Key capabilities and behaviors
-
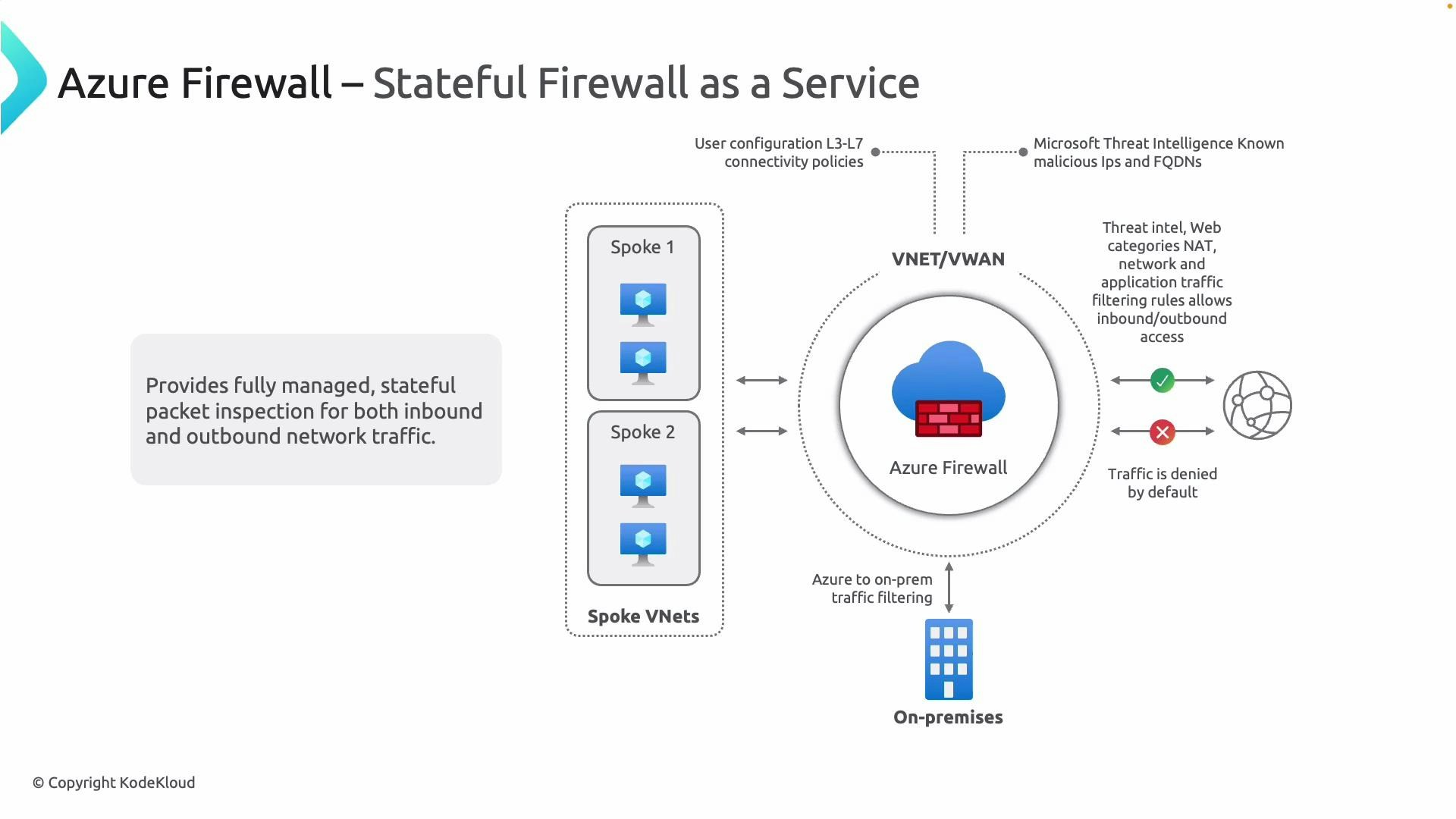
Stateful inspection
Azure Firewall maintains session state for both inbound and outbound flows, providing stronger enforcement than stateless packet filters and enabling correct handling of return traffic for TCP, UDP, and other supported protocols. -
Managed service with built-in redundancy and autoscaling
Microsoft manages high availability and scaling to eliminate single points of failure and lower operational overhead. -
Centralized policy, rule management, and logging
Define and enforce application, network, and NAT rules from a single control plane. Firewall logs and metrics can be collected and analyzed via Azure Monitor (Diagnostic Settings → Log Analytics / Storage / Event Hub): https://learn.microsoft.com/azure/azure-monitor/essentials/diagnostic-settings -
Threat intelligence
Use Microsoft threat intelligence feeds to detect and optionally block traffic to/from known malicious IPs, domains, and URLs (operating across layers 3–7). See: https://learn.microsoft.com/azure/firewall/threat-intelligence -
Hybrid protection
Azure Firewall can protect traffic crossing VPN and ExpressRoute gateways, extending firewall coverage to on‑premises environments: -
NAT capabilities (DNAT & SNAT)
Azure Firewall supports DNAT for publishing internal services to the internet and SNAT for outbound connections using a public IP: https://learn.microsoft.com/azure/firewall/nat-rule-overview
By default, Azure Firewall denies traffic unless an explicit allow rule matches. Plan rules for management, monitoring, jump hosts, and the application flows your workloads require.
Azure Firewall rule types — summary
| Rule type | OSI layer | Use case | Example |
|---|---|---|---|
| Application rules | Layer 7 | Allow/deny outbound HTTP/S and TLS based on FQDNs, URL categories, or explicit URLs | Allow outbound *.contoso.com and block *.malicious.com |
| Network rules | Layers 3/4 | Filter non-HTTP protocols and traffic by IP address, port range, and protocol (5-tuple) | Allow TCP 1433 from subnet A to SQL server IP |
| NAT rules (DNAT/SNAT) | Layer 3/4 | Translate public IP:port to private IP:port for inbound; translate outbound source to public IP | DNAT publicIP:443 -> 10.0.1.10:443 |
| Threat intelligence rules | Layers 3–7 | Block or alert on traffic to/from IPs/domains flagged by Microsoft threat feeds | Deny traffic from known malicious IP ranges |
| FQDN tags & service tags | n/a | Simplify rules by using Azure service or FQDN tag names instead of individual IPs | Use Sql service tag to allow Azure SQL access |
More about each rule type
-
Application rules
Operate at layer 7 and control outbound HTTP/S and TLS flows using FQDNs, built-in URL categories (Premium features), or explicit URLs (Premium/TLS inspection dependencies). They are ideal to restrict web access by hostname rather than IP. -
Network rules
Operate at layer 3/4 and match on source, source port, destination, destination port, and protocol (5-tuple). Use network rules for non-HTTP traffics such as RDP, SSH, database ports, or to control traffic using IP ranges and port ranges. -
NAT rules (DNAT and SNAT)
DNAT transforms a public IP and port into a private IP and port to publish services in Azure. SNAT is used for outbound connections when Azure Firewall translates private source IPs to one of the firewall’s public IPs. -
Threat intelligence-based filtering
Configure Azure Firewall to alert or deny traffic to/from IPs or domains detected by Microsoft’s threat intelligence feeds. This adds an extra defensive layer across multiple protocol layers. -
FQDN tags and service tags
Use Azure service tags (for Azure services) or FQDN tags (for collections of hostnames) to simplify rule maintenance and reduce the need to manage evolving IP lists.
Rule collection and priority evaluation
Azure Firewall evaluates rules using rule collections. Understanding collection types and priority order is essential to predict firewall behavior:- Rule collections group rules of the same type (Application, Network, NAT) and are evaluated in priority order — lower numeric priority executes first.
- Within a collection, rules are evaluated in the order they appear; the first match applies.
- Network and Application rule collections are separate; collection priorities determine cross-type evaluation when both apply.
Logging, metrics, and operational visibility
Collect logs and metrics to enable auditing, alerting, and troubleshooting:- Diagnostic settings → send to Log Analytics, Storage Account, or Event Hub: https://learn.microsoft.com/azure/azure-monitor/essentials/diagnostic-settings
- Typical log types:
- Firewall application logs (application rule matches)
- Firewall network logs (network rule matches)
- Firewall NAT logs (DNAT/SNAT translation events)
- Threat intelligence alerts
- Use Log Analytics queries and Workbooks to build dashboards and alerts. Integrate with SIEMs via Event Hub for long-term retention and cross-environment analysis.
SKUs, advanced features, and considerations
- Azure Firewall is available in multiple SKUs (Standard and Premium). Some advanced capabilities — such as TLS inspection, IDPS, and URL filtering by categories — are available only in the Premium SKU. Check the latest feature and SKU matrix: https://learn.microsoft.com/azure/firewall/
- Consider capacity planning for throughput and connection counts; Azure Firewall autoscaling handles many scenarios but design for expected peak load.
- For hybrid architectures, ensure traffic is steered correctly (UDRs, firewall routes, and gateway configuration) so that inter-subnet and on-premises flows traverse the firewall as intended.
- Azure Firewall documentation: https://learn.microsoft.com/azure/firewall/
- Azure Firewall threat intelligence: https://learn.microsoft.com/azure/firewall/threat-intelligence
- Azure Monitor diagnostic settings: https://learn.microsoft.com/azure/azure-monitor/essentials/diagnostic-settings