Request routing rules
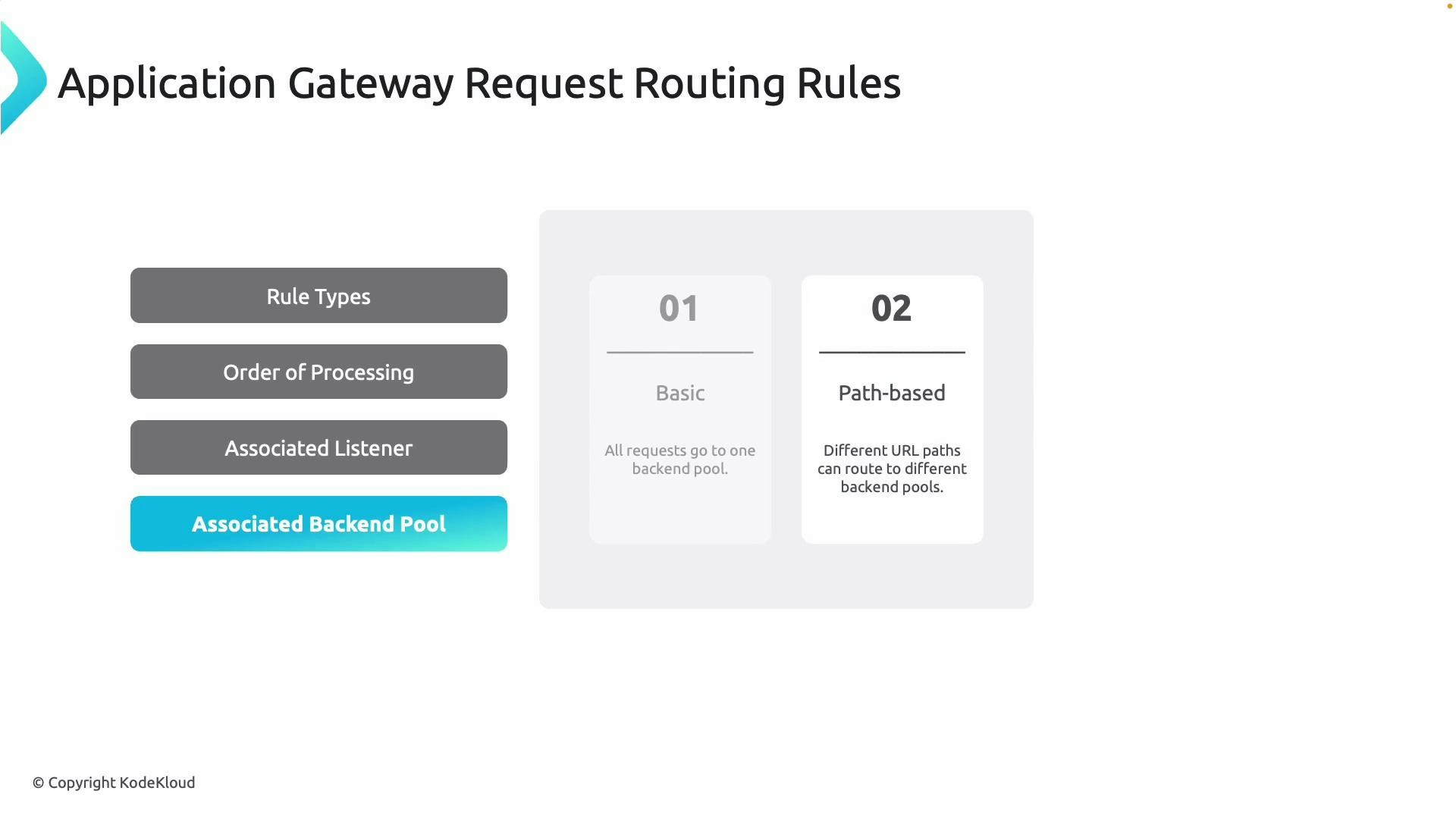
Request routing rules tell the Application Gateway how to forward incoming HTTP(S) requests to backend pools. Two primary rule types are commonly used:| Rule type | Behavior | Typical use case |
|---|---|---|
| Basic | All requests that match the listener are forwarded to a single backend pool. | Simple web apps or single-service frontends. |
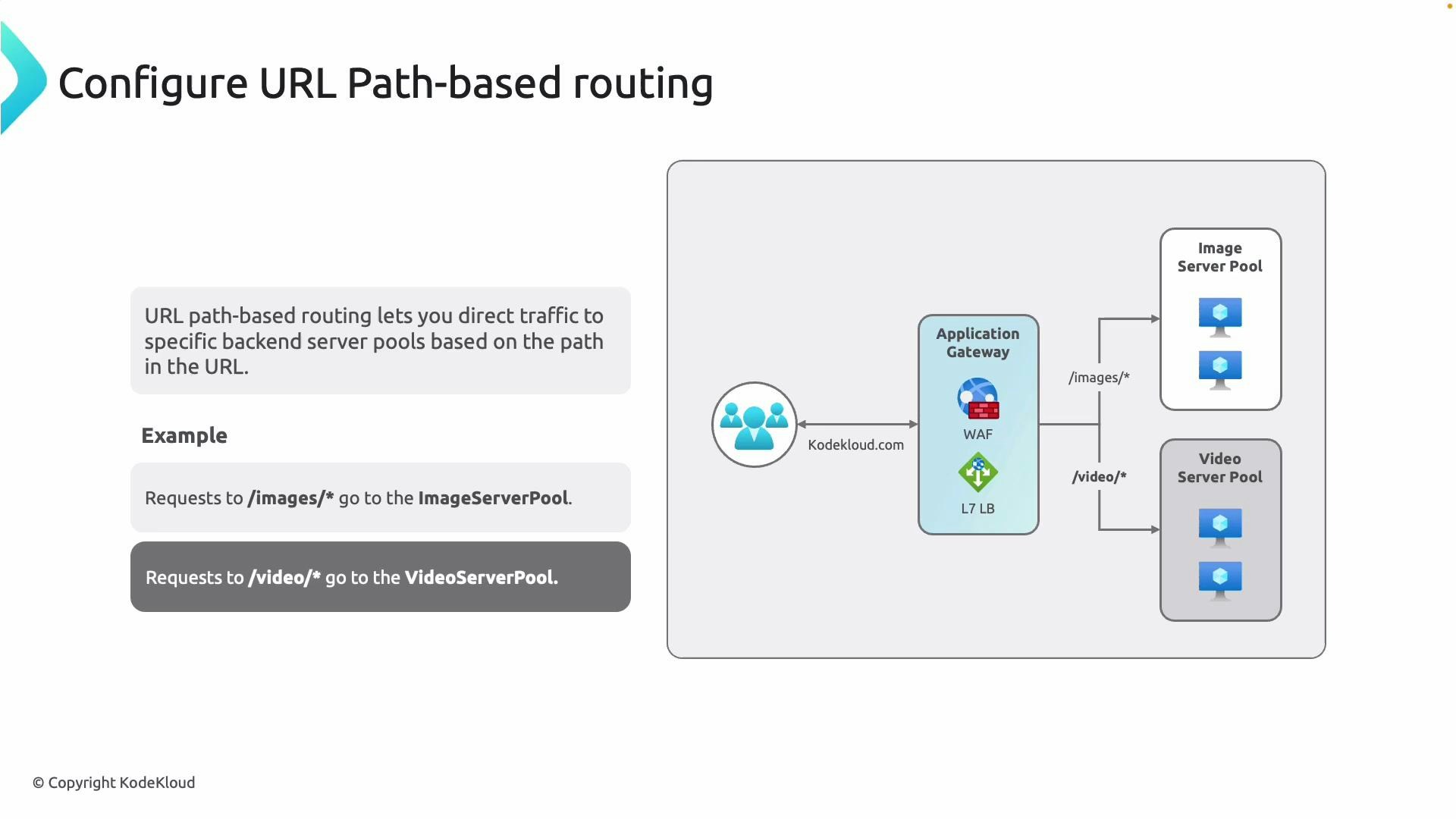
| Path-based | Requests are routed to different backend pools based on URL path patterns (for example /api/* → API pool, /images/* → Image pool). | Microservices, static assets separated from application logic, multi-tenant sites. |
/images/* to an Image Server Pool and /video/* to a Video Server Pool. This separation improves performance, scalability, and operational clarity because each pool can have its own scaling, health probes, and HTTP settings.
Each routing rule must reference a listener. Listeners bind frontend IP/port/protocol combinations to rules, and routing rules reference backend pools and HTTP settings to control how traffic reaches your application instances.
Redirection rules
Redirection rules send clients to different URLs, listeners, or external sites. Common uses include upgrading HTTP traffic to HTTPS, consolidating domains, or moving legacy paths to new endpoints. Supported HTTP redirect status codes:| Status code | Meaning | Typical scenario |
|---|---|---|
| 301 | Permanent Redirect | Moved permanently to a new domain/path. |
| 302 | Found (temporary) | Temporary redirect; user-agent may use original method. |
| 303 | See Other | Instructs client to use GET on the redirected URI. |
| 307 | Temporary Redirect (preserve method) | Temporary redirect while preserving HTTP method (e.g., POST). |
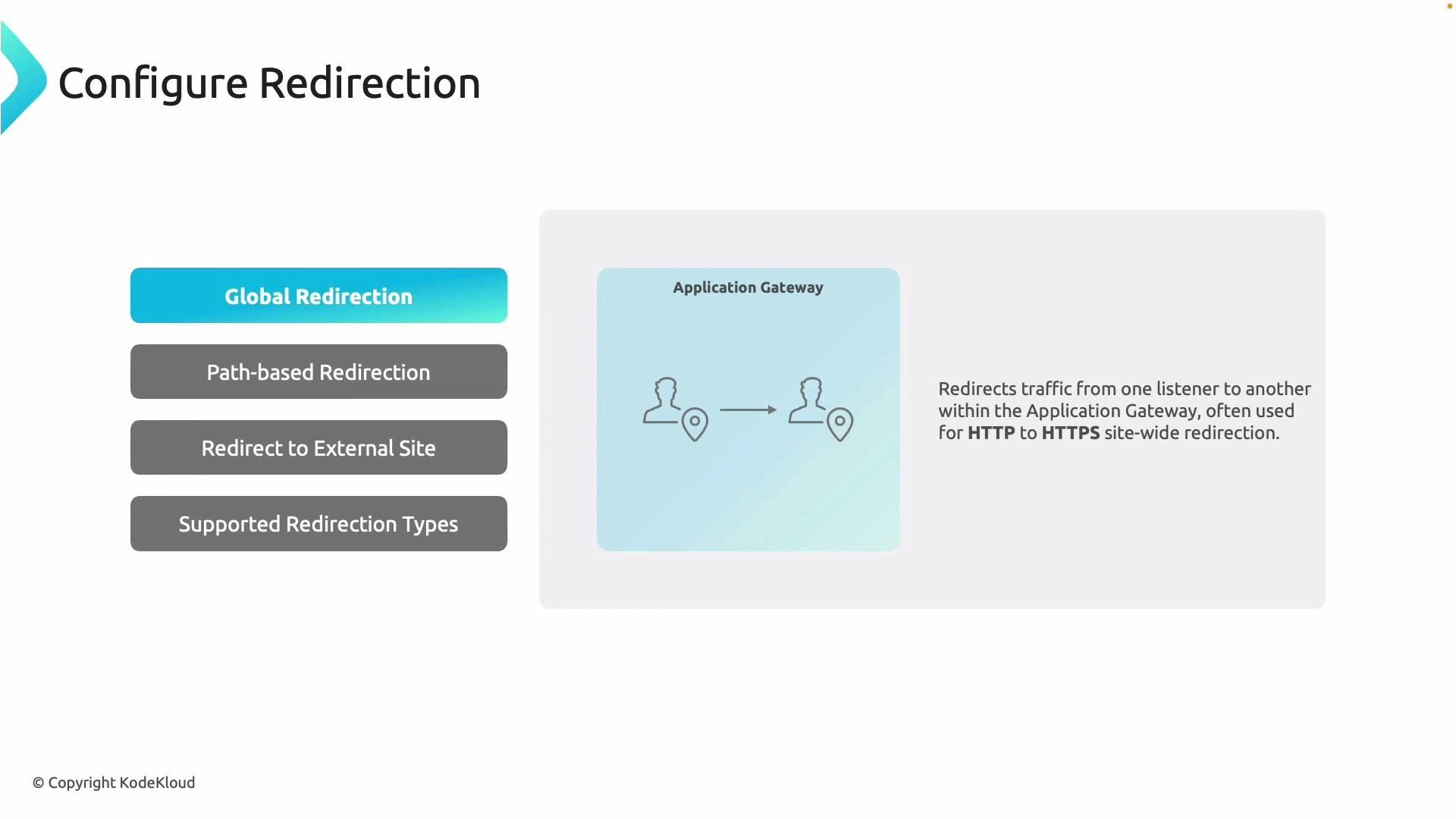
- Global redirection: Redirect all requests from one listener to another (commonly HTTP → HTTPS).
- Path-based redirection: Redirect only specific path patterns (for example,
/cart/*→ HTTPS). - Redirect to external site: Forward traffic to another domain or an external listener (requires a redirect configuration object).



Rewrite policies
Rewrite policies let you modify HTTP request and response attributes before traffic reaches your backend or before responses return to clients. Use rewrite sets (reusable collections of rules) and attach them to routing rules or listeners. Rules support conditions and actions, including header, path, and query-string changes. A valuable action is “re-evaluate request routing,” which reruns path-based routing after the path has been rewritten. Use cases:- Add or remove headers (e.g., X-Forwarded-For, security headers).
- Modify request host or path to match backend expectations.
- Add or alter query parameters for backend routing.
- Re-evaluate routing after path rewrite so the gateway forwards to the correct backend.

Rewrite sets are reusable collections of conditional rules. Associate them with listeners or routing rules to transform headers, paths, or queries before requests hit your backend—useful for host header overrides, security headers, and compatibility mapping.
Portal walkthrough — building a path-based routing example
This concise walkthrough shows how to configure a path-based Application Gateway in the Azure portal. The screenshots below follow the portal steps.- Create the Application Gateway resource:
- Choose subscription, resource group, region, and SKU (Standard_v2 or WAF_v2 for WAF). For this example we select Standard_v2 with a single instance.
- Note: WAF_v2 includes the web application firewall capability.

- Networking: deploy the Application Gateway into a dedicated subnet. Name the subnet exactly ApplicationGatewaySubnet (this exact name is required) and choose an appropriate address range (for example /27 if not using autoscale). Select the subnet for the gateway.
- Frontend: create or select a public IP (or private IP for internal gateways). This becomes the gateway frontend address.
- Backend pools: create backend pools for each service (for example API servers and image servers). Targets can be VM NICs, IP addresses, or FQDNs.
-
Routing rules: add a routing rule and create a listener (for example port 80, protocol HTTP). Choose “Path-based” and configure a default backend target plus path rules such as:
- /api → API backend pool
- /images → IMG backend pool

- Add path entries for
/apiand/images, each pointing to its respective backend settings and backend pool.

- Backend settings: configure HTTP settings for each pool (protocol, port, cookie-based affinity, connection draining, hostname override, etc.). Reuse HTTP settings across multiple paths when settings are identical.

- Finalize and create the gateway. Deployment usually takes several minutes.


Adding backend targets and health probes
- Add virtual machine NICs, IPs, or FQDNs to backend pools.
- Configure health probes (custom or default) and associate them with backend HTTP settings. Custom probes allow specifying a path, host header, HTTPS, interval, timeout, and unhealthy threshold.


Verify in the browser
Use the Application Gateway public IP (or DNS name) to test configured paths:- Hitting the root path should return the default backend content.
- Hitting
/apishould route to the API backend pool. - Hitting
/imagesor/images/index.htmlshould route to the image backend pool.

- Path mapping in the path-based rule.
- Presence of content on the backend (for example index.html).
- Host header or hostname override settings in the HTTP settings.

Rewrites and backend health checks
- Rewrites: Create rewrite sets and associate them with routing rules or listeners to change paths, headers, or query strings. Use conditions to target specific traffic and enable “re-evaluate request routing” when the path change should alter backend selection.
- Backend health: Use the Backend Health blade to inspect each backend instance’s probe status (HTTP 200 indicates healthy). This helps identify failing backend targets and misconfigured probes quickly.

Links and references
- Azure Application Gateway overview: https://learn.microsoft.com/azure/application-gateway/
- Application Gateway routing rules and rewrite policy docs: https://learn.microsoft.com/azure/application-gateway/configuration-overview
- Azure load balancing and traffic management concepts: https://learn.microsoft.com/azure/load-balancer/load-balancer-overview
- Use path-based routing to isolate microservices and static assets.
- Use custom health probes to precisely validate backend health.
- Prefer 301 redirects for permanent moves (SEO-friendly) and 307 for temporary redirects when preserving the HTTP method matters.
- Centralize header and path transformations via rewrite sets to avoid application-level coupling.