| Capability | Hub Virtual Network (Hub VNet) | Secured Virtual Hub (Virtual WAN) |
|---|---|---|
| Terminology | Standard Azure VNet acting as the hub | Secured hub built on Azure Virtual WAN |
| Connectivity model | Manual VNet peering (hub-and-spoke) | Automated hub-and-spoke via Virtual WAN |
| Scale | ~10 Gbps VPN throughput; ~30 S2S tunnels (typical) | Up to ~20 Gbps; thousands of tunnels; SD‑WAN integrations |
| Automation | Manual peering, routing, partner setup | Centralized management and partner integrations via VWAN |
| IP provisioning | Customer-managed firewall IPs | VWAN auto-generates hub IPs |
| Routing | UDRs and manual route management | BGP-based centralized route management in VWAN |
| Forced tunneling | Manual forced tunnel configurations | Combine Azure Firewall + partner services via VWAN |
| Third-party partners | Manual integration | Automated/managed partner integrations |
| WAF / NVAs | Supported; often hub or spoke | Supported; typically deployed in spokes |
| DDoS Protection | Directly integrable with DDoS Protection plans | Integration model differs; check Azure docs |
- Hub VNet: A standard Azure Virtual Network you create and manage to act as a central inspection and routing point.
- Secured Virtual Hub: A hub implemented with Azure Virtual WAN (VWAN) that offers higher automation, global connectivity, and partner integrations.
- Hub VNets use manual VNet peering for hub-and-spoke topologies. This gives control but increases operational overhead as the environment grows.
- Secured Hubs automate hub-and-spoke connectivity using Azure Virtual WAN. They scale higher and are designed for enterprise-grade, global connectivity with automated branch and SD‑WAN integrations.
- Hub VNets require explicit configuration for peering, routing (UDRs), and third-party integrations.
- Secured Hubs automate many connectivity tasks and include built-in partner integrations (for example, SD‑WAN providers and third‑party security services available through Virtual WAN).
- Hub VNets: you assign and manage firewall IP addresses.
- Secured Hubs: Virtual WAN can auto-provision hub IP addresses, reducing manual network configuration.
- Both models support availability zones and resiliency patterns.
- Third-party partner integrations (e.g., Zscaler, Check Point) require manual setup in Hub VNets, while VWAN secured hubs often provide automated integration workflows.
- Hub VNets rely on User-Defined Routes (UDRs) and route propagation you maintain.
- Secured Hubs centralize routing with BGP-based management inside the VWAN fabric, simplifying routing at scale.
- For forced tunneling to third-party services, Hub VNets need manual UDR and routing configuration; VWAN secured hubs can combine Azure Firewall for private traffic with an integrated partner for internet filtering.
- Both architectures support WAF (Application Gateway) and Network Virtual Appliances (NVAs). With VWAN secured hubs, these are typically placed in spokes to keep the hub focused on transit and centralized enforcement.
- Hub VNets: can be integrated directly with Azure DDoS Protection plans.
- Secured Hubs: the DDoS integration model differs — consult the latest Azure DDoS Protection documentation for current capabilities and limitations: https://learn.microsoft.com/en-us/azure/ddos-protection/ddos-protection-overview
DDoS integration models change over time. Always check Azure documentation before designing DDoS protection into VWAN-secured hubs or hub VNet topologies.
- Choose Hub VNet when you require fine-grained, customer-managed control over IP addressing, peering, and routing, and when your environment is small-to-medium scale.
- Choose Secured Virtual Hub (Virtual WAN) for global-scale environments needing automation, central BGP routing, integrated partner services, and high tunnel throughput for many branch sites.
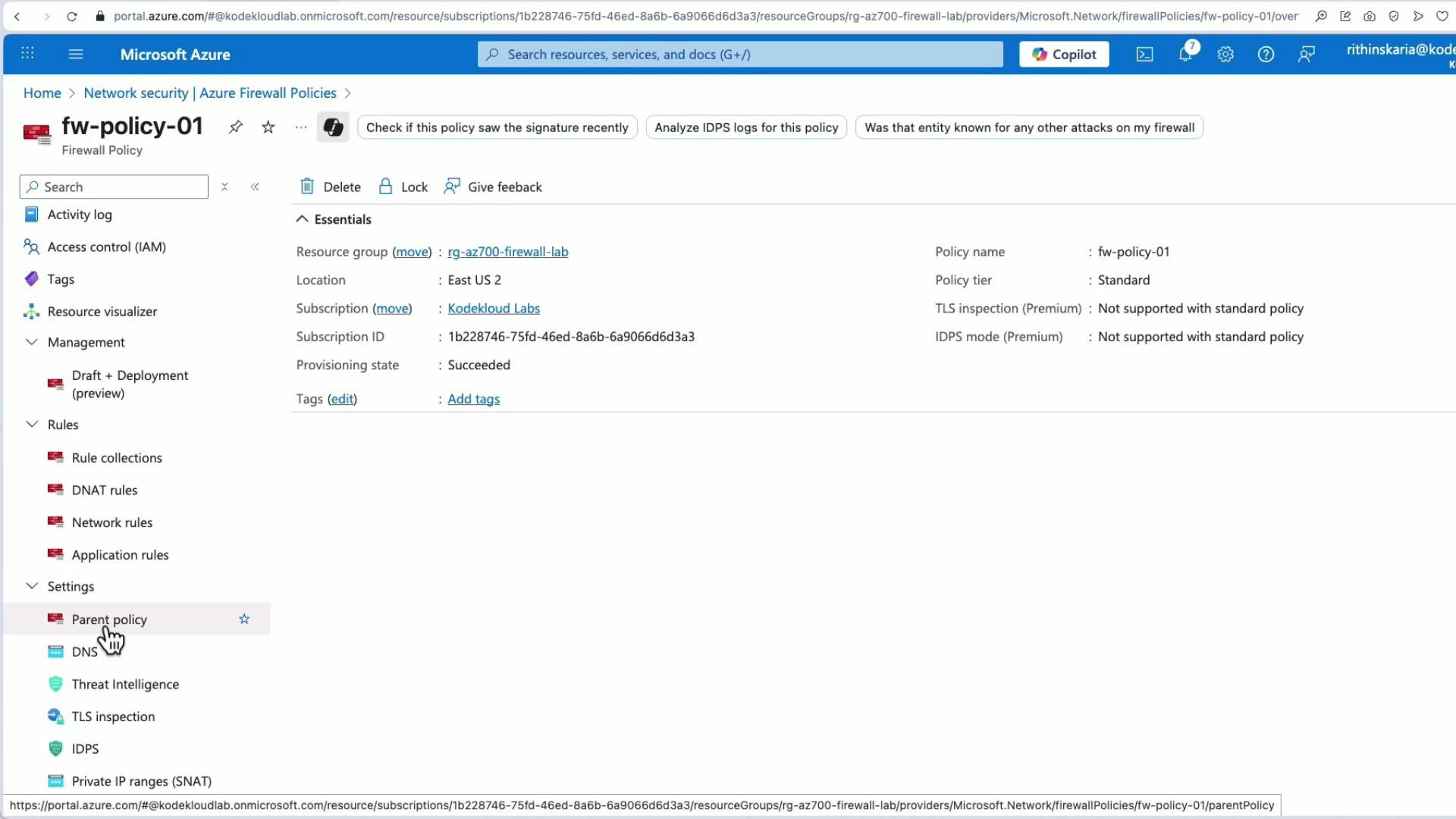
- Create an Azure Firewall Policy to define enforcement (DNAT, Network, Application rules, TLS inspection, Threat Intelligence settings).
- Design and implement the hub-and-spoke topology. Create the hub VNet and configure Manual VNet peering with spokes.
- Use Firewall Manager to centralize Azure Firewall policy management. If using third‑party NVAs, note these often require manual deployment and won’t be centrally managed by Firewall Manager the same way Azure Firewalls are.
- Configure UDRs on spoke subnets to force traffic to the hub firewall for inspection and egress routing.
- Design the topology using Azure Virtual WAN: create a secured virtual hub and define spokes through VWAN.
- Select security providers — use Azure Firewall and optionally configure supported partner services available through VWAN.
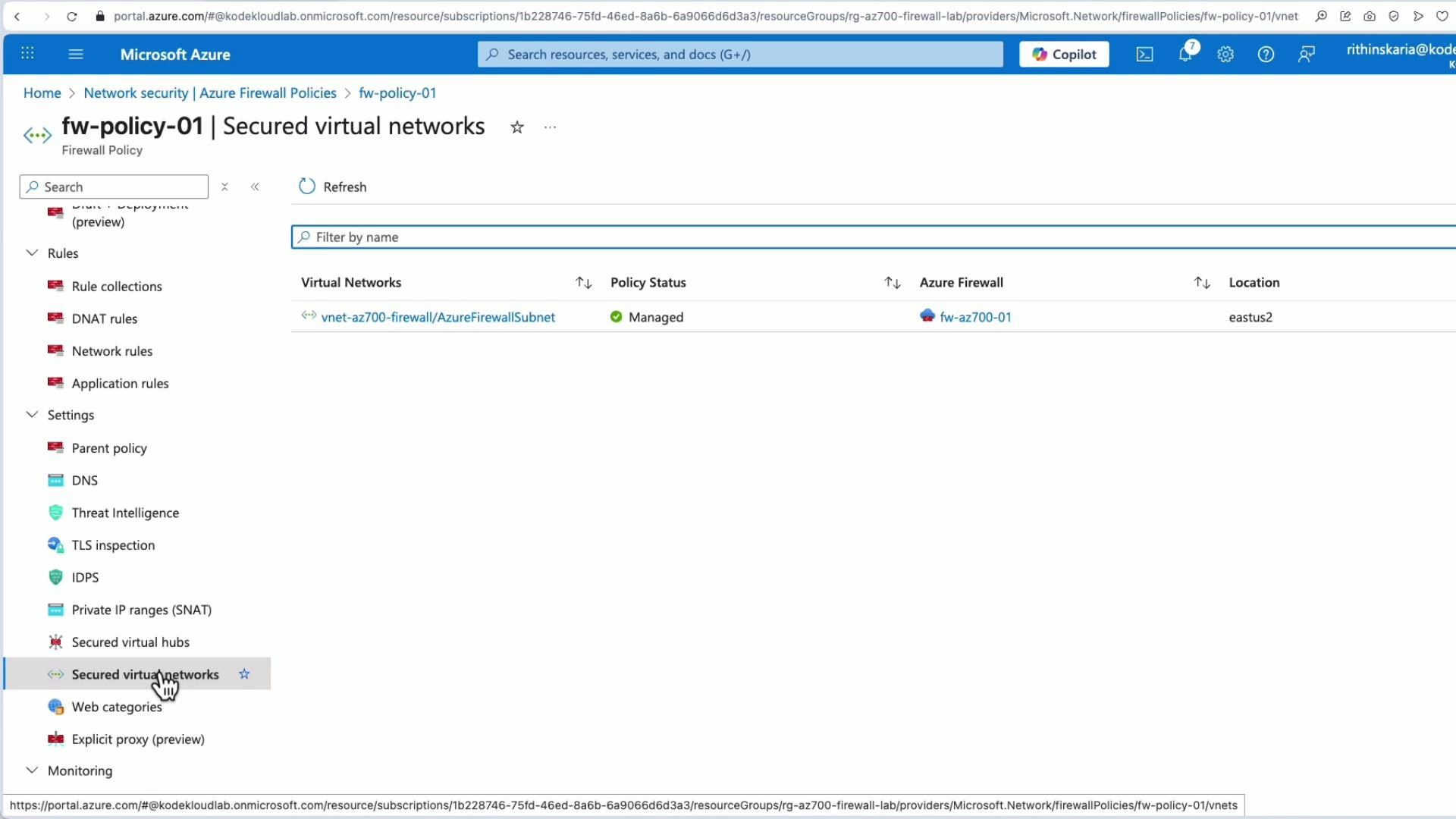
- Attach Firewall Policies directly to the secured hub to centralize rule enforcement across hub traffic.
- Rely on VWAN centralized/BGP route management to control traffic steering; this reduces the need for manual UDRs and manual route distribution.
Azure Firewall Manager is a management/control-plane service. Look for and manage the resources (Azure Firewalls, Firewall Policies, and hub configurations) rather than a separate Firewall Manager VM or appliance.
- Review and edit DNAT, Network, and Application rule collections.
- Configure settings such as Threat Intelligence, TLS Inspection, and parent/local policy relationships.
- Attach policies to virtual networks, secured hubs, or specific Azure Firewall instances.
- Azure Firewall Manager overview: https://learn.microsoft.com/en-us/azure/firewall-manager/overview
- Azure Firewall overview: https://learn.microsoft.com/en-us/azure/firewall/overview
- Azure Virtual WAN overview: https://learn.microsoft.com/en-us/azure/virtual-wan/virtual-wan-about
- Azure DDoS Protection overview: https://learn.microsoft.com/en-us/azure/ddos-protection/ddos-protection-overview