Where you can associate an NSG
- Subnet — applies rules to all resources within the subnet.
- Network interface (NIC) — applies rules to a single virtual machine or NIC.
How NSG rules are evaluated
Rules are evaluated in order of their numeric priority (lower number = higher precedence). Azure also enforces built-in system rules that provide default behavior; these cannot be deleted but can be effectively overridden by higher-precedence custom rules.| Resource association | Effect |
|---|---|
| Subnet | Controls traffic for all resources in that subnet (applies to traffic entering/exiting the subnet). |
| NIC | Controls traffic for the specific VM’s network interface (applies after subnet rules). |
Common rule properties
| Property | Description | Example |
|---|---|---|
| priority | Numeric order for evaluation. Lower numbers take precedence. | 100, 200 |
| name | Unique identifier for the rule within the NSG. | Allow-SSH-From-AdminNet |
| protocol | TCP, UDP, or * (Any). | TCP |
| port(s) | Single port or range. | 22, 3389, 80-443 |
| source | CIDR IP range, service tag, or Application Security Group (ASG). | 203.0.113.0/24, Internet, VirtualNetwork |
| destination | CIDR, service tag, or ASG. | 10.0.1.0/24, ApplicationGateway |
| action | Allow or Deny | Allow |
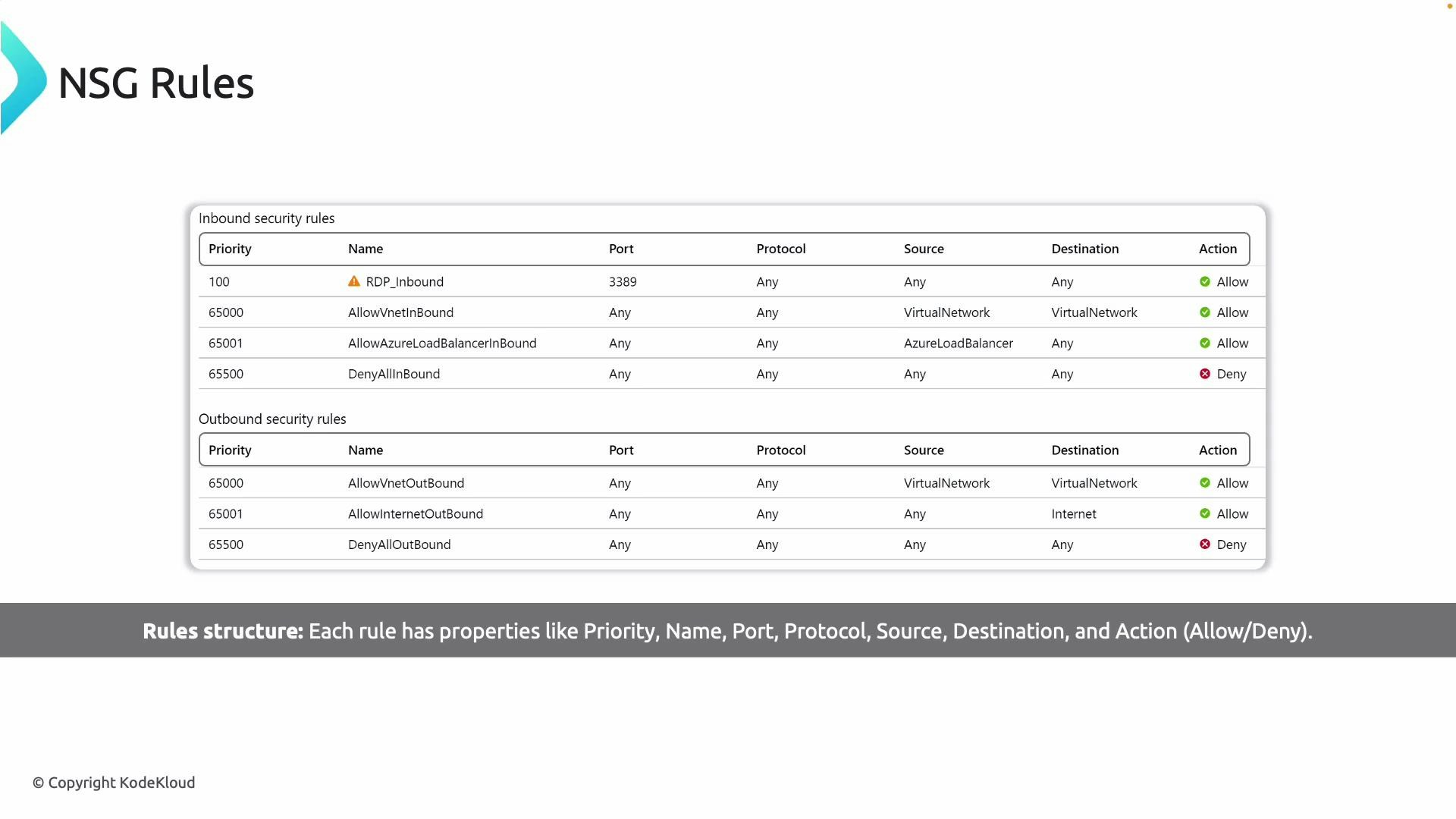
Default system rules
Azure NSGs include built-in rules that provide baseline connectivity. These default rules cannot be removed and have fixed priorities:- AllowVNet (service tag: VirtualNetwork) — permits traffic inside the VNet.
- AllowAzureLoadBalancer (service tag: AzureLoadBalancer) — permits load balancer health probes.
- AllowInternet / DenyAll (depending on direction) — controls internet access or denies remaining traffic.
Default NSG rules provide the baseline and cannot be deleted. To override a default, create a custom rule with a lower numeric priority (higher precedence). Prefer service tags and Application Security Groups for flexible, maintainable rules instead of hard-coded IP addresses.
Service tags and Application Security Groups (ASGs)
Use service tags (e.g., VirtualNetwork, Internet, AzureLoadBalancer) and ASGs to simplify rule management:- Service tags represent a group of IP address prefixes for Azure services and are maintained by Microsoft.
- ASGs group NICs or VMs by application role, allowing you to create rules that refer to the group instead of individual IPs.
Common use cases
- Open a management port from a known IP range (e.g., RDP TCP 3389 or SSH TCP 22).
- Restrict web tier access to only a load balancer or an application gateway.
- Allow only specific application-to-application traffic using ASGs for micro-segmentation.
Example: create an NSG and add a rule
Azure CLIBe careful when adding restrictive rules (especially for management ports). Misconfigured NSG rules can lock you out of virtual machines. Always test rules with a low-risk host or allow a temporary breakpoint rule for your own IP before applying globally.
Best practices
- Use least privilege: only open required ports and limit source ranges.
- Prefer service tags and ASGs over static IPs.
- Use clear, consistent naming conventions that include intent and scope (e.g., Allow-HTTP-From-ALB).
- Keep rule sets minimal and remove obsolete rules.
- Monitor and log traffic (Network Watcher, NSG flow logs) to validate rules and detect anomalies.