Attack categories — quick summary
| Attack Category | What it targets | Common examples | Typical mitigations |
|---|---|---|---|
| Volumetric | Network bandwidth | UDP floods, DNS/NTP amplification, spoofed-packet floods | Upstream scrubbing (ISP/cloud), rate limiting, Anycast/edge absorb |
| Protocol (state-exhaustion) | Network/transport protocol state (OSI Layers 3–4) | SYN floods, TCP connection exhaustion, reflection attacks | Protocol hardening, SYN cookies, state tracking limits, scrubbing |
| Application (Layer 7) | Application resources and logic | HTTP floods, Slowloris, abusive API requests, application exploits | WAF, behavioral analysis, rate limiting, auth & input validation |
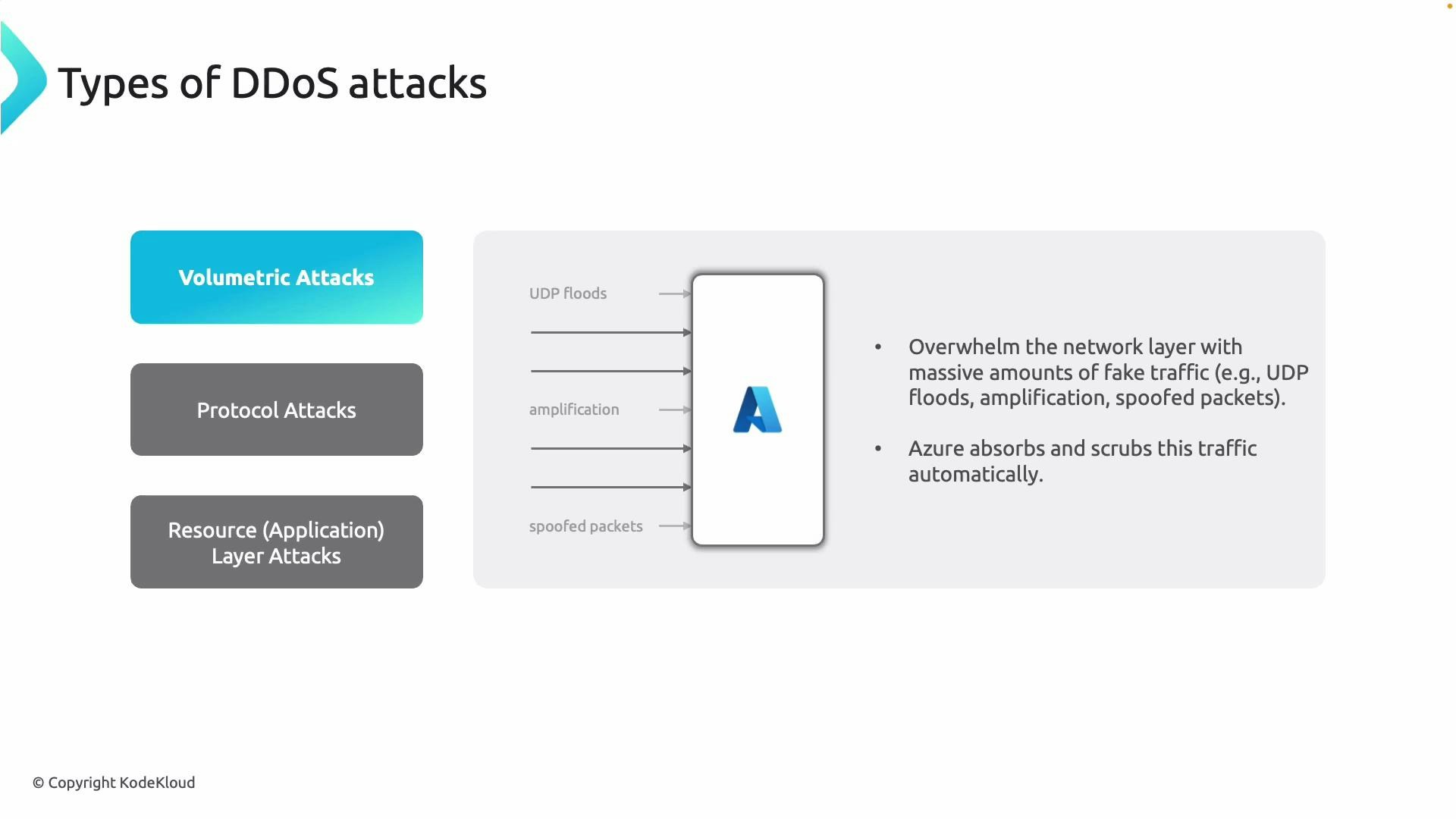
Volumetric attacks
Volumetric attacks aim to saturate the target’s network link or upstream bandwidth by generating massive volumes of traffic. These attacks often use amplification (e.g., DNS/NTP amplification), UDP floods, or spoofed-source packets that consume transit capacity. Key defenses:- Absorb/scrub malicious traffic at the provider/ISP edge (cloud providers like Azure offer DDoS mitigation services).
- Use Anycast or distributed edge networks to spread traffic.
- Apply rate limits and edge filtering to reduce unwanted flows before they reach origins.
Protocol (state-exhaustion) attacks
Protocol attacks exploit weaknesses in network and transport protocols to exhaust connection state or CPU on devices (routers, firewalls, load balancers, servers). Unlike volumetric attacks, protocol attacks may not need extremely large bandwidth to cause disruption. Examples include SYN floods (partial handshakes) and reflection-based attacks that force devices to track many bogus connections.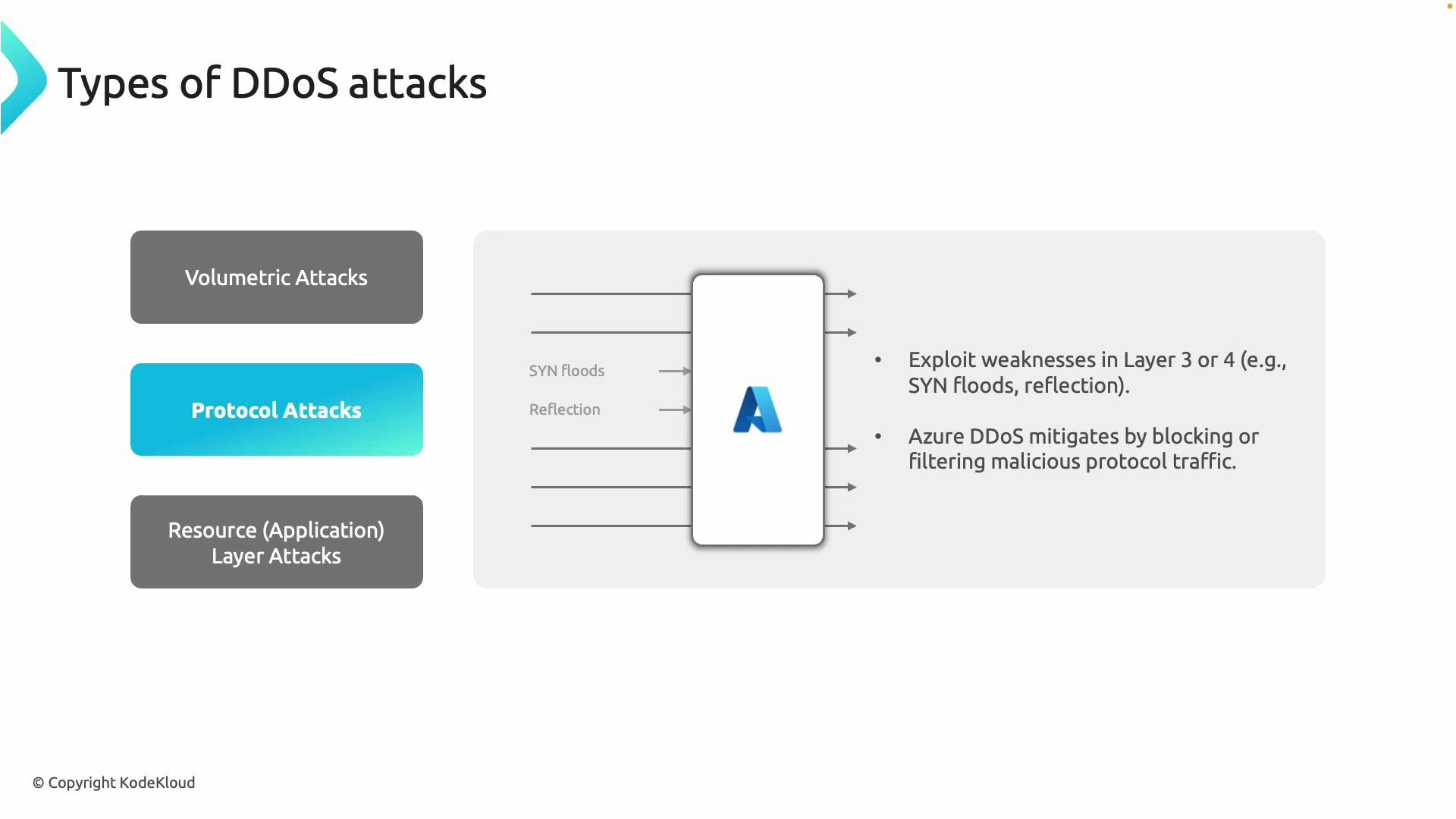
- Use SYN cookies and tune TCP stack parameters to limit half-open connections.
- Configure connection-tracking limits on network devices and enable aggressive timeouts for suspicious flows.
- Route traffic through a provider that performs protocol filtering and connection validation.
Application-layer (Layer 7) attacks
Application-layer attacks are the most targeted and often the hardest to detect because they mimic legitimate user behavior. Attackers may flood specific endpoints (HTTP POST/GET floods), use slow-rate attacks (Slowloris), or exploit application vulnerabilities to exhaust backend resources. Common protections:- Deploy an Application Gateway or Azure Front Door with a Web Application Firewall (WAF) to inspect, block, and rate-limit suspicious requests.
- Implement behavioral detection, bot management, and custom rules that identify anomalous request patterns.
- Harden application logic: input validation, authentication/authorization, caching, and scalable backend pools.

High-level mitigations and best practices
- Layered defense: combine upstream scrubbing (cloud provider or ISP) with network/protocol hardening and application-layer protections (WAF).
- Use managed DDoS protection (e.g., Azure DDoS Protection) for volumetric and protocol-level mitigation.
- Place an Application Gateway or Front Door with WAF in front of web apps to inspect Layer 7 traffic and apply behavioral rules.
- Implement rate limiting, CAPTCHA/challenge flows, IP reputation scoring, and strong authentication to reduce abuse.
- Scale backends and design for graceful degradation (circuit breakers, autoscaling, caching) to preserve service for legitimate users.
- Centralize logging and monitoring (network telemetry, WAF logs, application metrics) to detect anomalous patterns quickly and enable automated responses.
A robust DDoS strategy pairs upstream traffic scrubbing with application-aware defenses. Volumetric attacks are usually absorbed at the provider edge, while application-layer attacks require a WAF, behavior rules, and resilient backend design.
Detection and incident response tips
- Establish traffic baselines and alert on deviations (sudden spikes in requests, abnormal error rates, or long-tail TCP flows).
- Pre-authorize emergency rules with your cloud provider or DDoS response team to speed mitigation.
- Keep packet captures and logs for forensic analysis; many mitigations require historical context to tune rules without blocking legitimate traffic.
- Test resilience with tabletop exercises or controlled load tests that simulate attack conditions.
Further reading and references
- Azure DDoS Protection documentation
- OWASP — Denial of Service Prevention Cheat Sheet
- SANS — DDoS Attack and Mitigation Whitepaper