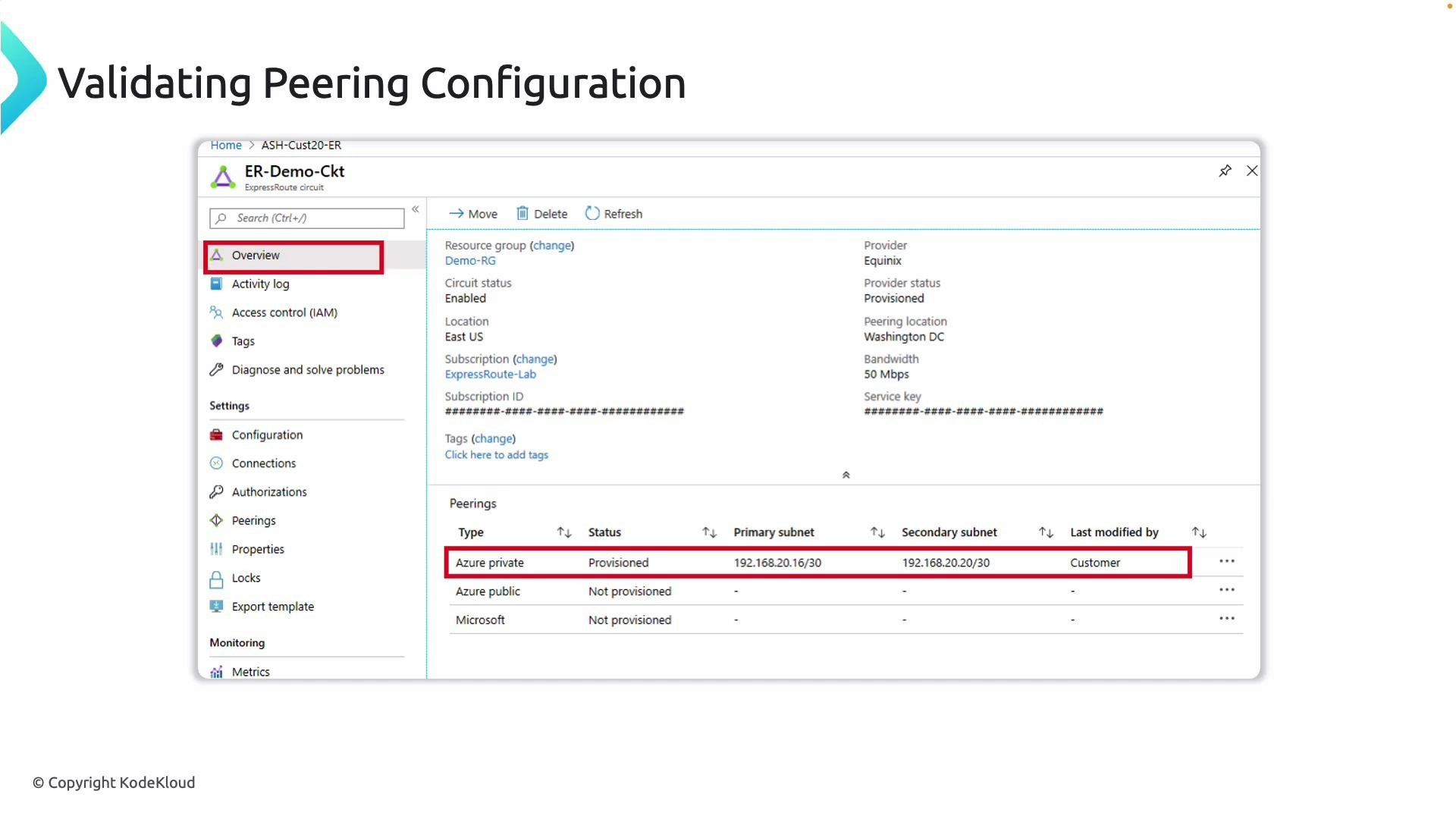
- Open the ExpressRoute circuit > Peerings blade in the Azure portal.
- Confirm each expected peering (Private, Microsoft, Public) appears in the list.
- Verify the status is “Provisioned” for each peering.
- Confirm the primary and secondary peer IP subnets shown match the values provided by your connectivity provider.
- If Provisioned but traffic isn’t working, proceed to validate BGP adjacency, route exchanges, and local/remote route tables.
- Confirm the circuit has been provisioned by your service provider and that they report no outstanding actions.
- Verify the peering configuration (VLAN ID, peer IP addresses, subnet masks) exactly matches the provider’s configuration.
- Confirm the correct peering types are enabled (Private, Microsoft, Public) and that ASN/BGP settings match both sides.
- Review the ExpressRoute circuit’s activity log, events, and notifications for provisioning or connectivity errors.
- If you recently changed settings, allow propagation time and re-check after the provider confirms provisioning.
| Symptom | Probable cause | Recommended remediation |
|---|---|---|
| Peering missing from Peerings blade | Provider has not finished provisioning | Contact provider; confirm VLAN and peering provisioning |
| Peering present but no subnets | Incomplete configuration or mismatched IP scheme | Verify expected peer IP subnets with provider and update settings |
| Status not “Provisioned” | VLAN mismatch or provisioning failure | Compare VLAN ID and peering type with provider; check circuit events |
| Provisioned but no traffic | BGP adjacency not established or routes not advertised | Validate BGP sessions and routes on both sides |
- List peerings (Azure CLI)
CLI
- Show a specific peering (Azure CLI)
- Check BGP session status and routes on your on-premises router (vendor-specific CLI).
- Use Network Watcher and diagnostic logs to inspect route propagation and reachability in Azure.
- Review ExpressRoute documentation for peering and BGP troubleshooting:
If a peering shows as Provisioned but traffic is not flowing, validate BGP adjacency and route tables next — “Provisioned” means Azure’s side is configured, not that BGP peering or routing is established. Verify BGP state, advertised prefixes, and route filters on both the Azure and provider sides.