How route filters work
- Each route filter contains one or more rules. Each rule corresponds to a Microsoft-managed BGP community that represents a set of public IP prefixes for a particular service (for example, SharePoint Online) or Azure region.
- When a route filter is attached to an ExpressRoute circuit’s Microsoft Peering, only the communities listed in the attached filter are advertised to your on-premises routers.
- Route filters apply only to Microsoft Peering (public/SaaS services). They do not affect private peering, which carries your private Azure Virtual Network prefixes.
Configure a route filter (step-by-step)
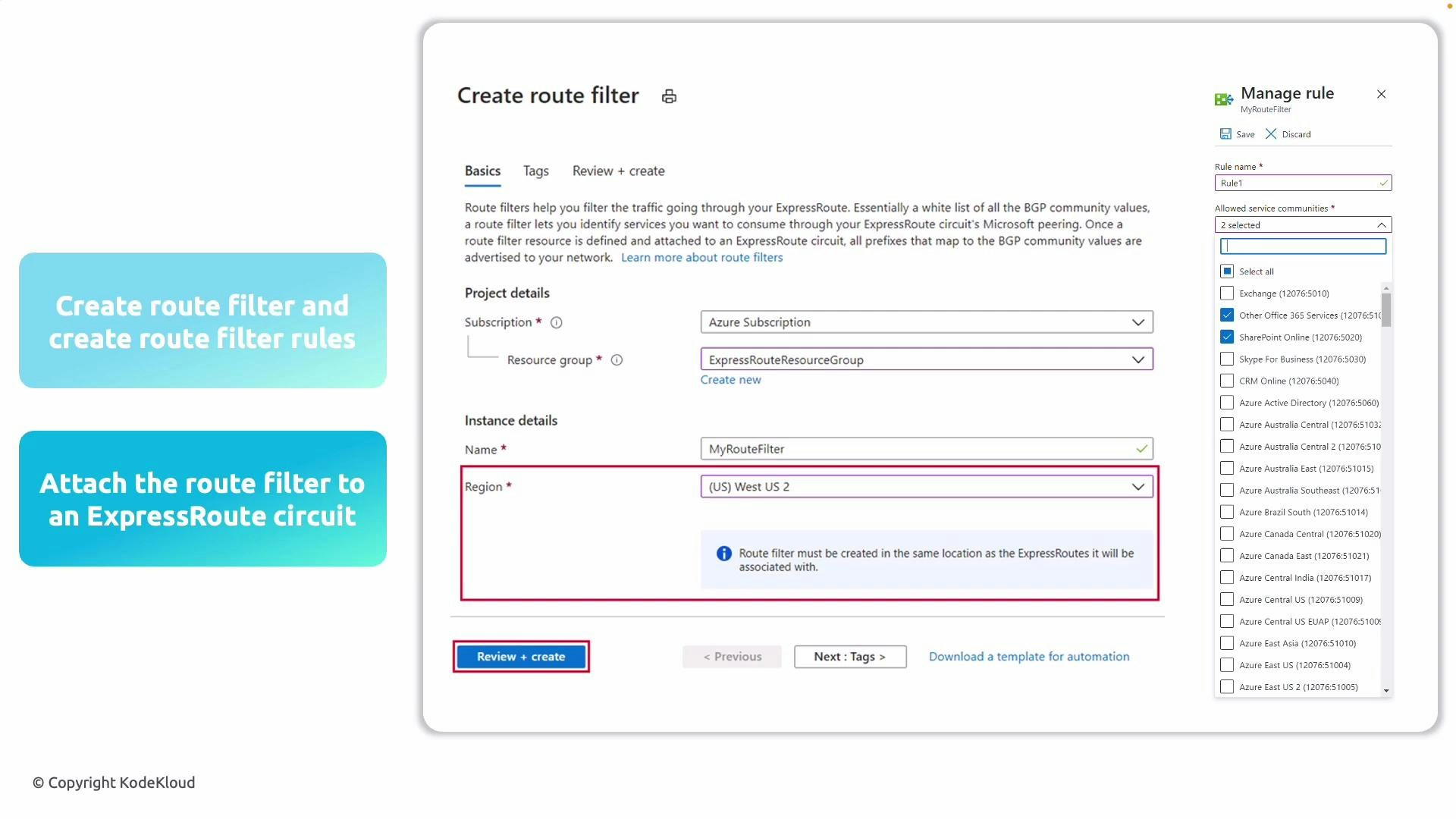
- Create the route filter resource:
- In the Azure portal create a new resource: choose the subscription, resource group, and a name for the route filter.
- Important: the route filter’s region must match the region of your ExpressRoute circuit.
- Add route filter rules:
- For each service or region you want to receive routes for, add a rule that selects the corresponding Microsoft BGP community.
- Each rule represents a set of Microsoft-managed public IP prefixes identified by community values.
- Attach the route filter to your ExpressRoute circuit:
- Attach the completed route filter to the ExpressRoute circuit that is using Microsoft Peering.
- After attaching, only the whitelisted services will advertise their BGP routes to your on-premises network.
Route filters only apply to Microsoft Peering (public/SaaS services). They are not used for private peering, which carries your private Azure Virtual Network prefixes.
Why use route filters
Route filters provide granular control and help maintain predictable routing by preventing unnecessary service prefixes from being advertised to your on-premises routers.| Benefit | What it does | Example |
|---|---|---|
| Restrict advertised services | Only receives prefixes for services you explicitly allow | Receive SharePoint Online prefixes but not Dynamics 365 |
| Reduce routing table size | Keeps on-premises routing tables smaller and simpler | Avoid thousands of unused prefixes from regions or services you don’t use |
| Improve security & manageability | Limits exposure to only required public service prefixes | Easier troubleshooting and policy enforcement |
Best practices
- Start with the minimum set of services you require, then expand the filter as needs change.
- Keep a documented list of which communities you’ve allowed and why.
- Ensure the route filter region matches the ExpressRoute circuit region before attaching.
- Periodically review route filters to remove unnecessary rules and reduce routing complexity.
Additional information and references
- For details on ExpressRoute and peering, see Azure ExpressRoute documentation.
- To see available Microsoft BGP community values and their meanings, consult the Microsoft peering community values documentation.
- You can also connect Virtual Networks to an ExpressRoute circuit using Azure private peering — see the ExpressRoute documentation for VNet connectivity.