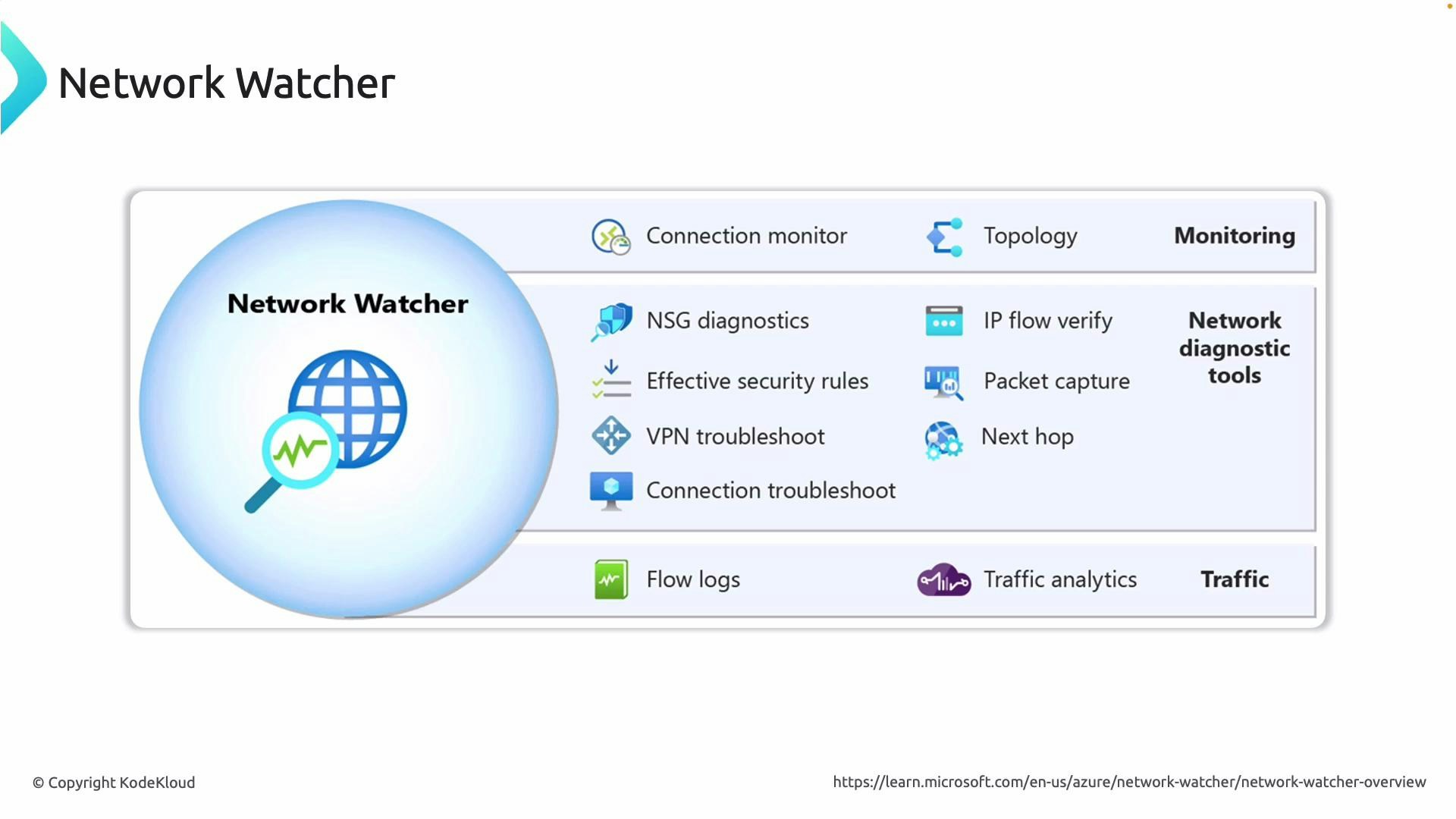
| Tool | Purpose | Typical use-case |
|---|---|---|
| IP Flow Verify | Verifies whether a packet flow to/from a VM is allowed or denied by evaluating effective NSG and UDR rules | Confirm whether NSG or route configuration is blocking traffic to/from a VM |
| Next hop | Determines the forwarding decision for outbound traffic from a VM based on route tables and UDRs | Validate which next hop (virtual appliance, Internet, peering, etc.) Azure will select |
| VPN Troubleshoot | Provides diagnostics and metrics for VPN gateway connections and tunnels | Troubleshoot IPsec/IKE negotiation, tunnel status, and packet drops |
| Flow Logs + Traffic Analytics | Collects NSG flow records to storage or Log Analytics for analysis | Detect anomalous traffic, analyze north-south and east-west flows, and support security investigations |
| Connection Troubleshoot (Connection Monitor) | Simulates end-to-end paths and reports reachability, latency, and loss | Detect path breaks, intermittent failures, or latency spikes between endpoints |
| Topology | Visualizes VNets, subnets, gateways, NICs, peerings, and relationships | Map architecture, find misconfigurations, and understand resource relationships |
- Visualize: Start with Topology to confirm the logical layout and identify unexpected connections or missing resources.
- Verify reachability: Use Connection Troubleshoot to test end-to-end paths and surface latency or loss.
- Inspect path decisions: Run Next hop to confirm which route/next-hop Azure will use for outbound traffic.
- Check access rules: Use IP Flow Verify to see whether NSGs or UDRs are allowing or denying traffic and which rule is responsible.
- Inspect gateways: For VPN issues, use VPN Troubleshoot to get tunnel health and negotiation diagnostics.
- Collect long-term telemetry: Enable Flow Logs (and Traffic Analytics) to capture historical traffic patterns for security and capacity planning.
-
IP Flow Verify
Use IP Flow Verify to test whether a specific 5-tuple flow (source IP, destination IP, source port, destination port, and protocol) to or from a VM is allowed or denied. The tool evaluates the effective NSG rules and route table associated with the VM’s NIC and pinpoints the rule that allowed or denied the traffic. This is the first place to check when a VM is reachable at the network level but application traffic is failing. -
Next hop
Next hop inspects the route table and Azure routing decisions for packets leaving a VM. It shows which next hop Azure will use (for example: virtual appliance, Internet, virtual network peering, or a specific IP gateway). Use this when you suspect packets are being forwarded to a wrong appliance, the Internet, or across a peering link due to UDRs or BGP routes. -
VPN Troubleshoot
Use VPN Troubleshoot to diagnose issues with VPN gateways, site-to-site tunnels, and ExpressRoute gateways. It provides tunnel status, IKE/IPsec negotiation details, packet drop metrics, and visibility into ephemeral errors that affect tunnel state. This tool is essential when tunnels are unstable or when remote sites cannot route traffic correctly. -
Flow Logs (NSG Flow Logs) and Traffic Analytics
Flow Logs capture NSG-permitted and NSG-denied flows and write records to a storage account or Log Analytics workspace. When combined with Traffic Analytics, you can group flows, identify top talkers, spot anomalous traffic, and produce reports for security operations and capacity planning. Retain flow logs to support forensic investigations and long-term trend analysis. -
Connection Troubleshoot (Connection Monitor)
Connection Troubleshoot runs active checks between two endpoints and reports on reachability, latency, and packet loss. It supports tests between VM-to-VM, VM-to-IP, and VM-to-FQDN and can be scheduled for continuous monitoring. Use it to detect routing or transient network issues that impact application responsiveness. -
Topology
Topology renders a visual map of your network resources and their relationships — VNets, subnets, gateways, NICs, and peerings. It’s useful for onboarding, architecture review, and quickly spotting misconfigured components (for example, an unexpected peering or missing gateway).
- Start with Topology and Connection Troubleshoot to narrow down whether an issue is structural (topology/routing) or operational (latency, packet loss).
- Use IP Flow Verify and Next hop together: Next hop confirms where traffic is forwarded; IP Flow Verify confirms whether NSGs/UDRs permit the flow.
- Enable Flow Logs and Traffic Analytics in production to build baselines and detect anomalies early. Retain logs in a secure storage account or Log Analytics workspace with defined retention policies.
- For VPN connectivity issues, collect both VPN Troubleshoot output and packet captures (if needed) to correlate tunnel health with packet flows.
Enable Network Watcher in every Azure region where you operate — Network Watcher is regional. Also ensure you have appropriate RBAC permissions (for example, Network Contributor or Owner) at the subscription or resource-group level to create/watch Network Watcher resources and run diagnostics.
- Enable Network Watcher per region (Portal, CLI, or ARM).
- Grant required RBAC roles (Network Contributor, Reader where appropriate).
- Configure a Log Analytics workspace or storage account for Flow Logs.
- Run topology, connection tests, IP flow verification, and next hop analysis as part of incident response.
- Retain flow logs and enable Traffic Analytics for security posture and capacity management.
- Azure Network Watcher overview: https://learn.microsoft.com/azure/network-watcher/
- NSG flow logs and Traffic Analytics: https://learn.microsoft.com/azure/network-watcher/flow-logging-overview
- Connection Monitor (Connection Troubleshoot): https://learn.microsoft.com/azure/network-watcher/network-watcher-monitoring-overview#connection-monitor
- Topology tool documentation: https://learn.microsoft.com/azure/network-watcher/network-watcher-topology-overview
- VPN diagnostics and troubleshooting: https://learn.microsoft.com/azure/vpn-gateway/vpn-gateway-troubleshoot