- Create a user-defined route (UDR) that overrides Azure system routes for selected subnets.
- Add a default route (0.0.0.0/0) in the UDR with next hop type VirtualNetworkGateway so traffic is sent to the VPN Gateway.
- Associate that route table with the subnet(s) you want to force through the VPN (for example, backend and mid-tier).
- Keep other subnets (e.g., frontend) without the UDR association so they use Azure system routes and can access the internet directly.
- Ensure the VPN Gateway is route-based and that the site-to-site VPN and on-premises devices are prepared for the returned and outbound flows.
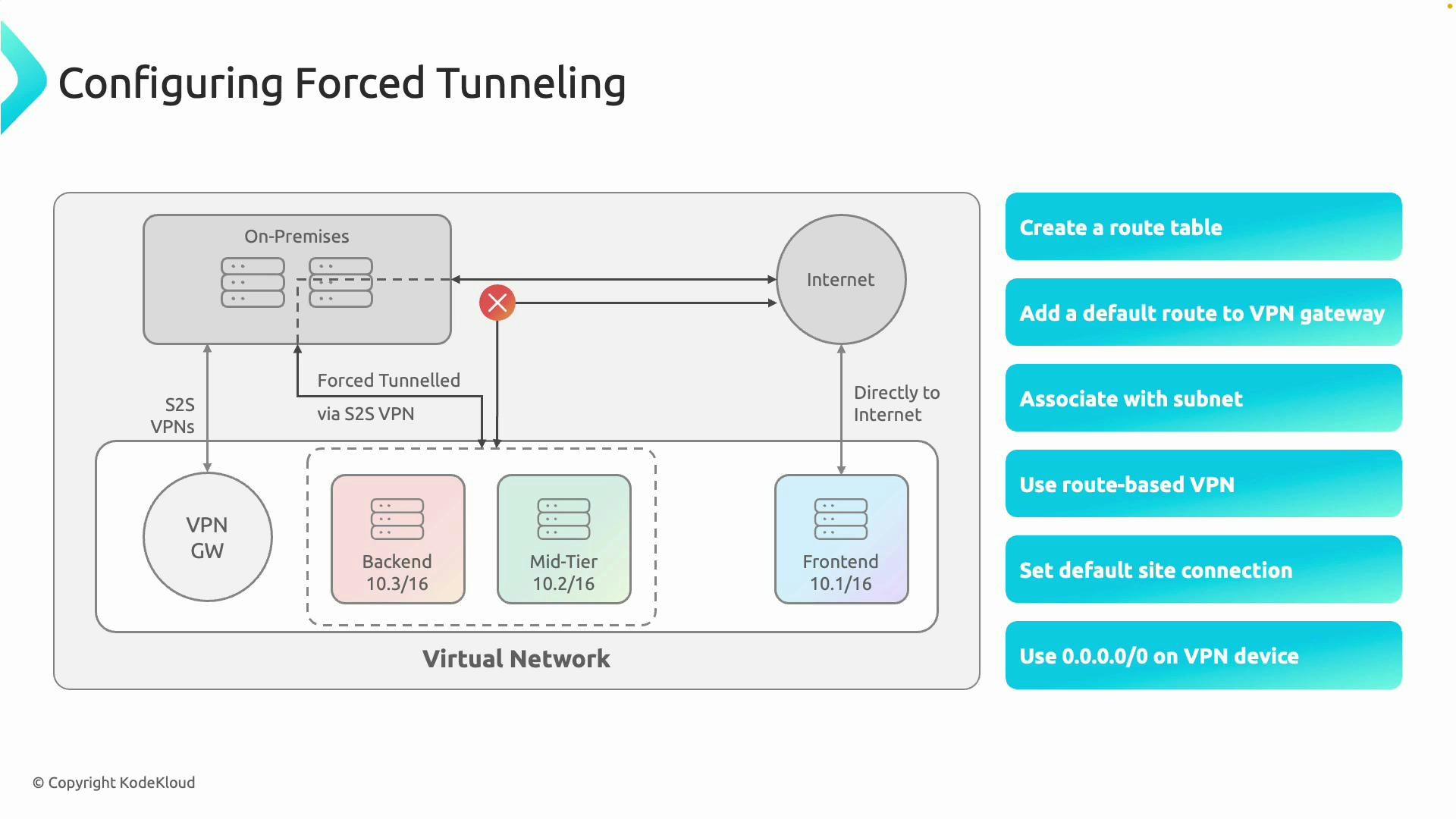
- Azure system routes include a default route to the internet. To intercept internet-bound traffic, you must create a user-defined route (UDR). See: User-defined routes (UDR) overview.
- Add a 0.0.0.0/0 route in the UDR with —next-hop-type VirtualNetworkGateway. This causes internet-bound traffic from the subnet to be forwarded to the VPN Gateway rather than directly to the internet.
- Associate the UDR with the subnet(s) that should use the forced tunnel (for example, backend and mid-tier). Any subnet without the association will continue to use Azure system routes (for example, frontend).
- Use a route-based VPN Gateway for forced tunneling; policy-based VPN gateways do not support this scenario. See: Azure VPN Gateway types and limitations.
- Ensure the site-to-site VPN connection is active and that your on-premises firewall/router is configured to accept the tunneled internet-bound flows — including NAT (SNAT), inspection, and forwarding to the internet.
- If you use BGP, verify route propagation so on-premises devices know how to route return traffic back to Azure. See: BGP with Azure VPN Gateway.
- Create a route table:
- Add a 0.0.0.0/0 route pointing to the virtual network gateway:
- Associate the route table with a subnet:
- Create a route-based VPN Gateway (example):
| Check | Why it matters | Action example |
|---|---|---|
| UDR association | Ensures chosen subnet traffic is routed to VPN Gateway | Verify route table is associated to target subnet(s) and contains 0.0.0.0/0 → VirtualNetworkGateway |
| VPN connection state | VPN must be up to carry traffic | Confirm site-to-site connection status in Azure portal or az network vpn-connection show |
| On-prem routing | Return traffic must be routed back to Azure | Ensure on-prem device has routes to Azure subnets (via BGP or static routes) |
| NAT/SNAT and inspection | On-premises device must be able to NAT/inspect traffic | Verify firewall/proxy is configured to SNAT and permit outbound connections |
| NSG rules | NSGs can block forwarded traffic | Review Network Security Groups applied to subnets and NICs for blocking rules |
| Service exceptions | Some services require direct outbound access | Validate Microsoft/third-party service requirements and create exceptions if needed |
- From a VM in the forced-tunnel subnet, test outbound connectivity to a public IP and capture packet traces to confirm the path goes to the VPN Gateway.
- Check the effective routes on the VM’s NIC/subnet in the Azure portal to confirm the UDR takes precedence over system routes.
- Confirm the on-premises firewall logs to validate traffic is received, inspected, and forwarded.
- Monitor latency and throughput once forced tunneling is enabled — added hops can affect performance.
- If using BGP, inspect route advertisements and learned routes on both sides to ensure correct return paths.
User-defined routes (UDRs) take precedence over Azure system routes. Adding a 0.0.0.0/0 UDR with next hop VirtualNetworkGateway ensures that a subnet’s internet-bound traffic is forwarded to the VPN Gateway instead of going directly to the internet.
Forced tunneling can add latency and incur bandwidth costs. It may also prevent direct access to some Azure or third-party services that expect direct outbound connectivity. Identify required service endpoints and plan exceptions or proxy rules before rolling out forced tunneling broadly.
| Resource | Purpose |
|---|---|
| Azure VPN Gateway overview | VPN types, SKUs, and capabilities |
| User-defined routes (UDR) overview | Controls routing for subnets |
| BGP with Azure VPN Gateway | Route propagation and BGP setup |
| Azure CLI documentation | General Azure CLI usage and reference |
| Network Security Groups (NSGs) overview | Filtering rules that may affect forwarded traffic |