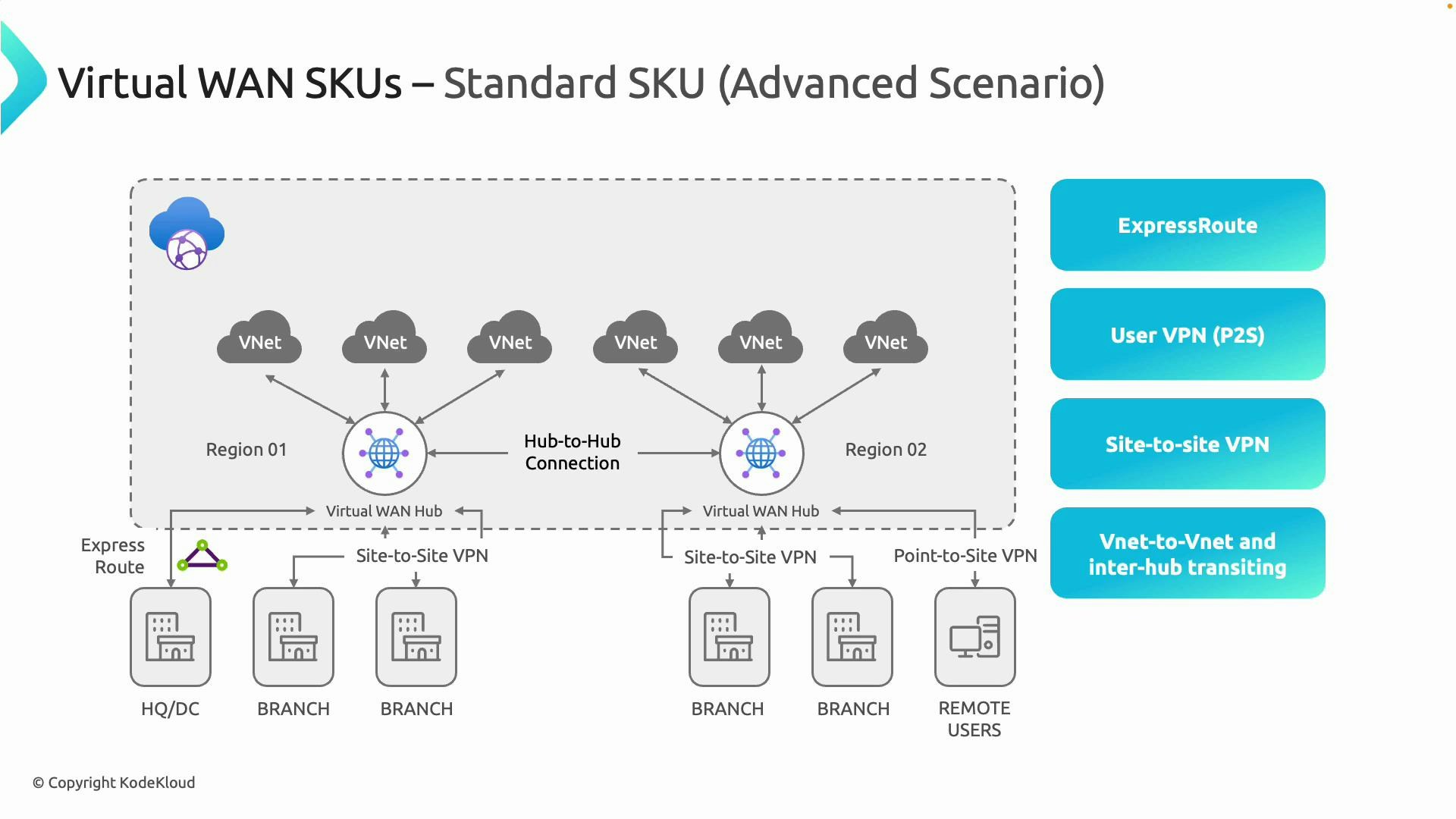
| Connection type | Typical use case |
|---|---|
| Site-to-site VPN | Branch office or data center ↔ Azure |
| Point-to-site VPN | Individual remote users (road warriors) |
| ExpressRoute | Private, dedicated connectivity for high-throughput/low-latency links |
| VNet-to-VNet / Inter-hub transit | VNet connectivity across regions and hubs |
- Centralized management: A single control plane for site-to-site, point-to-site, ExpressRoute, and VNet connectivity.
- Global transit and scalability: Add hubs, VNets, branches, or users without redesigning the fabric.
- Automation: Automated VNet attachments and route distribution reduce the need for manual peering and bespoke routing.
- Observability: Built‑in topology and traffic insights simplify troubleshooting and capacity planning.
- Managed service: Azure operates the underlying infrastructure (gateways, route distribution, managed subnets), reducing operational overhead.
| SKU | Best for | Supported connectivity/features |
|---|---|---|
| Basic | Simple, low-cost site-to-site deployments | Site-to-site VPN |
| Standard | Enterprise deployments with remote users and global transit | Site-to-site, Point-to-site (user) VPN, ExpressRoute, VNet-to-VNet, hub-to-hub transit, centralized user VPN configuration |
Choose Basic for straightforward, low-cost site‑to‑site scenarios. Choose Standard when you require point‑to‑site (remote user) VPNs, ExpressRoute integration, or inter‑hub transit across regions.
Mixing hub types with a different Virtual WAN SKU is not supported. Plan your SKU selection up front to avoid redeployments or architectural changes later.
- Minimum hub address space: /24.
- Azure manages internal subnets for gateways, route distribution, and managed services — you only supply the overall CIDR block.
- Hub address space is consumed by services such as VPN gateways, routing services, and optional managed firewalls.
- Avoid overlapping CIDR ranges with on-premises networks or other cloud VNets to prevent routing conflicts.
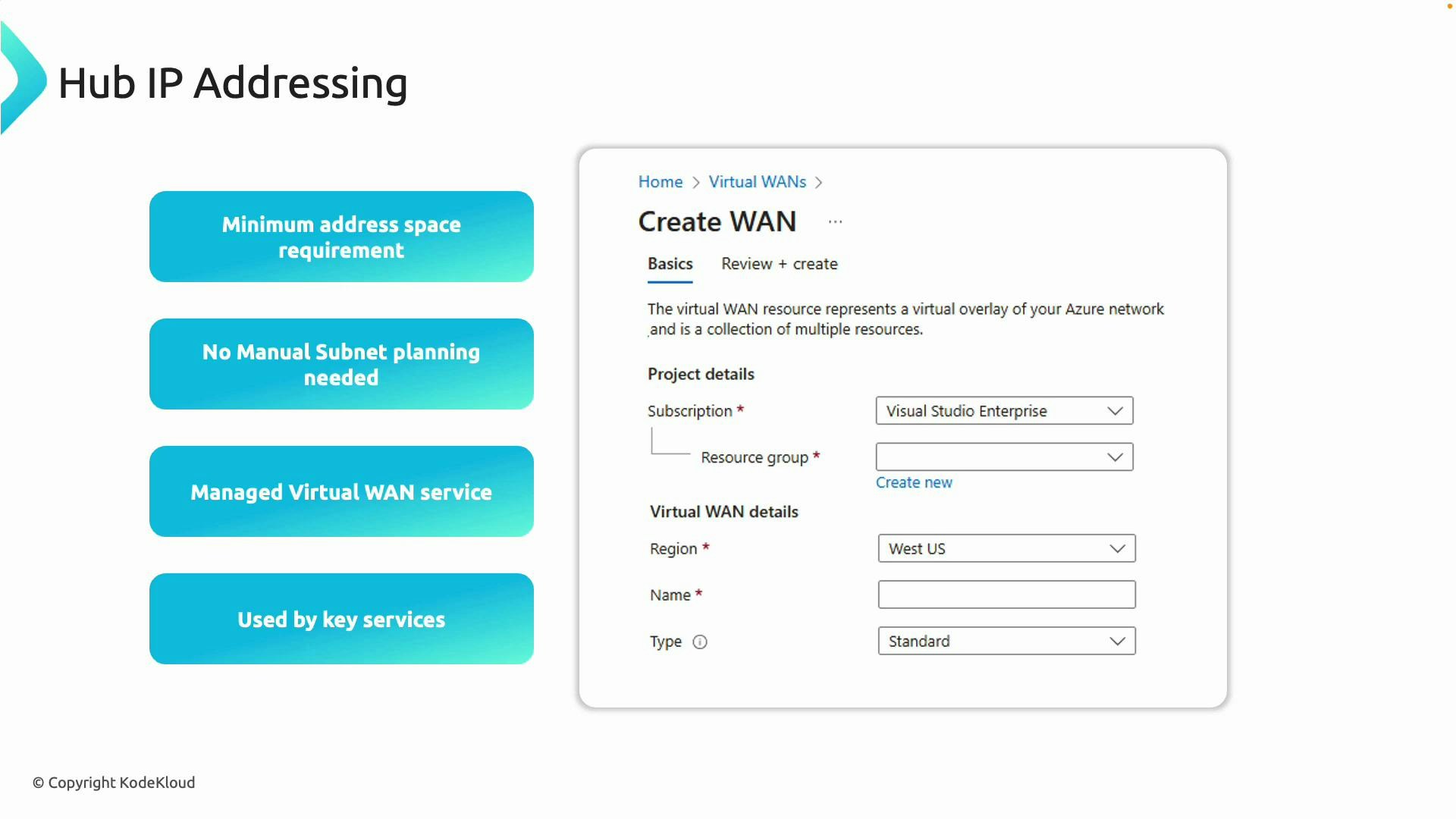
- Centralize IP addressing: Maintain a global IP plan so hub CIDRs, VNet CIDRs, and on-premises ranges do not overlap.
- Choose SKU based on required features: Use Standard for any deployment requiring user VPNs, ExpressRoute, or multi-hub transit.
- Let Virtual WAN manage hub subnets: Provide a CIDR that fits into your IP plan and allow Azure to provision subnets for managed services.
- Monitor and scale: Use Virtual WAN diagnostics, logs, and Network Insights to monitor traffic patterns and scale hubs or gateways as needed.
- Document hub-to-hub topology: For multi-region transit, maintain a clear diagram and route policy documentation to simplify troubleshooting and change control.
- Azure Virtual WAN overview: https://learn.microsoft.com/azure/virtual-wan/
- Azure ExpressRoute: https://learn.microsoft.com/azure/expressroute/
- Azure VPN Gateway: https://learn.microsoft.com/azure/vpn-gateway/
- Network Insights & diagnostics: https://learn.microsoft.com/azure/network-watcher/