NAT rules (DNAT)
NAT (DNAT) rules publish internal services by mapping a public IP address and port on the firewall to a private IP address and port inside your virtual network. Common use case: expose an internal web server by translating traffic destined for the firewall’s public IP on port 80 to the server’s private IP on port 80. Key points:- DNAT performs destination translation (public IP:port -> private IP:port).
- NAT rules are evaluated before any other rule type.
Network rules (L3 / L4)
Network rules apply at layers 3 and 4 to control transport-level access between endpoints. Use network rules to allow or deny connections based on protocol (TCP/UDP/Any), source IP ranges, destination IP ranges, and ports. Common scenarios:- Allowing TCP/UDP access between subnets
- Restricting access to specific IP ranges and ports (e.g., SQL, RDP)
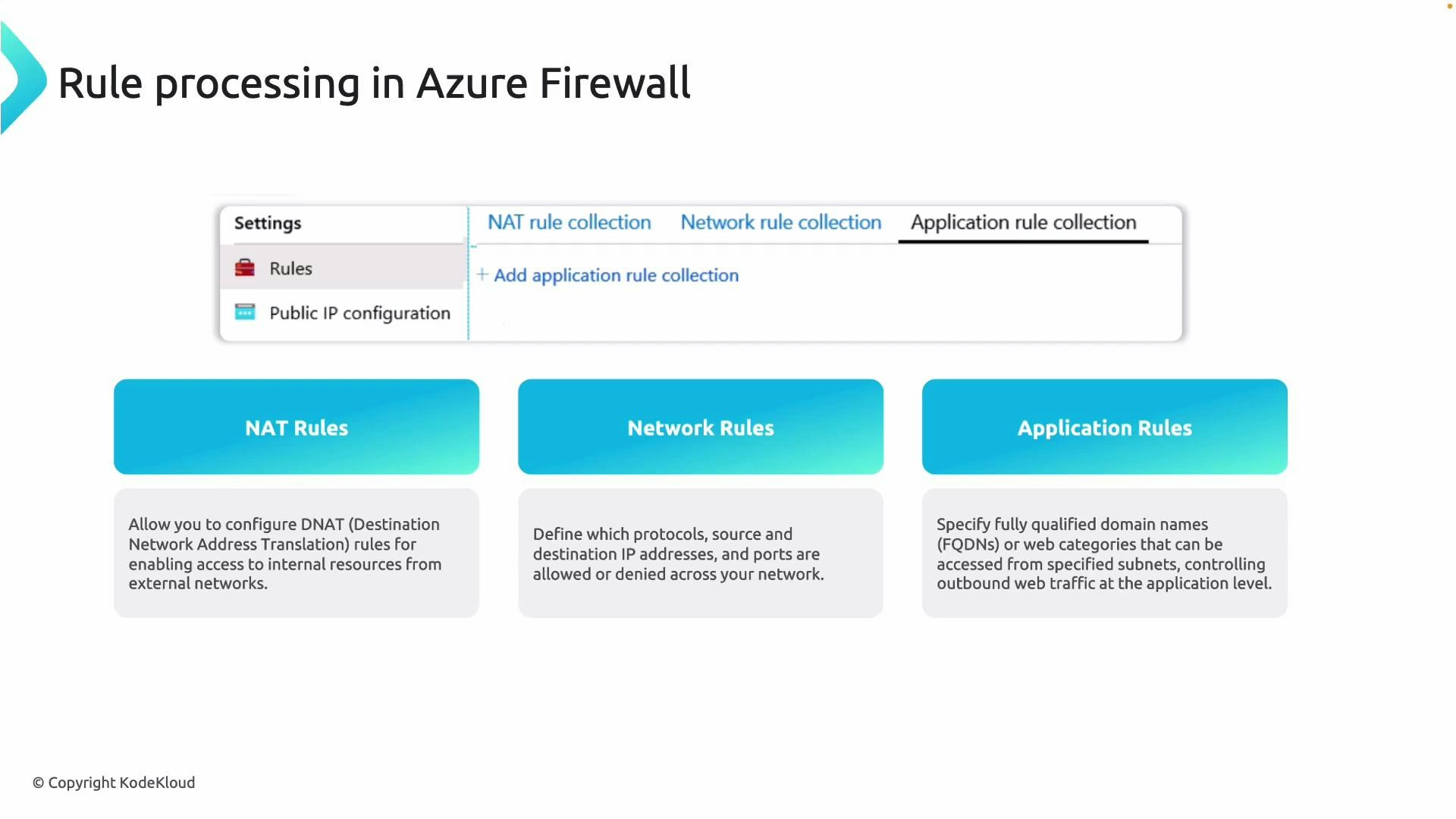
Application rules (L7)
Application rules operate at the application layer and control traffic based on fully qualified domain names (FQDNs) or web categories—ideal for HTTP/S filtering and URL-based access control. Key characteristics:- Used mainly for outbound HTTP/S traffic.
- Filter by FQDNs (e.g., *.microsoft.com) or by web categories (e.g., Social Networking).
- Application rules do not apply to inbound DNAT flows.
Quick comparison
| Rule Type | OSI Layer | Use Case | Example |
|---|---|---|---|
| NAT (DNAT) | L3/L4 (destination translation) | Publish internal services (inbound) | Map publicIP:80 → 10.0.1.4:80 |
| Network rule | L3/L4 | Transport-level allow/deny by IP and port | Allow TCP 1433 between subnets |
| Application rule | L7 | Domain/URL-based filtering for HTTP/S (outbound) | Allow *.microsoft.com only |
Rule processing order (strict)
Azure Firewall evaluates rules in this strict sequence for each flow:- NAT rules — evaluated first. A matched DNAT rule translates the destination IP/port and forwards the flow according to that mapping.
- Network rules — evaluated next if no NAT rule matched. Enforce protocol, source/destination IPs, and ports.
- Application rules — evaluated last if neither NAT nor network rules matched. Apply FQDN/web-category controls for HTTP/S.
Remember: NAT (DNAT) rules are always processed before network and application rules. If a DNAT rule matches a flow, the firewall translates and forwards that traffic without further evaluation by network or application rules for that flow.