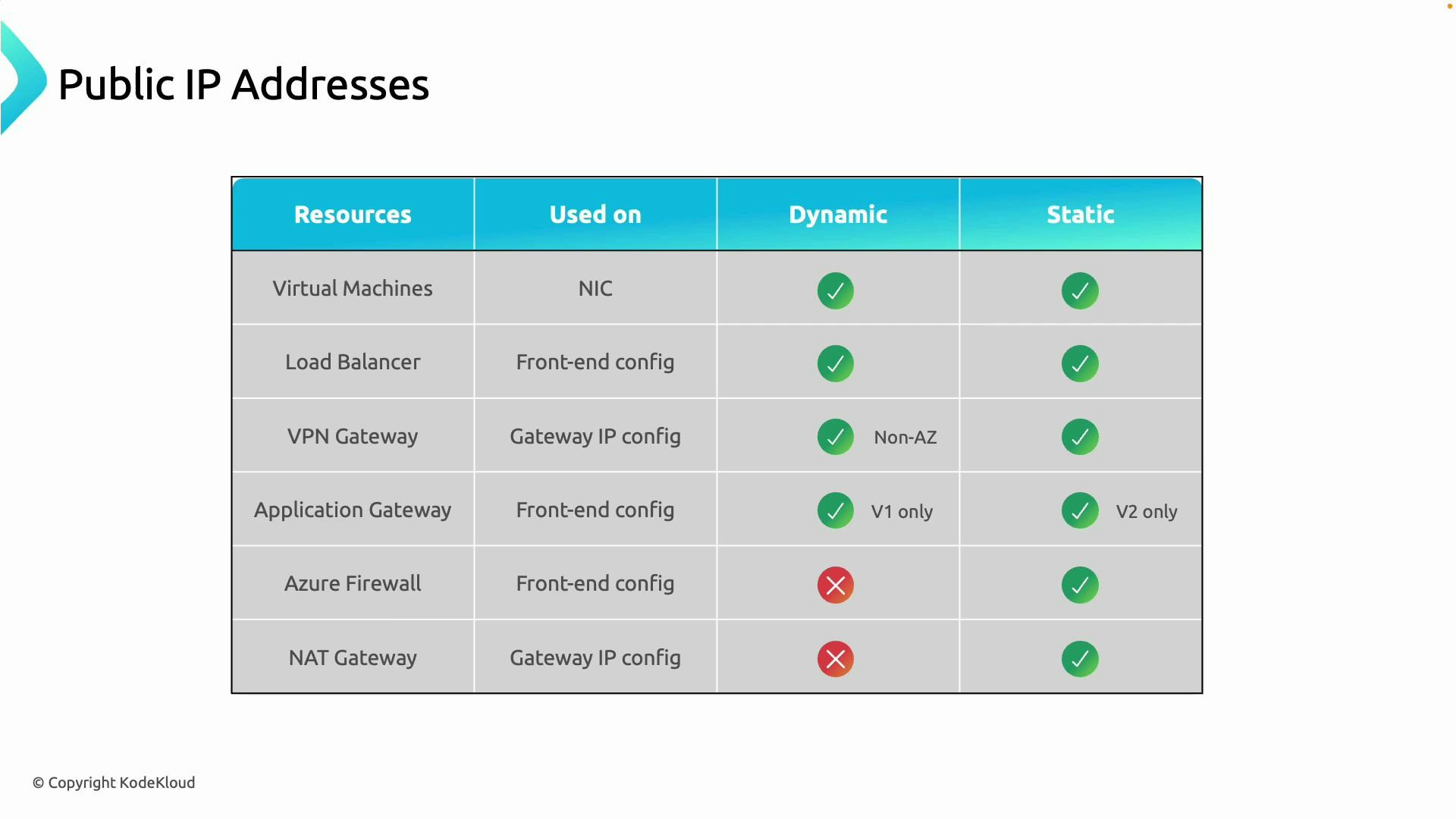
| Resource | Where public IP is attached | Static supported? | Dynamic supported? | Recommended for production |
|---|---|---|---|---|
| Virtual Machine (NIC) | Network Interface (NIC) | Yes (Standard or Basic static) | Yes (Basic dynamic) | Static (Standard) |
| Load Balancer (public) | Front-end IP configuration | Yes (Standard static) | Yes (Basic dynamic) | Static (Standard) |
| VPN Gateway | Gateway IP configuration | Yes (required for production) | No | Static (Standard) |
| Application Gateway | Front-end configuration | Yes (v2 Standard) | Historically v1 allowed dynamic | Static (v2/Standard) |
| Azure Firewall | Firewall front-end | Yes (static or prefix) | No | Static |
| NAT Gateway | NAT Gateway outbound | Requires static public IP / prefix | No | Static (required) |
-
Virtual Machines
Attach a public IP on the VM’s network interface (NIC) if the VM must be reachable from the internet. Basic SKU public IPs can be dynamic or static; Standard SKU public IPs are always static. For production workloads and DNS-backed endpoints, use a static Standard SKU public IP so the address remains predictable. -
Load Balancer
Public IPs attach to the load balancer’s front-end IP configuration. Basic SKU supports dynamic or static addresses; Standard SKU provides static addresses only and offers zone resilience and improved security. For public-facing load balancers (for example, web traffic), prefer a Standard static public IP. -
VPN Gateway
VPN Gateway public IPs attach to the gateway’s IP configuration. Production site-to-site and point-to-site VPNs require a static public IP (use the Standard SKU). Dynamic assignment is not appropriate because an IP change breaks persistent connectivity between sites. -
Application Gateway
The Application Gateway uses a public IP on its front-end configuration for internet-facing deployments. Application Gateway v2 targets production scenarios and pairs with Standard SKU static IP addresses; v1 historically allowed dynamic IPs. For internet-facing Application Gateways use a static Standard SKU public IP to keep DNS records and firewall rules stable. -
Azure Firewall
Azure Firewall requires public IPs on its front-end configuration to support predictable outbound SNAT and inbound rules. Use static public IP addresses or assign a public IP prefix. Static IPs keep source IPs predictable for external integrations and firewall rules. -
NAT Gateway
NAT Gateway provides outbound internet connectivity from subnets and is used to ensure predictable outbound source IP addresses. It requires static public IPs or a public IP prefix. Do not use dynamic public IPs for NAT Gateway.
Static public IPs are recommended for production services. They provide a predictable, persistent endpoint for DNS records, firewall rules, and external integrations. Dynamic public IPs are more appropriate for short-lived or test environments because they can change during lifecycle operations.
| SKU | Static vs Dynamic | Security posture | Availability zones | Recommended use |
|---|---|---|---|---|
| Standard | Always static | Secured by default (deny unless allowed) | Yes | New production workloads |
| Basic | Static or dynamic | Open by default (less secure) | No | Legacy or testing scenarios only |
- Always provides a static IP.
- Secured by default — network access is restricted unless you explicitly allow it.
- Supports availability zones.
- Intended for production workloads and recommended for new deployments.
- Can be configured as static or dynamic.
- Open by default and lacks the hardened defaults of Standard SKU.
- Does not support availability zones.
- Best avoided for new production deployments; use only for legacy compatibility or short-term testing.
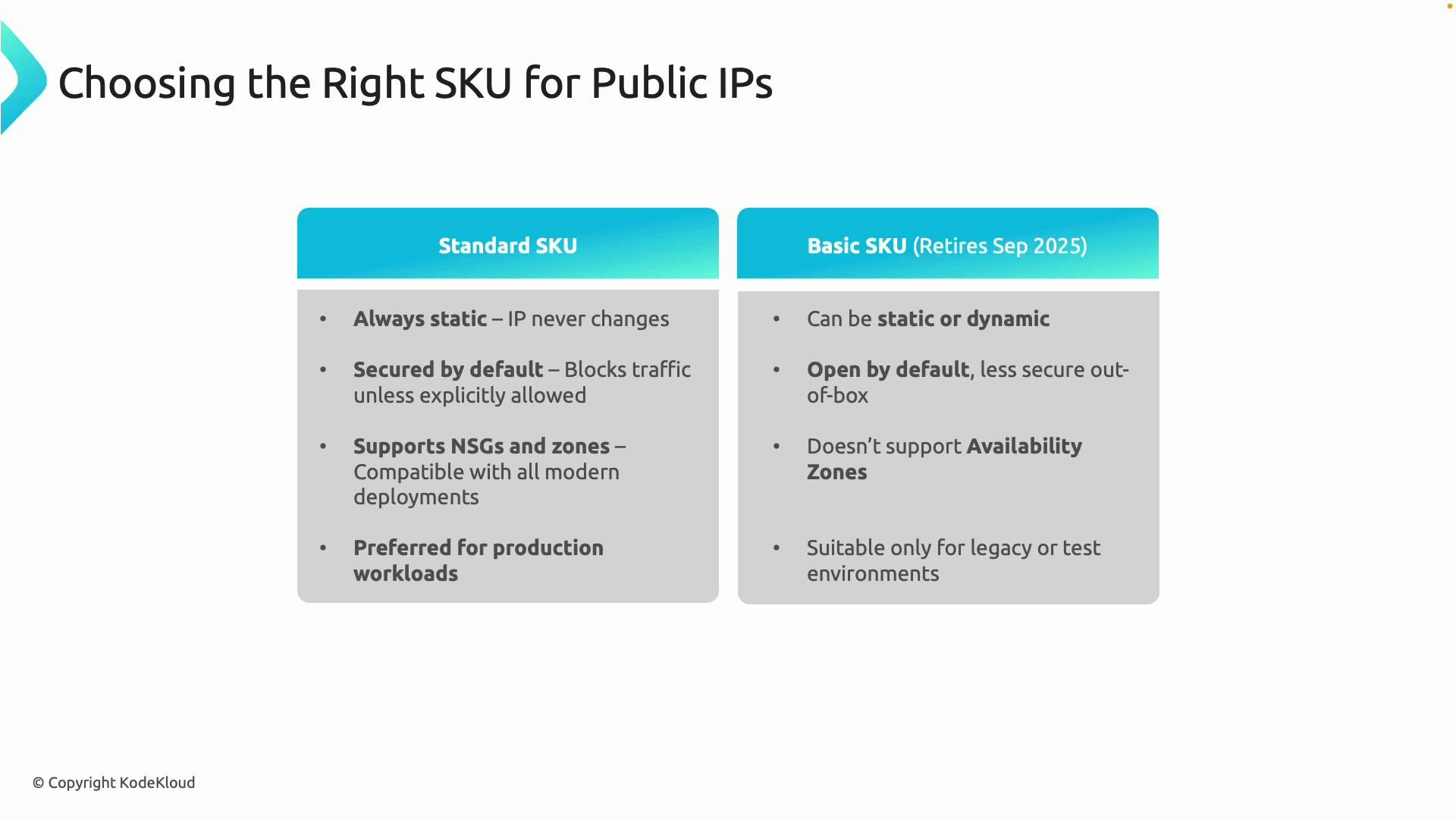
The Basic public IP SKU is intended for legacy/testing scenarios and may be deprecated in the future. For new or production deployments choose the Standard SKU to ensure security, availability zone support, and long-term compatibility.
- Use Standard SKU static public IPs for any service that must remain reachable or where an IP is embedded in DNS, firewall rules, or third-party allowlists.
- Attach public IPs in the recommended place for each service: NICs for VMs, front-end configs for load balancers and application gateways, gateway configs for VPN Gateway, firewall front-ends for Azure Firewall, and NAT Gateway for subnet egress.
- For predictable outbound IPs (SNAT) use NAT Gateway or assign static public IPs to firewall/NAT devices. Avoid relying on dynamic IPs for outbound egress in production.
- Consider using Public IP Prefixes when you need a contiguous range of static addresses (for example, when you must advertise a block to external partners).
- Public IPs are attached at different places depending on the Azure service: NIC (VMs), front-end configs (Load Balancer, Application Gateway), gateway IP config (VPN Gateway), firewall front-end (Azure Firewall), and NAT Gateway for outbound.
- Static public IPs should be used for production workloads to provide stability and predictability. Dynamic public IPs are suitable for temporary or test scenarios.
- Prefer Standard SKU public IPs for new deployments because they are secure by default and support availability zones. Phase out Basic SKU use in production.
- Azure Public IP documentation
- Azure Load Balancer overview
- Azure VPN Gateway documentation
- Azure Application Gateway documentation
- Azure Firewall documentation
- Azure NAT Gateway documentation