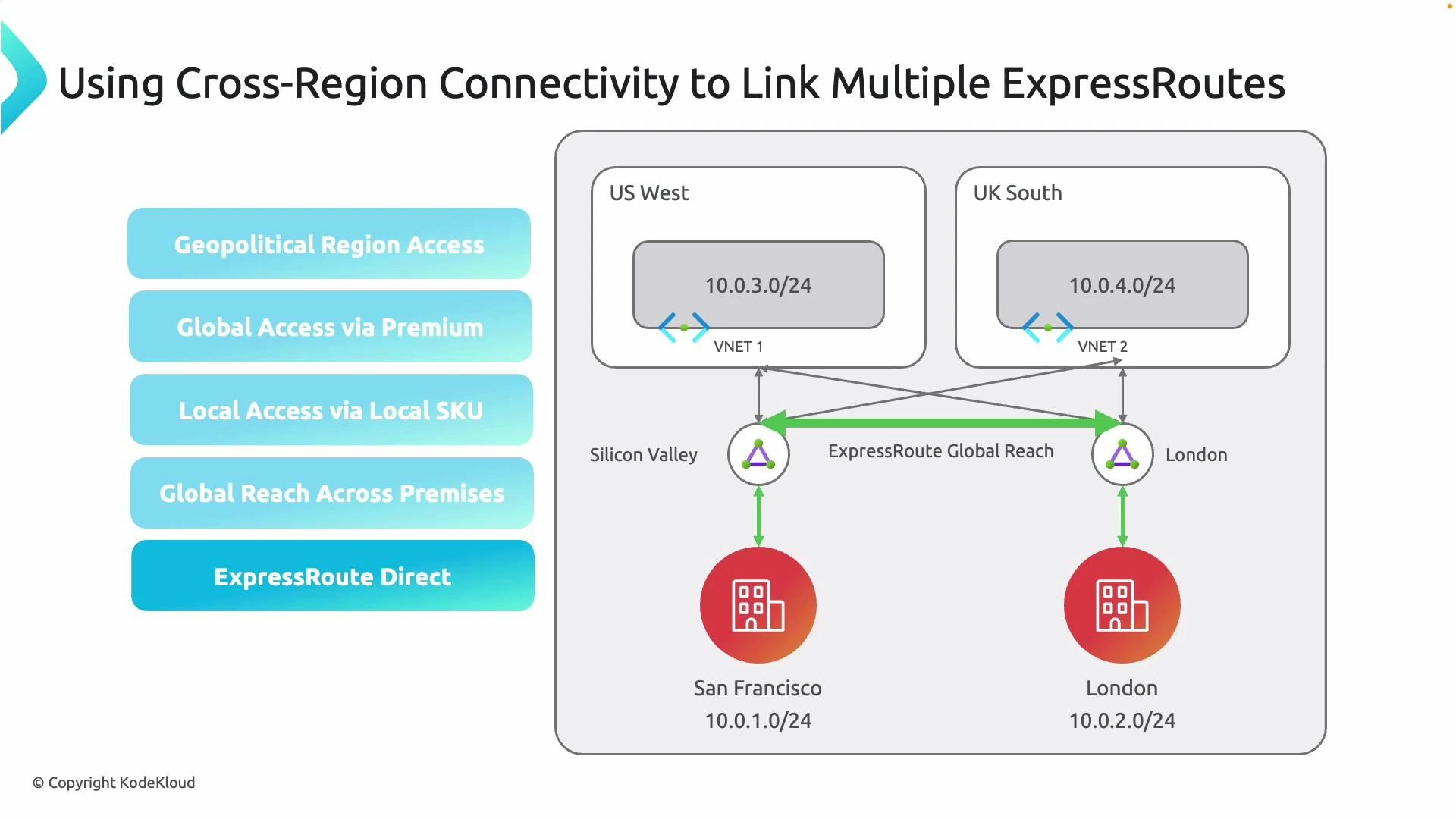
- Private, low-latency connectivity between on-premises sites across regions or countries.
- Centralized control of global traffic even when different local carriers are used at each site.
- Extended reach with Premium or add-on SKUs for multi-region and cross-continental connectivity. Local SKUs are limited to metro or same-region routing.
- Option to use ExpressRoute Direct for dedicated physical connections into Microsoft’s backbone when maximum control and availability are required.
How Global Reach works (real-world behavior)
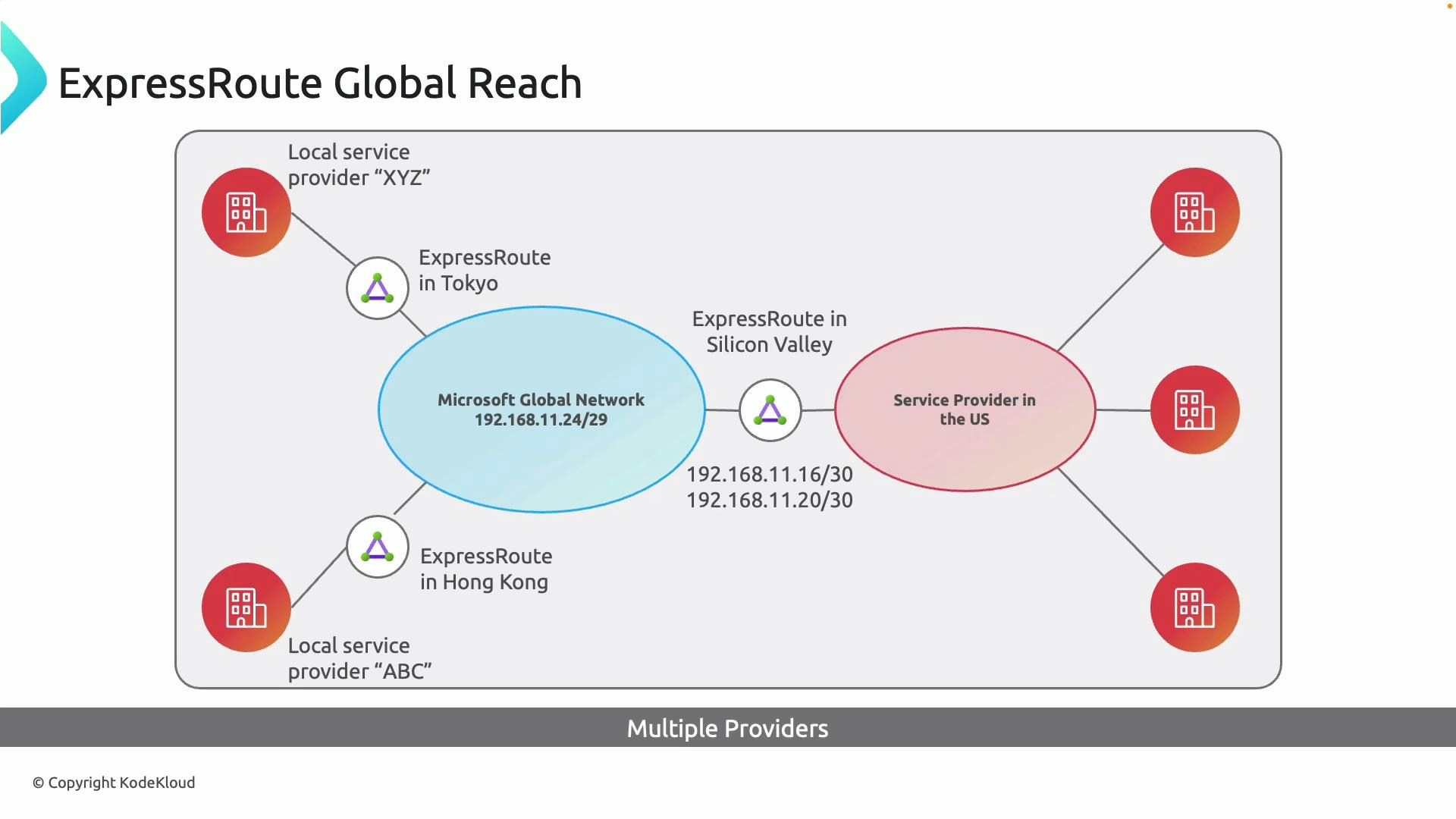
ExpressRoute Global Reach creates a private WAN overlay by linking the private peerings of two or more ExpressRoute circuits. Traffic from your on-premises networks is carried across Microsoft’s global network between those circuits rather than traversing the public internet. Example:- Circuits in Tokyo and Silicon Valley can be linked so the offices communicate privately across Microsoft’s backbone.
- Different local carriers may peer with Microsoft at each location; Global Reach keeps the inter-site traffic private and centrally managed.
Important considerations
Global Reach is not available in every region. Confirm regional availability and SKU requirements (Local vs. Standard vs. Premium) in Microsoft’s documentation before designing your deployment: https://learn.microsoft.com/en-us/azure/expressroute/expressroute-global-reach
- SKU and licensing: Premium/add-on SKUs enable cross-continent and multi-region routing; Local SKUs restrict routing scope.
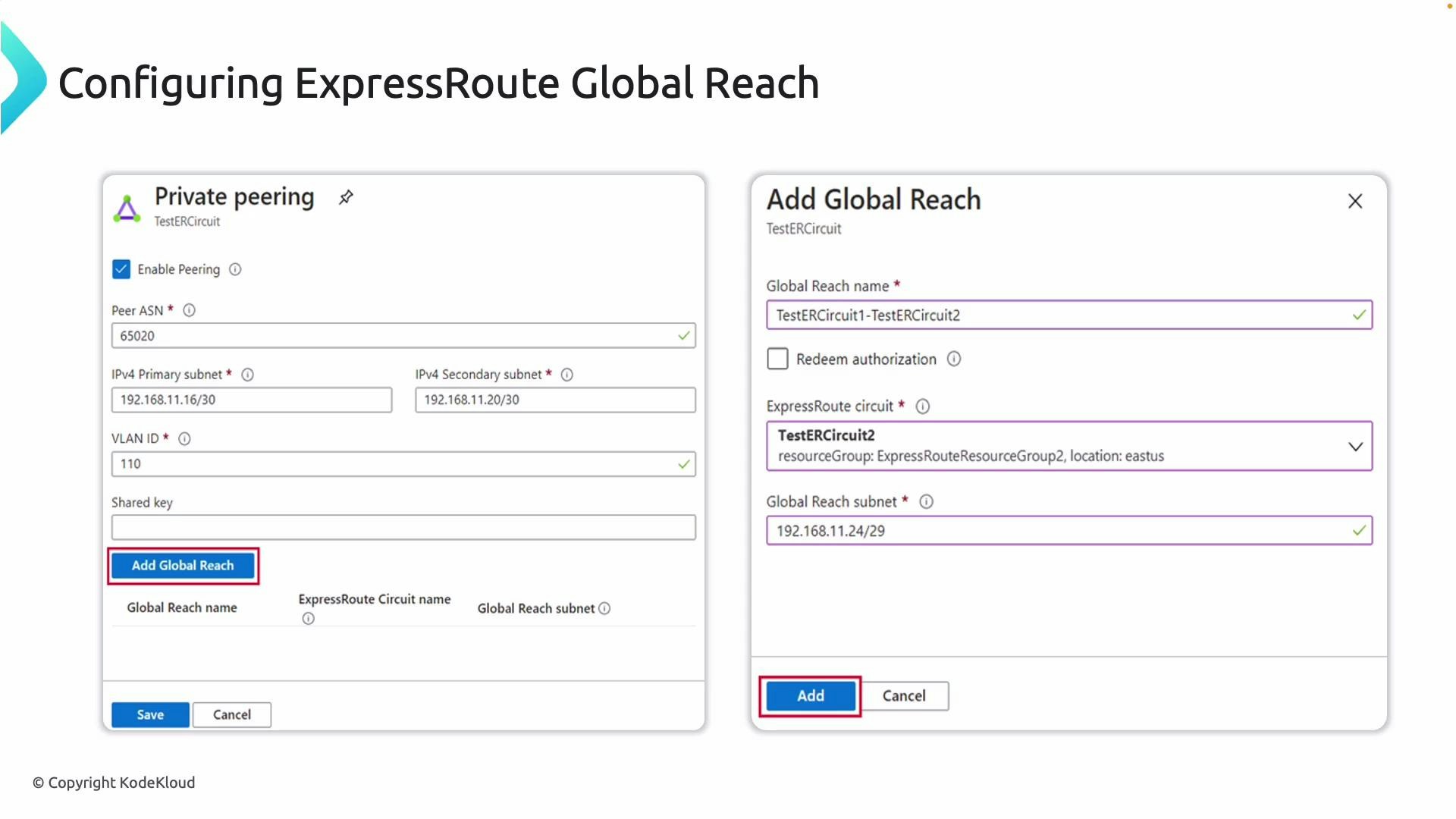
- Private peering configuration: ASN, VLAN IDs, and IPv4 primary/secondary subnets must be configured correctly on each circuit.
- IP addressing for the Global Reach interconnect: choose a dedicated subnet for the Global Reach peer to avoid overlap with existing networks.
- Security and isolation: you can optionally configure a shared key for the Global Reach pairing for additional validation.
ExpressRoute SKU comparison
| SKU | Typical Use Case | Routing Scope |
|---|---|---|
| Local | Single metro or regional connectivity | Limited to same metro/region |
| Standard | Regional connectivity with more features | Multiple regions within same geography |
| Premium / Add-on | Global multi-region and cross-continent connectivity | Broad global routing across Microsoft backbone |
Configuring ExpressRoute Global Reach (high level)
- Verify private peering on each ExpressRoute circuit:
- Confirm peer ASN, VLAN ID, and primary/secondary IPv4 subnets.
- In the Azure portal, open the ExpressRoute circuit you want to enable Global Reach for.
- Navigate to Private Peering or the Global Reach configuration area.
- Click Add Global Reach. In the dialog:
- Enter a Global Reach name.
- Select the peer ExpressRoute circuit to link (the circuit in the other office/region).
- Specify the Global Reach subnet for the interconnect.
- Optionally enter a shared key for additional security.
- Repeat Add Global Reach for each pairing you require.
- Save and validate connectivity. After configuration, on-premises networks connected to the paired circuits will route across Microsoft’s backbone.
Best practices:
- Use a non-overlapping, small subnet (for example, /30 or /29) for the Global Reach interconnect to simplify routing.
- Validate end-to-end routing with BGP route tables after enabling Global Reach.
- Document carrier and circuit details for each location to aid troubleshooting.
Validation and troubleshooting checklist
- Confirm BGP sessions for private peering are established on all circuits.
- Check route tables and BGP advertisements to ensure on-premises prefixes are visible across the linked circuits.
- Verify ACLs and firewall rules allow the expected traffic between sites.
- If traffic does not flow, check SKU limitations, regional availability, and whether Global Reach pairing has been accepted on both circuits.
Summary
ExpressRoute Global Reach turns separate ExpressRoute circuits into a secure, private global network overlay on Microsoft’s backbone, enabling predictable, lower-latency inter-site connectivity without traversing the public internet. Plan for SKU limits and regional availability, configure private peering carefully, and validate BGP routes after pairing circuits. Other ExpressRoute features include ExpressRoute Direct, ExpressRoute FastPath, and link redundancy options. For more details, see:- https://learn.microsoft.com/en-us/azure/expressroute/expressroute-global-reach
- https://learn.microsoft.com/en-us/azure/expressroute/expressroute-about-expressroute-direct